A System and Organization Controls 2 (SOC 2) report is an attestation framework developed by the American Institute of Certified Public Accountants (AICPA) that evaluates a service organization’s controls relevant to security, availability, processing integrity, confidentiality, or privacy. An independent Certified Public Accountant (CPA) firm performs the audit and provides a formal opinion on whether the organization’s controls are suitably designed (Type 1 report) and operating effectively over a period (Type 2 report) to meet the criteria defined in the AICPA’s Trust Services Criteria.
Figuring out which framework you need depends entirely on whether you require adaptable security reporting for a broad audience or a rigid, healthcare-specific certification. For organizations pursuing a SOC 2 audit, understanding HITRUST is crucial for navigating customer conversations and making strategic decisions about your compliance roadmap.
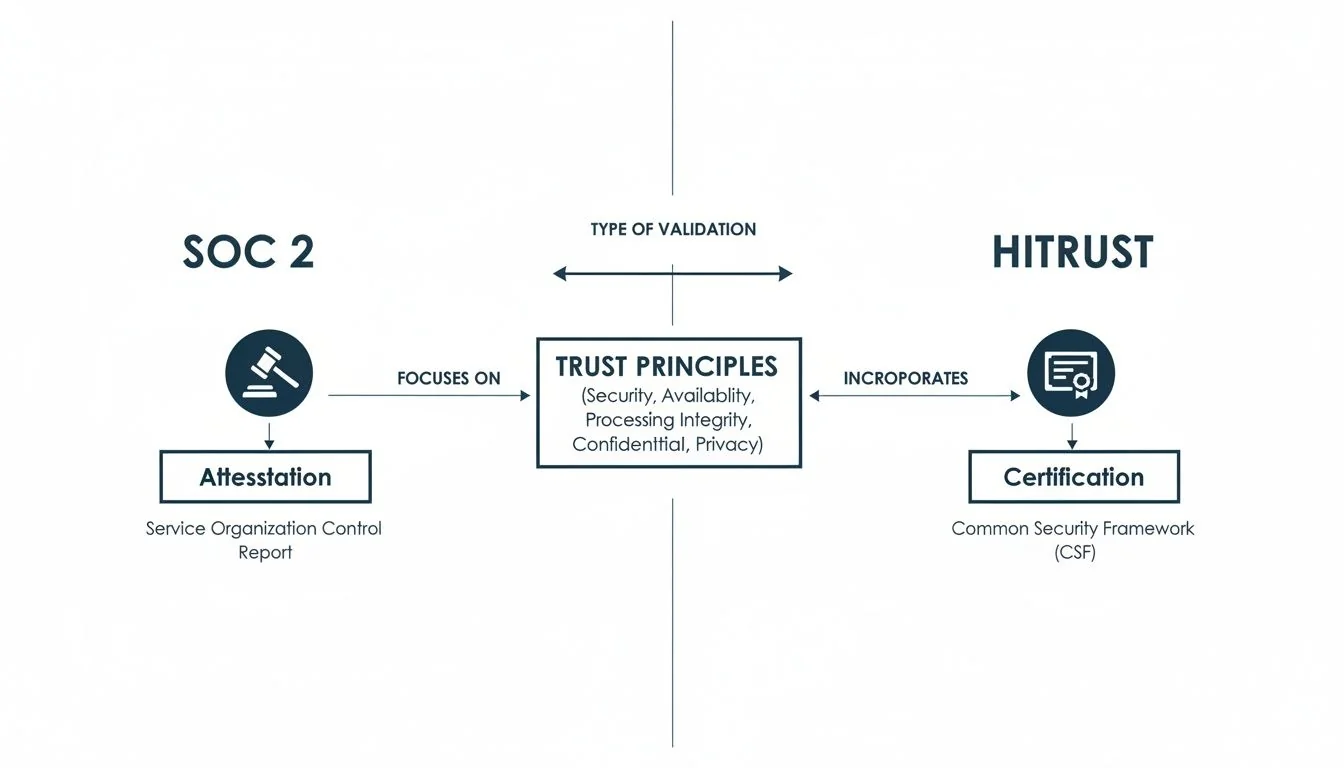
Defining SOC 2 Attestation and HITRUST Certification

A SOC 2 report is an attestation framework designed by the American Institute of Certified Public Accountants (AICPA). The primary purpose is for an independent auditor to evaluate a company’s controls against a set of principles called the Trust Services Criteria (TSC): Security, Availability, Confidentiality, Processing Integrity, and Privacy. The output is a detailed report with an auditor’s opinion, not a certificate.
