If you are preparing for a first SOC 2 audit, vendor management becomes painful the moment you realize how many third parties touch your systems, code, customer data, or uptime. The requirement is broader than procurement and narrower than generic risk management. It is the documented process for identifying vendors in scope, assessing their risk, setting requirements before engagement, monitoring them during the relationship, and closing them out cleanly when the relationship ends.
Most startups do fragments of this. Legal signs an MSA. Security reviews a few key tools. Engineering grants access. Finance pays invoices. SOC 2 forces those fragments into one operating process with evidence. That matters because auditors do not care that your team “knows the vendors.” They care that you can prove who the vendors are, why they were approved, what controls were reviewed, what contractual terms apply, who owns each relationship, and how changes are tracked over time.
For lean teams, the hard part is not understanding the principle. It is building a version of the process that is strong enough for audit without creating a full-time bureaucracy. That is where most of the cost sits. The good news is that soc 2 vendor management requirements are manageable if you build them around risk, not around paperwork volume.
Defining SOC 2 Vendor Management
SOC 2 vendor management is the set of policies, procedures, and records a company uses to assess and manage risks from vendors and business partners that affect its systems or data relevant to SOC 2. In the AICPA Trust Services Criteria, this sits under CC9.2, which states that “The entity assesses and manages risks associated with vendors and business partners” according to Atlas Systems’ summary of the criterion.
For a company pursuing SOC 2, that definition has direct implications.
A vendor is not your cloud host. It can include payroll, customer support tooling, observability platforms, identity systems, contractors with code access, backup providers, and any other third party whose failure or misuse could affect your controls. The formal expectation under CC9.2 includes four establishment elements captured in the same Atlas Systems summary: defining scope and compliance needs, performing due diligence, negotiating enforceable contract terms, and assigning responsibility for ongoing risk management.
That is why soc 2 vendor management requirements matter. They are not an administrative side quest. They are how you show an auditor that your security posture extends beyond assets you directly control.
What auditors care about
Auditors look for three things first:
- Completeness: Do you have a reliable inventory of vendors in scope?
- Consistency: Did you assess vendors using a repeatable method rather than ad hoc judgment?
- Follow-through: Can you show monitoring, issue handling, and offboarding evidence?
If one of those is weak, the rest of the program tends to unravel.
Key takeaway: Vendor management in SOC 2 is supply chain risk management with audit evidence attached.
Why startups struggle with it
Startups infrequently fail because they have no vendors. They fail because ownership is scattered. Procurement owns contracts, IT owns access, security owns questionnaires, legal owns DPAs, and nobody owns the full lifecycle.
That fragmentation creates predictable problems. A tool gets approved without a security review. A former vendor still has an active SSO integration. A critical provider’s SOC report expires and no one notices. SOC 2 turns those operational loose ends into control gaps.
Mapping Vendor Management to SOC 2 Trust Services Criteria
Vendor management sits most explicitly in CC9.2, but it affects every Trust Services Criteria category that your report includes. If you only think about vendor management as “collecting SOC reports,” you will miss how auditors evaluate third-party dependencies across your control environment.
