PCI DSS service providers are third-party entities that process, store, or transmit cardholder data on behalf of another organization, or manage components that could impact the security of the Cardholder Data Environment (CDE). These providers, which include Qualified Security Assessor (QSA) companies, Approved Scanning Vendors (ASV), and managed security service providers, are engaged to help an organization achieve and maintain compliance with the Payment Card Industry Data Security Standard (PCI DSS).
Understanding the Role of PCI DSS Service Providers in a SOC 2 Context
For an organization pursuing a SOC 2 attestation, the selection and management of a PCI DSS service provider is not merely an operational task; it is a critical control activity that directly impacts the scope and outcome of a SOC 2 audit. The services rendered by a PCI DSS provider generate evidence that can either strengthen or weaken an organization’s position against the AICPA Trust Services Criteria (TSC). A misaligned PCI DSS engagement can introduce control gaps, create redundant testing efforts, and ultimately delay the issuance of a SOC 2 report.
Why does this matter for someone pursuing SOC 2? The engagement with a PCI DSS service provider is a direct dependency for meeting several SOC 2 criteria. Specifically, under the Security Trust Services Criterion, CC9.2 requires that the entity assesses and manages the risks associated with vendors and business partners. The Report on Compliance (ROC) or Attestation of Compliance (AOC) from your PCI DSS provider serves as key evidence for this criterion. Furthermore, the technical testing, policy reviews, and access control validation performed during a PCI assessment produce artifacts that are directly reusable for a SOC 2 audit. Choosing a provider who understands this synergy prevents duplicated effort and ensures that evidence can be efficiently repurposed, saving significant time and resources.
This article provides a structured comparison of leading PCI DSS service providers, framed to help companies manage their parallel compliance efforts. We will detail each provider’s services, certifications, and ideal customer profile, complete with screenshots and direct links to help you make an informed decision.
1. Coalfire
Coalfire is a large, established PCI Qualified Security Assessor Company (QSAC) that provides a full lifecycle of PCI DSS services, from initial readiness and scoping to the final Report on Compliance (ROC) and Attestation of Compliance (AOC). Their offerings include SAQ validation, remediation advisory, and coordinated vulnerability scanning (ASV) and penetration testing.
Why does this matter for someone pursuing SOC 2? For organizations built on cloud platforms like AWS, Azure, or GCP, Coalfire’s experience is a significant advantage. A SOC 2 audit requires a deep understanding of shared responsibility models, and Coalfire’s expertise in assessing cloud-native environments ensures that controls are correctly mapped and evidenced for both PCI DSS and SOC 2. The penetration testing they conduct for PCI Requirement 11.4 directly satisfies SOC 2’s CC4.2 (evaluates security from a penetration testing perspective), providing a single testing artifact for both audits. This alignment prevents misinterpretations of requirements in complex settings and streamlines evidence collection.
What Makes Coalfire a Top PCI DSS Service Provider?
- Full PCI Lifecycle Management: They guide companies from gap analysis to continuous compliance, reducing the need to juggle multiple vendors for testing, advisory, and assessment. This single-vendor approach simplifies the vendor management process required by SOC 2’s CC9.2.
- Cloud and FinTech Specialization: Their assessors are familiar with the specific architectural challenges of cloud and fintech sectors, ensuring accurate application of controls for both PCI DSS and the related SOC 2 criteria.
- Robust Tooling and Control Mapping: Coalfire provides tools that help map PCI controls to SOC 2 criteria. For example, evidence for PCI Requirement 10 (logging and monitoring) directly supports SOC 2’s CC7.2 (monitoring of systems to detect changes). Their tooling streamlines the cross-referencing process.
Pricing and Engagement: Coalfire typically works with mid-market to enterprise-level organizations. Their pricing reflects this market position, so smaller businesses with a very limited PCI scope may find their quotes on the higher end. Due to their popularity, it is wise to schedule assessments well in advance, particularly during peak compliance seasons at year-end.
