A SOC 2 Type 2 report is an independent auditor’s stamp of approval on how a company’s security controls actually performed over a specific time, usually 3-12 months. It’s the ultimate proof that your security isn’t just a policy on a shelf—it’s a living, breathing practice.
For a complete overview of SOC 2 before getting into Type 2 specifics, read What is SOC 2?.
If you’re still deciding whether a Type 1 or Type 2 is the right fit for your company, start with our SOC 2 Type 1 vs Type 2 comparison.
The Definitive Answer to What Is a SOC 2 Type 2 Report
Here’s the best analogy I’ve heard: a SOC 2 Type 1 report is like a single, perfectly staged photo of a secure house. It shows the right locks are on the doors and the alarm system is installed. All the pieces are in place.
A SOC 2 Type 2 report, however, is the continuous security camera footage from the last six months. It proves the doors were consistently locked, the alarms were always armed, and every security rule was followed day in and day out.
That distinction is everything. A Type 2 report gives your customers a much higher level of assurance because it doesn’t just look at the design of your security controls; it verifies their operational effectiveness through rigorous testing over a real-world observation window.
A Deeper Look at the Report’s Purpose
At its core, a SOC 2 Type 2 report is an auditor’s official opinion that a company’s security practices—as they relate to the AICPA’s Trust Services Criteria—are both well-designed and consistently followed. This isn’t just some niche framework; it’s the globally recognized standard for cloud and SaaS companies trying to prove they can be trusted.
The real-world benefit? A recent Type 2 report dramatically reduces sales friction. Handing it over often satisfies the most demanding enterprise security questionnaires, shortening due diligence from weeks to days. If you want to dive into the nuts and bolts, Secureframe has a solid breakdown of the SOC 2 Type 2 methodology.
Ultimately, this report is the gold standard for building client trust. It’s the definitive answer to the questions every potential customer is asking:
- Can I really trust you with my sensitive data?
- Are your security promises just marketing fluff, or are they backed by consistent action?
- Do you have the discipline and processes to protect my information for the long haul?
An unqualified opinion in a Type 2 report is a powerful, third-party “yes” to all three.
Why SOC 2 Type 2 Has Become a Business Imperative
The demand for this level of assurance has exploded. Market adoption of SOC 2 certification jumped by a staggering 40% in just one year, and over 60% of businesses now say they are more likely to partner with a certified provider. A full 78% of enterprise clients now specifically require SOC 2 Type 2 from their vendors, cementing its status as a must-have credential for any B2B SaaS company serious about growth.
The threat landscape makes this even more urgent. In 2024, cyberattacks caused global damages topping $6 trillion, a number that’s expected to keep climbing. For companies handling sensitive data, SOC 2 Type 2 isn’t just a nice-to-have; it’s an essential shield that proves your controls work in the real world, not just on paper.
Getting certified has a direct impact on your bottom line:
- Reduce Sales Friction: It preemptively answers the tough security questions from enterprise procurement teams, which can dramatically shorten your sales cycles.
- Unlock Larger Deals: Many large corporations won’t even consider a vendor without a valid SOC 2 Type 2 report on file. It’s a key that opens bigger doors.
- Build Demonstrable Trust: It provides objective, third-party validation of your security commitment, giving you a powerful competitive edge.
SOC 2 Type 2 Report At a Glance
To boil it all down, here’s a quick summary of the key attributes of a SOC 2 Type 2 report. This table highlights what it covers, who it’s for, and why it matters in the real world.
| Attribute | Description |
|---|---|
| Primary Focus | Tests the operational effectiveness of security controls over a period of time (e.g., 6-12 months). |
| Key Question Answered | Do your security controls actually work as intended on a consistent, ongoing basis? |
| Intended Audience | Customers, partners, and stakeholders who need deep assurance about a vendor’s security posture. |
| Business Purpose | To build trust, satisfy enterprise vendor requirements, and accelerate sales cycles by proving security maturity. |
This table makes it clear: a Type 2 report isn’t just about checking a box. It’s a strategic asset for any company serious about earning and keeping customer trust.
Comparing SOC 2 Type 1 and Type 2 Reports

While they sound almost identical, the difference between a SOC 2 Type 1 and a Type 2 report is massive. Getting this wrong means you won’t understand the level of assurance a vendor is actually giving you. It’s the classic difference between a promise and real proof.
Here’s an analogy: think of building a high-security bank vault.