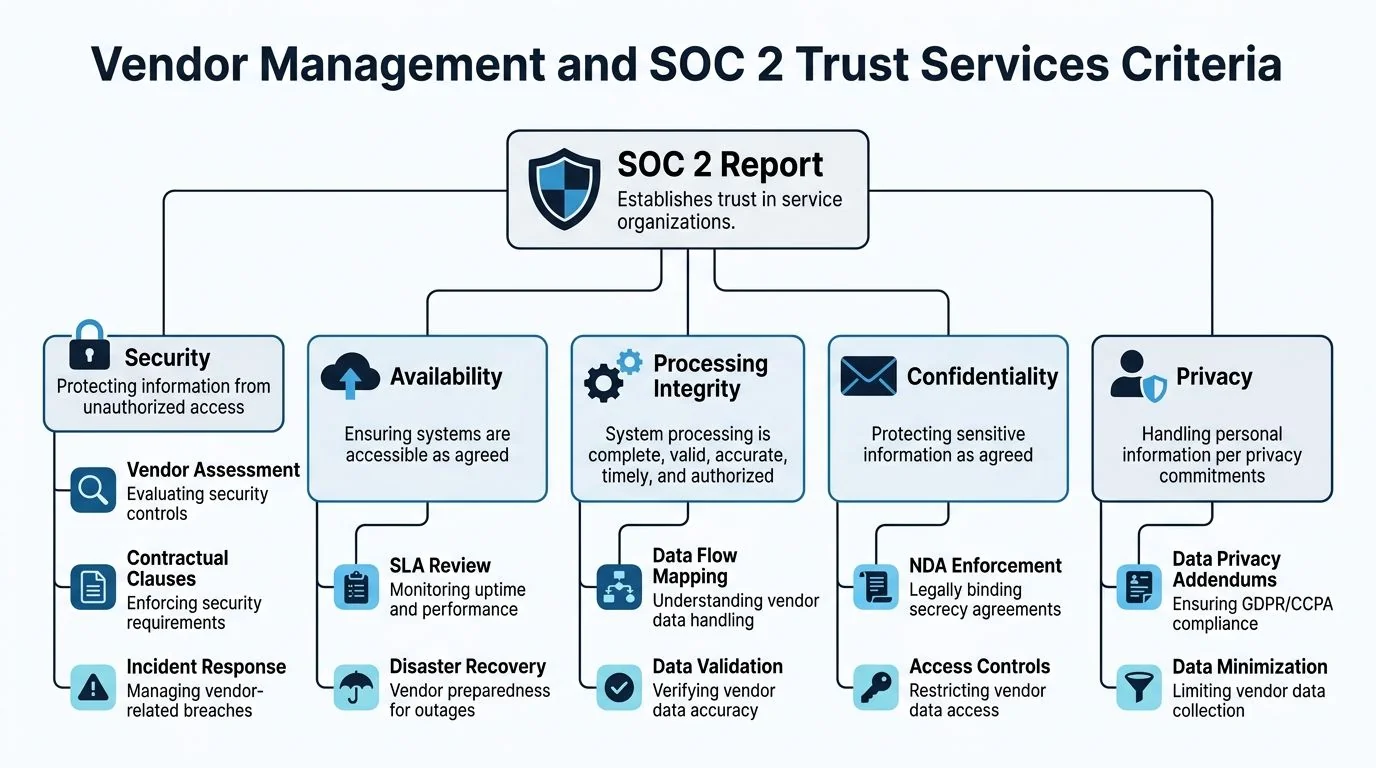
CC9.2 in plain English
The AICPA requirement under CC9.2 is straightforward: your company must assess and manage risks associated with vendors and business partners. The Atlas Systems breakdown ties that requirement to the full vendor lifecycle, from selection through offboarding, and notes that supply chain vulnerabilities affected a significant number of organizations with disruptions, as reported by the same source summary. It also states that ongoing monitoring requires periodic reassessments and that controls map directly to the five Trust Services Criteria. That is the reason this control gets so much audit attention. Vendor risk is not isolated. It is embedded in your broader control design.
A primer on the criteria themselves is SOC2Auditors’ guide to the SOC 2 Trust Services Criteria.
How vendor controls map to each criterion
A practical way to think about this is to map a vendor decision to the control objective it supports.
| Trust Services Criteria | What the vendor question looks like in practice |
|---|---|
| Security | Does this vendor have access to systems or data, and what controls limit that access? |
| Availability | If this vendor goes down, do you lose service delivery or key internal operations? |
| Processing Integrity | Does this vendor process, transform, sync, or validate important data? |
| Confidentiality | Does this vendor handle sensitive non-public information under contractual restrictions? |
| Privacy | Does this vendor collect, use, store, or dispose of personal information? |
Security is relevant. The others depend on your report scope and how the vendor supports your service.
