The Health Insurance Portability and Accountability Act (HIPAA) is a United States federal law that establishes national standards for the protection of individuals’ medical records and other identifiable health information, referred to as Protected Health Information (PHI). It applies to U.S. health plans, health care clearinghouses, and health care providers that conduct certain health care transactions electronically (Covered Entities), as well as their Business Associates who create, receive, maintain, or transmit PHI on their behalf. HIPAA has no direct legal jurisdiction within Canada; its requirements become applicable to Canadian organizations contractually, typically through a Business Associate Agreement (BAA) when handling the PHI of U.S. residents.
How HIPAA’s Rules Cross the Border into Canada

The Health Insurance Portability and Accountability Act (HIPAA) is strictly an American federal law. If a Canadian company exclusively serves Canadian clients and only handles Canadian data, HIPAA does not apply. However, the moment a Canadian software or service provider processes, stores, or transmits the Protected Health Information (PHI) of U.S. patients on behalf of an American client—a “Covered Entity” under HIPAA—the rules cross the border. The U.S. client cannot legally share PHI without a contractual guarantee that the data will be protected according to U.S. standards.
This is accomplished via a Business Associate Agreement (BAA), a mandatory contract under U.S. law. By signing a BAA, a Canadian company becomes a “Business Associate” and is contractually obligated to comply with specific provisions of the HIPAA Security, Privacy, and Breach Notification Rules. For a Canadian company pursuing SOC 2 compliance, this is critical. The BAA turns abstract U.S. legal requirements into specific, auditable control objectives. The security measures mandated by the HIPAA Security Rule—such as risk analysis, access controls, and incident response—directly align with the AICPA Trust Services Criteria for Security (the Common Criteria). A SOC 2 audit provides the ideal mechanism to demonstrate to U.S. clients that you are meeting your contractual BAA obligations, as an independent auditor is verifying the design and operating effectiveness of those very controls. For a deeper dive into HIPAA’s requirements, a practical guide to HIPAA compliance can be a valuable resource.
The Business Associate Agreement: Your Contractual Link to HIPAA
The BAA is the legal instrument that extends HIPAA’s data protection obligations into Canada. It is not optional. Signing it means making a binding commitment to implement specific safeguards to American standards.
Failure to meet these BAA obligations can lead to severe consequences:
- Contractual Liability: If a data breach originates from your systems, the U.S. client can hold you financially responsible for fines, which can be substantial.
- Contract Termination: Non-compliance with the BAA is a material breach of contract, often leading to immediate termination and loss of revenue.
- Reputational Damage: A security incident involving U.S. PHI will mark your company as a high-risk vendor, deterring future American customers.
For a company undergoing a SOC 2 audit, the BAA serves as a primary input for defining the scope of the examination. Your SOC 2 report must provide assurance that your control environment effectively mitigates the risks associated with handling PHI as defined in the BAA. For example, the HIPAA Security Rule’s requirement for a security risk analysis (§164.308(a)(1)(ii)(A)) directly maps to SOC 2 Common Criteria CC3.2, which requires the entity to identify risks. Demonstrating this during your audit is non-negotiable for proving to U.S. clients that you are a secure and trustworthy partner.
Understanding Canada’s Data Privacy Maze
Canada’s data privacy landscape is a complex mix of federal and provincial laws, unlike the U.S. which has a single federal law for health privacy. A Canadian company handling U.S. health data must comply with both HIPAA (via the BAA) and all applicable Canadian privacy regulations.
This dual-compliance obligation is a key consideration for anyone pursuing SOC 2. It matters because a SOC 2 audit requires you to demonstrate that your control environment meets your “system commitments.” These commitments include not just service level agreements, but also all applicable laws and regulations. An auditor will expect to see controls designed to meet the strictest standard, whether it originates from HIPAA, PIPEDA, or a provincial act. A generic set of controls will not suffice; your system must be able to identify the data’s origin and apply the correct legal framework.
The Federal Baseline: PIPEDA
Canada’s primary federal privacy law for the private sector is the Personal Information Protection and Electronic Documents Act (PIPEDA). It establishes rules for how organizations collect, use, and disclose personal information, including health information, during commercial activities.