A SOC 2 Type 1 report is like getting an architect to approve your blueprints. The auditor looks at the design of your security controls at a single moment—a “point in time”—and confirms that, on paper, they look solid enough to meet the criteria. It’s a snapshot.
A SOC 2 Type 2 report is like hiring a security team to monitor that vault for an entire year. They don’t just glance at the blueprints; they watch the guards, test the locks daily, and review months of camera footage to prove the vault was never breached. The auditor tests the operational effectiveness of your controls over a sustained period, usually 3 to 12 months.
This is why a search for what is a SOC 2 Type 2 report always circles back to the idea of ongoing proof. It provides hard evidence that your security isn’t just a theory but a day-in, day-out operational reality.
The Point-in-Time Snapshot
A Type 1 report absolutely has its place. It’s a fantastic first step for a company just starting its compliance journey. Many use it as a “readiness assessment” to validate their control design before tackling the more intense Type 2. It’s also faster and cheaper to get.
But its limitation is a big one. It tells you nothing about whether those well-designed controls actually worked yesterday, are working today, or will work tomorrow. A lot can happen after the photo is taken.
The Continuous Security Story
A Type 2 report tells a story over time. An auditor doesn’t just ask, “Do you have a firewall?” They collect evidence to prove that the firewall was properly configured and running without any sketchy changes throughout the entire audit period.
This is exactly why sophisticated customers—especially mid-market and enterprise clients—almost always demand a Type 2. They need to know your security practices are consistent and reliable, not just well-documented for one day of the year.
A Type 1 report shows you have a plan. A Type 2 report proves your plan actually works under real-world conditions, day after day. This distinction is the bedrock of trust in any vendor relationship.
Key Differences Between SOC 2 Type 1 and Type 2 Reports
To make this crystal clear, let’s put them side-by-side. This table breaks down the core differences across the factors that really matter when you’re evaluating a vendor’s security program.
| Factor | SOC 2 Type 1 | SOC 2 Type 2 |
|---|---|---|
| Audit Focus | Design Suitability of controls at a single point in time. | Operational Effectiveness of controls over a period of time. |
| Evidence | Primarily based on documentation, policies, and system descriptions. | Requires extensive evidence of controls operating, like logs and records. |
| Timeline | Faster to complete, as it only covers a specific date. | Longer process, requiring an observation period of 3-12 months. |
| Assurance Level | Provides moderate assurance that controls are designed correctly. | Provides high assurance that controls are designed and working effectively. |
| Best For | Early-stage companies proving initial compliance or internal readiness. | Companies selling to enterprise clients who require proof of ongoing security. |
In the end, while a Type 1 report is a respectable start, the SOC 2 Type 2 report is the true industry standard for showing you have a mature and trustworthy security program. It’s the document that unlocks bigger deals and builds lasting customer confidence.
Breaking Down the Five Trust Services Criteria
At the core of every SOC 2 report are the Trust Services Criteria (TSC). These are five principles the AICPA created to evaluate how a company protects customer data. Think of them like the subjects in your high school curriculum: you have to pass the mandatory classes, but you also pick electives based on what you want to specialize in.
This structure is what makes SOC 2 so practical. It’s not a rigid, one-size-fits-all checklist. Instead, it’s a flexible framework that lets you prove your security where it matters most to your customers.
Each criterion gives an auditor a specific lens to look through when they examine your controls, ensuring the final report is both comprehensive and relevant to the promises you make. A modern SOC 2 Type 2 report typically covers 60-150 control points across the selected criteria, with Availability appearing in 75.3% of reports and Confidentiality in 64.4%.
The Mandatory Foundation: Security
The Security criterion is the non-negotiable foundation of every single SOC 2 audit. You can’t get a report without it. It’s often called the “Common Criteria” for this reason. It answers the fundamental question: is your system protected against unauthorized access, use, or modification?
Think of it as the basic security for your house. It covers the essentials everyone expects:
- Access Controls: This is like having strong locks on your doors and windows, making sure only authorized people can get in. This includes both logical access to systems and physical access to data centers.
- Firewalls and Intrusion Detection: This is your fence, gate, and alarm system—creating a strong barrier between your private network and the public internet, and alerting you to anything suspicious.
- Two-Factor Authentication (2FA): A non-negotiable layer to prevent stolen credentials from causing a breach.
- Vulnerability Management: Your process for proactively finding and patching security holes before they get exploited.
- Change Management: Your formal process for pushing changes to production systems. Auditors want to see that you’re not introducing new security holes through uncontrolled code deployments.
