A SOC 2 management assertion letter is a formal, signed document that an organization’s management provides to its external auditor before a SOC 2 examination begins. In this letter, management attests that its description of the system is fairly presented, the controls stated within the description are suitably designed to meet the applicable Trust Services Criteria, and (for a Type 2 report) that the controls operated effectively throughout a specified period. This document is a mandatory prerequisite for a SOC 2 audit as required by the American Institute of Certified Public Accountants (AICPA).

This letter is the foundational claim your auditor will spend the entire engagement trying to prove. Signed by senior leadership on company letterhead, it’s a formal declaration of accountability. Without this document, the auditor has no formal assertion to attest to, and the SOC 2 examination cannot proceed. For anyone pursuing a SOC 2 report, understanding and correctly drafting this letter is not optional; it is the first critical step in the audit process.
What Is the SOC 2 Management Assertion Letter, Really?
The SOC 2 management assertion letter is a formal declaration from an organization’s management that establishes the basis and scope for a SOC 2 examination. It confirms management’s responsibility for the system’s description and the design (and operating effectiveness for Type 2) of its internal controls relative to the selected Trust Services Criteria. From a SOC 2 compliance perspective, this letter is the mechanism that formally presents the system and controls to the auditor for attestation.
The Core Purpose of the Assertion
From a SOC 2 compliance standpoint, the letter’s purpose is to establish clear ownership and define the scope of the examination, which are fundamental requirements of any attestation engagement. It formalizes management’s responsibility for the control environment, directly addressing AICPA requirements that management accept this responsibility. This formal statement ensures you and your auditor are in complete agreement on what is being examined, why it is being examined (the criteria), and over what period.
The letter makes a few key claims that are directly testable by an auditor:
- Fair Presentation: The system description and its boundaries are presented in accordance with the description criteria, meaning they are accurate and not misleading.
- Suitable Design: The controls stated in the description were suitably designed to provide reasonable assurance that the service organization’s service commitments and system requirements would be achieved based on the applicable Trust Services Criteria. For example, a control designed to enforce multi-factor authentication directly supports the Security criterion (specifically, CC6.1).
- Operating Effectiveness (Type 2 Only): For a Type 2 report, this is the assertion that the controls operated effectively throughout the specified period to meet the chosen criteria.
The assertion letter is the formal mechanism that transforms management’s internal confidence in their controls into a testable claim for an external auditor. It is the official “go” signal for the examination to begin.
This concept isn’t unique to SOC 2. The idea of formally declaring control effectiveness is standard practice in many attestation engagements, like a report on internal control over financial reporting, which involves a similar formal assessment from management. Ultimately, the management assertion letter is the bridge connecting all your internal prep work to the external audit process. It’s the document where leadership formally signs off on the hard work your teams did to build a secure and compliant system. A clear, accurate, and complete assertion is your first step toward a smooth audit, showing your auditor you’re ready for the scrutiny ahead.
Why the Assertion Is Critical for Your SOC 2 Audit
For an organization pursuing SOC 2 compliance, the management assertion letter is not a procedural formality but the cornerstone of the audit. This document is where your leadership team takes formal, written ownership of the company’s control environment and its claims of compliance. This act of accountability is a core tenet of the SOC 2 framework and sets the stage for a credible and successful audit.
Establishes Formal Accountability
By signing the management assertion, your C-suite formally takes responsibility for the system and its controls. This is a foundational requirement of the AICPA’s attestation standards and directly aligns with the Trust Services Criteria, particularly CC1 (Control Environment). This criterion family emphasizes the organization’s commitment to integrity, ethical values, and oversight. The signed assertion is a key piece of evidence demonstrating that this “tone at the top” exists.
This matters for your SOC 2 audit because it proves to the auditor that governance and accountability are taken seriously. It signals a mature compliance posture, differentiating your organization from one merely “checking a box.” For your customers, this top-down accountability provides tangible assurance that the security commitments outlined in your SOC 2 report are backed by the highest levels of the organization.
