A SOC 2 exception is a documented instance where a specific control, as described by a service organization, failed to operate effectively during the testing period of a SOC 2 audit. A qualified opinion is an auditor’s formal conclusion, stated in their report, that the collective impact of one or more exceptions is material and significant enough to cast doubt on the organization’s ability to meet one or more of the applicable AICPA Trust Services Criteria (TSC). While exceptions are factual findings from testing, a qualified opinion represents the auditor’s professional judgment on the overall reliability of the control environment. For anyone pursuing SOC 2, understanding this distinction is fundamental; an exception is a data point requiring remediation, whereas a qualified opinion is a material finding that can impact customer trust and requires a formal, strategic response.
Decoding Exceptions and Qualified Opinions in SOC 2
In a SOC 2 audit, an exception is a factual finding documented by the auditor when a control fails to operate as designed. For example, if a company’s control description states that all new hires must complete security awareness training within 30 days of their start date, and an auditor finds evidence that one new hire completed it on day 35, that is an exception. It is a specific, testable deviation from a stated control. A qualified opinion, conversely, is the auditor’s formal conclusion in Section I of the report. It is issued when the auditor determines that exceptions, either individually or in aggregate, are material enough to prevent the organization from achieving one or more of its service commitments based on the Trust Services Criteria.
Why This Distinction Matters for SOC 2 Compliance
For a company undergoing a SOC 2 audit, distinguishing between an exception and a qualified opinion is critical for risk management and communication. An exception is a manageable control failure that needs to be addressed through remediation. A qualified opinion, however, signals a significant breakdown in the control environment that directly impacts the trustworthiness of the system. A few isolated exceptions in a report with hundreds of controls are common and often acceptable to customers. A qualified opinion, however, requires a formal explanation to stakeholders and can impede sales cycles.
A qualified opinion is the auditor’s way of stating: “We have audited the service organization’s description of its system and the suitability of the design and operating effectiveness of its controls, and we conclude that the description is fairly presented and the controls are suitably designed and operated effectively, except for the material effects of the matters described in the Basis for Qualified Opinion section.”
Understanding this is essential for SOC 2 readiness. Your goal is not just to avoid exceptions but to ensure that if any are found, they are not severe or pervasive enough to warrant a qualified opinion. This involves implementing robust internal controls and having compensating controls in place. By examining a SOC 2 report example, you can see how auditors structure their opinions and document their findings, which is invaluable preparation for your own audit.
The Anatomy of a SOC 2 Report Finding

When an auditor identifies a SOC 2 exception, it is documented with methodical precision in Section IV of the report. This structured format provides complete transparency into the control failure, enabling stakeholders to assess its impact. For a company pursuing SOC 2 compliance, understanding this anatomy is non-negotiable. It allows your team to perform effective internal readiness assessments, precisely document your own control tests, and prepare clear, fact-based responses to any findings. This level of detail is what separates a well-prepared organization from one that is caught by surprise during the audit.
Key Components of an Exception
Every documented exception includes several standard components that collectively provide a complete narrative of the control failure. These components are the evidence that an auditor uses to determine if a finding is material enough to lead to a qualified opinion. For your SOC 2 readiness, you must learn to document your own internal findings using this same structure.
Here are the main parts you’ll see:
- The Control: The specific control statement being tested, which is mapped directly to an AICPA Trust Services Criterion, such as CC6.8 from the Security criteria.
- Auditor’s Test Procedure: A detailed description of the steps the auditor took to test the control’s effectiveness. For instance, “For a sample of terminated users, the auditor inspected system logs to verify that access was removed within the timeframe defined in the company’s access control policy.”
- Nature of the Exception: A factual statement describing precisely how the control failed the test.
- Population and Sample Size: The total number of items available for testing (e.g., 50 terminated employees during the audit period) and the subset of items the auditor selected for testing (e.g., a sample of 25).
- Number of Failures: The exact number of items within the sample that failed the test procedure.
Dissecting a Sample SOC 2 Exception
Let’s examine a real-world example of how an access control exception is documented. This format provides the objective evidence needed for you, your auditor, and your customers to evaluate the finding’s impact.
