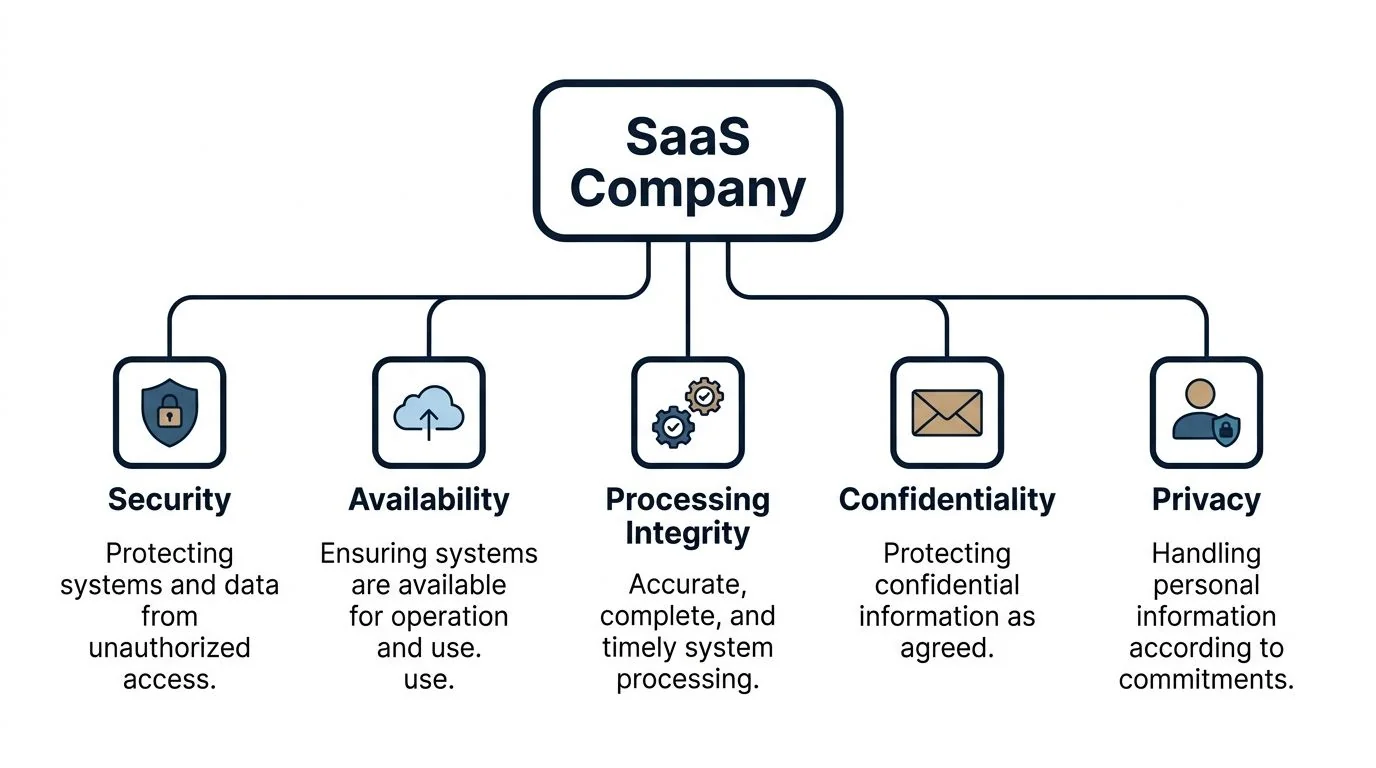
A SOC 2 report is an independent attestation performed by a licensed CPA firm under the American Institute of Certified Public Accountants framework to evaluate whether a service organization’s controls meet the applicable Trust Services Criteria: Security (required), plus optional Availability, Processing Integrity, Confidentiality, and Privacy. For SaaS companies, that matters because buyers do not evaluate your product alone. They evaluate how you secure the systems, people, processes, and vendors behind it.
For teams selling into larger accounts, soc 2 for saas companies is no longer a side project for legal or IT. It sits in the sales path, procurement path, and often the fundraising path. The companies that treat it as a late-stage documentation exercise spend more, move slower, and end up with a report that does less than they expected.
