Your SOC 2 report is approaching the end of its useful life, sales keeps getting security questionnaires, and procurement teams want a current report with no awkward explanation about timing. That is the point where soc 2 audit renewal stops being an annual admin task and becomes an operating decision. If you handle it well, renewal is faster, cleaner, and easier on engineering. If you handle it badly, you create evidence churn, scope creep, and uncomfortable customer conversations.
A SOC 2 audit renewal is a new examination of your controls over a new review period, usually for a Type 2 report, to confirm the controls tied to your selected Trust Services Criteria continue to operate effectively. It is not a rubber stamp on last year’s report. Auditors reassess your system description, your scoped services, your control set, and the evidence showing those controls worked throughout the period. For teams pursuing SOC 2, that matters because buyers do not treat an old report as proof that your current environment is still under control.
Defining the SOC 2 Audit Renewal
A SOC 2 audit renewal is the repeat attestation cycle that validates your control environment over a fresh audit period against the Trust Services Criteria you selected, commonly Security and, where needed, Availability, Processing Integrity, Confidentiality, and Privacy. For most companies, the practical focus is a new Type 2 report showing operational effectiveness over time, not a point-in-time design review.

The first fact to keep straight is timing. SOC 2 audit reports are valid for exactly 12 months from the date of issuance, which is why annual renewal is the normal cycle for SaaS, FinTech, and HealthTech teams. Some higher-risk organizations renew on a 6-month cycle, which occurs in 10-20% of cases, and 2024 benchmark data also showed broader control environments, with 23% of SOC 2 reports containing more than 150 controls, up from 16% in 2023, according to Konfirmity’s SOC 2 renewal guide.
What changes from the first audit
Your first SOC 2 effort is usually about standing up the program. Renewal is different. The auditor already expects controls to exist. The question becomes whether your team executed them consistently, updated them when the business changed, and retained evidence that stands up to testing.
That distinction matters for SOC 2 because enterprise customers care less about your intent than your operating discipline. A clean renewal tells them your controls survived a year of releases, incidents, vendor changes, personnel turnover, and infrastructure adjustments.
Why buyers care about renewal quality
Procurement teams look for continuity. A current report with a clear scope and no obvious lapse reduces back-and-forth in diligence. A stale report forces your sales team to explain timing, provide bridge documentation, and answer harder questions about what changed since the last period.
Practical takeaway: Treat renewal as proof of sustained control operation, not as a compliance anniversary. That mindset changes how you plan, collect evidence, and manage auditor expectations.
For anyone pursuing SOC 2, this is the true purpose of renewal. It preserves the credibility of the attestation, supports customer trust, and demonstrates that your control environment is part of normal operations rather than a one-time sprint.