The four elements auditors expect to see
The CC9.2 framework becomes more usable when broken into its operating parts.
Establish requirements before approval
Before a vendor is approved, define the basics. Scope of services, product specifications, roles, responsibilities, compliance needs, and service levels need to be clear. A lot of startups skip this because they buy fast and sort out control expectations later.
That creates friction in audit because the contract file does not show what security or operational standard the vendor was supposed to meet.
Perform due diligence before access
Due diligence is not one document. It is a set of checks matched to the vendor’s risk. For higher-risk vendors, that includes a security questionnaire, review of their SOC report if they have one, a check of business continuity posture, and a look at whether the service model introduces subservice organizations or data transfer issues.
If you cannot explain why the diligence depth matched the vendor’s risk, the process looks arbitrary.
Put enforceable terms in the contract
Many good programs break down at this stage. Teams review a vendor’s security but fail to contract for what matters. The Atlas Systems summary calls out examples that matter for SOC 2, including right-to-audit clauses, incident notification windows, data return or deletion at termination, and SLAs.
An auditor may not read every legal clause line by line, but they will sample contracts and test whether the required control language is present.
Practical tip: If legal insists on a standard paper process, give them a short security addendum template with required terms. That keeps negotiations faster and evidence cleaner.
Assign ownership and monitor over time
SOC 2 does not treat vendor approval as a one-time event. The same Atlas Systems summary notes periodic reassessments, performance tracking, incident monitoring, and evidence retention. In practice, that means every in-scope vendor needs an internal owner, a current risk tier, and a trigger for re-review.
Without named ownership, controls decay unnoticed. No one knows who should chase the updated SOC report, verify a breach notice, or confirm access was revoked at termination.
Building Your Risk-Based Vendor Management Program
Most companies do not need a complex third-party risk platform on day one. They need a working system that can survive audit sampling. Start with a centralized inventory, a basic tiering model, and a clean intake path.

Start with the inventory, not the questionnaire
A 2023 Linford analysis of 50+ SOC 2 reports found 28% of exceptions tied to undocumented access scopes, which increased remediation timelines by 40-60 days according to Linford & Co.’s vendor management analysis. That finding matches what shows up in practice. Teams jump to sending questionnaires before they have a defensible list of who the vendors are and what each one can access.
Your inventory should include, at minimum:
- Vendor name: The legal entity, not just the product nickname.
- Service description: What business function the vendor supports.
- System or data access: Customer data, production systems, privileged admin, code repos, employee data, or none.
- Risk tier: High, medium, or low.
- Owner: The employee accountable for the relationship.
- Status fields: Assessment date, contract date, renewal date, report status, and offboarding date when applicable.
For an early-stage company, Google Sheets or Airtable can work. For a larger environment, a GRC tool or vendor risk platform may make sense. The right choice depends less on maturity theater and more on whether the evidence is complete, current, and easy to retrieve.
Use a simple tiering model
The fastest way to waste time is to assess every vendor as if it were equally risky.
Use risk tiers that reflect real exposure:
| Tier | Typical profile | Review approach |
|---|---|---|
| High | Direct access to customer data, production systems, privileged admin, code, or critical service delivery | Full due diligence, contract review, recurring reassessment |
| Medium | Internal business tools with limited sensitive access or operational impact | Focused review and documented rationale |
| Low | Minimal or no system access and low effect on SOC 2 scope | Lightweight review and inventory entry |
Examples help. AWS, Azure, payroll processors, identity providers, MSPs, and key SaaS systems land high. Design tools may be medium if they store internal content but do not touch customer data. Office services are low.
Document the access scope before approval
Here, CC3.4 becomes operational. The requirement is not only to know that a vendor exists, but to document what changed in your control environment by bringing them in. If a vendor will connect to your codebase, ingest logs, or get SSO with admin privileges, that scope needs to be recorded before onboarding.