What Is SOC 2 and Why It Is a Market Imperative for SaaS
SOC 2 was introduced by the AICPA and is used to assess whether a service organization has designed and, depending on report type, operated controls that support the Trust Services Criteria. In SaaS, the report is used to answer one question from prospects and auditors: can this company reliably protect customer data and operate its service in a controlled way?
That definition matters because many SaaS teams approach SOC 2 as a badge. Auditors do not audit badges. They audit control design, evidence, and consistency.
Why SaaS companies are prioritizing it
Demand has shifted sharply. SOC 2 adoption among SaaS companies surged by 40% in 2024, and the IT sector accounts for approximately 45% of all SOC 2 certifications globally according to TryComp’s SOC 2 checklist for SaaS startups. That is not just a compliance trend. It is a buying pattern.
If you sell software that stores, processes, or transmits customer data, procurement teams will ask how access is controlled, how incidents are handled, what vendors you rely on, and whether an independent auditor has tested your controls. A clean security questionnaire helps. A current SOC 2 report helps more.
Why this matters for revenue, not just risk
SOC 2 changes how your company is evaluated in deals.
- Customer trust: Buyers use the report to reduce uncertainty before sharing data or integrating systems.
- Procurement speed: A mature report can reduce repetitive security questionnaires and shorten review cycles.
- Internal discipline: Engineering, IT, HR, and leadership align around documented operating practices instead of ad hoc decisions.
Key takeaway: A SaaS company without a defined control environment usually feels the pain first in enterprise sales, not in the audit room.
What strong teams understand early
The best SOC 2 programs start with a business decision, not a policy template. They answer three questions first:
| Question | Why it matters for SOC 2 |
|---|---|
| What products and environments are in scope | Scope determines cost, evidence load, and control complexity |
| Which buyers are asking for the report | Buyer expectations influence Type 1 vs Type 2 and TSC selection |
| Who owns the program internally | SOC 2 fails when nobody owns evidence collection and control maintenance |
A weak start looks the same. The company buys automation software, imports default policies, and assumes the auditor will tell them what matters. That is backwards. Your auditor attests to your controls. The auditor should not be designing your operating model for you.
For SaaS teams, the practical value of SOC 2 is straightforward. It gives prospects independent assurance, forces operational consistency, and creates a repeatable way to answer security diligence. That is why it has become a market imperative rather than a nice-to-have.
Decoding The SOC 2 Report Type 1 vs Type 2
The choice between Type 1 and Type 2 changes your audit timeline, your evidence burden, and how seriously enterprise buyers treat the report. Many SaaS teams get this wrong because they treat it as an audit preference instead of a sales and risk decision.

A Type 1 report assesses whether your controls are designed appropriately at a specific date. A Type 2 report assesses both control design and operating effectiveness over a defined review period. For SaaS companies, that difference affects procurement outcomes. Buyers may accept a Type 1 from an earlier-stage vendor, but security teams at larger accounts usually ask whether the controls have been followed over time.
When Type 1 makes sense
Type 1 is a practical option when the company has formalized controls recently and needs an audit report in market quickly. It gives prospects and customers evidence that the control set exists, the scope is defined, and management has started treating compliance as an operating discipline.
Type 1 usually fits three situations:
- An active deal needs evidence now: Sales cannot wait through a longer observation period.
- Controls are in place but still new: The team needs time to produce clean operating history.
- Leadership wants to validate scope before committing to Type 2: A shorter audit often surfaces documentation gaps, unclear ownership, and weak evidence collection processes early.
There is a real trade-off. Type 1 is faster, but experienced reviewers know it does not answer the harder question. Are the controls being performed consistently, by the right people, with evidence that stands up to testing?
Why Type 2 is the report buyers prefer
Type 2 is usually the target for SaaS companies selling into mid-market and enterprise accounts. It gives customers more than a snapshot. It shows that controls operated over time, which is what procurement, security, and internal audit teams want to see during vendor review.
In practice, Type 2 carries more weight because it tests repeatability. Access reviews need to happen on schedule. Change management needs approvals and retained evidence. Incident response, backups, onboarding, and offboarding cannot exist only in policy form. They need a track record.
That distinction affects deal quality, not just compliance posture.
If your product handles sensitive customer workflows, security criteria and related control expectations often push buyers toward requesting Type 2 instead of accepting a point-in-time report. Teams that want a clearer view of scope decisions should review this breakdown of SOC 2 Trust Services Criteria for SaaS companies.