However, PIPEDA allows provinces to enact their own “substantially similar” privacy laws, which then take precedence. For a SOC 2 audit, this means your controls related to privacy principles—like notice, consent, and access—must be adaptable. For instance, your control activities for P3.1 (Notice and Communication of Privacy Practices) under the SOC 2 Privacy criteria must show that you can provide different privacy notices depending on whether the data subject is in a PIPEDA-governed province or one with its own specific law.
It’s crucial to understand the legislative differences. Canada lacks a direct equivalent to the U.S. HIPAA (1996), which standardized health data protection nationally. Instead, Canada relies on a combination of laws. The federal PIPEDA (2000) provides a baseline, but specific provincial acts like Ontario’s Personal Health Information Protection Act (PHIPA) (2004) impose stricter rules on “Health Information Custodians” (HICs), similar to how HIPAA governs “Covered Entities.” You can explore more about how Canadian and US healthcare privacy laws compare for additional context.
Stricter Provincial Health Laws
Provinces such as Ontario, Alberta, and British Columbia have enacted their own health-specific privacy legislation that is often more stringent than PIPEDA.
Two critical examples are:
- Ontario’s Personal Health Information Protection Act (PHIPA): This act imposes strict rules on “Health Information Custodians” (HICs) and their agents (which would be your company if you provide services to them). PHIPA’s requirements for express consent and data handling are significantly more rigorous than PIPEDA’s.
- Alberta’s Health Information Act (HIA): Similar to PHIPA, the HIA outlines detailed rules for custodians managing health information, including specific requirements for security safeguards and breach reporting.
For a company pursuing SOC 2, this legal fragmentation is a direct challenge to your control environment. An auditor will probe your processes to ensure you can distinguish between different data types and apply the correct rules. For example, if you process PHI from both a U.S. client (under HIPAA) and an Ontario hospital (under PHIPA), your entire system must be capable of operating at PHIPA’s stricter level. This directly impacts SOC 2 controls under the Privacy criteria, such as P6.1, which requires the entity to collect information in accordance with its stated privacy notice and for the purposes identified in that notice. Your system must demonstrate it can enforce the more granular purpose limitations required by PHIPA, not just the broader uses permitted by HIPAA.
HIPAA vs PIPEDA vs PHIPA Key Differences
| Compliance Area | HIPAA (U.S.) | PIPEDA (Canada-Federal) | PHIPA (Ontario) |
|---|---|---|---|
| Primary Scope | Protected Health Information (PHI) held by Covered Entities & Business Associates. | Personal Information in commercial activities by private-sector orgs. | Personal Health Information (PHI) held by Health Information Custodians (HICs) & their agents. |
| Consent Model | Implied consent is often sufficient for Treatment, Payment, & Operations (TPO). | Requires consent, which can be express or implied depending on the sensitivity of the data. | Requires express consent for most disclosures, with specific and limited exceptions. Generally stricter than HIPAA. |
| Data Subject Rights | Right of access, amendment, and accounting of disclosures. | Right of access and correction to one’s personal information. | Robust rights of access and correction; right to “lock box” parts of their health record. |
| Breach Notification | Mandatory notification to individuals and HHS for breaches affecting 500+ people within 60 days; annual reporting for smaller breaches. | Mandatory notification to individuals and the Privacy Commissioner if there is a “real risk of significant harm.” | Mandatory notification to individuals and the Information and Privacy Commissioner of Ontario (IPC). |
| Key Enforcement Body | Office for Civil Rights (OCR) within the Dept. of Health and Human Services (HHS). | Office of the Privacy Commissioner of Canada (OPC). | Information and Privacy Commissioner of Ontario (IPC). |
Consent Models and Patient Rights
A significant compliance challenge for Canadian companies is the difference in patient consent models. Under HIPAA, U.S. covered entities can use or disclose PHI for treatment, payment, and healthcare operations (TPO) with implied consent. This is a foundational principle that allows the U.S. healthcare system to function efficiently.