Many teams now include specialized reviews for code-adjacent vendors. If a contractor platform, AI coding assistant, or development service touches repositories or build pipelines, a focused technical review can save significant downstream cleanup. For teams evaluating those kinds of integrations, this guide on an AI code security audit is an example of the level of scrutiny code-access vendors warrant.
What works: One intake form used by procurement, IT, and security. What does not: Slack approvals, side emails, and “we’ll document it later.”
Keep questionnaires scoped and reusable
Do not send a large security questionnaire to every vendor. That slows procurement and creates review fatigue.
Build a short standard set for medium-risk vendors and a deeper set for high-risk vendors. If you need a starting point, this vendor security questionnaire guide provides a practical structure you can adapt.
Later in the process, a short training video can help align internal owners on what “good” vendor intake looks like before audit season.
Spreadsheets versus tools when budget is tight
The financial burden becomes real at this point.
Spreadsheets are cheap and flexible. They work when the vendor count is manageable, ownership is clear, and one person can enforce updates. They fail when multiple teams edit the file, documents live in scattered folders, and reassessment dates start slipping.
Dedicated tools reduce chasing and improve evidence consistency, but they only pay off if the process is mature enough to use them properly. Buying a platform before you define ownership, tiering, and approval gates automates confusion.
A lean rule of thumb works. Use a spreadsheet when the process is still being shaped. Move to a tool when the manual tracking burden starts causing missed reviews, duplicate requests, or unreliable evidence.
The Vendor Lifecycle From Onboarding to Offboarding
A vendor program only becomes real when you follow one vendor all the way through the lifecycle. High-risk vendors expose where the process is strong and where it is performative.
Take an example. Your company wants to onboard a payroll and HR platform with employee PII, finance integrations, and privileged admin access for parts of the people team. That is not a procurement task. It is a control chain.
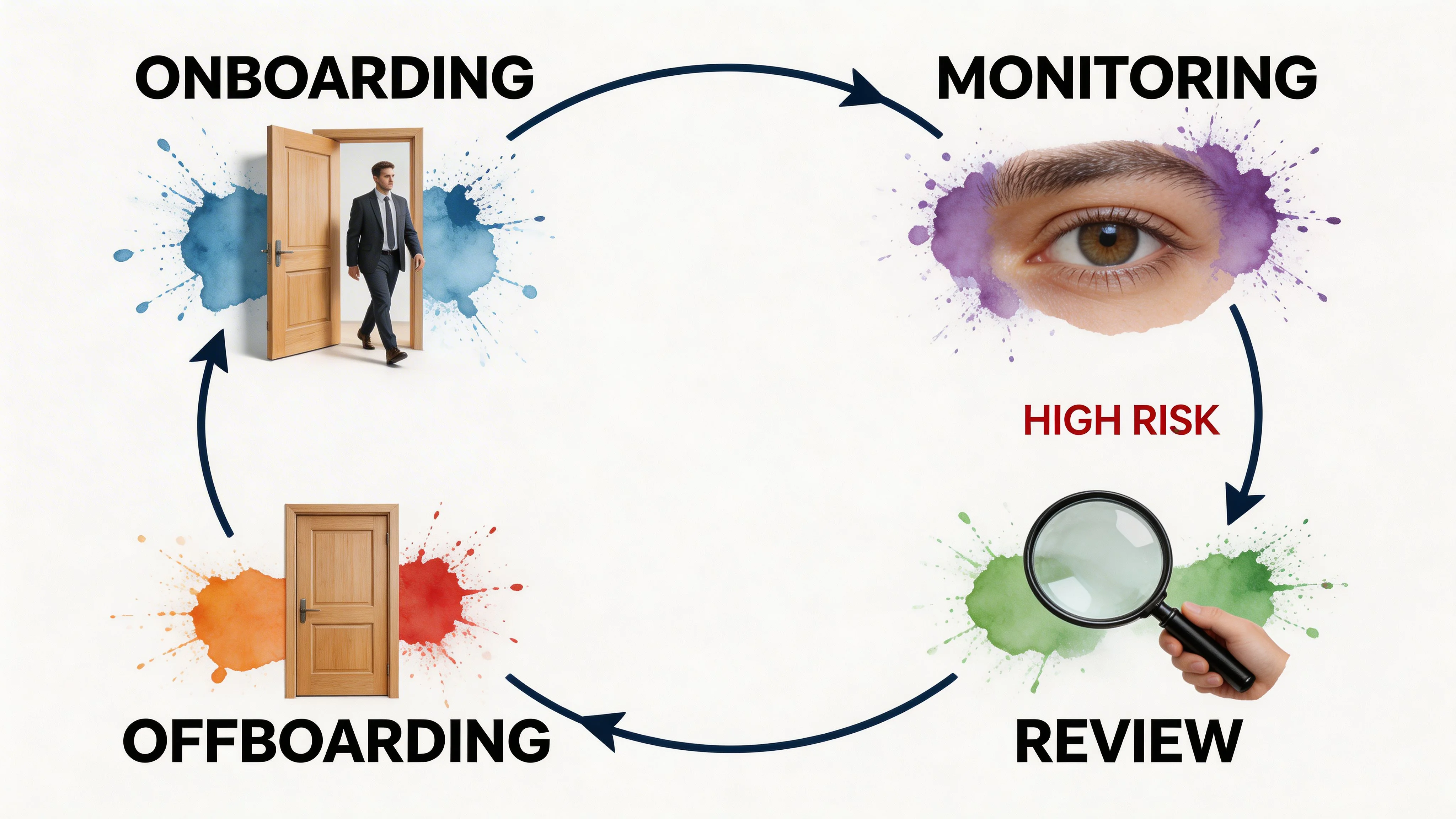
Due diligence before signature
The first gate is due diligence. For a high-risk vendor, review the security questionnaire, validate their SOC report if available, and check how they handle continuity, incident response, and access control.