HITRUST, on the other hand, offers a certifiable framework—the HITRUST CSF. It was built to harmonize dozens of different security and privacy regulations into a single, massive control set. It originated in the healthcare industry’s need for a standardized, prescriptive, and repeatable method to demonstrate security and compliance.
The Core Distinction: Flexibility vs. Prescription
The fundamental difference between SOC 2 and HITRUST is that SOC 2 is principles-based, while HITRUST is prescriptive.
With SOC 2, the AICPA tells you what you need to achieve (the criteria), but your organization defines how you achieve it (the controls). This flexibility allows you to design a control environment that aligns with your specific business operations, technology stack, and risk tolerance. For example, to meet criterion CC6.2 regarding periodic content access reviews, a startup might use a manual spreadsheet-based process, whereas a larger enterprise might implement an automated Identity and Access Management (IAM) solution. As long as the control is effective in meeting the criterion, it is acceptable for a SOC 2 audit.
HITRUST takes the opposite approach. It provides a detailed, prescriptive list of controls that must be implemented and tested against specific scoring rubrics. Its requirements are mapped to a vast number of standards, including NIST, ISO 27001, and HIPAA. This is why organizations in the healthcare space often have to deal with overlapping requirements like HIPAA compliance when considering HITRUST.
Why this matters for someone pursuing SOC 2: The flexibility of SOC 2 is its primary advantage for most tech companies. It provides a more accessible and faster path to proving a strong security posture. You can focus your budget and engineering resources on the controls that are most relevant to your specific services and customer commitments, without the burden of a large, prescriptive framework that may include many irrelevant requirements. This makes achieving SOC 2 audit readiness a more efficient and targeted effort.
SOC 2 and HITRUST at a Glance
This table breaks down the core DNA of each framework, highlighting where they fundamentally differ in structure and purpose.
| Attribute | SOC 2 | HITRUST |
|---|---|---|
| Governing Body | AICPA (American Institute of CPAs) | HITRUST Alliance |
| Type | Attestation Report (Auditor’s Opinion) | Certification (Pass/Fail Score) |
| Approach | Principles-based & Flexible | Prescriptive & Standardized |
| Primary Industry | Technology, SaaS, FinTech, General | Healthcare, Life Sciences |
| Control Set | Based on selected Trust Services Criteria | Comprehensive, mapped to multiple standards |
Understanding this core distinction is the first step toward effective SOC 2 audit readiness. For the vast majority of technology companies not exclusively serving the healthcare market, SOC 2 offers a credible, adaptable, and efficient path to building customer trust. It establishes a strong compliance foundation that proves your commitment to security, paving the way for a successful attestation that will satisfy even the most demanding enterprise customers.
Understanding the Purpose and Assurance Model
At its core, the difference between SOC 2 and HITRUST boils down to a critical concept: attestation versus certification. This distinction directly impacts how you prepare for your audit and how you communicate your security posture to customers.
A SOC 2 report is an attestation—an independent CPA firm’s professional opinion on your security controls. HITRUST, on the other hand, is a formal certification, a pass/fail designation earned by meeting a prescriptive, quantitative score against the HITRUST CSF.
Attestation: An Expert Opinion
The SOC 2 assurance model is centered on professional attestation. A licensed CPA firm, expert in audit standards, evaluates your security program against the AICPA’s Trust Services Criteria. The final SOC 2 report is not a certificate; it’s the auditor’s formal opinion letter, accompanied by a detailed description of your controls and the auditor’s tests.