- System Operations Monitoring: How you monitor your infrastructure for anomalous behavior and what happens when you detect an incident.
These controls are universal because they form the bedrock of any trustworthy service. Without a solid security foundation, the other criteria are pretty much meaningless.
Choosing Your Additional Criteria
Beyond Security, you get to choose which other TSCs to include based on your business and the commitments you’ve made to customers. This is where you tailor the audit to tell the right story.
For a deeper dive on this, check out our detailed guide on the SOC 2 Trust Services Criteria in our detailed guide.
Let’s break down the other four criteria with some real-world examples.
-
Availability: This one is for services that promise serious uptime. If your SLA promises 99.9% uptime or better, this criterion is non-negotiable. The audit focuses on whether your system is available for use as you’ve agreed. A cloud provider like AWS or a critical tool like Slack would absolutely include Availability to prove they have solid disaster recovery plans, performance monitoring, and incident response procedures in place. Auditors will want to see tested disaster recovery plans, live monitoring dashboards, and proof of backup and redundancy systems.
-
Processing Integrity: This is crucial for any platform that performs calculations or handles transactions. It looks at whether your system processing is complete, valid, accurate, and timely. A fintech app processing payments or a payroll platform calculating employee wages needs this to prove every calculation is perfect. Auditors scrutinize data input validation, output checks, QA procedures, and error correction workflows.
-
Confidentiality: This criterion is all about protecting information that has been specifically designated as confidential. If your service handles intellectual property, sensitive M&A documents, or legal contracts, you’ll need this one. A virtual data room service used during mergers and acquisitions is a perfect candidate—its entire purpose is safeguarding highly sensitive corporate documents. Key controls include data encryption both at rest and in transit, strict access policies based on the principle of least privilege, Non-Disclosure Agreements (NDAs), and secure data disposal methods to ensure deleted data is truly gone.
-
Privacy: While it sounds a lot like Confidentiality, Privacy is laser-focused on Personally Identifiable Information (PII). It covers how PII is collected, used, retained, and destroyed. The controls for Privacy are heavily influenced by frameworks like GDPR and CCPA, focusing on the clarity of your privacy notices, your process for honoring user data requests, and your data retention policies. Any company handling customer health records, social security numbers, or other personal data—like a HealthTech platform—must include the Privacy criteria.
Picking the right TSCs is a strategic decision. Adding criteria you don’t need wastes time and money. But leaving out one that your customers expect can make your report look weak. Your choices should directly mirror the promises you make in your contracts and marketing.
How to Actually Read a SOC 2 Type 2 Report
Getting a 100-page SOC 2 Type 2 report from a vendor can feel like homework. It’s dense, technical, and looks like it was written by auditors, for auditors. But you don’t need to be a security guru to pull out the critical information you need to make a smart risk decision.
The secret is knowing where to look and what to look for. The most important stuff isn’t buried on page 73; it’s right up front. Learning to decipher this document lets you move beyond the cover page and truly vet a vendor’s security posture against your own standards.
Start with the Auditor’s Opinion
Before you touch anything else, flip to Section 1: The Independent Auditor’s Report. This is where the CPA firm gives its official verdict on the vendor’s controls. Think of it as the executive summary for the entire report.
You’re hunting for one key phrase: an unqualified opinion. This is the best possible outcome. It means the auditor found that the vendor described their system fairly and their controls were designed properly and actually worked throughout the entire audit period. It’s a clean bill of health.
Anything else is a potential red flag:
- Qualified Opinion: This means the auditor found issues with one or more specific controls, but the rest of the report is fine. It’s a “mostly good, but…” verdict that demands you dig deeper into what went wrong.
- Adverse Opinion: This is a huge deal. It means the auditor found significant, widespread problems and believes the vendor’s controls are fundamentally ineffective. Walk away.
- Disclaimer of Opinion: Also a massive red flag. This means the auditor couldn’t even gather enough evidence to form an opinion, which usually points to a total lack of cooperation or abysmal record-keeping.
Hunt for Exceptions and Scope Limitations
After checking the opinion, your next stop is the section detailing the auditor’s tests and results. Here, you’re looking for exceptions. An exception is a documented instance where a control failed when the auditor tested it.
A few minor exceptions might be okay, especially if the vendor has a solid explanation and a plan to fix them. But a long list of exceptions—or repeated failures in critical areas like access control or change management—points to a weak security culture.