The assertion letter acts as a contractual agreement between your management and the auditor. It transforms your internal security posture from an abstract concept into a concrete, testable set of claims that the auditor is mandated to verify.
This accountability is what builds real trust. When your assertion states that you’ve implemented controls based on actionable cybersecurity tips to protect data, the signature from your CEO or CTO serves as a formal pledge that those measures are an integral, functioning part of your operations.
Defines the Audit Scope and Focus
The management assertion is the definitive guide for the audit. It clearly draws the boundaries for the entire examination, preventing scope creep and ambiguity that can derail a SOC 2 project. For a successful SOC 2 audit, precise scope definition is paramount to ensuring the final report meets customer expectations without incurring unnecessary costs or delays.
The assertion must be crystal clear on:
- The System: What specific infrastructure, software, data, and people are included in the scope of the service being audited.
- The Criteria: Which Trust Services Criteria (Security, Availability, Confidentiality, Processing Integrity, or Privacy) you are asserting compliance against.
- The Timeframe: The exact “point-in-time” for a Type 1 report or the review period (e.g., October 1, 2023, to March 31, 2024) for a Type 2.
This precision is vital for your SOC 2 journey. A vague assertion leads to a vague and potentially incomplete audit, while a specific one ensures the auditor’s testing is focused and relevant. This clarity prevents misunderstandings, reduces surprise evidence requests, and helps keep the audit timeline and budget on track. This focused approach ensures your final SOC 2 report is a valuable asset that your clients can rely on, demonstrating you have a well-governed security program with clearly defined and managed boundaries.
Key Elements of a Management Assertion Letter
A SOC 2 management assertion letter must follow a specific structure mandated by AICPA attestation standards (AT-C Section 205). It is not a free-form document but a formal declaration where your leadership makes specific, testable claims about its control environment. For anyone pursuing a SOC 2 report, getting these elements right is critical to avoid immediate roadblocks with your audit firm. An incorrect or incomplete assertion will be rejected by the auditor, causing delays until it is corrected.
This table breaks down each required component, its purpose, and why it matters from a SOC 2 compliance perspective.
| Component | Purpose and Explanation | Why It Matters for SOC 2 |
|---|---|---|
| System Identification | Clearly defines the boundaries of the audit—the specific platform, infrastructure, software, people, procedures, and data being examined. | A vague description leads to scope creep and audit inefficiencies. A precise one, aligned with the system description, keeps the audit focused, preventing wasted time and money testing out-of-scope components. |
| Trust Services Criteria (TSC) Declaration | Formally lists which of the five TSCs (Security, Availability, Confidentiality, Processing Integrity, Privacy) are included in the scope of the audit. The Security criteria are always required. | This is a binding commitment. The auditor will only test controls against the criteria you explicitly declare here. Omitting a criterion required by a key customer renders the final report useless for that sales engagement. |
| Management’s Responsibility Statement | A formal declaration that management is responsible for the system description, selecting the criteria, and the design, implementation, and operation of the controls. | This is a non-negotiable AICPA requirement. It confirms you own the control environment and are not shifting that responsibility to the auditor, which is a prerequisite for an attestation engagement. |
| Audit Period or “As-Of” Date | Specifies the exact timeframe for the audit. For a Type 2, it’s a period (e.g., January 1, 2024, to June 30, 2024). For a Type 1, it’s a single point in time (e.g., “as of June 30, 2024”). | This defines whether the report attests to the operating effectiveness of controls over time (Type 2) or their design suitability at a point in time (Type 1). An incorrect date can invalidate evidence and halt the audit. |
| Subservice Organization Disclosure | Identifies critical third-party vendors (like AWS) whose controls are necessary to meet the criteria, and states whether you are using the “carve-out” or “inclusive” method. | Provides transparency required by the AICPA about which controls you manage versus those you rely on your vendors to perform. This is crucial for users of the report to understand the full scope of your control environment. |
| Signature of Responsible Executive | The letter must be signed by a member of senior management (e.g., CEO, CTO, CISO) who has sufficient and appropriate responsibility for and knowledge of the system and controls. | This signature is evidence of “tone at the top” and management oversight, a key aspect of the Control Environment (CC1) criteria. It demonstrates executive buy-in and accountability, giving the audit process credibility. |
Identification of the System
First, you must clearly define the “system” being audited to set the official boundary for the examination. From a compliance perspective, this description must be consistent with the more detailed narrative in Section 3 of your SOC 2 report. For example, a proper system identification might read: “The ‘DataSafe’ software-as-a-service (SaaS) platform, including the production environment hosted on AWS in the us-east-1 region, the associated application code, the personnel of the engineering and operations teams, and the automated procedures involved in providing the ‘DataSafe’ services to customers.”