Here, many teams underestimate the operational burden. The Vendr compliance guide notes that organizations using ~120 SaaS tools have to maintain inventories and periodic assessments, while guidance on the ROI of that oversight is missing. The same source also highlights the challenge of sustaining the process at scale without significant overhead, when compliance requirements contribute to vendor churn in mid-market environments, as summarized in Vendr’s SOC 2 compliance guide.
A practical response is to reserve heavy diligence for high-risk vendors and accept lighter evidence for low-risk ones. Trying to run deep review on every tool burns time without reducing much risk.
Contracting terms that matter
Once the vendor clears diligence, contract language needs to back it up.
For SOC 2 purposes, the most relevant clauses include:
- Incident notification: A defined notice window if the vendor experiences a security event affecting your data or service.
- Right to audit or review evidence: Even if rarely used, it gives legal footing for evidence requests.
- Data handling obligations: Restrictions on use, retention, and disclosure.
- Return or deletion at termination: You need an end-state, not just a cancelled invoice.
- Service levels: Availability expectations when uptime matters to your control environment.
Startups over-negotiate low-risk vendors and under-negotiate high-risk ones in this area. Tie the legal effort to the risk tier.
Onboarding without creating hidden risk
The onboarding step is where technical shortcuts create future findings.
Access should be provisioned to the minimum needed, integration points should be documented, and the internal owner should confirm what data the vendor will receive. If the vendor needs SSO, API keys, admin rights, or repository access, that approval path should be captured.
For vendors with elevated privileges, involve the system owner and security owner together. A surprising number of audit issues come from a vendor being approved commercially but onboarded technically through an informal path.
Tip: Treat vendor onboarding like employee onboarding. If access and approvals are not standardized, the control will drift.
Monitoring and re-review
Monitoring should match risk. High-risk vendors need a defined reassessment cadence, updated report collection, incident review, and checks against service commitments. Lower-risk vendors need less.