For organizations navigating multiple compliance mandates, Coalfire’s ability to map controls across different frameworks is critical. Many PCI DSS controls directly overlap with SOC 2 Trust Services Criteria, especially within Security (Common Criteria) and Availability. For instance, PCI Requirement 9.1 (restricting physical access) aligns with SOC 2’s CC6.3, and PCI Requirement 10 (logging and monitoring) directly supports SOC 2’s CC7.2. Engaging a firm like Coalfire, which understands these overlaps, can create significant efficiencies. As you align your PCI DSS and SOC 2 programs, referencing a comparison of compliance frameworks can help identify these synergies, allowing you to use the same evidence for multiple audits and reduce overall compliance effort.
2. Schellman
Schellman operates as a specialized, audit-only firm, holding certifications as a PCI Qualified Security Assessor (QSA), PA-QSA, P2PE Assessor, and 3DS Assessor. This focus on independent assessment means they do not offer remediation or managed services, positioning them as an objective third party for validation. Their services cover the full spectrum of PCI DSS, from Report on Compliance (ROC) and Attestation of Compliance (AOC) assessments for large entities to SAQ validation for smaller merchants and service providers.
Why does this matter for someone pursuing SOC 2? Schellman’s ability to conduct integrated audits for PCI DSS, SOC 2, ISO 27001, and HIPAA simultaneously is a major operational benefit for an organization seeking multiple attestations. This unified approach directly addresses the need for efficiency in compliance management. By using a single firm for both assessments, the evidence for PCI Requirement 8 (access control) can be used to satisfy SOC 2’s CC6.1 (logical access controls) without requiring separate walkthroughs or evidence requests. This reduces audit fatigue and ensures consistency in the assessment of shared controls, which is highly valued by stakeholders.
What Makes Schellman a Top PCI DSS Service Provider?
- Audit-Only Independence: By not selling remediation products, Schellman avoids potential conflicts of interest. For a SOC 2 audit, this objective assessment strengthens the credibility of the evidence presented, particularly for vendor management criteria (CC9.2).
- Broad PCI Standard Coverage: Their wide range of PCI qualifications makes them a single source for complex payment ecosystem players, simplifying vendor due diligence.
- Integrated Audit Expertise: Schellman specializes in combining audits. Their assessors understand how evidence for PCI DSS can satisfy requirements for other frameworks, reducing redundant evidence collection. For example, the business continuity and disaster recovery plan tested for PCI can also satisfy the Availability TSC in a SOC 2 audit.
Pricing and Engagement: Schellman’s services are positioned at a premium, reflecting their specialization and reputation for rigor. They are a strong fit for mid-market and enterprise companies, but early-stage startups with complex compliance needs also find value in their structured approach. Lead times can be significant, so booking an assessment several months in advance is recommended.
For SaaS companies, the overlap between PCI DSS and SOC 2 is significant. Controls around access management (PCI Req. 7 & 8), logging (PCI Req. 10), and network security (PCI Req. 1) directly support the SOC 2 Trust Services Criteria for Security. A firm like Schellman, experienced in both, can perform an integrated audit where evidence collection for one framework directly supports the other. Understanding the key differences and overlaps between these two standards is essential for efficient compliance; reading up on SOC 2 vs. PCI DSS for SaaS platforms can provide clarity on how to align these efforts and satisfy multiple compliance requirements with a single, coordinated audit.
3. A-LIGN
A-LIGN is a prominent PCI Qualified Security Assessor (QSA) Company with a strong U.S. presence, known for delivering integrated compliance solutions. They offer end-to-end PCI DSS services, from readiness assessments and scoping to the issuance of a final Report on Compliance (ROC) or Attestation of Compliance (AOC). Their services are well-suited to startups and mid-market SaaS, fintech, and payment companies seeking efficient, multi-framework audits.
Why does this matter for someone pursuing SOC 2? A-LIGN’s approach is particularly effective for organizations needing compliance for deal readiness and customer due diligence, which often means achieving both PCI DSS and SOC 2. By coordinating these audits concurrently, they help meet multiple compliance demands at once. For instance, the information security policy required by PCI Requirement 12 directly supports SOC 2’s foundational CC1.1 (the control environment). A-LIGN can review this policy once and apply it to both audits, ensuring consistent governance and saving significant internal review time. This consolidation is a pragmatic way to meet commercial demands without overburdening engineering and compliance teams.