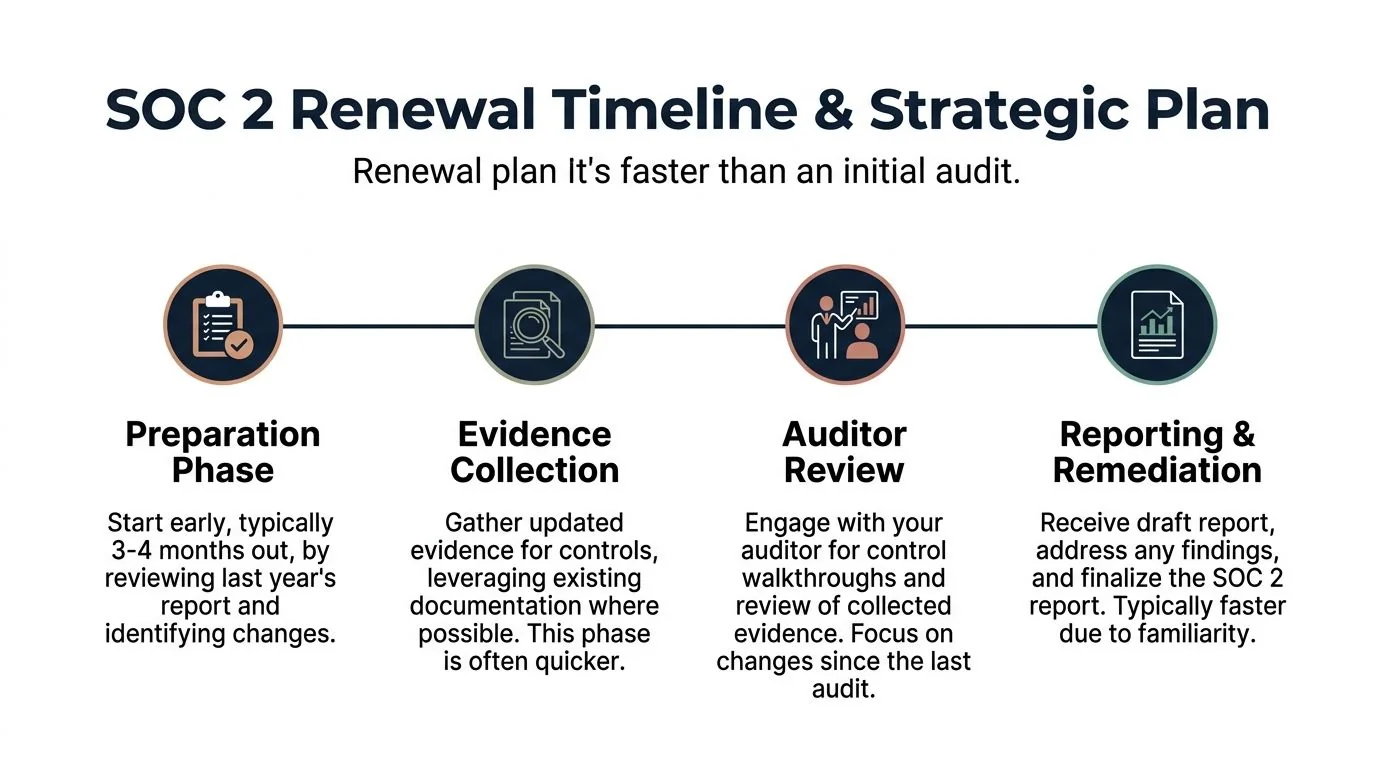
Your Renewal Timeline and Strategic Plan
Most renewal projects go off track for one reason. Teams start when the report is almost due instead of when the observation period and staffing calendar require action. Renewal can move faster than an initial audit, but only if you lock the plan before evidence gaps appear.
Renewal audits for SOC 2 Type 2 typically complete in 6-8 months, compared with 9-12+ months for first-time audits, because the controls and evidence motions already exist. That advantage disappears when companies start late and create a gap in attestation coverage, as noted in Scrut’s SOC 2 compliance timeline.
A practical planning reference is this guide on how long a SOC 2 audit takes. Use it to set expectations with leadership before you commit to customer-facing dates.
Build the plan backward from period end
The cleanest renewals are scheduled backward from the end of the observation period, not forward from the date sales wants the report. If the report needs to support procurement in a specific quarter, the controls, walkthroughs, internal testing, and fieldwork all need owners long before then.
Use this operating sequence:
| Phase | What the team should do | Why it matters for SOC 2 |
|---|---|---|
| Pre-planning | Review prior report, exceptions, scope changes, ownership, and customer commitments | Prevents repeat issues and misalignment |
| Readiness | Test key controls, organize evidence, confirm policy and system changes | Reduces fieldwork churn |
| Fieldwork | Provide samples, walkthroughs, explanations, and follow-up evidence | Determines whether the report can be issued cleanly |
| Reporting and remediation | Resolve findings, update disclosures, finalize management assertions | Protects report quality and buyer confidence |
Pre-planning before the period closes
Experienced teams gain an advantage here.
A strong pre-planning cycle includes:
- Prior-year exception review: Every exception, observation, or awkward auditor comment should have an owner, corrective action, and proof that the issue stayed fixed.
- Scope validation: Confirm what services, systems, environments, vendors, and entities are in scope. If you added a product, migrated infrastructure, or changed your subservice organization mix, the description needs to reflect that.
- Control ownership reset: Engineering managers leave. IT admins rotate. GRC leads inherit half-documented programs. Resetting control owners early prevents evidence requests from landing in the wrong queue.
Readiness work before fieldwork starts
Renewal gets easier when the evidence already exists in the right format. It gets expensive when the company tries to recreate a year of operation from chat logs, screenshots, and memory.
Focus your readiness work on three areas:
-
Control performance checks Confirm recurring controls ran. Access reviews. change approvals. vulnerability scanning. incident logging. vendor reviews. backup testing. policy acknowledgments.
-
Narrative updates Your system description, complementary user entity controls, and control language need to match reality. If your written control says one thing and the engineering workflow does another, the auditor will test both.