Sample SOC 2 Exception Documentation
This table illustrates the standard format auditors use to document a control exception within a SOC 2 report, detailing the control, test, and findings.
| Component | Example Description |
|---|---|
| Control | CC6.8: The entity removes or disables logical access credentials for terminated users in a timely manner based on assigned roles and responsibilities. |
| Auditor’s Test | Inspected the list of 50 employees terminated during the review period to verify that system access was revoked within 24 hours of their last day, per company policy. A sample of 25 terminated employees was selected for testing. |
| Nature of Exception | For 2 of the 25 employees tested, system access remained active for more than 72 hours after their termination date. One employee’s access was active for 4 days, and the other for 6 days. |
This clear, quantifiable failure in meeting the control objective specified in CC6.8 directly impacts the Security criterion. This matters for SOC 2 readiness because it demonstrates that policies alone are insufficient. You must have mechanisms to enforce those policies and generate auditable evidence. By using this same rigorous documentation format during your internal assessments, you force your team to confront control gaps with the same scrutiny an external auditor will apply, significantly reducing the risk of unexpected exceptions or a qualified opinion.
Common Causes of SOC 2 Exceptions
SOC 2 exceptions are rarely random; they are typically symptoms of underlying process weaknesses or systemic issues. For an organization pursuing a SOC 2 report, identifying and addressing these root causes proactively is the most effective strategy to prevent exceptions and avoid a qualified opinion. Understanding where auditors most commonly find failures allows you to focus your readiness efforts on high-risk areas, ensuring your controls are not just designed correctly but are also operating effectively and provably.
The Dominance of Access Control Failures
Access control is consistently the leading cause of SOC 2 exceptions and qualified opinions. Failures in this area directly relate to fundamental security principles and are a primary focus for auditors. These exceptions often arise from a disconnect between written policies and actual operational practices, especially when manual processes are involved. For example, the AICPA’s Common Criteria (CC) 6.0 series, which covers logical and physical access controls, is a hotbed for audit findings.
Specifically, CC6.8 (related to timely removal of access for terminated users) and CC6.3 (related to periodic review of access rights) are the most frequent sources of exceptions. An auditor’s job is to verify that these controls are operating consistently. If your offboarding policy requires access to be revoked within 24 hours, but a sample test shows it took 48 hours for even one terminated employee, an exception will be noted. For your SOC 2 pursuit, this means you must have an ironclad, evidence-backed process for managing user access throughout its lifecycle—from onboarding to termination.
Top Offenders in SOC 2 Audits
Beyond general access control, several specific operational failures repeatedly lead to exceptions. These are critical areas to address during your SOC 2 readiness phase.
- Employee Offboarding Delays: This is the most common SOC 2 exception. A user is terminated in the HR system, but their access to critical systems like AWS, Salesforce, or production databases remains active. This is a direct failure of control CC6.8 and is often caused by a lack of integration between HR and IT systems.
- Inconsistent Access Reviews: Your security policy likely mandates periodic (e.g., quarterly) reviews of user access, especially for privileged accounts, as required by CC6.3. An exception occurs when the review is missed, not fully completed, or—most commonly—not documented with evidence of who performed the review and signed off on it.
- Poor Change Management Evidence: Per CC8.1, changes to infrastructure and software must be authorized, tested, and approved before implementation. An auditor will select a sample of production changes and request evidence of this process (e.g., peer review approvals in GitHub, QA testing results in Jira). If your developers rely on informal Slack messages for approvals, you will not have the auditable evidence to pass the test.
An auditor can only test the evidence you provide. A control that was performed but not documented is, for the purposes of the audit, a control that failed. This is a hard lesson many companies learn during their first SOC 2.
The complexity of environments, such as a HIPAA SharePoint migration, can further increase the likelihood of exceptions if evidence collection is not automated. The common thread is a reliance on manual processes and human memory. To achieve SOC 2 readiness, you must automate these critical workflows wherever possible to enforce policies and generate the audit trail needed to prove effectiveness.
How Auditors Judge Exceptions
When an auditor uncovers a SOC 2 exception, they begin a critical evaluation process to determine its significance. The decision to issue a qualified opinion is not based on the sheer number of exceptions but on their materiality. A material exception is a control failure so significant that it could mislead a user of the report or impact their decision-making. For a company undergoing a SOC 2 audit, understanding this judgment process is vital. It helps you prioritize which control gaps to fix and how to discuss any potential findings with your auditor.