What Makes A-LIGN a Top PCI DSS Service Provider?
- Integrated Audit Programs: They excel at combining PCI DSS assessments with SOC 2, ISO 27001, HITRUST, and FedRAMP audits. This consolidates evidence collection and auditor interactions, saving significant time and internal resources needed for a SOC 2 audit.
- Mid-Market Focus: Their processes are built to accommodate the needs of mid-market technology companies, understanding the urgency behind achieving compliance to meet partnership requirements and unblock sales cycles.
- Familiarity with Modern Stacks: A-LIGN assessors have experience with the security architectures common in SaaS and fintech, ensuring that PCI DSS requirements are applied correctly within cloud environments, which is critical for an accurate SOC 2 that includes the Availability and Security TSCs.
Pricing and Engagement: A-LIGN provides quote-based pricing that is scope-dependent, with no public price lists. For companies with complex environments or those bundling multiple audits, the investment is generally in the mid-to-upper range for the market. Their model is designed to accelerate compliance, making them a good fit for businesses with clear commercial drivers for their audit.
The strategic value of a firm like A-LIGN becomes clear when preparing for both PCI DSS and a SOC 2 audit. Many PCI DSS requirements have direct parallels in the SOC 2 Trust Services Criteria, creating opportunities for efficiency. For example, PCI Requirement 3 (protect stored account data) maps closely to SOC 2’s CC6.1, which addresses logical access controls to prevent unauthorized use of information. Similarly, PCI Requirement 12 (maintain a policy that addresses information security) aligns with SOC 2’s foundational CC1.1, concerning the control environment. By engaging a provider that manages both audits, you can use the same control evidence to satisfy both frameworks, significantly reducing redundant work and audit fatigue.
4. NCC Group
NCC Group provides a global payment security practice offering a wide array of services including PCI DSS, PCI 3DS, P2PE, and Card Production. They combine their Qualified Security Assessor (QSA) capabilities with deep technical testing and implementation experience, making them a strong choice for organizations with complex payment flows and hybrid or cloud-based networks.
Why does this matter for someone pursuing SOC 2? NCC Group’s deep technical proficiency is a key benefit for a SOC 2 audit. The penetration testing performed for PCI DSS Requirement 11.4 must be robust enough to satisfy the expectations of a SOC 2 auditor evaluating CC4.2 (penetration testing). An inadequately scoped or executed penetration test for PCI could be rejected during a SOC 2 audit, forcing a costly and time-consuming re-test. Engaging a technically skilled firm like NCC Group ensures that testing activities are comprehensive enough to generate evidence for both standards from a single engagement, saving considerable time and resources.
What Makes NCC Group a Top PCI DSS Service Provider?
- Broad PCI Portfolio: Their services extend beyond PCI DSS to include niche standards like PCI 3DS and P2PE, simplifying vendor management for organizations with diverse payment security needs and satisfying SOC 2’s CC9.2.
- Combined Assessment and Technical Testing: NCC Group can perform both the QSA audit and the required technical tests, such as penetration testing. This integration ensures the testing scope and methodology align with the requirements of both PCI DSS and SOC 2.
- Expertise in Complex Environments: They are well-versed in assessing highly regulated, multi-region companies, and their assessors understand the specific challenges of hybrid-cloud architectures, which is crucial for a SOC 2 audit that includes the Availability and Security TSCs.
Pricing and Engagement: NCC Group is geared toward enterprise clients with substantial and often international compliance needs. Consequently, their engagement costs may be higher than those of providers focused on smaller merchants. Given the complexity of the projects they often undertake, it is best practice to begin engagement discussions well ahead of desired assessment timelines.