-
Stakeholder kickoff Run a short kickoff with security, engineering, IT, HR, legal, and the executive sponsor. Each team should know which controls they own and when evidence will be requested.
Tip: If a control depends on one person remembering to export proof at quarter end, treat that as a weak control operation model even if the control technically worked.
Fieldwork and report issuance
Fieldwork usually goes smoothly when the company has already aligned on samples, repository structure, and explanations for changes. It turns painful when the first time anyone discusses a control is in the auditor meeting.
A good fieldwork posture looks like this:
- Fast sample response: Pull exactly what was requested, with dates, owner context, and enough metadata to understand the artifact.
- Clear explanations of change: If you switched identity providers, rewrote deployment workflows, or onboarded a new cloud service, explain the transition and the replacement controls.
- Visible remediation path: If the auditor flags an issue, show the root cause and the fix quickly.
Strategic planning mistakes that create gaps
The most common pattern is assuming renewal is “just last year again.” It rarely is. Product growth, customer commitments, privacy obligations, and vendor dependencies shift the control environment every year.
Watch for these failure modes:
- Late auditor booking
- Unclear period boundaries
- Missing owner coverage during holidays
- Scope changes discovered during fieldwork
- Sales promises made before GRC validates timing
For someone pursuing SOC 2, the value of a real renewal plan is straightforward. It keeps attestation current, protects sales cycles, and reduces the internal cost of producing a report that can survive buyer scrutiny.
Optimizing Your Audit Scope and TSCs
Renewal is the right time to challenge your scope. Many teams do the opposite. They inherit the original boundary and keep adding systems, data flows, and criteria until the audit becomes slow, expensive, and hard to explain.

That approach hurts both compliance and go-to-market. A bloated scope increases evidence volume, testing complexity, and the chance that one weak area drags down the whole report. A narrow but accurate scope can be much more useful if it aligns with what customers buy and what your system does.
Scope is a commercial decision
SOC 2 scope should answer a customer question. Which service are you attesting to? Which data is protected? Which commitments are you making under the selected TSCs?
If your customers buy one core SaaS platform, scope that platform cleanly. If you acquired a legacy tool that few customers use and the controls are not yet harmonized, think carefully before dragging it into the same report. You do not win points for making the report larger than necessary.
For renewal, use these decision criteria:
- Add to scope when the service is customer-facing, contractually relevant, and already managed under your core controls.
- Keep in scope when the service remains strategically important and the evidence burden is predictable.
- Remove from scope when the system is being retired, no longer part of the customer promise, or requires a separate remediation effort before it belongs in the report.
Choosing the right TSCs
Most organizations start with Security because it is the baseline criterion buyers expect. The other criteria should be added only when they reflect customer commitments or business requirements.
A practical lens:
| TSC | Add it when | Avoid forcing it when |
|---|---|---|
| Security | Always the baseline for most SOC 2 reports | Not typically optional in buyer expectations |
| Availability | You make uptime, resilience, backup, or recovery commitments | Your operations do not support deeper testing yet |
| Processing Integrity | Your value depends on complete, accurate, timely processing | The language would overstate what your product guarantees |
| Confidentiality | You commit to protecting specific confidential data classes | Data classification and handling are still informal |
| Privacy | You process personal information in ways that require formal privacy controls | Privacy governance is immature or fragmented |
This is also where specific AICPA criteria matter in practice. If you add Privacy, you need more than a privacy policy on the website. Auditors will expect evidence that notice, consent where applicable, retention, access, and related control activities are operating in a controlled way. If you include Confidentiality, your data handling, classification, and disposal practices need to match the claim.
A useful explainer for non-GRC stakeholders:
Scope optimization questions worth asking
Ask these before you lock the renewal:
- Which products do prospects ask about in diligence?
- Which environments generate the highest evidence burden?
- Which systems changed enough that the control narrative needs rewriting?
- Which TSCs support sales and contracts, and which ones just look good on paper?
- Which subservice organizations are now critical to your control story?
Key takeaway: A better SOC 2 report is not the broadest report. It is the report whose scope, TSCs, and system description match your customer commitments.
For someone pursuing SOC 2, scope optimization matters because it directly affects cost, audit effort, and the usefulness of the report in customer reviews. Good scoping turns renewal into a business asset. Bad scoping turns it into recurring drag.