This matters for a SOC 2 audit because your systems must be designed to accommodate multiple, conflicting consent models. If your platform only supports HIPAA’s implied consent model, it will be non-compliant with Canadian law and fail to meet the requirements of the SOC 2 Privacy criteria if you handle Canadian data. Your system must demonstrate the technical capability to enforce the specific consent rules applicable to each piece of data it processes.
The Canadian Consent Standard
Canada’s privacy laws generally require a more explicit form of consent. While PIPEDA allows for implied consent, the principle is that the form of consent must be appropriate to the sensitivity of the information. For highly sensitive health data, this leans heavily towards express consent. Provincial laws like Ontario’s PHIPA are even stricter, requiring express consent for many disclosures of personal health information. You can find more insights on how other countries’ healthcare laws compare to see these global differences in action.
Therefore, a Canadian company handling data from both the U.S. and Canada must build its systems to the highest standard. You cannot default to the more permissive HIPAA model.
Building a Dual-Compliant Consent Workflow
To satisfy the requirements of a SOC 2 audit while operating in this dual-jurisdiction environment, a generic consent workflow is inadequate. An actionable, compliant approach requires specific technical controls:
- Jurisdictional Data Tagging: Implement a mechanism to tag data at the point of ingestion with its jurisdiction of origin (e.g., “US-HIPAA,” “ON-PHIPA”). This metadata should drive all subsequent processing rules. This is direct evidence for SOC 2 criterion P2.1, which requires the entity to communicate its privacy commitments.
- Granular Consent Engine: Design interfaces that capture and record specific, granular consent for distinct data uses, rather than a single “I agree” checkbox. The system must be able to block a data use if express consent for that specific purpose has not been obtained, as required under PHIPA.
- Immutable Consent Logging: Maintain a robust, tamper-evident audit trail of all consent-related actions: who consented, when, to what specific uses, and from which jurisdiction. This log is crucial evidence for a SOC 2 auditor testing controls related to P6.1 (Collection) and P6.3 (Use, Retention, and Disposal).
From a SOC 2 perspective, the ability to manage these complex, cross-border consent rules is a sign of a mature privacy program. It directly supports the AICPA Trust Services Criteria for Privacy, specifically P3.1 (Notice and Communication of Privacy Practices) and P6.0 (Collection, Use, Retention, Disposal, and Disclosure), by demonstrating that you have implemented controls to adhere to your legal and regulatory commitments.
Your Obligations as a Canadian Business Associate
 The Business Associate Agreement (BAA) contractually obligates your Canadian company to implement specific safeguards from the HIPAA Security Rule. This is where the legal theory of HIPAA in Canada becomes a practical, operational reality.
The Business Associate Agreement (BAA) contractually obligates your Canadian company to implement specific safeguards from the HIPAA Security Rule. This is where the legal theory of HIPAA in Canada becomes a practical, operational reality.
For a company pursuing SOC 2, this is a significant advantage. The controls required by the HIPAA Security Rule are not a separate checklist; they are security best practices that have a one-to-one mapping with the SOC 2 Trust Services Criteria. By building a control framework to satisfy your BAA, you are simultaneously building the evidence required to pass a SOC 2 audit. A unified approach allows you to meet two sets of requirements with a single set of controls, creating significant efficiencies.
Mapping HIPAA Safeguards to SOC 2 Criteria
The HIPAA Security Rule is structured into three categories of safeguards that align directly with the SOC 2 Security criterion (Common Criteria).
- Administrative Safeguards: These are the policies and procedures that govern your security program, such as conducting a formal risk analysis (maps to SOC 2 CC3.2), implementing security awareness training (maps to CC2.2), and assigning a security officer.
- Physical Safeguards: These controls protect physical access to systems, including server room access controls and workstation security policies (maps to CC6.4 and CC6.5).
- Technical Safeguards: These are the technology-based controls that protect data, such as access controls (maps to CC6.1, CC6.3), data encryption (maps to CC6.8), and audit logging (maps to CC7.2).
These are not just HIPAA tasks; they are the core components of any robust security program and are precisely what a SOC 2 auditor will test.