A practical way to decide
Use your sales motion, control maturity, and buyer pressure to make the call.
| Decision factor | Type 1 | Type 2 |
|---|---|---|
| Buyer expectation | Baseline assurance for near-term diligence | Stronger assurance for enterprise review |
| Audit effort | Lower initial evidence load | Higher evidence load and longer testing period |
| Best fit | Newly formalized program, urgent revenue need | Matureer controls, upmarket sales, renewals |
| What the report proves | Controls are suitably designed on a date | Controls are suitably designed and operated over time |
A common mistake is assuming Type 1 saves money. It can, but only if it satisfies the buyer. If the target account comes back and asks for Type 2 anyway, the company pays for two audit cycles, two rounds of project management, and another stretch of internal evidence collection.
Where SaaS teams misjudge the trade-off
I see two failure patterns repeatedly.
The first is choosing Type 1 because leadership wants speed, even though the pipeline is already full of enterprise prospects that will not accept it. The second is pushing into Type 2 before core controls are stable, which leads to exceptions, cleanup work, and an avoidable hit to credibility with both the auditor and the board.
The better decision is usually straightforward. Choose the report type that matches how you sell, how mature your controls are, and what your target buyers will accept. In soc 2 for saas companies, Type 1 versus Type 2 is rarely a technical debate. It is a budget, timeline, and revenue decision.
Selecting Your Trust Services Criteria for SaaS
Every SOC 2 report includes Security. The other criteria, Availability, Processing Integrity, Confidentiality, and Privacy, are added based on your service, your data handling, and the commitments you make to customers. Here, many SaaS companies either overscope the audit and make life harder, or underscope it and end up with a report that does not answer buyer concerns.
Start with customer promises, not theory
The right scope follows your contracts, architecture, and sales claims.
If your product supports critical workflows and you commit to uptime or resiliency, Availability deserves serious consideration. If your platform transforms or calculates business-critical data and customers care about correct outputs, Processing Integrity may matter. If you handle sensitive business data, source documents, financial records, health data, or customer-uploaded files, Confidentiality is the stronger add-on. If you process personal information in a way that requires detailed privacy commitments, Privacy may belong in scope.
A scope that looks impressive on paper can backfire if your team cannot support it with evidence.
What auditors look for under Confidentiality
For many SaaS companies, Confidentiality is the most practical optional criterion because it maps to buyer concerns around sensitive data handling.
Auditors evaluate encryption controls closely. For SaaS companies handling sensitive customer data, configuration scans verify AES-256 or equivalent for data at rest and TLS 1.2+ with strong ciphers for data in transit across APIs, HTTPS traffic, and inter-service communications, as described in Sprinto’s guide on why SOC 2 matters for SaaS companies.
That matters for SOC 2 because “we encrypt data” is not evidence. Auditors want to see configurations, key management practices, system settings, and documentation that matches production reality.
A practical scoping model
Use this as a starting point:
- B2B application handling standard business data: Start with Security, then add Confidentiality if contracts or customer diligence focus on sensitive records.
- Infrastructure or workflow platform with uptime commitments: Add Availability if reliability is central to the service you sell.
- Fintech or healthtech SaaS: Security plus Confidentiality is the baseline conversation because of the sensitivity of the data involved.
- Data transformation or transaction-heavy systems: Consider Processing Integrity if customers depend on accuracy and completeness of outputs.
- PII-heavy platforms with explicit privacy commitments: Add Privacy only when you are prepared for the added documentation and operational rigor.
What over-scoping looks like
A common mistake is selecting every optional criterion because it sounds stronger in sales. That creates a heavier evidence burden with little commercial upside.
Another mistake is choosing Privacy when the company means Confidentiality. Privacy is not just “we protect personal data.” It involves how personal information is collected, used, retained, disclosed, and handled against stated commitments.
If your team needs a plain-English reference for security criteria and how controls map into a practical security program, that can help before you finalize scope. For a more direct breakdown of the Trust Services Criteria themselves, this guide from https://soc2auditors.org/insights/soc-2-trust-services-criteria/ is a useful companion during scoping.