Mastering Evidence Collection and Continuous Monitoring
Most painful renewals are not caused by weak controls. They are caused by weak evidence operations. The company may be doing the right things, but if no one can show that the controls ran, when they ran, and who reviewed the output, the audit still becomes messy.
Mature teams distinguish themselves through this approach. They stop treating evidence as a once-a-year project and move to continuous collection. That model is more resilient for SOC 2 because Type 2 testing is about operation over time, not just control design.
Start with prior-year exceptions and current-year testing
A solid renewal method starts with two disciplines. First, fix every prior-year exception in a way that changes the operating process, not just the slide deck. Second, run internal testing before the auditor does.
According to Kahn Litwin’s guidance on renewing your SOC 2 report, internal testing can prevent 70% of common deficiencies. The same source notes that unaddressed prior exceptions drive 40% of failures, ignored framework evolution such as CC6.8 vendor risk issues drive 25% of exceptions, and GRC tool integration can reduce manual effort by 70% while helping teams reach 95% first-pass rates on evidence submission.
That matters for SOC 2 because auditors do not just test whether a control exists. They test whether the control owner carried it out consistently and whether the evidence supports the narrative.
The three evidence categories that matter
A collection model should encompass the full control environment. In practice, most evidence falls into three groups.
Automated logs and machine-generated records
This is the highest-value category because it is time-stamped, repeatable, and hard to dispute.
Examples include:
- Access control records from Okta, Microsoft Entra ID, Google Workspace, or your identity provider for user lifecycle and MFA enforcement
- Security monitoring output from SIEM platforms and detection tools
- Cloud activity and configuration data from AWS, Azure, or GCP
- Vulnerability scan results and ticket closure evidence
- Change management records from Jira, GitHub, GitLab, or your deployment tooling
For criteria such as CC6.1 logical access and CC7.2 change management, this evidence is often your primary proof that the control operated throughout the period.
Human-generated artifacts
These are easy to underrate and easy to lose.
They include policy acknowledgments, access review sign-offs, meeting minutes, training completion records, exception approvals, risk review notes, and incident postmortems. Auditors often need these to connect the system-generated data to human oversight.
Configuration and point-in-time screenshots
Screenshots are weaker than logs, but they still matter when used correctly. Configuration exports, setting pages, and console views can support claims about encryption, retention, alerting, backup settings, or privileged access restrictions.
The key is not to rely on screenshots where logs should exist. Use them to support the story, not carry the whole story.
A workable operating model
The best evidence programs assign a home, an owner, and a cadence to every recurring artifact. If any one of those is missing, renewal turns into detective work.
Here is a simple coordination model.
| Control Area (Example TSC) | Primary Owner (Team) | Key Evidence Required | Collection Cadence |
|---|---|---|---|
| Logical access (Security) | IT and Security | Provisioning records, deprovisioning records, MFA enforcement evidence, access review sign-offs | Ongoing, with formal periodic review |
| Change management (Security, Processing Integrity) | Engineering | Pull request approvals, deployment records, ticket links, emergency change approvals | Per change, with recurring review |
| Vendor management (Security, Confidentiality) | Security, Procurement, Legal | Vendor reviews, risk assessments, contract clauses, subservice monitoring records | At onboarding and on a recurring review cycle |
| Incident response (Security, Availability) | Security and Engineering | Incident logs, escalation records, postmortems, corrective actions | As incidents occur, plus periodic tabletop support |
| Security awareness (Security, Privacy) | HR and Security | Training assignments, completion records, policy acknowledgments | At onboarding and recurring thereafter |
If your team wants a detailed artifact map, this SOC 2 evidence collection guide is a useful operational reference.
What continuous monitoring looks like in practice
Continuous monitoring does not mean every control is automated. It means the control operation and the evidence path are both stable.
A practical stack often includes Vanta or Drata for evidence orchestration, Jira for tracked remediation, GitHub or GitLab for engineering approvals, cloud-native logs for activity evidence, and a central repository for artifacts that cannot be pulled automatically.
What works:
- Pulling identity, endpoint, cloud, and ticketing data automatically where possible
- Naming artifacts consistently by control, date, and owner
- Running periodic internal checks before the auditor samples the control
- Keeping policy versions and sign-off records tied to the audit period
- Storing exception decisions with the approving owner and rationale
What does not work:
- Screenshot folders with no naming standard
- Shared drives where only one person understands the structure
- Manual evidence exports done at year end
- Control narratives copied from last year after the workflow changed
- Vendor reviews performed informally but not documented
Tip: If the evidence repository cannot survive one key employee going on leave, it is not audit-ready.