For companies also undergoing a SOC 2 audit, NCC Group’s technical proficiency is a key benefit. Many PCI DSS requirements have direct parallels in the SOC 2 Trust Services Criteria. For example, PCI DSS Requirement 11.3 (penetration testing) directly supports SOC 2’s CC7.1, which requires the use of detection and monitoring procedures to identify vulnerabilities. Engaging a technically skilled firm like NCC Group ensures that penetration tests are thorough enough to satisfy both standards. This integrated approach to testing can save considerable time and resources by using a single, robust testing activity to generate evidence for both your PCI DSS and SOC 2 audits.
5. SecurityMetrics
SecurityMetrics is a long-standing PCI Qualified Security Assessor (QSA) and Approved Scanning Vendor (ASV) that provides a cohesive suite of compliance services, including QSA-led audits, SAQ validation, ASV vulnerability scanning, and PCI Forensic Investigator (PFI) services. They bundle these core services with added tools like webpage integrity monitoring and security awareness training.
Why does this matter for someone pursuing SOC 2? For organizations pursuing SOC 2, SecurityMetrics’ bundled services provide a clear, auditable trail of continuous monitoring activities. The ASV scanning they provide for PCI Requirement 11.3 directly supports the vulnerability management activities required under SOC 2’s CC4.1 (vulnerability scanning). The scan reports serve as direct evidence for a SOC 2 auditor. Similarly, their security awareness training addresses PCI Requirement 12.6, which aligns with SOC 2’s CC1.2 (demonstrating a commitment to competence). By using a single provider for these overlapping requirements, an organization can consolidate evidence collection and demonstrate a cohesive, ongoing security program to SOC 2 auditors.
What Makes SecurityMetrics a Top PCI DSS Service Provider?
- Integrated Service Bundles: They combine QSA audits with ASV scanning and security training. This all-in-one approach provides evidence for multiple SOC 2 criteria (CC4.1, CC1.2) from a single vendor relationship.
- Transparent Pricing Model: Their public price-range estimator allows for better budget forecasting, which supports the resource planning and oversight functions detailed in SOC 2’s CC1 series.
- Broad Market Appeal: Their services are designed to be accessible, allowing companies of various sizes to establish the foundational controls that will later be tested in a SOC 2 audit.
Pricing and Engagement: SecurityMetrics serves a broad market and is known for its transparent pricing tools. However, some customers, often those onboarded through acquiring bank partnerships, have noted a frequent communication and upsell cadence. Organizations that prefer a more hands-off relationship with minimal vendor interaction should discuss communication preferences early in the engagement.
For organizations pursuing both PCI DSS and SOC 2 compliance, SecurityMetrics’ integrated approach offers a clear path to control alignment. The ASV scanning they provide for PCI Requirement 11.3 directly supports the vulnerability management activities expected under SOC 2’s CC4.1. Similarly, their webpage integrity monitoring aligns with the change detection controls in SOC 2’s CC3.2. By using a single provider for these overlapping technical requirements, an organization can consolidate evidence collection. This is especially useful when demonstrating to a SOC 2 auditor that you have a formal process for identifying and addressing vulnerabilities, a key criterion for meeting the Security Trust Services Principle.
6. ControlCase
ControlCase is a PCI QSAC and ASV that operates on a platform-led, managed compliance model, using proprietary software to standardize evidence collection and operationalize recurring compliance activities. This approach is built for organizations seeking a repeatable, continuous compliance program.