Declaring the Trust Services Criteria
Next, you must formally state which of the five Trust Services Criteria (TSCs) are in scope. This dictates exactly which controls the auditor will test. You cannot claim compliance with a criterion you did not explicitly list in the assertion.
The five TSCs are:
- Security (Common Criteria): Mandatory for all SOC 2 audits. It addresses the protection of information and systems from unauthorized access, unauthorized disclosure of information, and damage to systems.
- Availability: Asserts the system is available for operation and use as committed or agreed. This is critical for services with uptime SLAs.
- Confidentiality: Covers the protection of information designated as confidential from unauthorized disclosure.
- Processing Integrity: Focuses on whether system processing is complete, valid, accurate, timely, and authorized.
- Privacy: Deals with the collection, use, retention, disclosure, and disposal of personal information in conformity with the commitments in the entity’s privacy notice.
Why This Matters for SOC 2: The assertion letter is your final word on the audit’s scope. If you forget to include a criterion that a major customer needs (like Availability), the final report might be useless for that sales deal, making the whole audit a waste of time and money.
Specifying the Audit Period (For Type 2)
For a SOC 2 Type 2 report, your assertion has to name the exact review period. This is the timeframe—typically between six and twelve months—during which you’re claiming your controls were operating effectively. For a Type 1 report, you’d instead state a “point-in-time” date. The language also shifts: a Type 2 asserts controls operated effectively, while a Type 1 asserts they are suitably designed. This distinction is fundamental to the value and purpose of your SOC 2 report.
Disclosing Subservice Organizations
Finally, you are required to disclose any subservice organizations you rely on to provide your service. If you run your platform on AWS, their controls for physical data center security are part of your overall control environment. Your assertion letter must state whether you’re using the “carve-out” method (excluding the subservice organization’s controls from your assertion) or the “inclusive” method (including their controls and providing a separate assertion from them). This transparency is an AICPA requirement and is critical for your customers to understand the complete picture of your security posture.
How Assertions Differ for SOC 2 Type 1 and Type 2 Audits
The claims made in a management assertion letter differ fundamentally for a SOC 2 Type 1 versus a SOC 2 Type 2 audit. This distinction is at the heart of the SOC 2 framework and determines the level of assurance the final report provides. For an organization undergoing a SOC 2 audit, choosing the right assertion is a strategic decision that impacts the audit’s scope, timeline, and cost.
For a Type 1, you assert that controls were suitably designed at a single point in time. For a Type 2, you assert that controls were both suitably designed and operated effectively over a specified period. This is the core difference: design versus operational effectiveness.
The Point-in-Time Assertion for a Type 1 Report
The assertion for a Type 1 audit focuses on a single moment. Management formally states that, as of a specific date, the documented controls are designed to meet the selected Trust Services Criteria. From a compliance perspective, this demonstrates that you have established a formal control environment, even if its long-term effectiveness has not yet been proven.
