A System and Organization Controls 2 (SOC 2) report is an independent audit report developed by the American Institute of Certified Public Accountants (AICPA). It evaluates a service organization’s controls relevant to the security, availability, processing integrity, confidentiality, and/or privacy of customer data. For an e-commerce platform, a SOC 2 report provides objective, third-party validation that the platform has implemented effective controls to protect the systems and data it manages on behalf of merchants and their customers.
Defining SOC 2 in an E-Commerce Context

SOC 2 is a flexible security framework, not a rigid checklist. Unlike prescriptive regulations such as PCI DSS, SOC 2 provides objectives based on five Trust Services Criteria (TSCs): Security, Availability, Processing Integrity, Confidentiality, and Privacy. An e-commerce platform selects the TSCs relevant to the services it provides and the commitments it makes to its customers. The audit then assesses whether the platform has designed and implemented effective controls to meet those objectives.
For someone pursuing SOC 2, this matters because it requires a shift in mindset from following a specific list of rules to demonstrating how your internal processes, policies, and technologies collectively achieve the principles-based objectives of the chosen TSCs. The focus is on proving the effectiveness of your unique control environment.
Why SOC 2 Matters to E-Commerce Growth
SOC 2 is a critical sales and trust enablement tool for e-commerce platforms, not just a compliance requirement. For an organization pursuing a SOC 2 report, its primary value lies in its ability to dismantle security and due diligence barriers during sales cycles with enterprise clients. Large merchants will not partner with or build their business on a platform that cannot provide independent assurance of its security and operational controls. A SOC 2 report serves as that verifiable proof.
SOC 2 serves as independent validation of your security posture. This builds critical trust with customers, satisfies due diligence requirements from enterprise partners who rely on your platform, and creates a significant competitive advantage in a crowded marketplace.
The benefits from a SOC 2 compliance perspective are tangible:
- Build Customer Trust: A SOC 2 report provides auditable proof that you have controls in place to protect sensitive customer data, satisfying a key requirement for B2B customers.
- Enable Enterprise Sales: A SOC 2 report is often a non-negotiable prerequisite for enterprise procurement processes. Possessing one shortens sales cycles and unlocks revenue from larger, more security-conscious clients.
- Strengthen Internal Operations: The process of preparing for a SOC 2 audit forces the formalization and documentation of controls, which inherently strengthens the organization’s security posture and operational resilience, directly contributing to audit readiness.
A Framework for Operational Excellence
The SOC 2 framework should be viewed as a blueprint for operational maturity. For a team pursuing compliance, this is crucial because the audit process itself drives the implementation of foundational best practices. The AICPA’s Common Criteria (the set of controls required for the Security TSC) mandates formal processes that mature a growing company.
Specifically, the audit requires you to prove the existence and effectiveness of controls like:
- CC3.1 (Risk Assessment): The entity identifies risks to the achievement of its objectives. This means you must have a formal risk management program.
- CC6.1 (Logical Access): The entity implements logical access security software, infrastructure, and architectures. This requires demonstrating role-based access control (RBAC) and other access controls.
- CC8.1 (Change Management): The entity authorizes, designs, develops or acquires, configures, documents, tests, approves, and implements changes to infrastructure, data, software, and procedures. This necessitates a formal change control process.
By implementing these controls to meet audit requirements, you are simultaneously building a more resilient, secure, and well-governed platform, which is the core goal of the SOC 2 framework.
Mapping E-Commerce Operations to Trust Services Criteria
Preparing for a SOC 2 audit requires translating your e-commerce platform’s features and operational processes into the language of the AICPA’s Trust Services Criteria (TSCs). This mapping exercise is the most critical first step for any organization pursuing SOC 2. It demystifies the audit by connecting the abstract requirements of the TSCs to the concrete, day-to-day activities of your business. This process provides a clear roadmap for evidence collection and demonstrates to auditors that you understand how your controls meet their testing requirements.
A SOC 2 audit measures your platform against up to five TSCs: Security, Availability, Processing Integrity, Confidentiality, and Privacy. The Security criterion is mandatory for all SOC 2 reports.