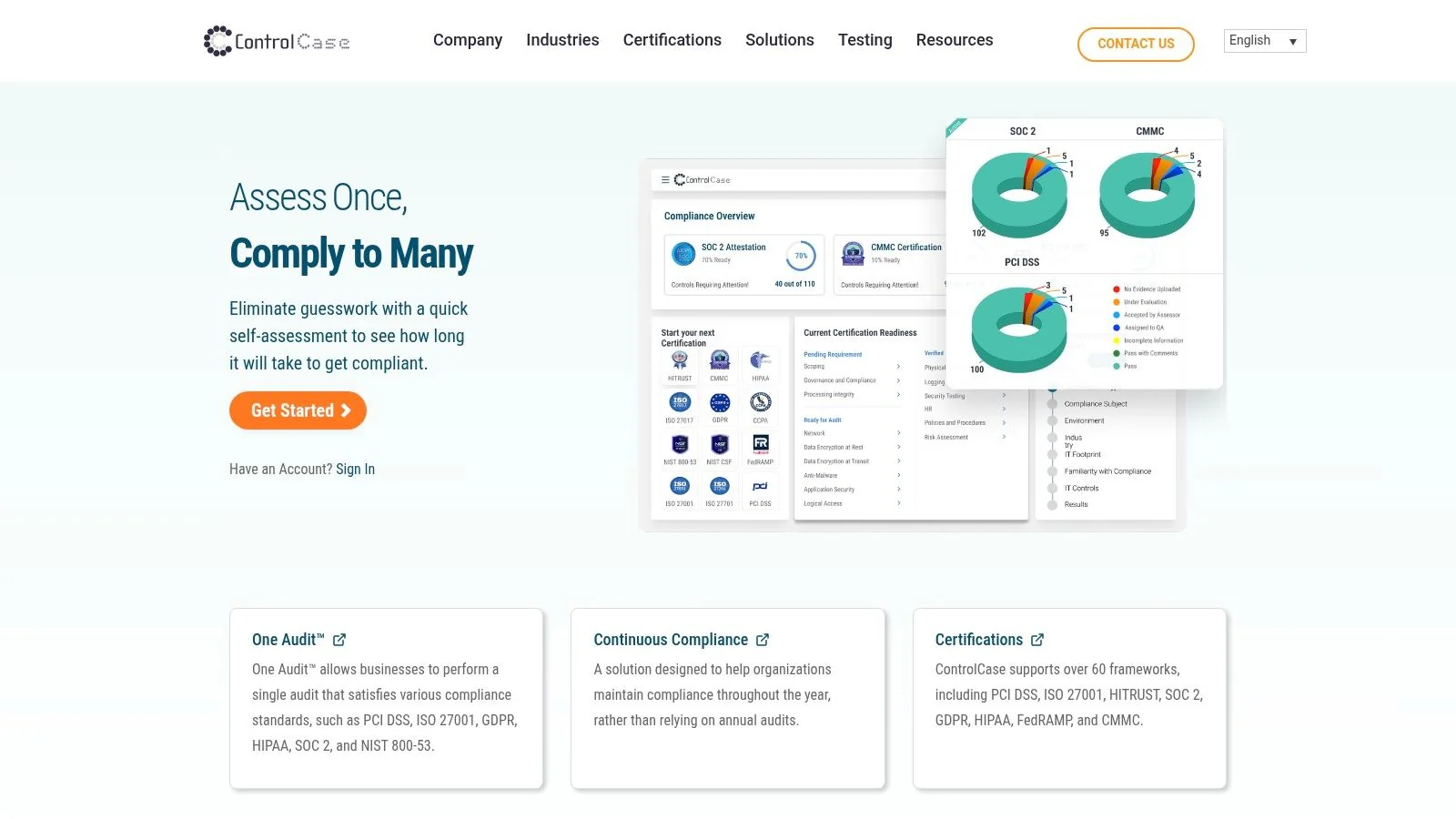
Why does this matter for someone pursuing SOC 2? ControlCase’s platform-driven methodology is highly beneficial for companies managing SOC 2, particularly for a Type 2 report which assesses controls over a period of time. The platform’s ability to centralize evidence and demonstrate ongoing compliance activities is a significant asset. For instance, the quarterly access reviews required by PCI can be tracked in the platform, providing timestamped evidence that the control is operating effectively, which is essential for a SOC 2 Type 2. Evidence collected for PCI Requirement 3 (protect stored cardholder data) can be directly mapped within the platform to SOC 2’s CC6.1, demonstrating a consistent control posture to auditors.
What Makes ControlCase a Top PCI DSS Service Provider?
- Platform-Driven Compliance: The Compliance Manager platform provides a structured workflow, reducing administrative burden and creating a clear audit trail that is invaluable for a SOC 2 examination.