Tip: Pick criteria that you can defend to buyers and support with evidence. A narrower, credible report is usually better than a broader report full of weak controls.
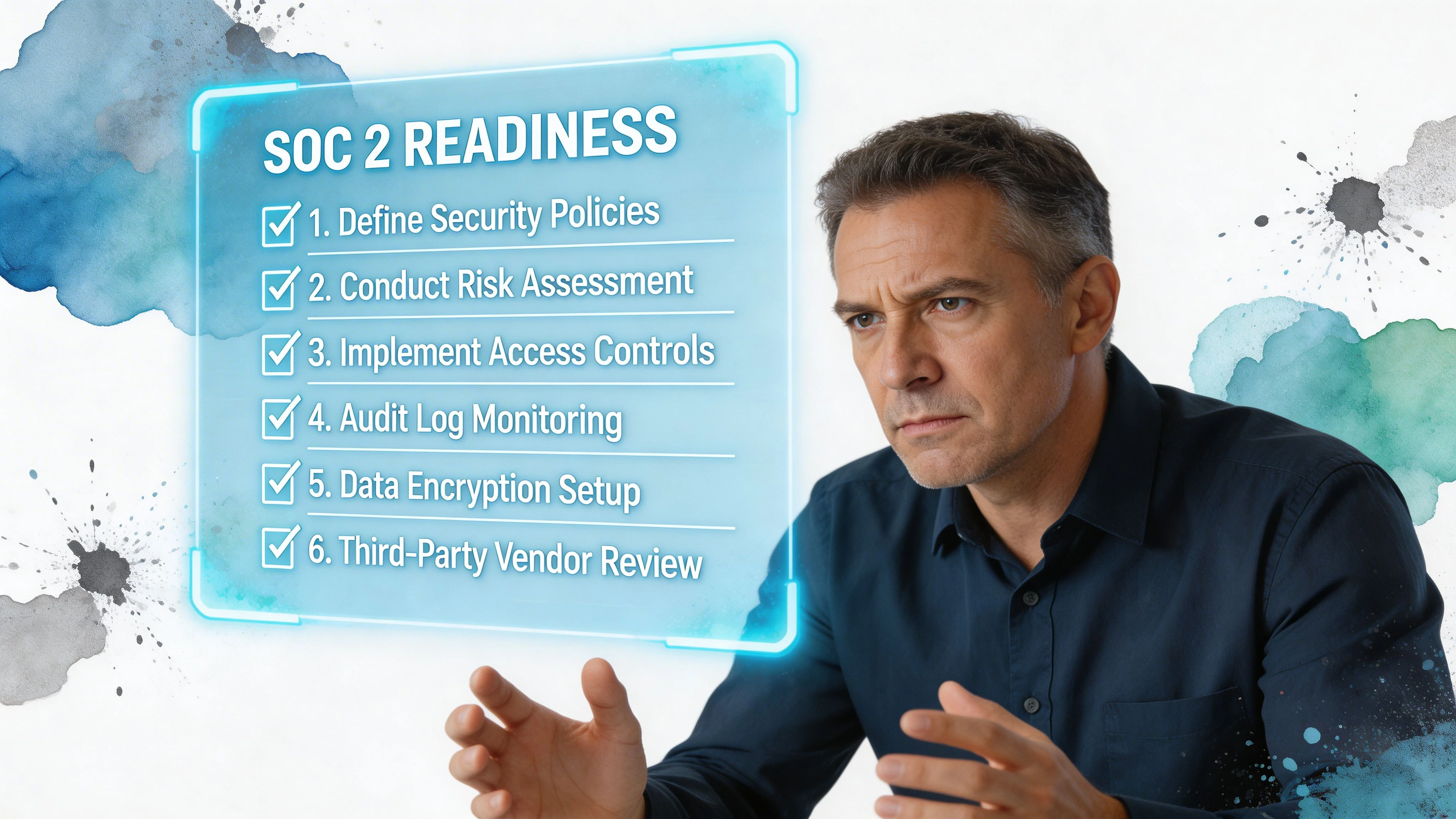
Your Actionable SOC 2 Preparation Checklist
Preparation is where most first-time audits are won or lost. Not in fieldwork. Not in the report draft. In the months before the auditor starts testing. A clean SOC 2 process comes from stable controls, defined ownership, and evidence that already exists because your team works that way.