Security: The Common Criteria
For a team pursuing SOC 2, the Security TSC (also known as the Common Criteria) is the foundation of the entire audit. Its objective is to prove that the system is protected against unauthorized access, use, or modification. An auditor will require concrete evidence that you have implemented specific technical and procedural controls.
This matters because without strong evidence for the Security TSC, you cannot pass a SOC 2 audit. For an e-commerce platform, this means demonstrating controls like:
- Role-Based Access Control (RBAC): Evidence, such as system screenshots and configuration files, must show that user permissions are restricted based on job function (e.g., a support agent cannot access code repositories). This directly addresses CC6.1 on logical access.
- Multi-Factor Authentication (MFA): You must provide proof, like logs from your identity provider, that MFA is enforced for all administrative access to critical systems, including your platform backend, cloud infrastructure (AWS, Google Cloud), and code repositories.
- Encryption: Auditors will require evidence that data is encrypted both at rest (e.g., database encryption settings) and in transit (e.g., TLS configuration files), satisfying controls like CC6.7.
Think of this as building a fortress around your entire operation. It’s not just about a firewall. It’s about showing a multi-layered, intentional strategy to protect the data people have entrusted to you.
Availability: Uptime and Performance
The Availability criterion assesses whether the system is available for operation and use as committed or agreed. For someone pursuing SOC 2, this is about proving you have controls to meet your Service Level Agreements (SLAs) for uptime. This is especially critical for e-commerce platforms, where downtime directly translates to lost revenue for merchants, making it a key area of customer concern addressed by platforms like Shopify and BigCommerce. As highlighted by the role of compliance in e-commerce on Indusface.com, uptime is a core tenet of trust.
To satisfy the Availability TSC, you must provide evidence of:
- Load Balancing and Auto-Scaling: Configuration files and performance logs showing your infrastructure’s ability to handle traffic spikes.
- Redundant Infrastructure: Architectural diagrams and configurations demonstrating failover capabilities for critical components like databases.
- Disaster Recovery (DR) Testing: This is crucial. You need to provide the DR plan itself, along with test results, after-action reports, and evidence of remediation for any issues found. This addresses A1.3, which requires testing of recovery plans.
Processing Integrity, Confidentiality, and Privacy
For a company pursuing SOC 2, deciding whether to include Processing Integrity, Confidentiality, or Privacy in the audit scope depends entirely on the specific services offered and contractual promises made.
- Processing Integrity: Matters if your platform performs calculations or processing that must be complete, valid, accurate, timely, and authorized. For e-commerce, this means proving order totals, tax calculations, and inventory counts are correct (PI1.1). Evidence includes QA test scripts, system logic documentation, and transaction reconciliation reports.
- Confidentiality: Is relevant if you store and manage sensitive data that is not PII but is protected by agreements (e.g., merchant sales data, proprietary analytics). You must demonstrate controls like data classification policies and strict access control lists to prove you are protecting this information as promised (C1.1).
- Privacy: Applies specifically to how you collect, use, retain, disclose, and dispose of Personally Identifiable Information (PII). This is critical for e-commerce and involves providing evidence of privacy policies, consent mechanisms, and data subject access request procedures, aligning with controls like P2.1 (related to notice and communication of objectives).
Trust Services Criteria Mapping for E-Commerce Platforms
This table provides actionable examples of how to map e-commerce functions to SOC 2 requirements. For someone pursuing SOC 2, this demonstrates the direct link between an operational task, the relevant AICPA criterion, and the specific evidence an auditor will request.
| Trust Service Criterion | E-Commerce Application | Example Control (AICPA Reference) | Evidence for Auditors |
|---|---|---|---|
| Security | Protecting against unauthorized access to the admin panel. | Implement logical access security measures. (CC6.1) | Screenshots of RBAC settings; logs showing MFA enforcement. |
| Availability | Ensuring the checkout process works during a sales event. | Test recovery plan procedures to meet recovery objectives. (A1.3) | Disaster recovery test results; load testing reports. |
| Processing Integrity | Calculating correct order totals with tax and shipping. | System processes transactions in a timely and accurate manner. (PI1.1) | QA test scripts for checkout flow; order record samples. |
| Confidentiality | Securing merchant-specific sales and performance data. | The entity identifies and protects confidential information. (C1.1) | Data classification policy; access control lists for reports. |
| Privacy | Securely handling shopper PII for order fulfillment. | The entity obtains or generates PII for its defined objectives. (P2.1) | Public-facing privacy policy; screenshots of consent banners. |
This mapping turns the abstract challenge of a SOC 2 audit into a manageable, evidence-based review of your existing operations, providing a clear path to compliance.