- Continuous Compliance Model: Their model is designed for ongoing compliance, which helps an organization prove to a SOC 2 auditor that controls are not just designed appropriately (for a Type 1) but are also operating effectively over time (for a Type 2).
- Global Delivery Consistency: For multinational corporations, ControlCase provides a standardized assessment methodology that can be applied across different subsidiaries, ensuring uniform quality and supporting consistent control application as required by the SOC 2 framework.
Pricing and Engagement: ControlCase is best suited for mid-market to enterprise organizations that can benefit from a managed, platform-based service. The initial investment in their managed model might be higher than a traditional one-time audit, but it is structured to deliver long-term savings through efficiency. Organizations with very simple PCI scopes may find the platform adds unnecessary overhead.
The methodology ControlCase uses is highly beneficial for companies also managing SOC 2. The platform’s ability to centralize evidence and map controls is a significant asset. For instance, evidence collected for PCI Requirement 3 (protect stored cardholder data) can be directly mapped to SOC 2’s CC6.1, which addresses logical access controls. Likewise, the procedures for PCI Requirement 12 (maintain a policy that addresses information security) support the control environment criteria in SOC 2. Using a unified platform helps prove that these controls are not just designed but are operating effectively over time, a key requirement for a SOC 2 Type 2 report.
7. VikingCloud
VikingCloud, one of the largest PCI DSS service providers globally, provides a broad range of compliance services, including QSA-led assessments, ASV services, and PFI capabilities. Their key differentiator is their proprietary compliance platform, widely adopted by payment acquirers to manage the compliance of their merchant portfolios.
Why does this matter for someone pursuing SOC 2? For an organization undergoing a SOC 2 audit, VikingCloud’s services can directly support several Trust Services Criteria. Their ASV scanning directly addresses SOC 2’s CC4.1 (vulnerability scanning), and the scan reports serve as critical evidence of a formal vulnerability management process. The dashboards and reporting within the Asgard platform align with CC2.1, which pertains to communications with responsible parties about the achievement of objectives. By providing clear visibility into compliance status, the platform helps management fulfill its oversight and governance duties, demonstrating a structured approach to security that auditors value for a SOC 2 attestation.
What Makes VikingCloud a Top PCI DSS Service Provider?
- Unmatched Scale for Merchant Portfolios: Their platform is designed to handle immense scale, making them a strong partner for acquirers and payment service providers who must demonstrate oversight of their downstream merchants, a key aspect of vendor management under SOC 2’s CC9.2.
- Integrated Technology Platform: The Asgard platform provides a single pane of glass for tracking compliance status, which can be presented to a SOC 2 auditor as evidence of a formalized monitoring program (CC2.1).
- Full Suite of PCI Credentials: VikingCloud holds key PCI certifications, allowing them to serve as a single point of contact for assessment, scanning, and incident response, simplifying the vendor due diligence process.
- Acquirer and Partner Integrations: Deep integrations with payment partners often mean merchants are enrolled in VikingCloud’s programs automatically, streamlining the compliance process.
Pricing and Engagement: Many businesses encounter VikingCloud through their acquiring bank or payment processor, with costs often bundled into their merchant services. For direct QSA engagements, their pricing is competitive. Clients should clarify the communication cadence and program details, as some users have reported frequent automated reminders and upsell offers tied to their acquirer’s program.
For an organization undergoing a SOC 2 audit, VikingCloud’s services can directly support several Trust Services Criteria. Their ASV scanning directly addresses SOC 2’s CC7.1, which requires the use of detection and monitoring procedures to identify changes and potential vulnerabilities. The reports from these scans serve as critical evidence for auditors. Likewise, the dashboards and reporting within the Asgard platform align with CC2.1, which pertains to communications with responsible parties about the achievement of objectives. By providing clear visibility into compliance status, the platform helps management fulfill its oversight and governance duties, demonstrating a structured approach to security that auditors value.