You also need to scrutinize the audit’s scope. Did the vendor conveniently leave a critical part of their service out of the audit? For example, if your team relies on their mobile app but the SOC 2 only covers their web platform, you’ve got a massive blind spot. A suspiciously narrow scope can be a clever way to hide weaknesses.
Understand Your Responsibilities with CUECs
One of the most overlooked parts of a SOC 2 report is the section on Complementary User Entity Controls (CUECs). These are the security tasks the vendor explicitly says are your job, not theirs.
Think of CUECs as the security instructions that come with a new product. If a vendor says, “You are responsible for enforcing strong user passwords,” and you don’t, then any breach from a weak password is on you—even if their SOC 2 report is perfect.
Ignoring these is a common and costly mistake. For a hands-on look at where these elements appear and how they are presented in a real-world document, you can review a SOC 2 report example here.
The business impact of getting this right is immense. With the average cost of a data breach hovering around $4.44 million, proper vendor due diligence isn’t just a checkbox item. It’s why buyers treat Type 2 reports as essential proof of a vendor’s commitment, with 96% of organizations in some studies citing it as the dominant standard for security assurance.
Check Management’s Assertion and the System Description
Right after the auditor’s opinion, look for Management’s Assertion—a formal statement from the vendor’s leadership confirming that the system description is accurate and that the controls they claim to have were in place and working. It’s the company’s own official stamp on the report.
The System Description that follows sets the context for everything else. It describes the vendor’s services, infrastructure, software, and the people and processes that keep things secure. This is where you confirm the boundaries of what was actually audited. A suspiciously narrow system description can be just as revealing as a list of exceptions.
The Control Tests and Results
The bulk of the report is a detailed table listing every control the auditor tested. For each one, you’ll see three things: a short description of the control itself (e.g., “New user access is formally approved before being granted”), a summary of how the auditor tested it (e.g., “Inspected a sample of 25 new hire access request tickets to verify manager approval”), and a clear statement on whether it passed. Any failures are called exceptions and are documented right there. A few minor exceptions with solid management responses are usually fine. A pattern of failures—especially in access control or change management—is not.
This decision tree shows how companies typically select the Trust Services Criteria that form the basis of their audit, starting with the mandatory Security criterion.
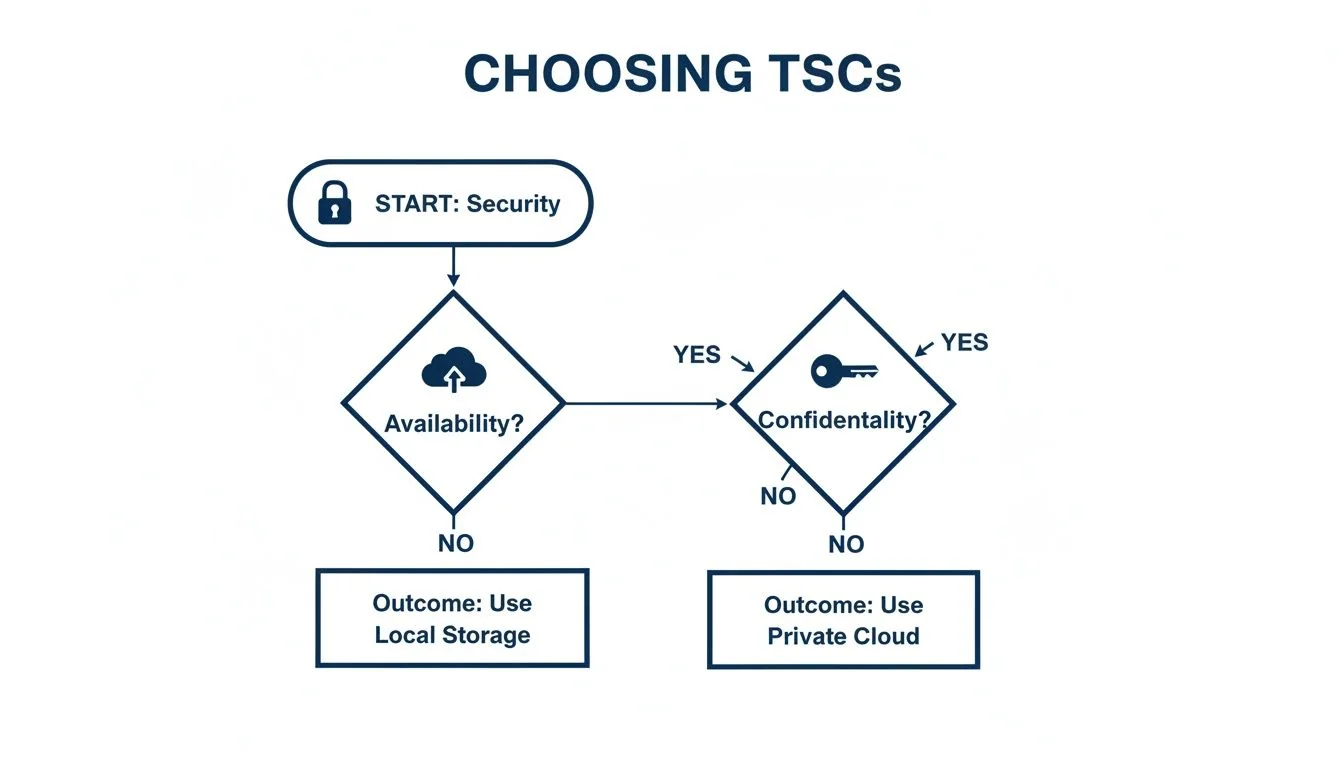
The flowchart makes it clear: after meeting the foundational Security requirements, a company’s choices for additional criteria like Availability or Confidentiality are driven entirely by the specific services they offer and the promises they make to their customers.