Putting Your Key E-Commerce Controls in Place
After scoping the audit, the next phase is implementing and documenting the specific controls an auditor will test. For an organization pursuing SOC 2, this is the most intensive part of the process. It involves creating a body of evidence—policies, procedures, configurations, and logs—that proves your controls are designed and operating effectively. Without this verifiable evidence, your security claims are unsubstantiated from an audit perspective.
Securing the Payment Process
For an e-commerce platform, auditors will heavily scrutinize controls around the payment process for both the Security and Processing Integrity criteria. While using a PCI-compliant processor like Stripe or PayPal is standard, your responsibility extends to securing the integration with these services.
This matters for SOC 2 because a compromise of your payment integration could lead to financial loss or service disruption. Your controls must address:
- API Key Management: Store API keys and other secrets in a dedicated vault, never in source code. Access must be logged and restricted. This is a direct response to AICPA Common Criterion CC6.1 (logical access).
- Key Rotation: You must have a documented policy and proof of execution for rotating API keys at a defined interval (e.g., every 90 days) to limit the impact of a potential compromise.
- Environment Segregation: Provide evidence that separate API keys are used for development, staging, and production environments to prevent test data from ever impacting live transactions.
Authentication and Access Controls
Defining and enforcing who can access your systems and what they can do is fundamental to the Security TSC. For someone pursuing SOC 2, this means demonstrating the principle of least privilege in action. An auditor will require proof that users only have the minimum access necessary to perform their job functions.
Key controls and the evidence required include:
- Multi-Factor Authentication (MFA): This is a mandatory control. Evidence must include screenshots from your identity provider or system logs that show MFA is enforced for all users with administrative or privileged access.
- Role-Based Access Control (RBAC): Provide documentation of defined roles (e.g., Admin, Developer, Support) and their associated permissions. Supplement this with screenshots of the RBAC configuration in your platform, demonstrating that a support agent cannot perform developer functions.
When implementing these key controls for e-commerce platforms, it’s vital to consider specific regulations such as Fipa Privacy Essentials For Online Businesses to safeguard customer data. Proper access controls are a cornerstone of both security and privacy compliance.
Formalizing Change Management
Change management is the process of ensuring that all changes to your production environment are authorized, tested, and documented. For a company pursuing SOC 2, this is critical because it directly addresses AICPA Common Criterion CC8.1. A failure in change control could introduce a catastrophic bug or security vulnerability.
An auditable change management process requires:
- A Formal Request: Every change, no matter how small, must originate from a ticket in a system like Jira.
- Peer Review and Staging: Provide evidence (e.g., pull request history) that all code is reviewed by another engineer and tested in a production-like staging environment.
- Formal Approval: The audit trail must show explicit approval from a designated manager before deployment.
- Deployment and Verification: Deployment logs and post-deployment validation checks must be available for auditors.
Your evidence will be a sample of completed change tickets demonstrating this entire documented lifecycle.
Logging and Monitoring for Accountability
Logging and monitoring controls are your “eyes on glass,” providing the necessary visibility to detect, investigate, and respond to security incidents. This matters for a SOC 2 audit because it demonstrates your ability to maintain accountability and detect anomalies. Auditors will expect to see that you are not only collecting but actively reviewing logs from critical systems.
You must provide evidence of logging and alerting for:
- Financial Transactions: All successful and failed payment attempts.
- Administrative Access: All logins (successful and failed) to privileged systems.
- Security Events: Changes to critical configurations, permissions, or firewall rules.
With third-party breaches impacting 97% of top retailers, having robust internal monitoring is no longer optional. These documented controls form the evidentiary backbone of your SOC 2 report and are essential for proving your commitment to security.