Building a Unified Control Framework
Instead of treating HIPAA and SOC 2 as separate compliance initiatives, integrate them into a single, unified control framework. A well-designed control can satisfy requirements from both, which is the most efficient path to compliance.
This table demonstrates the direct alignment between specific HIPAA Security Rule requirements and the SOC 2 Common Criteria.
| HIPAA Safeguard (Technical) | Description | Corresponding SOC 2 Criterion |
|---|---|---|
| Access Control (164.312(a)) | Implement technical policies and procedures to allow access only to those persons or software programs that have been granted access rights. | CC6.1, CC6.3: The entity implements logical access security measures to protect against unauthorized access. |
| Audit Controls (164.312(b)) | Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use ePHI. | CC7.2: The entity monitors its systems and takes action to prevent or detect the failure of security procedures. |
| Transmission Security (164.312(e)) | Implement technical security measures to guard against unauthorized access to ePHI that is being transmitted over an electronic network. | CC6.8: The entity implements controls to prevent or detect and act upon the introduction of unauthorized and malicious software. (Note: This is often tested here as encryption in transit.) |
For a SOC 2 audit, you must provide evidence that these controls are not only designed appropriately but are also operating effectively over a period of time (for a Type 2 report). For a Canadian company that has signed a BAA, this means demonstrating to an auditor that your access control reviews, your monitoring of audit logs, and your use of encryption meet the standards required by both HIPAA and the AICPA. The evidence you generate for one is directly applicable to the other, making a SOC 2 report the most powerful tool for proving your security posture to American clients.
Managing Cross Border Breach Notifications
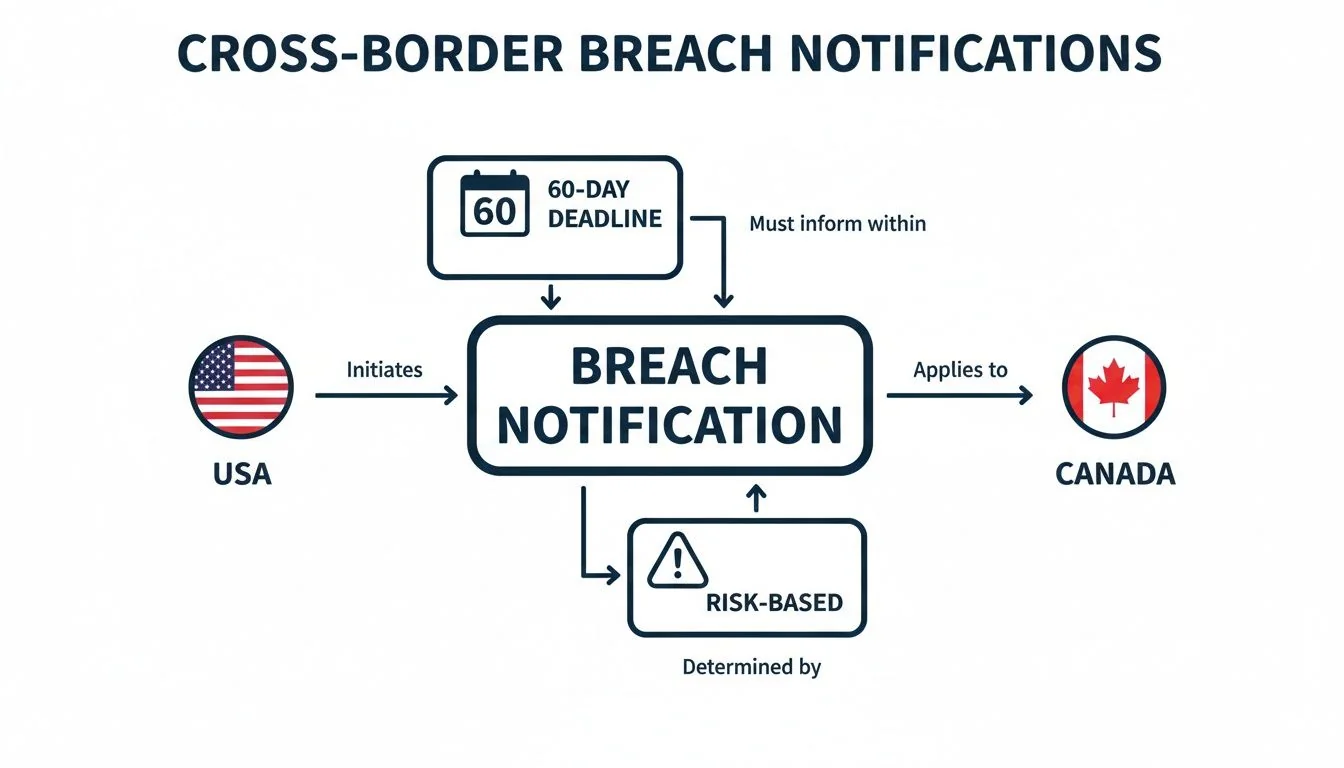
A data breach affecting a Canadian company holding U.S. health data triggers parallel and often conflicting notification obligations. This is a critical risk area that matters immensely for a SOC 2 audit. Your incident response plan is a key control that will be scrutinized by auditors. A generic plan that does not account for these jurisdictional nuances will be deemed inadequate, representing a significant control deficiency under SOC 2 Common Criteria CC7.3 (Incident Response).