For someone pursuing SOC 2, evidence discipline is where readiness becomes real. It reduces the burden on engineering, lowers the chance of exceptions, and lets the audit test your controls instead of your ability to reconstruct history.
Deciding on Your Auditor When to Stay or Switch
Many teams default to the same audit firm every year. Sometimes that is the right call. Sometimes it is the most expensive way to preserve familiar friction.
The renewal decision is not just “Do we like our auditor?” A central question is whether the current firm still fits your scope, growth stage, buyer expectations, and internal operating style. That matters for SOC 2 because the auditor affects timeline, evidence load, report clarity, and how painful fieldwork feels across the business.
When staying makes sense
Continuity has real value. A firm that knows your environment, your control language, and your service model can reduce re-education and keep the renewal moving. That is especially true when your scope is stable and your internal team is lean.
Staying is usually the better choice when:
- The firm communicates clearly and gives precise requests
- The prior report was well written and useful in customer diligence
- The audit team understood your technical stack without repeated correction
- Fees remained reasonable relative to scope and service level
- You expect moderate changes, not a major scope redesign
When switching is worth the disruption
Switching can be the right move when the relationship is slowing the program down. Common triggers include slow responses, unclear requests, bloated sample demands, weak SaaS fluency, or a report style that creates more customer questions than it answers.
Consider a competitive process if any of these are true:
| Signal | What it usually means |
|---|---|
| Repeatedly vague evidence requests | The team lacks a clear testing approach |
| Heavy dependence on one senior contact | Delivery risk if staffing changes |
| Report language that buyers struggle to interpret | Low commercial value from the attestation |
| Escalating cost without better service | Poor fit for your current stage |
| Limited understanding of your industry | More explanations, more cycles, more stress |
New teams create real renewal friction
Even if you stay with the same firm, you may not get the same people. That is where many companies get surprised. Fresh auditor preferences can materially change the evidence experience.
According to Codefortynine’s audit renewal insights, new auditor preferences can lead to 20-40% more evidence requests, especially when controls changed. The same analysis notes that 28% of 2025 renewals flagged new evidence gaps because of nuanced privacy interpretation, and working with an auditor that has low team turnover can reduce stress by up to 40%.
That matters for SOC 2 because a renewal can become painful even without a change in firm. A new team may ask for different formats, deeper explanations, or more mapping around privacy and vendor controls.
A practical decision framework
Use this decision sequence before you sign the next engagement letter.
Review the last cycle thoroughly
Ask the people who supplied evidence, not just the executive sponsor.
Questions worth asking:
- Did engineering feel the requests were targeted or repetitive?
- Did security spend time educating the auditors on basic architecture?
- Did the final report answer customer questions cleanly?
- Were there avoidable delays tied to staffing or handoffs?
- Did the firm handle scope changes with discipline?
Test the market before you commit
Even if you are inclined to stay, get a market check. Not to play pricing games. To understand whether your current assumptions about service level, timeline, and specialization are still valid.
Ask candidate firms about:
- Experience with your industry and TSC mix
- How they manage team continuity year over year
- How they structure walkthroughs and sample requests
- Whether they support staged scope changes
- What they expect from the client before fieldwork begins
If you switch, manage the handoff tightly
The mistake is assuming the new firm will “figure it out” from last year’s report. They will not. A strong transition package should include your prior report, control matrix, system description, current scope statement, evidence index, known exceptions, and major environmental changes.
Key takeaway: Auditor switching is not risky by itself. Unmanaged switching is risky.
Stay or switch is really a readiness decision
If your controls are mature, your evidence repository is clean, and your control owners are stable, switching firms is manageable. If your documentation is thin and your operating model depends on institutional memory, continuity may be worth more than a lower fee.
For someone pursuing SOC 2, the right auditor decision is the one that produces a credible report with the least operational drag. That means evaluating the firm like any other critical vendor. On delivery quality, not just brand recognition.
Navigating Common Renewal Pitfalls and Remediation
Even well-run renewals hit issues. The difference between a contained problem and a bad report is usually how quickly the team documents the gap, stabilizes the control, and gives the auditor a coherent remediation story.
This matters for SOC 2 because auditors are not only looking for perfection. They are evaluating whether management understands the control environment, responds appropriately to failure, and can show that exceptions were identified and addressed in a disciplined way.