This model is inherently flexible. Your organization defines the specific controls you use to meet the AICPA’s principles. The auditor’s job is to test if those controls are designed appropriately and operating effectively. For instance, to meet the logical access criterion CC6.1 (COSO Principle 12), you might implement controls like multi-factor authentication, role-based access control (RBAC) policies, and quarterly user access reviews. The auditor opines on their effectiveness—they do not prescribe these specific controls.
This is why there’s no such thing as being “SOC 2 certified.” You receive a SOC 2 report with an auditor’s opinion, which you then share with customers to provide assurance.
Certification: A Prescriptive Benchmark
HITRUST operates on a certification model. It uses the standardized, prescriptive HITRUST CSF framework, where every organization is scored against the exact same detailed requirements. This approach is built for consistency, particularly in regulated industries like healthcare where uniform compliance is paramount.
To become HITRUST certified, an organization’s controls are scored against the CSF based on a defined maturity model (Policy, Procedure, Implemented, Tested, and Managed). You must meet or exceed a defined scoring threshold to earn the certification. It’s a clear, pass/fail system.
Why this matters for someone pursuing SOC 2: Understanding this distinction is crucial during customer security reviews. You can educate prospects that your SOC 2 report provides a deeper, more tailored form of assurance than a simple certificate. By explaining that a licensed CPA firm has rendered a professional opinion on your specific control environment, you can build trust and demonstrate a mature understanding of security assurance. This is often more valuable to sophisticated buyers than a generic pass/fail checkmark.
This model removes all ambiguity. When a customer sees a “HITRUST certified” vendor, they know that vendor has met a specific, high bar for security and compliance controls as defined by the HITRUST Alliance.
Comparing Scope Controls and Applicability
When weighing SOC 2 against HITRUST from a compliance perspective, the most significant differences lie in scope and control requirements. The choice you make here directly impacts the resources, time, and focus of your security team.
A SOC 2 report evaluates your controls against the AICPA’s Trust Services Criteria (TSC). The framework is principles-based, which is a major advantage for organizations preparing for a SOC 2 audit. It specifies the objectives to meet but grants you the freedom to design the controls to achieve them.
HITRUST, in contrast, is a prescriptive and certifiable framework. It’s designed to harmonize numerous regulations—like HIPAA, NIST, and ISO—into a single, comprehensive set of controls. This creates a standardized, non-negotiable benchmark that has become the de facto standard for the healthcare industry and its vendors.
SOC 2’s Flexible, Principles-Based Approach
The power of SOC 2 lies in its adaptability. When preparing for a SOC 2 audit, you must address the Security criterion (also known as the common criteria). You then have the option to add Availability, Confidentiality, Processing Integrity, and Privacy to the scope, based on your service commitments and customer promises.
This selective scoping is a strategic advantage. It allows you to tailor the audit directly to your business, making the process more focused and cost-effective. You can concentrate your resources on proving the controls that are most relevant to your clients.
For example, a common criterion like CC6 (Logical and Physical Access Controls) requires you to restrict system access. In a SOC 2 audit, you define those controls. This might include a combination of role-based access control (RBAC), quarterly access reviews, and automated de-provisioning scripts. The auditor’s job is to test whether your chosen controls effectively meet the criterion’s objective, not to mandate a specific tool or process.
HITRUST’s Prescriptive, All-Inclusive Controls
HITRUST takes a more rigid—and much more expansive—approach. Instead of flexible principles, it provides a massive, prescriptive library of controls mapped across dozens of authoritative sources. This prescriptive nature is its core strength, as it creates a uniform standard that is highly valued in regulated sectors.
A typical HITRUST r2 certification requires implementing and testing 300-400+ specific controls, a significant increase from the 30-100+ controls in a typical SOC 2 report. The full HITRUST framework contains over 2,000 controls across 19 domains, from which a custom set is derived based on organizational factors.