Planning Your Journey to a SOC 2 Type 2 Report
Getting a SOC 2 Type 2 report is a serious commitment, not a weekend project. The single most important thing you can do for a successful audit is to map out the entire journey—the timeline, the real costs, and the internal effort required. I’ve seen too many companies dive in without a clear plan, only to face painful delays and budget overruns.
This process is a marathon, not a sprint. It starts long before your auditor ever begins testing, with a critical readiness and remediation phase. This is where you roll up your sleeves, find the gaps in your controls, and implement the necessary fixes. This prep work alone can take several months of focused effort from your team.
Only after your controls are humming along does the clock start on the observation period. This is the 6 to 12-month window where your controls have to be working consistently for the auditor to test them. Rushing this step is a classic mistake that almost guarantees a qualified report or, worse, a failed audit.
Deconstructing the Timeline from Start to Finish
A realistic timeline for a first-time SOC 2 Type 2 report usually lands somewhere between 9 and 15 months. It’s a multi-stage process where each phase builds on the last. Don’t let anyone sell you on the idea that it can be done in a few weeks—that’s just not how a real Type 2 engagement works.
Here’s what the journey typically looks like:
- Readiness and Gap Analysis (2-6 weeks for assessment, 1-6 months for remediation): This is where you start with a gap analysis to see where you stand. Your team will spend this time writing policies, tweaking system configurations, deploying new tools (endpoint detection, vulnerability scanning, security awareness training), and training staff to close those gaps. A thorough readiness assessment is your audit’s early warning system—it gives you the chance to fix problems on your own timeline, not under the pressure of an active audit.
- Observation Period (6-12 months): Once your controls are in place, the formal audit window opens. During this stretch, you have to live and breathe your new policies and gather the evidence that proves your controls are working day in and day out.
- Audit Fieldwork and Reporting (4-8 weeks): After the observation period closes, the auditor steps in to do their thing. They’ll request evidence, interview your team, and perform their tests before writing up their final report and official opinion.
The total timeline is a huge planning factor, usually taking 9-12 months for most companies. Modern compliance automation can seriously compress the prep phase; some startups use these platforms to get audit-ready in as little as 2 weeks. For first-timers doing it manually, expect prep alone to take 3-6 months.
Defining Your Audit Scope
Before you touch a single policy or start hunting for evidence, define the boundaries of your audit. This is the single most important first step. Scope creep is the number one reason timelines and budgets blow up. Ask yourself three questions:
- Which Trust Services Criteria do we actually need? Security is mandatory. Only add Availability, Confidentiality, Processing Integrity, or Privacy if you have specific contractual promises to customers that require them—not because they sound impressive.
- What systems are in scope? Map your production environment: databases, apps, core infrastructure. Keep development and testing environments out of scope unless they touch real customer data.
- Who are the key people? Pinpoint the engineering, DevOps, and security team members responsible for managing and securing the in-scope systems. They will own most of the evidence collection.
Running a Gap Analysis Before You Start
A gap analysis is your secret weapon. It’s essentially a dry run where you compare your current controls against the SOC 2 requirements for your chosen criteria—before the real audit observation period kicks off. Think of it as turning a pile of unknown risks into a manageable action plan.