Taming Your Third-Party and Vendor Risk
An e-commerce platform’s security posture is inextricably linked to the security of its third-party vendors, from cloud infrastructure providers like AWS and Google Cloud to analytics services like Mixpanel. For an organization pursuing SOC 2, this matters because AICPA Common Criterion CC9.2 requires you to have a formal process to assess and manage risks associated with your vendors. You are responsible for the security of your data throughout its entire lifecycle, including when it is handled by a third party.
Create a Vendor Inventory and Classification System
The first step in demonstrating compliance with CC9.2 is to create and maintain a comprehensive inventory of all third-party vendors. This is not just a list; it must be a managed document that includes the data classification of information shared with the vendor and a designated internal owner.
Once the inventory is complete, you must classify vendors based on risk. This is critical for prioritizing due diligence efforts. Classification should be based on:
- Criticality: How integral is the vendor to your platform’s operation? (e.g., a payment processor like Stripe is a critical vendor).
- Data Access: What is the sensitivity of the data the vendor accesses? (e.g., a vendor processing PII is high-risk).
An auditor will expect to see this inventory and classification methodology to confirm you have a structured approach to vendor risk management.
Your vendor inventory is not a one-and-done task; it’s a living document. Auditors want to see that you review and update it regularly, especially as new services are onboarded or old ones are retired. This proves your vendor management program is an active, ongoing process, not just a checkbox exercise.
Get Serious About Vendor Due Diligence
For vendors classified as high-risk, you must perform formal due diligence to ensure they meet your security requirements. For someone pursuing SOC 2, this is about collecting evidence that your partners’ security controls are adequate.
The primary form of evidence to request is the vendor’s own SOC 2 Type 2 report. This provides the highest level of assurance. Other acceptable evidence includes an ISO 27001 certification or a PCI DSS Attestation of Compliance (AOC).
If a vendor cannot provide a standard compliance report, you must demonstrate you have taken alternative steps to mitigate the risk. This matters to an auditor because it shows you don’t simply ignore the risk. Options include:
- Security Questionnaires: Documented evidence that you sent the vendor a detailed security questionnaire and reviewed their responses.
- Contractual Requirements: Ensuring your vendor contracts include specific security clauses, incident notification requirements, and the right to audit.
- Compensating Controls: Implementing your own technical controls to limit the vendor’s access or encrypting data before it is sent to them.
The financial stakes are high, with a single payment card breach costing an average of $4.8M, as noted in compliance research. Digging into key compliance statistics on Indusface.com further highlights the importance of this. A documented vendor management program is not an optional extra for a SOC 2 audit; it is a mandatory component for proving you are managing the security of your entire service delivery ecosystem.
Navigating the Audit Process Timeline and Costs
For an organization pursuing SOC 2 compliance, understanding the timeline and associated costs is essential for effective project planning and budgeting. The process is not a simple, one-time audit; it is a multi-stage project that requires significant internal resource allocation and direct financial investment.
The first decision is between a Type 1 and a Type 2 report. A Type 1 report attests to the design of your controls at a single point in time. It is faster and less expensive, making it a viable starting point. However, a Type 2 report, which attests to the operating effectiveness of controls over a period (typically 3-12 months), is the standard expected by most enterprise customers. This matters because choosing a Type 2 audit commits your organization to a longer observation period where controls must be continuously executed and evidenced.
Breaking Down the Audit Timeline
A first-time SOC 2 Type 2 audit journey typically spans six to twelve months. The audit fieldwork itself is only a small portion of this timeline. For a team pursuing compliance, the majority of the work is front-loaded in the readiness and remediation phases.