Define the system boundary
Start by writing down what is in scope.
That includes your production environment, supporting infrastructure, repositories, identity provider, ticketing tools, HR onboarding workflow, and any vendors that materially affect the service being audited. For a modern SaaS stack, that means systems like AWS, Google Cloud, Azure, GitHub, Okta, Jira, Google Workspace, and your endpoint management platform.
If the boundary is vague, everything downstream gets harder. Evidence requests multiply. Engineers argue over ownership. Auditors test systems that never should have been included.
Run a readiness review before the audit
A readiness assessment should look for control gaps, not just policy gaps. The difference matters.
Policies say what should happen. Readiness asks whether it happens and whether you can prove it happened.
Focus on these areas first:
- Access control: MFA enforcement, least privilege, joiner-mover-leaver process, privileged access review
- Change management: pull request approvals, branch protections, deployment approvals, rollback discipline
- Logging and monitoring: audit logs, alert coverage, escalation path, retention
- Incident response: documented process, roles, evidence that incidents would be tracked and reviewed
- Vendor management: inventory, risk review, contracts, subprocessors that matter to the service
Write policies that match operations
SOC 2 policies fail when legal language outruns reality.
If your change management policy says every production change gets formal approval, but your emergency fixes go straight through GitHub and Slack, the auditor will find the mismatch. Good policies are short, operational, and aligned to the systems your team uses daily.
A practical policy set covers information security, access control, incident response, change management, risk assessment, vendor management, acceptable use, and business continuity.
Tip: Use your tooling when writing procedures. If alerts live in Datadog and tickets live in Jira, say that. Generic process language creates evidence problems later.
Implement controls with evidence in mind
SOC 2 controls should leave a trail.
Examples that work well in SaaS environments:
-
Identity and access Okta or Google Workspace for SSO. MFA on all administrative access. Scheduled access reviews with exported evidence.
-
Cloud and infrastructure IAM roles mapped to job function. Encryption enabled where required. Centralized logging for key systems.
-
Code and change control GitHub branch protection rules, required reviews, ticket references tied to production changes.
-
Endpoint and device security MDM enforcement, disk encryption, screen lock, deprovisioning workflow.
-
Incident handling A documented response process plus tickets, post-incident notes, and follow-up actions.
This walkthrough can help teams visualize what a readiness workflow should feel like in practice:
Build an evidence calendar
The easiest SOC 2 audits are boring because evidence collection is routine.
Create a calendar for monthly and quarterly activities such as access reviews, vulnerability review, vendor review, policy acknowledgment, and incident tabletop exercises. Assign an owner for each item. Store outputs in a consistent location. If you use automation platforms, validate the integrations. Do not assume screenshots pulled by software satisfy every request.
Final readiness checks
Before fieldwork starts, confirm these basics:
| Area | Audit-ready signal |
|---|---|
| Scope | Systems, products, and entities are clearly documented |
| Ownership | Every control has an internal owner |
| Evidence | Artifacts are organized and easy to retrieve |
| Exceptions | Known issues are documented with remediation plans |
| Communication | Engineering, IT, HR, and leadership know their role |
A SaaS company becomes audit-ready when controls operate consistently enough that evidence collection feels administrative, not investigative. That is the standard to aim for.
Budgeting for SOC 2 Timelines and Costs in 2026
Audit fees are usually the smallest number leadership fixates on and the least useful one for planning. Budgeting needs to account for internal labor, remediation, tooling, testing, and the cost of slowing product and security work while the team assembles evidence.
Start with scope, report type, and control maturity. Price shopping before those decisions usually produces a neat proposal and a messy project.
What the external audit may cost
The external attestation fee can vary widely. Broader auditor market data shows pricing from $15,000 to $400,000+ and timelines from 3 to 20 months, depending on scope, complexity, and firm selection, as discussed in this overview of how much a SOC 2 audit can cost.
That spread exists for a reason. A single-product SaaS company running on a standard cloud stack with a narrow scope should not budget like a multi-entity business supporting enterprise customers, custom infrastructure, and a long vendor chain. I have seen teams overbuy audit firm brand, and I have seen others choose the cheapest option and spend the difference later on delay, rework, and scope confusion.