This is a common and practical approach for companies new to SOC 2 compliance.
- It serves as a valuable first step, allowing you to establish a baseline of controls.
- The assertion is less demanding as it doesn’t require historical evidence of operation, resulting in a faster and less expensive audit.
- It shows prospective customers that you have a documented, thoughtfully designed security program.
Your assertion must clearly specify the three core elements of the engagement.
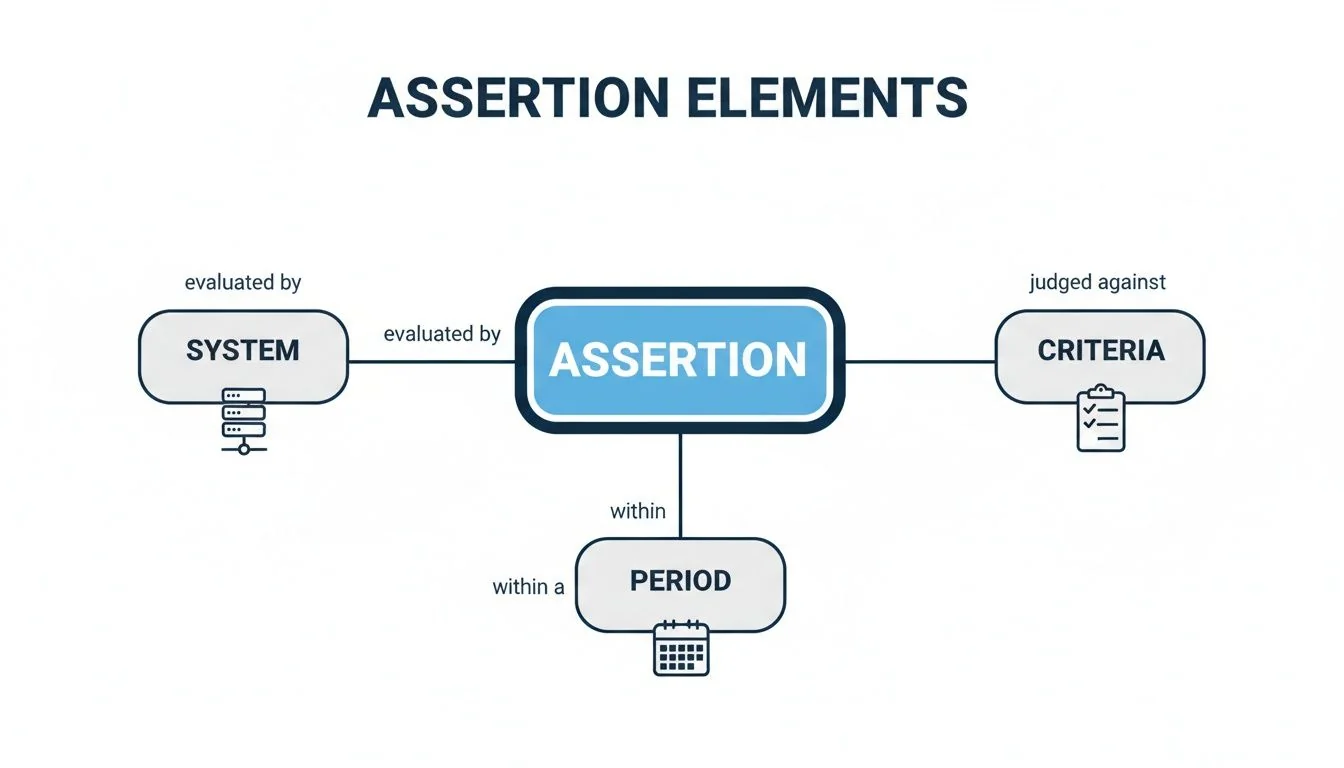
As this diagram shows, your assertion must specify exactly what system is being audited, which criteria it is being evaluated against, and the specific time period (or point-in-time) for the review.