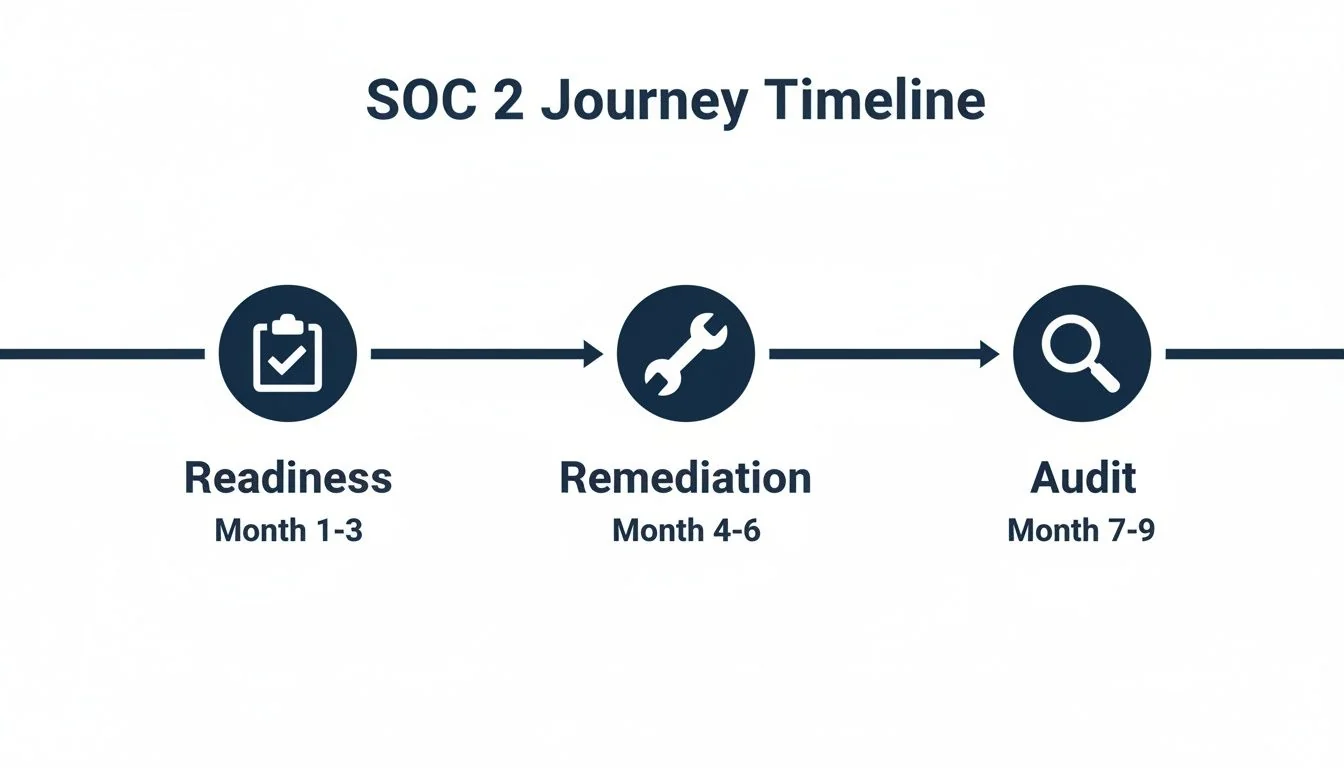
The actionable stages of the timeline are:
- Readiness Assessment (Months 1-2): A formal gap analysis performed with an auditor or consultant to identify missing or deficient controls against the selected Trust Services Criteria.
- Remediation (Months 2-5): The internal team’s implementation phase. This involves writing policies, deploying new tools (e.g., for MFA or logging), and hardening system configurations to close the gaps identified.
- Observation Period (Months 6-11 for Type 2): The period during which your controls must be operating effectively. You will be actively collecting evidence (e.g., change management tickets, access review reports, system logs) to prove this to the auditors.
- Fieldwork & Reporting (Months 11-12): The formal audit period where the auditors test your controls, review evidence, conduct interviews, and ultimately issue the final report.
Benchmarking Your Audit Costs
A SOC 2 audit is a significant investment. For a mid-sized e-commerce platform, a Type 1 audit typically costs between $20,000 and $40,000, while a Type 2 audit ranges from $30,000 to $70,000 for the first year.
The complexity of your platform’s scope is the single biggest driver of cost. An audit covering only the Security criterion will be far less expensive than one that also includes Availability, Processing Integrity, Confidentiality, and Privacy.
This matters for budgeting because every additional TSC adds a significant number of controls that must be tested, increasing the audit effort and cost. Other factors influencing the price include company size, technology stack complexity, and the choice of audit firm. You can dive deeper into the numbers by checking out our detailed breakdown of how much a SOC 2 audit costs on our blog.