This depth is precisely why healthcare organizations demand it. The HITRUST r2 certification—which requires two years of operational evidence—delivers a formal certification, not just an attestation report like SOC 2. It signals a highly mature risk management program to covered entities.
As you can see, SOC 2 results in an auditor’s opinion (an attestation), while HITRUST leads to a formal, pass/fail certification. This distinction is critical to enterprise buyers in regulated industries.
Why this matters for someone pursuing SOC 2: The lower control count and flexible scoping of SOC 2 make it a far more attainable and manageable project. You can achieve a high level of assurance for your customers without the immense resource drain required by HITRUST. For your SOC 2 audit, you can focus on implementing robust controls for key areas like CC7.1 (System Monitoring for Changes) and CC7.2 (Incident Response) that directly address the security of your platform, rather than being forced to implement hundreds of prescriptive controls that may not be relevant to your service.
A Reality Check on Cost and Timeline
When planning for a compliance initiative, the business case often comes down to two factors: cost and timeline. For a company focused on achieving a SOC 2 report, understanding the resource commitment compared to HITRUST reinforces why SOC 2 is the strategic choice for most technology organizations.
SOC 2 is designed to be an efficient path to demonstrating security. The costs are generally manageable for a growing business. HITRUST, due to its prescriptive nature, expansive control set, and rigorous scoring process, represents a significantly larger financial and operational commitment.

Breaking Down the SOC 2 Investment
With a SOC 2 audit, you’ll encounter two main report types: Type 1 and Type 2.
A SOC 2 Type 1 report serves as a snapshot, attesting that your controls were suitably designed at a single point in time. It’s a fast and affordable way to show prospects you are serious about security, often used to meet initial due diligence requirements.
The SOC 2 Type 2 report is the goal for most organizations. It evaluates the operating effectiveness of your controls over a period (typically 3-12 months). Its value is exponentially higher, as it provides customers with assurance that your security program works in practice, not just on paper. This is the report that satisfies enterprise security teams and unlocks larger deals.
Here’s a look at typical costs and timelines for SOC 2:
- SOC 2 Type 1:
- Cost: Generally runs from $15,000 to $35,000.
- Timeline: Can be completed in 1-3 months, from readiness assessment to final report issuance.
- SOC 2 Type 2:
- Cost: Typically lands between $25,000 and $70,000+ for the first year, depending on scope and complexity.
- Timeline: Plan for 6-12 months for the first audit, which includes the crucial audit observation period.
The Higher Stakes of HITRUST Certification
HITRUST certification operates in a different financial and temporal stratosphere. The process is famously complex due to its strict control requirements, granular scoring, and the mandatory use of the MyCSF platform, which itself carries subscription fees.
The investment varies based on the chosen assessment. The i1 (implemented, 1-year) validated assessment provides moderate assurance. However, the r2 (risk-based, 2-year) validated assessment is the gold standard for healthcare and demands a massive commitment of time, people, and budget, often starting at $60,000–$200,000.
Why this matters for someone pursuing SOC 2: The significant cost and time difference is a powerful business justification for prioritizing SOC 2. The budget saved by choosing SOC 2 over HITRUST can be reinvested into product development, sales, or engineering—the core drivers of growth. When you need to balance credible security assurance with fiscal reality, the path to SOC 2 audit readiness provides a powerful strategic advantage, delivering the trust your customers need without derailing your budget or roadmap. This efficiency is a core part of the SOC 2 value proposition.
Picking the Right Framework: Real-World Scenarios
Deciding between SOC 2 and HITRUST is a practical business decision driven by your customers, your industry, and your growth strategy. It’s not about which framework is “better,” but which one is the right tool to help you achieve your business objectives.
For a company pursuing a SOC 2 audit, it’s critical to be able to articulate why it’s the right choice for your business when a customer asks about HITRUST. Knowing your market demands is key. According to industry data, for a deeper dive on this, check out this analysis of the core differences between HITRUST and SOC 2. This market split is what guides smart GRC decisions.