Top 7 PCI DSS Service Providers Comparison
| Vendor | Implementation complexity | Resource requirements | Expected outcomes | Ideal use cases | Key advantages |
|---|---|---|---|---|---|
| Coalfire | High — handles complex cloud-native and fintech scopes | Enterprise-level budget; multi-team engagement; scheduling lead times | Comprehensive PCI v4.0.1 ROC/AOC and readiness with tooling to reduce rework | Large merchants, fintechs, cloud providers with complex payment architectures | Deep cloud and PCI expertise, robust tooling, thought leadership |
| Schellman | Moderate–High — auditor-focused, rigorous processes | Requires experienced control owners and premium budget | Independent, clear ROC/AOC and cross-framework alignment | Startups to mid-market and enterprises needing rigorous, independent audits | Reputation for rigor, clear reporting, strong cross-framework guidance |
| A-LIGN | Moderate — mid‑market friendly, integrated audit delivery | Mid-market budget; coordination for parallel SOC 2/ISO engagements | Accelerated deal readiness and combined audit outputs | SaaS, fintech and mid‑market firms doing PCI plus SOC 2/ISO | Efficient coordination, integrated programs, mid‑market processes |
| NCC Group | High — supports multi-standard and technical testing | Enterprise resources; technical testing and multi-region planning | Thorough assessments plus strong independent technical testing | Complex payment flows, hybrid/cloud networks, regulated multi-region environments | Broad PCI portfolio, strong technical testing and implementation expertise |
| SecurityMetrics | Low–Moderate — straightforward audit + tooling packages | Lower-cost options; bundled ASV/PFI/scanning; transparent pricing | Audit delivery with continuous scanning, training and monitoring tools | Merchants and service providers seeking bundled scans and simple pricing | Transparent pricing, bundled tools, SMB-to-enterprise accessibility |
| ControlCase | Moderate — platform-led managed compliance model | Investment in platform and managed services; scales with portfolio | Operationalized, repeatable continuous compliance and standardized evidence | Service providers and multi-entity portfolios needing ongoing compliance | Platform-driven automation, standardized workflows, global delivery consistency |
| VikingCloud | Low–High (scale-dependent) — designed for distributed merchant networks | Scale-capable infrastructure; acquirer integrations; mobile adoption | Centralized tracking and continuous compliance for large populations | Acquirers, ISOs/PSPs and large multi-brand merchant programs | Proprietary platform, acquirer integrations, centralized dashboards and mobile workflows |
From Provider Selection to SOC 2 Readiness: Your Next Steps
Selecting the right PCI DSS service provider is a foundational element of your broader governance, risk, and compliance (GRC) strategy, with direct implications for your organization’s SOC 2 audit readiness. An effective PCI DSS engagement should not be viewed as a standalone compliance task but as a strategic activity that generates critical evidence for your SOC 2 attestation. The technical assessments, control validations, and policy reviews conducted by your QSA are not just for achieving a PCI ROC; they are integral components of the body of evidence required to demonstrate adherence to the AICPA Trust Services Criteria.
To maximize the return on your PCI DSS investment and accelerate your SOC 2 timeline, you must proactively manage the overlap between the two frameworks. When your QSA firm performs penetration testing and vulnerability scans for PCI DSS Requirement 11, ensure the reports are detailed enough to also satisfy the criteria for CC4.2 (penetration testing) and CC4.1 (vulnerability scanning). The user access reviews and role-based access control (RBAC) configurations validated for PCI DSS Requirements 7 and 8 provide direct evidence for the SOC 2 CC6 series on logical access. Similarly, the documented vendor management processes required by PCI DSS Requirement 12.8 are essential for satisfying SOC 2’s CC9.2 on vendor risk management. By explicitly connecting these activities, you transform a compliance necessity into a strategic asset for your SOC 2 audit, reducing redundant work and demonstrating a mature, integrated security posture to auditors, customers, and partners.
Ready to find an auditor that understands the crucial link between PCI DSS and SOC 2? The SOC2Auditors platform provides data-driven comparisons of top audit firms, helping you select a partner with the right expertise for your technology stack and compliance goals. Find your ideal SOC 2 auditor in minutes.