Pitfall one is untreated prior findings
The worst place to lose credibility is on a repeat issue. If last year’s report noted a gap in access review timing or vendor risk documentation, and the same area breaks again, the auditor will question whether the remediation changed operations or just produced paperwork.
What to do:
- Reconstruct the original root cause
- Show the process change, not only the policy update
- Demonstrate monitoring that would catch recurrence
- Keep dated evidence showing the fix operated during the period
If the prior issue involved a TSC area like Security or Confidentiality, make sure the owner can explain how the revised workflow now prevents or detects the same failure.
Pitfall two is evidence that conflicts with policy
This happens constantly. The policy says quarterly access reviews. The evidence shows one review happened late and one is missing. The policy says all production changes require approval. The emergency deployment trail shows exceptions with no after-the-fact review.
The fix is not to rewrite history. The fix is to align the documentation with reality and address the missed control directly.
A workable remediation pattern:
- Document the exact control failure and affected dates.
- Assess whether this was isolated or systemic.
- Implement the corrective action.
- Decide whether the policy needs revision, the process needs enforcement, or both.
- Present the auditor with the old state, the break, and the corrected state.
Pitfall three is turnover in key control owners
Renewal often slips when the people who know the process leave. The control may still exist, but the evidence chain breaks because ownership was never formalized.
Build around that risk by keeping:
- A current control matrix with named owners
- Backup owners for critical controls
- Stored procedural notes for recurring evidence pulls
- Centralized repositories instead of local knowledge
This is especially important for controls around provisioning, incident response, and vendor review, where a departed owner can leave a big documentation hole.
Tip: A control is not mature if only one person knows how to prove it worked.
Pitfall four is a control failure during the period
Sometimes the issue is real and material. A monitoring control stopped running. Backups were not reviewed. A critical availability process failed for part of the period. The right response is measured, not defensive.
Use this remediation structure:
| Situation | Immediate action | Auditor-facing response |
|---|---|---|
| Missed recurring review | Perform the overdue review, identify impact, set calendar enforcement | Explain the lapse, show catch-up and preventive action |
| Change approvals bypassed | Investigate affected changes, implement emergency review process | Provide scope of issue and updated workflow |
| Vendor review gap | Complete assessment, evaluate contractual and security impact | Show revised vendor governance process |
| Incident handling inconsistency | Document actual response, update runbooks, train responders | Demonstrate lessons learned and control reinforcement |
If the failure touches Availability, Privacy, or another selected TSC, the critical question is whether the breakdown was isolated and whether you can show containment. Auditors can work with an issue that management identified and corrected. They are less comfortable with issues discovered late, described vaguely, or unsupported by evidence.
Pitfall five is discovering scope drift too late
You renewed the report assuming one set of systems was in scope, then fieldwork reveals a new hosting pattern, a newly material vendor, or product functionality that changes how personal data is handled. That is not just an evidence issue. It can alter the report boundary.
When this happens:
- Freeze the facts first
- Decide whether the item belongs in current scope
- Update the system description if needed
- Align with counsel, security, and the auditor on the right representation
- Avoid casual verbal explanations that are not backed by revised documentation
For someone pursuing SOC 2, remediation skill is part of readiness. The ultimate test is not whether your environment is perfect. It is whether your team can identify gaps, correct them, preserve evidence, and keep the renewal credible when normal operational problems appear.
Conclusion From Annual Renewal to Continuous Readiness
The companies that handle soc 2 audit renewal well do not treat it as a yearly scramble. They treat it as a managed control cycle. They plan early, keep scope aligned with the business, collect evidence continuously, and evaluate their auditor relationship with the same discipline they apply to other critical vendors.
That approach saves time, but the bigger benefit is quality. A renewal built on current scope, reliable control owners, clean evidence, and realistic remediation gives customers a report they can trust. It also gives your internal teams a process they can repeat without burning out engineering every audit season.
If your next renewal is coming up, pressure-test the decisions that cause the most pain. Scope only what supports your customer commitments. Fix prior issues before the auditor asks. Standardize evidence handling. Decide whether continuity with your auditor still helps more than it hurts. If you need help comparing firms for the next cycle, SOC2Auditors can help you assess options based on timeline, fit, and delivery quality.
SOC 2 readiness is the primary objective. Renewal is just the annual proof point. When your controls, evidence, ownership, and governance are operating cleanly throughout the year, the audit becomes validation of readiness instead of a search for it.