For example, you might discover you don’t have a formal process for de-provisioning employee access when they leave. That’s a critical gap. Finding it during a gap analysis gives you the runway to build the process, document it, and get it operating consistently—before the auditor starts watching. For more detail, check out our guide on the SOC 2 readiness assessment.
Remediating Gaps and Collecting Evidence
Once you have your punch list from the gap analysis, remediation begins. This is the longest stretch of prep work. Typical activities include:
- Writing and Formalizing Policies: Creating clear, written policies for everything from access control and vendor management to incident response.
- Implementing New Tools: Deploying software for endpoint detection, vulnerability scanning, or security awareness training.
- Configuring System Settings: Hardening servers, enforcing strong password policies across all systems, and making sure your logging and monitoring are up to snuff.
- Training Your Team: Making sure every single employee understands their security responsibilities and actually follows the new procedures.
As you fix each control, start gathering proof immediately. A Type 2 audit requires a steady stream of logs, screenshots, meeting minutes, and signed documents from your entire observation period.
The real challenge isn’t just having the controls. It’s proving they were actually working on a random Tuesday three months ago. Without automation, this turns into a frantic scramble that’s begging for human error and missed evidence.
Compliance automation platforms like Vanta, Drata, or Secureframe are worth serious consideration here. They plug into your cloud environment and other apps to pull evidence automatically—turning a grueling manual process into a continuous, low-error workflow. The time savings alone justify the cost for most teams.
Understanding the True Cost of an Audit
The cost of a SOC 2 report is much more than just the auditor’s invoice. While the audit fees themselves can range from $7,000 to over $100,000, the total investment is significantly higher when you add up all the pieces. For most small to mid-sized companies, the all-in cost—including readiness, tools, and internal time—is usually between $30,000 and $150,000. The global market for these services is projected to hit nearly $10.5 billion by 2030, which shows just how much demand there is for this level of security assurance.
Your budget has to account for more than just the final report. The real investment is in building a sustainable compliance program. That includes tooling, expert guidance, and your team’s most valuable resource: their time.
The most common “hidden” costs to watch out for are:
- Compliance Automation Tools: Platforms that help manage evidence collection and keep an eye on your controls. Expect to pay $5,000 to $60,000+ a year depending on company size, employee count, and platform features. The hundreds of hours they save in manual labor make them a no-brainer for most teams.
- Readiness Consultants: Bringing in an expert to guide you through the prep work can save a ton of time and prevent expensive mistakes down the road. Budget $10,000 to $50,000+ depending on how much hand-holding you need.
- Penetration Testing: While not technically mandatory, most auditors expect a recent pen test to satisfy the Security criterion. Budget $5,000 to $25,000 depending on environment complexity.
- Legal and Consulting Fees: Legal review of policies or specialized consultants for complex controls can run $5,000 to $50,000.
- Internal Staff Time: Getting ready for an audit often requires 200-600+ hours from your engineering and leadership teams. Research shows 62% of small and mid-sized companies struggle with the requirements precisely because they underestimate this commitment.
For a comprehensive breakdown of what to expect, check out our detailed guide on the SOC 2 Type 2 audit cost. Getting on the same page about time and money from the very beginning is the key to setting your company up for a smooth and successful audit.
Total Cost Breakdown by Company Size
The numbers below give you a realistic picture of what the first-year investment looks like end to end—not just the auditor’s invoice, but everything that goes into getting a clean Type 2 report.
| Cost Component | Small Startup (1-50 Employees) | Mid-Market Company (51-250 Employees) |
|---|---|---|
| Readiness Assessment | $5,000 - $15,000 | $10,000 - $25,000 |
| Audit Fees (CPA Firm) | $15,000 - $35,000 | $30,000 - $75,000 |
| Compliance Automation Tool | $5,000 - $15,000 / year | $12,000 - $30,000 / year |
| Penetration Test (Often Required) | $5,000 - $15,000 | $10,000 - $25,000 |
| Legal and Consulting | $5,000 - $15,000 | $10,000 - $50,000 |
| Internal Team Time | 200-400 hours | 400-800+ hours |
| Ongoing Maintenance (Annual) | 15-20% of initial cost | 15-20% of initial cost |
| Estimated Total First-Year Cost | $30,000 - $80,000+ | $62,000 - $155,000+ |
Data shows total first-year costs for companies under 50 employees average around $91,000, jumping to $186,000 for businesses with 50-250 people—when you factor in the full cost of internal team hours and productivity impact.