The hidden budget lines that change the total
The audit invoice covers attestation. It does not fix weak controls, clean up access, or produce months of operating evidence.
| Cost area | What usually drives it |
|---|---|
| Internal staff time | Engineering support, evidence collection, security reviews, policy updates |
| Readiness support | Gap assessment, remediation planning, control mapping |
| Software | Compliance automation, ticketing, monitoring, identity, device management |
| Remediation | Logging changes, access cleanup, vendor reviews, process redesign |
| Security testing | Activities required by your controls or expected by customers |
Budgets frequently break here. Finance approves the audit fee. The team then discovers that engineering needs to configure logging, IT needs to tighten endpoint controls, HR needs documented onboarding and offboarding evidence, and security needs to run reviews on a recurring schedule. None of that is optional if the controls are in scope.
Plan timelines as operating windows, not audit windows
Quoted fieldwork dates are not the project timeline. They are one slice of it.
A realistic plan includes scoping, readiness work, remediation, evidence collection, control stabilization, the observation period for Type 2, auditor testing, follow-up questions, and report finalization. If controls are still changing during the observation period, the calendar slips. If ownership is unclear, the calendar slips again.
For early-stage SaaS companies, the biggest timeline risk is not auditor availability. It is internal inconsistency. Controls exist on paper, but reviews are skipped, tickets are incomplete, or evidence lives in five different systems.
Why the spend usually makes business sense
Buyers, procurement teams, and security reviewers treat SOC 2 as a trust signal. As noted earlier, companies without recognized certifications often lose deals. The practical question is not whether SOC 2 costs money. It does. The practical question is whether the company wants that cost to be controlled and time-bound, or paid later through delayed sales cycles, extra questionnaires, and avoidable rework.
The strongest budgeting conversations focus on efficiency. Which Trust Services Criteria are needed. Which systems belong in scope now. Which remediation items must be fixed before fieldwork, and which can be documented and scheduled. Those decisions shape both spend and speed far more than the first audit quote.
Budgeting advice: Build the budget around internal ownership, remediation effort, and evidence collection first. Then choose the auditor that fits the scope and pace of the business. That sequence prevents the most expensive mistake in SOC 2 projects: buying an audit before the company is ready to pass it.
How to Select Your SOC 2 Auditor
Auditor selection is the highest-impact decision in the process. It affects price, timeline, report quality, buyer confidence, and how much pain your team experiences during fieldwork. Yet most SaaS companies choose with little useful data.
The market makes this harder than it should be. Practical guidance on comparing firms is thin, even though real differences exist in pricing, timeline expectations, responsiveness, and experience with modern SaaS environments.
Why this decision is harder than it looks
One of the clearest gaps in the market is the lack of transparent comparison guidance for audit firms, including verified pricing ranges of $15K to $400K+ and timelines of 3 to 20 months, plus meaningful differentiators between specialist firms and Big Four options, as noted by IS Partners on SOC 2 for SaaS.
That matters for SOC 2 readiness because the wrong auditor does not just create inconvenience. It can force scope resets, prolong evidence requests, and leave you with a report that buyers find less useful than expected.
SOC 2 Auditor Comparison Specialist Firm vs Big Four
| Factor | Specialist SOC 2 Firm | Big Four (PwC, Deloitte, etc.) |
|---|---|---|
| Typical fit | Startups and mid-market SaaS, focused scopes, fast-moving teams | Larger organizations, multi-entity environments, broader assurance needs |
| Cost profile | Often more economical for focused audits | Often higher, especially with added coordination layers |
| SaaS tooling familiarity | Usually stronger with modern stacks like cloud-native infra, GitHub, Okta, automation platforms | Varies by team and practice |
| Hands-on guidance | Often more operational and accessible during audit coordination | Can be more formal and structured |
| Brand recognition | Usually sufficient for most SaaS buyers if the report is solid | Strong recognition with large enterprise procurement |
| Process flexibility | Often more adaptable for first-time audits | Often more standardized |
What to ask before signing
A good selection process sounds less like procurement and more like due diligence.
Ask questions that expose how the firm operates:
- How many SaaS audits like ours do you handle?
- What does evidence collection look like for our stack?
- Who will manage day-to-day communication?
- How do you handle scope changes midstream?
- What delays most often affect your clients?
- What distinguishes your Type 1 and Type 2 process?