Under HIPAA, a data breach is presumed reportable unless a documented risk assessment demonstrates a low probability of compromise. This leads to rigid reporting deadlines. In contrast, Canadian laws like PIPEDA are based on a “real risk of significant harm” threshold, which requires a different type of analysis.
The Critical Timeline Differences
HIPAA’s Breach Notification Rule is inflexible. You must notify affected individuals “without unreasonable delay” and no later than 60 calendar days from discovery. For breaches affecting 500 or more individuals, the Secretary of Health and Human Services (HHS) must also be notified within this 60-day window.
Canadian law provides more flexibility. PIPEDA requires reporting “as soon as feasible” after determining a breach poses a “real risk of significant harm.” This creates a complex scenario where a single incident requires two separate analytical tracks and potentially two different reporting timelines.
For a SOC 2 audit, your incident response plan must explicitly address this duality. A plan that merely states “notify as required by law” is a major red flag indicating a lack of operational readiness. A mature, auditable plan will contain specific decision trees and procedures for handling a cross-border incident, demonstrating that the control has been designed to meet your specific legal and contractual commitments, a core tenet of a SOC 2 examination.
Building a Dual-Compliant Incident Response Framework
To pass muster in a SOC 2 audit, your incident response plan must be a detailed, actionable framework that integrates both U.S. and Canadian requirements.
Here is an actionable framework:
- Immediate Containment and Triage: The plan’s first step must be to contain the incident and preserve evidence, initiating a chain of custody for forensic analysis. This is foundational for SOC 2’s CC7.0 series.
- Jurisdictional Assessment: The plan must require an immediate determination of the data’s jurisdictional nature. Was it U.S. PHI (HIPAA), Canadian PHI (PHIPA/provincial law), or both? This classification dictates the subsequent response path.
- Parallel Risk Evaluation: The plan must mandate two simultaneous risk assessment processes:
- HIPAA Track: Conduct and document the four-factor risk assessment to determine if the “low probability of compromise” safe harbor can be met. If not, the 60-day notification clock is running.
- Canadian Track: Conduct and document the “real risk of significant harm” assessment to determine if notification is required under PIPEDA or applicable provincial law.
- Coordinated Notification Workflow: Based on the outcomes of the parallel assessments, the plan must trigger specific, pre-defined notification procedures, including templates and contact lists for HHS, the Office of the Privacy Commissioner of Canada, provincial commissioners, and affected individuals.
This level of detail is exactly what a SOC 2 auditor will look for when testing CC7.3 (Responds to Security Incidents). A plan that explicitly navigates the complexities of HIPAA in Canada demonstrates a high degree of control maturity, which strengthens your SOC 2 report and builds significant trust with enterprise clients.
Using SOC 2 to Demonstrate HIPAA Compliance
For a Canadian company handling U.S. health data, an official “HIPAA certification” does not exist. The de facto standard for demonstrating compliance to American clients is a Service Organization Control (SOC) 2 report.