The Pervasiveness and Severity Test
Auditors assess materiality by examining the severity and pervasiveness of each exception. This framework helps them distinguish between an isolated mistake and a systemic breakdown of the control environment.
-
Severity: This measures the potential impact of the control failure. For example, a single new hire completing security training one day late is a low-severity exception. In contrast, the failure to apply a patch for a critical remote code execution vulnerability for 90 days is a high-severity failure that directly threatens the Security criterion.
-
Pervasiveness: This measures how widespread the issue is. If one out of 500 employees missed their annual security training, the failure is not pervasive. However, if your change management controls failed for 50% of the production deployments tested, the problem is pervasive, indicating a systemic failure in your process.
An exception that is both severe and pervasive is highly likely to result in a qualified opinion. For instance, if auditors find that multiple terminated employees retained access to sensitive data for weeks (CC6.8), the failure is severe (high risk) and pervasive (indicates a broken process). This directly undermines the control environment and makes a qualified opinion very likely. For anyone pursuing SOC 2, this means your readiness efforts must focus not just on having controls, but on ensuring they operate consistently across the board.
The Role of Compensating Controls
Before finalizing their opinion, auditors will also consider the presence of compensating controls. These are alternative controls that mitigate the risk associated with the failure of a primary control.
For example, imagine a primary control—a firewall rule intended to block traffic from known malicious IP addresses—was misconfigured during the audit period. This is a clear exception. However, if the auditor discovers a compensating control, such as a host-based intrusion detection system (HIDS) on the servers that also blocks connections from those same IP addresses, the overall risk is reduced.
While the primary control failed, the compensating control effectively reduced the risk to an acceptable level. The exception will still be noted, but the auditor may conclude it’s not material enough to qualify the opinion.
This demonstrates that auditors evaluate the control environment holistically. A strong, layered security posture can prevent a single point of failure from becoming a material weakness. As you can discover more about how to handle SOC 2 test exceptions on strikegraph.com, understanding and documenting your compensating controls is a critical part of audit readiness and can be the key to maintaining an unqualified opinion even when minor exceptions are found.
Evaluating a Vendor with a Qualified SOC 2 Report
Receiving a vendor’s SOC 2 report with a qualified opinion is not an automatic disqualification; it is a trigger for heightened due diligence. It means the auditor identified a material weakness, and it is now your responsibility to determine if that weakness poses an unacceptable risk to your organization. For anyone in a compliance or security role, knowing how to properly dissect a qualified report is a critical skill for managing third-party risk effectively.
The Initial Triage
Your first step is to locate the auditor’s opinion letter in Section I of the report. This section explicitly states the auditor’s conclusion and will clearly identify which Trust Services Criteria (e.g., Security, Availability, Confidentiality) the qualification applies to. It will also reference a “Basis for Qualified Opinion” section, which provides a summary of the material issues. This initial triage allows you to immediately focus your investigation on the areas of highest concern.
A Step-by-Step Vendor Evaluation Process
A structured evaluation ensures your analysis is thorough, repeatable, and defensible. The goal is to move beyond the “qualified” label and understand the specific context of the failure and its potential impact on your data and services.
Here’s a practical process to follow:
- Scrutinize Section IV: Go to the detailed testing section of the report. Find the specific exceptions that led to the qualified opinion. Analyze the auditor’s test procedures, the nature of the failures, and, most importantly, the population and sample size. Was this a single failure in a large sample, or a high failure rate indicating a systemic problem?
- Analyze Section V (Management’s Response): This is where the vendor provides their official response to each exception. A strong response acknowledges the finding, accepts responsibility, and provides a detailed remediation plan with committed timelines. A vague or defensive response that deflects blame is a significant red flag about the vendor’s security culture.
- Determine the Real-World Impact: This is the crucial step. Does the failed control protect data or systems relevant to your engagement with the vendor? A failure in physical security controls at a data center you are not using may be irrelevant. However, a systemic failure to remove terminated employee access (CC6.8) for a SaaS platform where your customer data will reside is a direct and material risk.