Scenario 1: The B2B SaaS Startup
Imagine a growing B2B SaaS company selling project management software. Its sales team repeatedly faces security questionnaires from larger enterprise prospects before they will even agree to a demo. These customers are in diverse industries: manufacturing, retail, and marketing.
The Right Choice: SOC 2 Type 2.
Why it Matters for a SOC 2 Pursuit: This is the classic use case for SOC 2. The company does not handle Protected Health Information (PHI), so the immense overhead and cost of HITRUST would be a misallocation of critical resources. A SOC 2 report, scoped to the Security and Availability Trust Services Criteria, directly addresses the primary concerns of a broad B2B customer base: “Is my data safe?” and “Will your service be available when I need it?” Obtaining a SOC 2 report is the most efficient way to unblock enterprise sales and demonstrate a credible security posture.
Scenario 2: The Mid-Market FinTech Platform
Consider a mid-market FinTech platform that processes sensitive financial data for other businesses. It’s not a bank, but its services are mission-critical for its customers’ financial operations, who are intensely risk-averse.
The Right Choice: SOC 2 Type 2 with Security, Availability, and Confidentiality.
Why it Matters for a SOC 2 Pursuit: In this scenario, SOC 2’s flexibility is again the key. By adding the Confidentiality TSC to the scope, the company can provide audited proof that it has controls in place to protect sensitive data from unauthorized disclosure, a primary concern for financial services clients. This tailored report answers the sophisticated due diligence questions from discerning buyers and demonstrates a mature security program, all without the healthcare-specific focus and prescriptive burden of HITRUST.
Scenario 3: The Specialized HealthTech Provider
Finally, picture a HealthTech company with a patient data analytics platform sold directly to large hospital systems. Its entire business is built on processing and analyzing massive volumes of PHI.
The Right Choice: HITRUST r2 Certification.
Why it Matters for a SOC 2 Pursuit: Even for a company on a SOC 2 path, understanding this scenario is vital. It clarifies when SOC 2 is not enough. In the U.S. healthcare ecosystem, HITRUST is often a non-negotiable contractual requirement. Knowing this allows you to strategically identify which market segments your SOC 2 report will serve and when you might need to plan for a future HITRUST project. You can confidently explain to a non-healthcare prospect why your SOC 2 report is the appropriate and sufficient standard for their needs.
These scenarios prove that choosing a framework is a strategic business decision. For a company pursuing SOC 2, it is not a “lesser” standard—it is the “right” standard for a vast range of technology companies that need to prove security efficiently. Your SOC 2 readiness journey should be guided by what your specific customers require, ensuring your compliance investment translates directly into closing more deals.
Using SOC 2 as a Stepping Stone to HITRUST
For companies with long-term ambitions in regulated markets, completing a SOC 2 audit should not be viewed as the finish line, but as a strategic starting block. The investment made in achieving your first SOC 2 report provides a powerful foundation for future compliance efforts, including a potential HITRUST certification.
There is significant control overlap between the SOC 2 framework and the HITRUST CSF. This means the policies, procedures, and evidence you develop for your SOC 2 audit are not a sunk cost; they are a reusable asset.
Completing a SOC 2 audit forces your organization to build essential “compliance muscle.” You establish repeatable processes for documenting controls, gathering evidence, managing policies, and training your team on security best practices. These operational capabilities are non-negotiable prerequisites for tackling any major compliance framework. An organization that has successfully navigated a SOC 2 audit is far better prepared to approach HITRUST than one starting from scratch.
Build Your SOC 2 Program to Win Later
To maximize the value of your SOC 2 program as a strategic asset, you must be intentional from day one. This means structuring your audit readiness with an eye toward a potential future HITRUST assessment.
Here is some actionable guidance for future-proofing your SOC 2 program:
- Centralize and Organize Evidence: Don’t just collect evidence to satisfy the immediate audit request. Implement a system (such as a compliance automation platform or a well-organized cloud drive) to meticulously organize, label, and archive all evidence. This makes mapping your existing SOC 2 controls to HITRUST requirements infinitely easier.