This matters because a SOC 2 report is not a self-assessment; it is an independent attestation from a licensed CPA firm that your control environment is designed and operating effectively. For a Canadian Business Associate, a SOC 2 report is the most credible and widely accepted mechanism to prove you are meeting your contractual BAA obligations. The significant overlap between the HIPAA Security Rule and the SOC 2 criteria means you can use the SOC 2 audit process to validate your HIPAA compliance posture, making it a highly efficient strategy.
The AICPA HIPAA to SOC 2 Mapping
The American Institute of Certified Public Accountants (AICPA) provides an official mapping that illustrates how the HIPAA Security and Privacy Rules align with the SOC 2 Trust Services Criteria. This document is the blueprint for a unified compliance strategy. It allows you to design a single control that satisfies a HIPAA requirement and then have that same control tested by a SOC 2 auditor.
For example:
- HIPAA Security Rule § 164.312(a)(1) - Access Control: Requires implementation of technical policies and procedures to allow access only to authorized persons or programs.
- SOC 2 Common Criteria CC6.1: Requires the entity to implement logical access security measures over software, infrastructure, and architectures.
These are functionally identical requirements. By implementing role-based access controls (RBAC) and conducting quarterly access reviews, you generate the evidence needed to satisfy both your BAA obligations and the SOC 2 auditor’s testing procedures. For a detailed look at the audit process, this practical guide to navigating a SOC 2 audit is an excellent resource.
Structuring Your SOC 2 Report for U.S. Clients
To maximize the value of your SOC 2 report for the U.S. healthcare market, it must be strategically structured to address HIPAA concerns proactively.
There are two specific ways to achieve this:
- System Description (Section 3): This narrative section of the report describes your systems and controls. Work with your auditor to include explicit language detailing how your control environment is designed to meet your contractual obligations as a HIPAA Business Associate. Specifically reference your implementation of administrative, physical, and technical safeguards.
- Control Mapping Appendix (Optional but Recommended): The most effective SOC 2 reports for this use case include a supplemental appendix that explicitly maps the tested SOC 2 controls back to the specific citations in the HIPAA Security Rule. This provides definitive, third-party validation that your security program has been assessed against HIPAA requirements.
When a prospective U.S. client’s compliance team reviews a SOC 2 report structured this way, it immediately answers their primary question: “Does this vendor take HIPAA seriously?”
This level of detail is especially crucial for high-risk areas like incident response. A SOC 2 auditor will examine your plan’s ability to handle the divergent timelines for breach notification—the rigid 60-day HIPAA deadline versus Canada’s risk-based approach. A report that confirms your plan is robust provides immense assurance. To see how SOC 2 compares to other frameworks, refer to this SOC 2 compliance framework comparison chart.
Choosing the Right Audit Partner
Selecting an audit firm is a critical decision. You require a firm with demonstrated expertise in both SOC 2 and HIPAA. An auditor unfamiliar with the nuances of PHI and the BAA framework will not be able to provide the level of assurance your U.S. clients need.
Ask potential audit firms these specific questions:
- Can you provide examples of SOC 2 reports you have issued for other Canadian BAs that include HIPAA mappings?
- How does your team utilize the official AICPA HIPAA to SOC 2 mapping in your audit methodology?
- Will you collaborate with us to include language in the Section 3 system description that specifically addresses our HIPAA obligations?
- Do you offer, as a standard practice, the inclusion of a HIPAA Security Rule mapping appendix in the final report?
An audit firm that can confidently answer “yes” is a strategic partner who understands your specific cross-border compliance challenges. They will help you produce a SOC 2 report that is not just a compliance artifact, but a key sales enablement tool.
For Canadian companies serving the U.S. healthcare market, navigating the complexities of “hipaa in canada” is a business imperative. A SOC 2 audit, when executed correctly, is the most effective and efficient path to demonstrating compliance and earning the trust of American clients. Achieving SOC 2 audit readiness means building a robust, unified control framework that addresses your dual legal and contractual obligations. This not only satisfies auditors but also proves to the marketplace that you are a secure, reliable, and mature partner ready for enterprise-level deals.