- Demand Proof of Remediation: Do not accept the vendor’s promise to fix the issue. Request concrete evidence of remediation. This could be a SOC 2 bridge letter covering the period since the audit, a re-tested control sample, or a formal attestation from their management confirming the fix has been implemented and verified.
This methodical approach turns a potentially contentious review into a collaborative, risk-based discussion focused on tangible evidence.
Vendor Qualified Opinion Evaluation Checklist
Use this checklist to ensure a consistent and documented vendor review process. This creates an audit trail demonstrating your organization’s due diligence.
| Evaluation Step | Key Question to Answer | Action Item |
|---|---|---|
| Auditor’s Opinion | Which TSCs were qualified? What was the auditor’s overall conclusion? | Read Section I. Note the specific criteria (e.g., Security, Availability) mentioned in the qualification. |
| Exception Analysis | What were the exact control failures? Were they systemic or isolated? | Analyze Section IV. Quantify the failure rate (e.g., 2 out of 25 samples failed). |
| Management Response | Is the response credible, accountable, and detailed? Does it include a clear remediation plan? | Review Section V. Look for specific dates, assigned responsibilities, and technical details of the fix. |
| Risk Contextualization | Does the failure directly impact the security of our data or service availability? | Map the failed control to your specific use case with the vendor. Assess the real-world risk to your organization. |
| Remediation Verification | Has the vendor provided proof that the issue is resolved and controls are now effective? | Request a bridge letter, updated control evidence (e.g., screenshots), or a formal attestation of remediation. |
Mastering this evaluation process does more than protect your organization from supply chain risk. It provides a blueprint for how your own customers will scrutinize your SOC 2 report. This perspective is invaluable for building a compliance program that not only passes an audit but instills genuine confidence in your clients.
Turning SOC 2 Readiness into a Continuous State
Treating SOC 2 as an annual event is a flawed strategy that leads to audit fatigue, last-minute scrambles, and an increased risk of SOC 2 exceptions and qualified opinions. The most effective approach is to embed compliance into your daily operations, transforming SOC 2 readiness from a project into a continuous, automated program. This proactive posture ensures that your controls are always operating effectively and that evidence is being collected year-round, not just in the weeks before an audit.
A mature SOC 2 program begins with a rigorous readiness assessment where you act as your own auditor, pressure-testing your controls against the AICPA Trust Services Criteria. The goal is to find and fix control gaps yourself, long before an external auditor has the chance. This internal diligence is the foundation of a clean report.
From Manual Checklists to Automated Proof
An analysis of common SOC 2 failures reveals a clear pattern: a heavy reliance on manual processes. Controls that depend on an individual remembering to perform a task—such as de-provisioning a terminated user’s access or conducting a quarterly access review—are inherently fragile and difficult to prove. For a company serious about SOC 2, automation is not a luxury; it is a core requirement for scalable compliance.
Automating high-failure controls provides a direct solution. For example, by integrating your HR Information System (HRIS) with your identity provider (e.g., Okta), you can create a workflow that automatically de-provisions a user’s access across all applications the moment they are marked as terminated in the HRIS. This not only strengthens your security posture in line with CC6.8 but also generates an immutable, time-stamped audit trail that serves as perfect evidence for your auditor.
This decision tree shows the critical path teams must follow when a qualified opinion shows up in a vendor’s report, guiding the review from the initial finding to a final, risk-based decision.