The Period-of-Time Assertion for a Type 2 Report
A Type 2 assertion provides a much higher level of assurance and is what most enterprise customers demand. Here, management claims not only that the controls were designed correctly but that they also operated effectively throughout a review period, typically six to twelve months. This requires extensive evidence collection to prove consistent adherence to policies and procedures.
For a Type 2 report, your assertion moves from “we have the right policies” to “we followed our policies every single day for the last six months.” This is what enterprise customers are looking for.
For example, if you have a control for revoking terminated employee access within 24 hours (related to CC6.3), a Type 2 assertion means you are claiming this happened for every termination during the audit period. The auditor will then test a sample of terminations from that period, requesting HR records and system de-provisioning logs to verify your claim. You can learn more about selecting a SOC 2 observation period to see how this strategic choice impacts your audit. For SOC 2 compliance, the Type 2 assertion is the ultimate goal, as it provides tangible proof of a living, breathing security program.
How Your Assertion Letter Becomes the Auditor’s Playbook
The management assertion letter is not just a preliminary document; it is the definitive roadmap for the entire SOC 2 audit. Each claim made in the letter becomes a specific audit objective that the auditor is professionally obligated to test. For an organization pursuing SOC 2, this means every sentence in the assertion must be deliberate, accurate, and, most importantly, provable.
When management asserts that a specific control is in place and effective, it gives the auditor a direct mandate to verify that claim. For example, if your letter claims that “controls are in place to monitor for and respond to security incidents,” the auditor is required to design tests to validate this. This will trigger evidence requests for incident response plans, logs from security monitoring tools (SIEM), and records of how past incidents were handled.
From Assertion to Evidence Request
Every claim in your assertion letter translates directly into an evidence request. Making an aspirational or unsubstantiated claim is one of the fastest ways to complicate your audit. It leads to expanded testing, follow-up questions, and potential findings of non-conformity (exceptions), all of which increase audit time and cost.
For instance, asserting that your system meets the Availability criteria means the auditor must test controls related to performance, redundancy, and recovery. This matters for your SOC 2 audit because it will trigger requests for:
- Performance Monitoring (A1.1): The auditor will demand system uptime reports, performance dashboards, and SLA metrics.
- Disaster Recovery (A1.2): They will ask for your DR plan and, more importantly, evidence that you tested it during the audit period (e.g., test results, post-mortem reports).
- Incident Response: They will examine incident logs and response documentation to confirm that any availability-related incidents were managed according to your defined procedures.
Your management assertion is the formal IOU you give your auditor. When management claims every employee gets annual cybersecurity training, the auditor has no choice but to validate it by reviewing completion certificates and training records. This validation process is a major driver of project timelines, which can range from 3 to 20 months depending on your readiness.
A Smart Way to Manage Audit Costs
Strategically drafting your assertion letter is a powerful tool for controlling the scope, timeline, and cost of your SOC 2 audit. By being precise, realistic, and aligning the assertion with readily available evidence, you focus the auditor’s effort only on the controls that are mature, relevant, and required.
A well-written assertion sets clear boundaries, preventing the audit from expanding into a time-consuming search for evidence you don’t have. This is a critical component of effective SOC 2 audit readiness. A sharp, well-defined assertion, backed by organized evidence, signals to the auditor that you are prepared, which sets a positive and efficient tone for the entire engagement and leads to a smoother compliance journey.
Common Pitfalls When Drafting Your Assertion
For a SOC 2 audit, the management assertion letter is a high-stakes document where precision is paramount. Mistakes in this letter are not just clerical errors; they are red flags to an auditor that can indicate a lack of readiness or internal control weaknesses. Avoiding these common pitfalls is essential for a smooth and successful SOC 2 engagement.
Most of these pitfalls stem from a disconnect between what management claims in the letter and what the organization can prove with concrete evidence. For SOC 2 compliance, this alignment is non-negotiable.