The common mistake is to monitor only after something goes wrong. Auditors are more interested in whether your process would have caught drift even if no incident occurred.
Offboarding is where many programs fail
Offboarding is the weakest part of soc 2 vendor management requirements because it is operationally messy. Contracts end. Business owners leave. Integrations remain. Data lingers in archived systems.
A defensible offboarding record should show that access was revoked, data return or deletion requirements were addressed, and the relationship was marked closed in the inventory. If the vendor had privileged access or sensitive data, keep proof.
That proof can be simple. A deletion confirmation, ticket closure, access removal screenshot, or contract termination record is enough if it is consistent and retained.
Required Evidence and Common Audit Gaps
During fieldwork, auditors do not want your philosophy on vendor risk. They want artifacts. If your process is real, you should be able to produce evidence for a sample of vendors across risk tiers.
Konfirmity’s SOC 2 KPI summary notes that 95% vendor compliance rates are a benchmark for passing Type 2 audits, with auditors looking for items such as 100% quarterly access reviews for privileged accounts, MTTR for vendor vulnerabilities under 4 hours, and evidence of offboarding access revocation within 24 hours. The same summary states that weak vendor controls contribute to 15-30% of audit findings in this area, captured in Konfirmity’s SOC 2 metrics and KPIs guide.
That is why evidence discipline matters. A control can exist in policy and still fail in testing if the records are inconsistent.
What auditors usually request
If your repository is disorganized, start by understanding the basics of what is an audit trail. Vendor management evidence lives or dies on traceability. The auditor should be able to follow a clean path from vendor intake to approval to monitoring to exit.
SOC 2 Vendor Management Evidence and Common Gaps
| Control Area | Required Evidence Examples | Common Audit Gap | |---|---| | Vendor inventory | Central list of in-scope vendors, service descriptions, risk tiers, owners, assessment dates | Inventory is incomplete, outdated, or missing vendors discovered through AP or SSO logs | | Risk classification | Documented tiering criteria and assigned tier per vendor | Tiers assigned without rationale or not updated when access changed | | Due diligence | Completed questionnaires, SOC reports, review notes, approval records | Reviews happen informally over email with no final decision record | | Access scope review | Documentation of data types, systems touched, privilege level, integration method | Vendor approved without documented access scope | | Contract controls | Executed MSA, DPA, SLA, security addendum, breach notice and deletion terms | Security terms discussed but not included in signed agreements | | Ongoing monitoring | Reassessment records, updated reports, incident logs, review tickets | No evidence that monitoring occurred during the audit period | | Privileged access reviews | Quarterly review records for vendor-related privileged access | Reviews are partial, late, or cannot be tied back to named vendors | | Issue management | Exceptions log, remediation plans, risk acceptance approvals | Findings identified but no owner or closure evidence | | Offboarding | Access revocation records, deletion confirmation, termination checklist | Contract closed but access or retained data not verified | | Ownership | Named internal owner for each vendor and evidence of accountability | Shared mailbox ownership or “Security team” listed with no individual accountable |
The gaps that create avoidable findings
Missing linkage between documents
A company may have the inventory, a contract folder, and a questionnaire folder, but no way to tie them together. That slows sampling and makes controls look ad hoc. Use a vendor ID, a standardized folder name, or a shared ticket reference.
Evidence that exists only in chat
Slack approvals are not evidence unless retained and organized in a repeatable way. The same goes for verbal approvals in procurement meetings.
Annual reviews that never happened on time
A lot of teams set a review cadence they cannot maintain. Auditors notice this. It is better to set a realistic frequency by tier and hit it consistently than promise a more aggressive schedule that slips.
Best practice: Build the evidence path first, then optimize the workflow. A clumsy but complete process passes more than an elegant process with missing records.
Offboarding treated as an IT-only task
Vendor offboarding needs IT, security, legal, and the business owner. If one group assumes another handled data deletion or contract closure, the evidence trail breaks.