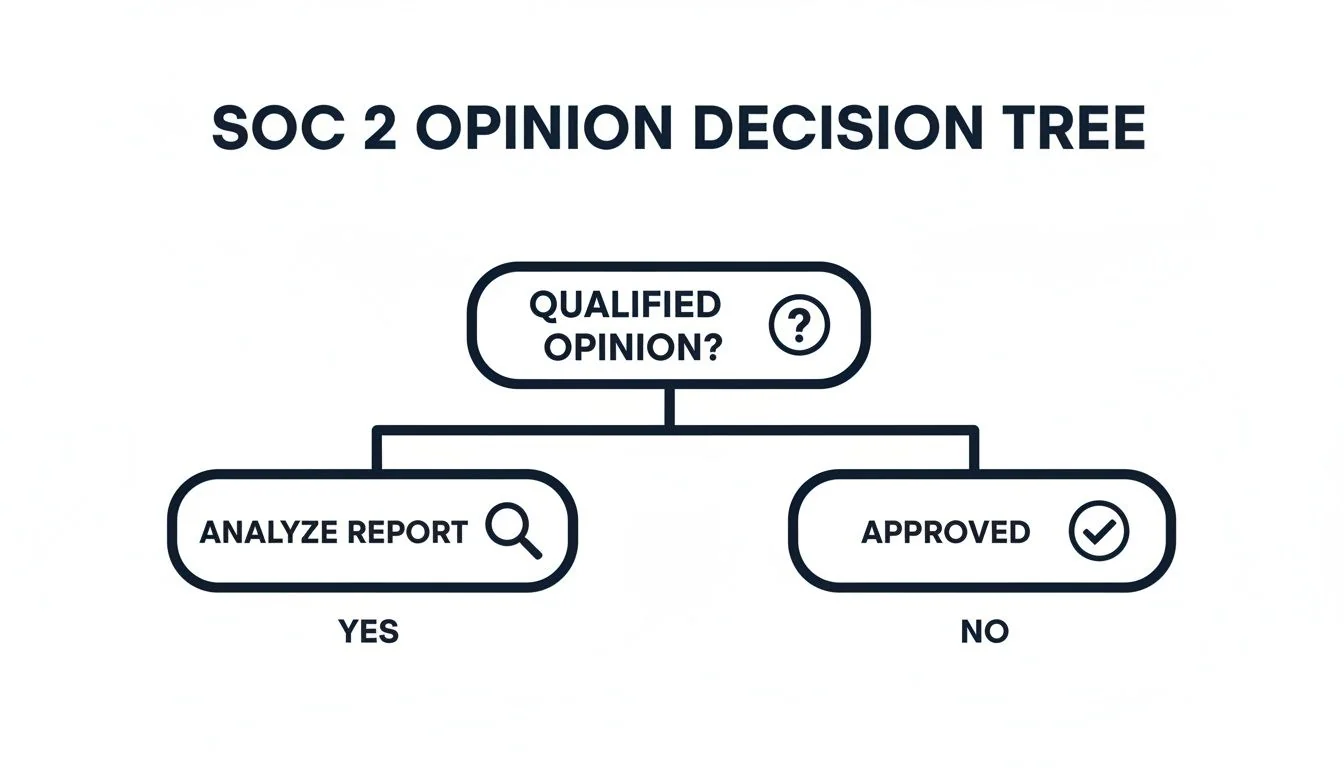
The flowchart makes it clear: a qualified opinion isn’t a dead end. It’s a trigger for a much deeper, structured investigation into the report’s findings.
Adopt Continuous Control Monitoring
The cornerstone of a modern SOC 2 readiness program is continuous control monitoring (CCM). Instead of manually gathering screenshots and logs just before the audit, CCM tools automatically collect evidence from your core systems throughout the year.
- Effortless Evidence: CCM platforms integrate with your cloud providers, code repositories, and HR systems to automatically log events like access changes, policy updates, and security training completions, storing them in an audit-ready format.
- Real-Time Alerts: This technology can instantly detect and alert you to control failures—such as a new public S3 bucket being created without proper tags—allowing for immediate remediation rather than discovering the gap months later during an audit.
- No More Audit Fatigue: When your audit fieldwork begins, a significant portion of the required evidence is already collected, organized, and mapped to specific SOC 2 controls. This drastically reduces the burden on your engineering and security teams.
Adopting continuous monitoring shifts the audit from a historical review of what you did to a real-time validation of your security posture right now. It makes proving compliance an effortless byproduct of just having strong security operations.
Ultimately, achieving SOC 2 readiness is about building and maintaining a verifiably secure environment that earns and retains customer trust. By understanding how auditors scrutinize SOC 2 exceptions and qualified opinions, you can shift your focus from simply passing the audit to building a robust, continuous compliance program. This approach not only ensures a clean report but also fosters a culture of security that becomes a competitive advantage.
Finding the right auditor is the first step toward a successful SOC 2 journey. SOC2Auditors helps you compare 90+ verified audit firms based on real pricing, timelines, and client satisfaction scores. Get three tailored auditor matches in 24 hours, without the sales calls, and make a data-driven choice with confidence. Start your auditor search at https://soc2auditors.org.