Mismatched Assertions and Evidence
This is the most critical and frequent mistake. The assertion makes a claim that cannot be fully substantiated with evidence. Remember, the auditor is required to test what you assert.
- What Not to Do: Asserting, “All employees complete annual security training within 30 days of hire,” when you know your records will show several employees completed it on day 45. This guarantees an audit exception because you have asserted a perfect outcome that did not occur.
- What to Do Instead: Frame the assertion around your established process. For example: “The company has implemented a process to ensure new hires complete security awareness training.” Then, be prepared to show evidence of this process, including how you track completion and follow up on deviations. This asserts the control’s existence and design, which is more defensible than asserting flawless execution.
Incorrect Audit Periods
Specifying the wrong audit period in a Type 2 assertion is a fatal error. The letter must state the exact start and end dates of the review period (e.g., January 1, 2024, to June 30, 2024), and this period must align perfectly with your evidence.
An incorrect date range on the assertion letter is a showstopper. The letter must precisely match the period for which you’ve collected evidence. If it’s off by even one day, the auditor can’t issue an opinion, and you’ll have to redo all your documentation.
- What Not to Do: Listing your audit period as “January 1 to June 30” when a key piece of evidence, like your annual penetration test, was completed on December 28 of the prior year. That evidence is now outside the audit period and cannot be used to support your assertion.
- What to Do Instead: Before drafting the letter, conduct a final review to confirm that all key control evidence (e.g., access reviews, DR tests, vulnerability scans) falls within your proposed audit window. This proactive check is a cornerstone of SOC 2 readiness.
Forgetting Subservice Organizations
Organizations do not operate in a vacuum; they rely on critical third-party vendors, known as subservice organizations (e.g., AWS, Azure, Google Cloud). A common pitfall is failing to identify these organizations and specify how their controls are addressed (typically via the “carve-out” method).
This disclosure is a non-negotiable AICPA requirement. For SOC 2 compliance, it matters because it demonstrates a mature understanding of your own control boundaries. It provides transparency to your customers and auditors about which controls you perform and which you rely on your vendors to perform, giving them a complete and honest picture of your service’s security posture.
Preparing Your Assertion for a Successful Audit
The SOC 2 management assertion letter is the formal declaration that initiates your audit. Presented on official company letterhead and signed by a responsible executive, it is management’s definitive statement of accountability. In it, you formally assert that your system description is fairly presented, your controls are suitably designed, and (for a Type 2) that those controls operated effectively.
From a SOC 2 compliance perspective, this letter is not just a formality but the culmination of your readiness efforts. It demonstrates that management has taken ownership of the control environment, a core principle of the Trust Services Criteria. A well-crafted assertion, backed by meticulously gathered evidence, signals to the auditor that your organization is prepared for the rigorous examination to come. You can see more on how these pieces fit together from the team at Secureframe.
A rock-solid assertion sets a positive tone for the entire engagement. It is backed by all the evidence you’ve painstakingly gathered, showing you’re serious about security. For a deep dive into organizing that proof, check out our guide on SOC 2 evidence collection.
A thoughtfully prepared assertion isn’t just about avoiding audit exceptions; it’s about proving your organization’s security maturity. It shows you’ve done the due diligence, making the auditor’s job of validation smoother and more efficient.
Ultimately, a precise and accurate SOC 2 management assertion letter is a critical element of demonstrating your commitment to security and compliance. It connects your internal controls to the external audit process, building credibility with your auditor and providing the foundation for a report that will earn the trust of your customers. This document marks the official transition from preparation to examination, making it a pivotal step in your journey toward SOC 2 audit readiness.
Finding the right auditor is as critical as writing the perfect assertion. SOC2Auditors is a matching platform that helps you compare 100+ verified audit firms on price, timeline, and satisfaction scores to find your ideal partner without the sales pressure. Find your top three auditor matches at SOC2Auditors.