The market data underlines why this investment is worth it. Only 7% of pre-seed and seed startups have a SOC 2 Type 2 report, but that number jumps to 45% for companies with over $100M in funding. SOC 2 adoptions surged 40% in 2024 alone, and the global SOC reporting services market hit USD 5.4 billion in 2024—projected to nearly double by 2030. The demand for this level of proof is only accelerating.
Choosing the Right Auditor: Boutique vs Big Four
Picking an auditor is one of the most consequential decisions in the process. The choice between a smaller, specialized boutique firm and a Big Four name (Deloitte, PwC, EY, KPMG) has real implications for cost, speed, and the quality of guidance you’ll get.
Boutique audit firms tend to offer more hands-on support from senior partners, greater flexibility on timeline, and pricing that’s friendlier to startup and growth-stage budgets. They often specialize in SaaS and tech, which means they understand your environment without you having to explain it.
Big Four firms bring unmatched brand recognition—some enterprise customers and investors weigh a Big Four name heavily—plus deep resources for audits of significant scale and complexity, and global reach for multinational operations.
For most startups and growth-stage companies, a specialized boutique firm strikes the right balance of cost, speed, and expert support. The goal is a partner, not just a processor—someone who feels like an extension of your team and helps you build a stronger security posture, not just a report.
Key Questions to Ask Potential Auditors
Before you sign any engagement letter, put potential auditors through their paces. Their answers will tell you everything you need to know about fit:
- Industry Experience: “How many audits have you done for companies in our specific industry—like FinTech or SaaS—and at our current size?” You need someone who has seen this movie before.
- The Process: “Walk me through your entire audit process, from the first call to the final report. What’s your communication like, and what’s a realistic response time?”
- Your Team: “Who is actually going to be on our engagement team? What are their qualifications?” Make sure you won’t be handed off to junior staff after signing the contract.
- The Final Product: “Can we see a redacted sample report? We want to know how you present findings.” A clean, easy-to-read report is a sales tool in itself.
- Tools and Tech: “What platforms do you use for evidence collection? Do you have experience with compliance automation tools like Vanta or Drata?”
A great auditor doesn’t just point out problems; they give you context and practical advice. Their job is to help you genuinely improve your security, not just tick items off a checklist. Look for a firm that wants to add real value to your business.
Common Pitfalls That Derail a SOC 2 Type 2 Audit
Even well-prepared companies stumble on these recurring mistakes. Knowing them upfront can save you months of delays and thousands in wasted spend.
1. Poor Scoping and Scope Creep. The most expensive mistake is including systems or Trust Services Criteria you don’t actually need. Every additional criterion increases the audit workload—and your bill. Start with Security (mandatory) and only add criteria that map directly to customer contractual commitments. Before the observation period begins, create a definitive scope document that becomes your North Star.
2. Underestimating Evidence Collection. Teams are often blindsided by the sheer volume of proof a Type 2 audit requires. This isn’t a one-time document drop—it’s months of continuous evidence gathering. Research shows 550-600 internal hours is typical for a first-time audit at a small to mid-sized company. Without automation, this becomes a frantic scramble that pulls your best engineers off their real work.
3. Treating Compliance as a One-Time Project. A SOC 2 Type 2 report expires after 12 months. Companies that treat the first audit as a sprint often find themselves scrambling again the following year. In fact, 58% of organizations expect to conduct four or more compliance audits annually. Build compliance into your daily operations from day one—it’s dramatically cheaper to maintain than to rebuild.
4. Lacking Executive Buy-In. When leadership views SOC 2 as a cost center rather than a business enabler, resource allocation suffers. Frame it in terms of revenue: 42% of enterprise firms mandate SOC 2 before signing a contract. Don’t talk about controls—talk about how it unblocks enterprise deals, shortens sales cycles, and builds a moat around your business. Come prepared with a clear budget and timeline to change the conversation from a technical chore into a strategic investment.
5. Rushing the Observation Period. While the AICPA allows a minimum 3-month observation window, going shorter than 6 months raises questions from sophisticated buyers. A rushed observation period also means less time for your team to find and fix control failures before the auditor documents them as exceptions.
Your Burning SOC 2 Questions, Answered
Even after you get the basics down, the finer points of a SOC 2 report can be tricky. Let’s tackle the most common questions we hear from companies navigating compliance for the first time.
How Long Is a SOC 2 Type 2 Report Good For?
A SOC 2 Type 2 report is generally considered valid for twelve months from the day it’s issued. Once it hits the one-year mark, it’s officially “stale,” and its power to assure prospects about your current security posture drops off a cliff.