Managing Subservice Organizations and Your Digital Supply Chain
One common mistake in soc 2 vendor management requirements is assuming your diligence ends once you collect your direct vendor’s SOC report. It does not. Your vendor may rely on other critical providers, and those relationships can materially affect your risk.
Subservice organizations are significant in this context.
Why this matters in audit
If a vendor hosts its platform on a cloud provider, relies on a managed data center, or outsources a sensitive function, part of your effective control environment sits downstream from the contract you signed. Auditors expect companies to understand that dependency chain for high-risk vendors.
This does not mean you must audit every fourth-party yourself. It means you must know where the major dependencies sit and how they are addressed in the vendor’s control reporting and contract commitments.
What to review in a vendor SOC report
When you review a vendor’s SOC report, pay close attention to the section describing subservice organizations.
There are two practical scenarios:
- Inclusive approach: The report includes relevant controls at the subservice organization within the scope described by the report.
- Carve-out approach: The report excludes those controls and assumes certain complementary controls or external reliance.
For your team, the implication is simple. If a critical dependency is carved out, do not assume the report covers that risk. Ask the vendor how they monitor that provider, what contingency plans exist, and whether additional evidence is available.
A lightweight downstream review model
You do not need a large fourth-party risk program to be credible. For high-risk vendors, use a short downstream check:
| Downstream review question | Why it matters |
|---|---|
| Does this vendor rely on critical cloud, hosting, or MSP providers? | Reveals concentration and availability risk |
| Are those dependencies named in their SOC report? | Confirms whether the reliance is transparent |
| Is the treatment inclusive or carved out? | Tells you how much control coverage the report provides |
| How does the vendor monitor those providers? | Shows whether they manage their own supply chain |
| Could failure of that dependency affect your service or data? | Helps determine whether compensating controls are needed |
What works for lean teams
A practical approach is to apply downstream review only to vendors that are high-risk. Do not create a full subservice review ritual for every low-impact tool.
Ask for clear answers to a few questions. Note the dependencies in your inventory. Save the relevant SOC report excerpt or vendor response. If a dependency is critical, capture the compensating control on your side, such as backup export capability, redundancy, or incident escalation procedures.
This is one of those areas where mature companies look mature. Not because they assess everything, but because they know where concentration risk sits and can explain how they manage it.
Turning Vendor Management into a Competitive Advantage
The fastest way to make vendor management expensive is to treat every vendor the same and every document as equally important. The fastest way to make it effective is to run it as a risk-based operating process tied to real business dependencies.
For startups and mid-market teams, the winning pattern is simple:
- Keep one inventory: If it is not in the inventory, it is not approved.
- Tier by real risk: Data access, system criticality, and business impact should drive review depth.
- Standardize the intake path: Security, legal, procurement, and IT should all work from the same approval record.
- Focus legal effort where it counts: High-risk vendors need stronger terms and clearer offboarding obligations.
- Make evidence retrieval easy: A folder structure, ticketing model, or GRC workflow should let you answer auditor samples quickly.
There is a commercial upside. Enterprise buyers ask how you manage third-party risk, not whether you have a SOC 2 report. A clean vendor program gives your sales team better answers during security review and reduces the scramble when customers ask about subprocessors, contract controls, or dependency monitoring.
If you are selecting an audit firm, it helps to compare how different firms test vendor controls for first-time audits and lean compliance teams. SOC2Auditors.org is one option that lets companies compare audit firms on practical factors like timelines, pricing ranges, and Type 1 versus Type 2 fit without starting with direct sales outreach.
A strong vendor management program is not busywork. It is how you keep compliance effort proportional to risk, avoid avoidable remediation, and show customers that your controls extend beyond your own walls. Further, it is a direct part of SOC 2 audit readiness. If your vendor inventory is complete, your high-risk reviews are documented, your contracts contain the right terms, and your monitoring and offboarding records are easy to produce, you make fieldwork cleaner and your path to a defensible SOC 2 report shorter.