- Write Policies Aligned with Broader Frameworks: When drafting policies for SOC 2, reference established security principles from frameworks like the NIST Cybersecurity Framework (CSF), which heavily influences HITRUST. This ensures your foundational policies for areas like incident response (CC7.3) and change management (CC8.1) won’t require a complete rewrite later.
- Choose Scalable GRC Tools: Implement tools for access reviews, vulnerability scanning, and security awareness training that can scale with you. A manual, spreadsheet-based system that barely suffices for a SOC 2 audit will collapse under the weight and complexity of a HITRUST assessment.
Why this matters for someone pursuing SOC 2: Treating your SOC 2 program as a strategic asset, rather than a one-off project, transforms it from a cost center into a scalable investment. By being deliberate in your documentation and tool selection, you not only make your current SOC 2 audit smoother but also significantly reduce the time and cost of any future compliance initiatives, including HITRUST.
The significant overlap between the SOC 2 Trust Services Criteria and the HITRUST CSF means your SOC 2 efforts directly contribute to HITRUST readiness. Controls you implement for SOC 2’s CC6 (Logical and Physical Access Controls) and CC7 (System Operations) are foundational to similar control domains in HITRUST. This alignment means a large portion of your SOC 2 evidence can be repurposed, saving substantial time and resources. As you begin to map out your compliance roadmap, our guide on how to get SOC 2 certified can be a huge help in laying this critical groundwork.
Your Path to SOC 2 Audit Readiness
Preparing for a SOC 2 audit is the process of transforming your security posture from an abstract commitment into a documented, provable reality. It is a methodical journey of defining your system based on customer promises, systematically implementing controls to meet the applicable AICPA Trust Services Criteria, and gathering the evidence to demonstrate their effectiveness.
After comparing SOC 2 vs. HITRUST, it becomes clear that for most SaaS, FinTech, and B2B service providers, SOC 2 is the most logical, efficient, and cost-effective path to demonstrating security and satisfying enterprise vendor requirements.
Your High-Level SOC 2 Checklist
Once you’ve committed to SOC 2, the focus shifts to execution. While each audit is unique, the path to readiness follows a clear, repeatable playbook.
- Scope Your Audit: The first critical decision is selecting the right Trust Services Criteria. Security is mandatory. You must then decide if Availability, Confidentiality, Processing Integrity, or Privacy are relevant to your service commitments and customer contracts.
- Conduct a Readiness Assessment: This is an essential step where an auditor or consultant benchmarks your current controls against the selected TSCs. The output is a “gap analysis” that provides a clear roadmap of what needs to be fixed.
- Remediate Identified Gaps: This is where the core work happens. Your team will implement new controls, write and approve policies, and configure systems to close every identified gap. For example, the readiness assessment might reveal a need to formalize your incident response plan to satisfy criterion CC7.3 (Response to System Malfunctions and Incidents) or to implement a formal change management process for CC8.1 (Management of Changes).
Why this matters for someone pursuing SOC 2: By methodically addressing each gap identified in the readiness assessment, you are not just preparing for an audit; you are building a more resilient, mature security program that genuinely protects your business and your customers. This process of continuous improvement is at the heart of the SOC 2 framework. A clean SOC 2 report is the external validation of this internal commitment.
Ultimately, connecting your SOC 2 compliance efforts directly to audit readiness ensures that every action you take is purposeful and contributes to the end goal: earning an unqualified opinion from your auditor. This report serves as tangible proof to the market that your organization’s security program is not only well-designed but operates effectively, providing the assurance needed to build trust, accelerate sales, and fuel growth.
Finding the right auditor is the most critical decision you’ll make in your SOC 2 journey. At SOC2Auditors, we swap the guesswork of auditor selection for a data-driven matching platform. Get three tailored, verified auditor quotes in 24 hours and choose with confidence by visiting soc2auditors.org.