The answers tell you more than logo recognition.
What experienced teams screen for
Strong auditor selection comes down to four things:
-
Scope fit A firm that understands your environment reduces avoidable back-and-forth.
-
Communication quality Slow or unclear request handling can derail already-busy engineering teams.
-
Report credibility Buyers care that the report is clean, relevant, and issued by a recognized CPA firm.
-
Process realism Firms that oversimplify the work often create downstream surprises.
Some companies do need the brand comfort of a large accounting firm. Many do not. If your environment is a focused SaaS stack and your priority is a practical, efficient audit, a strong specialist firm may be the better fit.
The key point is simple. Do not choose an auditor based only on the first proposal that lands in your inbox. In soc 2 for saas companies, audit quality is part of the product you are buying.
Common SOC 2 Pitfalls and How SaaS Companies Avoid Them
The failures that delay SOC 2 are not dramatic. They are ordinary operational mistakes that compound under audit pressure.
The scope that kept expanding
A SaaS team starts with one customer-facing product in scope. During readiness, someone adds an internal analytics environment. Then a legacy admin tool gets pulled in because it touches production data. Then a side service with shared credentials gets noticed during fieldwork.
The audit does not fail. It just gets slower, messier, and more expensive.
Avoid this by documenting a clear system boundary and testing every “include it anyway” decision against a simple question: does this materially support the in-scope service or the selected criteria?
The policy set nobody followed
Another team buys templates, publishes them, and checks the box. The access control policy requires formal quarterly reviews. Nobody runs them. The incident response policy says incidents are tracked centrally. Engineers still handle issues in chat without tickets.
Auditors spot these gaps fast because policies create testable expectations. If you need a reference point for structure and level of detail, reviewing a detailed security policy can help teams calibrate what “documented” should look like before writing their own.
The evidence scramble
This one is common in engineering-led organizations. Controls exist, but evidence is scattered across Slack, GitHub, Jira, cloud logs, and someone’s local notes. Two weeks before fieldwork, the compliance owner starts chasing screenshots and exports.
That is not a tooling problem first. It is an operating rhythm problem.
Use recurring review cadences, standard storage locations, and named owners. Evidence should accumulate as part of the month, not as a panic project before fieldwork.
Practical warning: If evidence only appears when the auditor asks for it, your controls are probably not mature enough yet.
The one-time audit mindset
Some companies act like SOC 2 ends when the report is issued. Then access reviews slip, vendor reviews stop, and exceptions pile up before renewal season.
The better approach is continuous. Treat controls as ongoing operating requirements tied to onboarding, engineering change, incident response, and vendor oversight. SaaS companies that do this find the second cycle far easier than the first.
From Readiness to Revenue With Data-Driven Auditor Selection
A strong SOC 2 outcome comes from a chain of practical decisions. Choose the right report type. Scope the right Trust Services Criteria. Build controls that match how your SaaS company operates. Gather evidence in a repeatable way. Then choose an auditor who fits your environment, budget, and deadlines.
That last step is where many solid programs lose momentum. Auditor selection is still too opaque. Firms differ materially in price, timing, support style, and how well they handle modern SaaS stacks, but most buyers still compare them with partial information and generic proposals.
SOC2Auditors exists to fix that problem. The platform helps teams compare firms using verified pricing ranges, timeline benchmarks, satisfaction data, responsiveness metrics, and side-by-side fit criteria. Instead of guessing whether a specialist firm or a larger accounting firm is right for your environment, you can make a structured choice based on your product scope, industry, budget, and target audit timeline.
For companies pursuing soc 2 for saas companies, that matters because the auditor is not just a vendor. The auditor affects how quickly you get to a usable report and how much internal friction the process creates. Better matching means fewer delays, better-fit expectations, and a cleaner path to enterprise deal readiness.
SOC 2 only helps the business when the report arrives on time, answers buyer concerns, and reflects a control environment that can stand up to scrutiny. This connection is central to SOC 2 audit readiness. Readiness is not just having policies and screenshots. It is being operationally prepared, correctly scoped, and paired with an auditor who can validate your controls without turning the process into avoidable rework.
If you are comparing firms now, SOC2Auditors.org can help you narrow the field with verified cost and timeline data, then get matched with auditor options that fit your SaaS company’s scope and readiness level.