A SOC service provider is a third-party organization engaged to assist a service organization in preparing for, executing, or maintaining compliance with the American Institute of Certified Public Accountants (AICPA) System and Organization Controls (SOC) framework. These providers include licensed CPA firms authorized to perform SOC 2 attestations, readiness consultants who help design and implement controls, and Managed Security Service Providers (MSSPs) that operate specific security functions required by the Trust Services Criteria.
Why does this matter for someone pursuing SOC 2? The selection of SOC service providers is a foundational control decision that directly impacts the validity, cost, and timeline of a SOC 2 audit. A misaligned provider choice or failure to maintain auditor independence can lead to a qualified opinion or a failed attestation, undermining the report’s value to customers and stakeholders.
The SOC 2 Provider Ecosystem: Who Does What?
A SOC service provider is any external entity engaged to assist with SOC 2 compliance, but their roles are distinct and governed by strict AICPA rules on independence. Confusing these roles is a common error that can invalidate an audit. The market for SOC reporting services was valued at USD 5,392 million in 2024 and is projected to reach USD 10,470 million by 2030, reflecting intense market pressure on organizations to provide independently verified assurance over their systems and data.
Why does this matter for someone pursuing SOC 2? The AICPA’s professional standards require strict independence between the entity performing the attestation (the auditor) and any entity that designed or implemented the controls being audited. Understanding the defined roles within the SOC 2 ecosystem is critical for structuring an engagement that will be accepted as valid. You cannot hire one firm to both build your controls and audit them; doing so is a direct conflict of interest.
The Three Core Provider Types
For any SOC 2 audit, you’ll likely engage one or more of these provider types. Understanding their specific functions is essential for maintaining the separation of duties required for a credible attestation.
-
Licensed CPA Firms (The Auditors): These are the only firms authorized by the AICPA to issue an official SOC 2 report. Their role is to act as an independent third party, testing the design (Type 1) and operating effectiveness (Type 2) of a service organization’s controls against the selected Trust Services Criteria and issuing the final attestation. They are the final arbiters of compliance.
-
Readiness Consultants: These are advisory firms that prepare an organization for its SOC 2 audit. Their work includes conducting a gap analysis against the Trust Services Criteria, assisting in the design and documentation of controls and policies, and helping organize evidence for the audit. They cannot perform the final attestation. Our guide on SOC 2 compliance consultants details their function.
-
Managed Security Service Providers (MSSPs): These firms are operational partners that manage specific security controls on behalf of an organization. Services often include 24/7 security monitoring, vulnerability management, and incident response. They provide the technical execution and evidence needed to meet many of the Common Criteria, such as CC7.1 (Monitoring) and CC7.2 (Incident Response).
When discussing these providers, it’s important to remember the central role of the dedicated third-party professionals, commonly known as auditors, who conduct the actual assessment. The AICPA’s independence rule is fundamental: the firm performing the audit (the CPA firm) cannot have been involved in the design or implementation of the controls being audited (the role of a consultant or MSSP). This separation is non-negotiable for a valid SOC 2 report.
Comparing the Four Models of SOC Service Providers
Selecting a SOC 2 provider model is a strategic decision that directly impacts the cost, timeline, and perceived credibility of your audit report. The provider you choose influences the interpretation of the Trust Services Criteria and the specific evidence required for attestation.
Why does this matter for someone pursuing SOC 2? The choice of provider model determines the audit experience and the report’s utility. A Big Four report may be necessary to satisfy risk-averse enterprise clients, while a boutique firm might offer more practical guidance for a cloud-native environment. This decision must align with your budget, risk tolerance, and the expectations of your key customers.
The Big Four Firms
The Big Four—Deloitte, PwC, Ernst & Young (EY), and KPMG—offer unparalleled brand recognition. For public companies or those on an IPO path, a SOC 2 report issued by a Big Four firm provides a high level of assurance to boards, investors, and regulators.
They employ rigorous, standardized methodologies, but this structure can be inflexible and slow for smaller, agile organizations. Timelines are often longer, and costs are significantly higher. A SOC 2 Type 2 engagement frequently starts at $60,000 and can readily exceed six figures, depending on scope and complexity.
Why This Matters for Your SOC 2 Audit: Engaging a Big Four firm satisfies the vendor risk management requirements of the most conservative enterprise customers and investors. The brand itself acts as a form of assurance, often reducing friction in sales cycles where the counterparty demands the highest level of perceived diligence.
Specialized Boutique Auditors
Specialized boutique CPA firms focus exclusively on information security audits like SOC 2, ISO 27001, and HIPAA attestations. Their lower overhead allows for more competitive pricing, with a typical Type 2 audit costing between $20,000 to $50,000.
Their auditors typically possess deep, practical experience with modern cloud environments (AWS, Azure, GCP) and SaaS business models. This focus results in more pragmatic guidance on implementing controls within a cloud-native context. Clients often receive more direct access to senior partners, accelerating problem-solving.