This is why annual audits are the industry standard. Your customers, especially the big ones, want to see proof of an ongoing commitment to security—not a snapshot of what your controls looked like over a year ago. Consistent, yearly audits signal that your security program is a living, breathing process, not a one-time project.
Can You Fail a SOC 2 Audit?
Technically, you don’t “pass” or “fail” a SOC 2 audit. It’s not a test with a score. Instead, the auditor issues a professional opinion on how well your controls are designed and operating:
- Unqualified Opinion: This is the gold standard. It means your controls are effective, with no significant issues found. It’s the clean bill of health you’re aiming for.
- Qualified Opinion: This means the auditor found one or more issues or exceptions. It’s not a total failure, but it flags areas for improvement that your customers will notice and ask about.
- Adverse Opinion: This signals significant, material problems with your security controls. It’s the one you absolutely want to avoid.
The best way to lock in that coveted unqualified opinion? A thorough readiness assessment that finds and fixes problems before the auditor does.
What Happens If the Auditor Finds an Issue?
Don’t panic. Finding an “exception” or two during an audit is incredibly common and doesn’t mean you’ve failed. What matters is how you respond.
The auditor will note the issue in the report, and right next to it, there will be a section for your management team’s response. This is your chance to show you’re on top of things: explain what happened, what the actual impact was (or wasn’t), and most importantly, describe the exact steps you’ve already taken to fix it. A report with a few minor, well-handled exceptions can actually signal a mature and transparent security program.
Is a Penetration Test Required for a SOC 2 Audit?
While the official AICPA guidance doesn’t explicitly mandate a penetration test, it’s pretty much a non-negotiable best practice. To satisfy the mandatory Security criterion, you have to show you’re actively finding and fixing vulnerabilities. A recent pen test is the single best piece of evidence for this. Most auditors will expect to see one, especially if you’re handling any kind of sensitive customer data. It’s powerful, independent proof that you’re proactively trying to break your own systems before attackers do.
Can We Get a SOC 2 Type 2 Report in Less Than 6 Months?
Technically yes, but it’s rarely advisable. The AICPA allows a minimum 3-month observation window, but enterprise buyers view shorter periods skeptically. A 3-month Type 2 often triggers the same follow-up questions that a Type 1 would, defeating the purpose of the longer engagement. If you’re in a genuine time crunch, consider a Type 1 as a bridge while you build toward a full 6-12 month Type 2 observation period.
Is Compliance Automation Software Required?
While it’s not officially mandatory, using compliance automation software has become the standard for a reason. Trying to manage a SOC 2 audit manually with spreadsheets and shared drives is a recipe for headaches and costly mistakes. Platforms like Vanta, Drata, or Secureframe automate evidence collection, centralize policy management, and continuously monitor your controls. They can cut the manual evidence-gathering workload by as much as 80%, saving hundreds of hours and slashing the risk of human error.
How Is SOC 2 Different from ISO 27001?
While they’re both heavy hitters in information security, SOC 2 and ISO 27001 have fundamentally different philosophies and goals.
- SOC 2 is an attestation report, performed by a CPA firm, that digs into the nitty-gritty of your security controls against the AICPA’s Trust Services Criteria. It’s the go-to framework in North America for proving your controls are designed well and actually work over time.
- ISO 27001 is a certification. It validates that your organization has implemented a comprehensive Information Security Management System (ISMS). It’s more globally recognized and focuses on your overall risk management process rather than testing hundreds of individual controls.
Think of it this way: ISO 27001 certifies your system for managing security, while a SOC 2 Type 2 report attests to the actual performance of your security controls.
Does Every SaaS Company Need a SOC 2 Report?
Not every startup needs a SOC 2 report on day one. But it quickly becomes a non-negotiable ticket to play as you start selling to bigger customers. In the early days, you can probably get by with security questionnaires, but that strategy simply doesn’t scale.
The second you start targeting mid-market or enterprise clients, a SOC 2 Type 2 report transforms from a “nice-to-have” into a critical sales asset. These customers won’t gamble their data on a vendor without independent proof of security. For many, not having a report is an immediate deal-breaker, making it one of the most essential investments you can make for growth.
Finding the right auditor is the most critical step in your SOC 2 journey. At SOC2Auditors, we replace endless sales calls with a data-driven matching process. Get transparent pricing, timelines, and verified reviews to choose the perfect audit firm for your company with confidence. Find your ideal SOC 2 auditor at https://soc2auditors.org.