Sample SOC 2 Type 2 Timeline and Cost Benchmark for E-Commerce
This table provides a specific, actionable benchmark for a mid-sized e-commerce platform undertaking its first SOC 2 Type 2 audit. This is crucial for anyone pursuing SOC 2 to set realistic expectations with leadership regarding time and budget.
| Phase | Typical Duration | Key Activities | Estimated Cost Range |
|---|---|---|---|
| Phase 1: Readiness & Scoping | 1-2 Months | Gap analysis, auditor selection, TSC scoping, policy writing. | $10,000 - $25,000 |
| Phase 2: Remediation & Implementation | 2-4 Months | Implementing new controls, configuring tools, training staff. | Internal costs; tool subscriptions |
| Phase 3: Observation Period | 6 Months | Operating controls consistently, collecting evidence (logs, etc.). | Internal costs; ongoing |
| Phase 4: Fieldwork & Reporting | 1-2 Months | Auditor testing, interviews, evidence review, report drafting. | $30,000 - $70,000+ |
| Total | 10-14 Months | $40,000 - $95,000+ |
This breakdown illustrates that the total investment is a combination of direct audit fees and significant internal resource commitment.
You Passed the Audit. Now What? Keeping and Using Your SOC 2 Report

Achieving a SOC 2 report is not the end of the compliance journey; it is the beginning of a continuous compliance cycle. For an organization that has just completed an audit, it is critical to understand that the report is valid for only 12 months. The next audit cycle begins immediately. This matters because failing to maintain controls and prepare for the next audit negates the investment made and reintroduces sales and security risks. Transitioning from a project-based audit preparation to a state of continuous compliance is essential for long-term success. For ongoing support, you can explore services that offer secure, scalable support for your e-commerce store.
Turning Your Report into a Sales Weapon
From a compliance perspective, the primary goal of the SOC 2 report is to serve as a tool for building trust and enabling sales. You must have a formal process for using it effectively while protecting the confidential information it contains.
Actionable steps include:
- Create a public security page: This page should state that your platform is SOC 2 compliant, list the audited TSCs, and provide a high-level summary of your security program. This is your primary marketing asset for compliance.
- Share the report under an NDA: Develop a standardized process using a Non-Disclosure Agreement (NDA) to share the full report with prospects and customers during their due diligence. This protects your detailed control information.
- Train your sales team: The sales team must be equipped with specific, factual language to discuss the SOC 2 report, explain its significance, and use it to address security objections from enterprise clients.
How to Stay Audit-Ready, Always
Maintaining a state of continuous compliance is the most efficient way to handle annual SOC 2 audits. This means embedding control operation and evidence collection into your daily workflows.
A mature SOC 2 program means “audit readiness” is your normal, everyday state. Your systems and processes are always operating in a compliant manner, so an audit simply becomes a formal review of what you already do.
To achieve this state, you must implement specific, ongoing processes:
- Automate evidence collection: Use compliance automation software or scripts to continuously gather required evidence, such as logs, configuration snapshots, and user access lists. This eliminates the year-end scramble for documentation.
- Conduct internal reviews: Schedule and perform regular (e.g., quarterly) internal audits of key controls, such as change management, employee onboarding/offboarding, and access reviews. Document these reviews as proof of ongoing monitoring.
- Stay current: The compliance lead must monitor for changes to the AICPA Trust Services Criteria and evolving security threats to ensure controls remain effective and relevant.
As research about compliance trends on Indusface.com indicates, a growing number of organizations are leveraging compliance to demonstrate their security commitment. This ongoing commitment to maintaining and improving controls is the final, critical step in the SOC 2 journey. It ensures the platform remains secure, compliant, and continuously ready for the next audit, turning the annual requirement from a stressful project into a routine validation of operational excellence.
Finding the right audit firm is critical to a successful SOC 2 journey. SOC2Auditors helps you compare 90+ verified firms, matching you with the right partner based on your e-commerce platform’s specific needs—without the sales pressure. Get tailored auditor matches at https://soc2auditors.org.