This infographic breaks down the key roles you’ll encounter in the SOC 2 ecosystem.
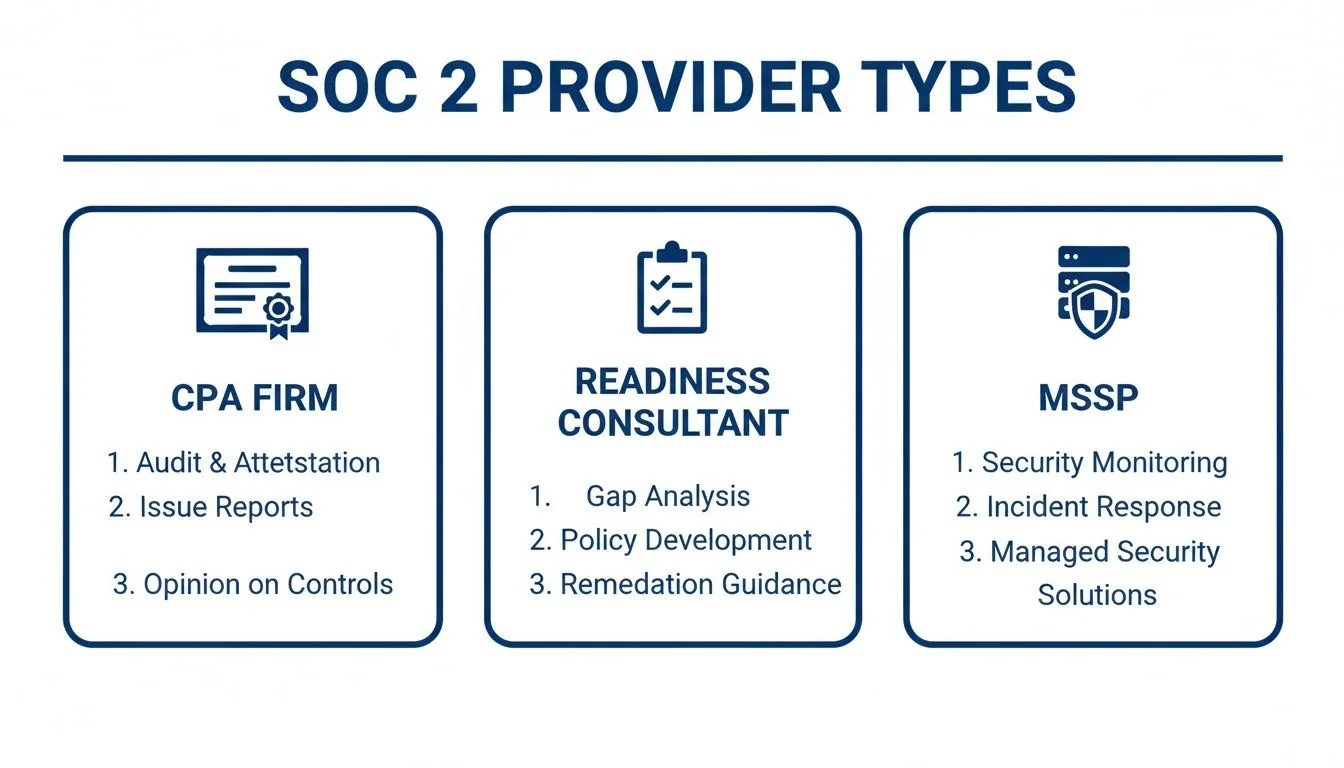
The key takeaway is the required separation of duties: the CPA firm attests, the consultant prepares, and the MSSP operates. This structure is essential for a valid audit under AICPA standards.
Readiness Consultants
Readiness consultants are advisory firms that do not issue the final SOC 2 report. Their sole function is to prepare an organization for the formal audit. This involves performing a gap analysis against the Trust Services Criteria, assisting with the design and documentation of controls, and guiding the evidence collection process.
Why does this matter for someone pursuing SOC 2? Engaging a readiness consultant de-risks the formal audit by identifying and remediating control gaps before the auditor begins testing. This significantly reduces the likelihood of receiving a qualified opinion or a failed attestation. They act as an expert liaison, translating AICPA requirements into actionable tasks for technical teams, which is crucial for meeting criteria like CC2.1 (Control Environment), which requires formalizing and communicating policies and procedures.
SOC-as-a-Service and Compliance Automation
This model combines compliance automation software (e.g., Drata, Vanta) with expert guidance, often from an integrated consulting or MSSP partner. These platforms connect to an organization’s technology stack to continuously monitor controls, automate the collection of evidence, and identify gaps in real-time.
Why does this matter for someone pursuing SOC 2? For a Type 2 report, which requires evidence of control operation over a 3-12 month period, automation is critical. These platforms transform periodic evidence gathering into a continuous, manageable process. For example, they can automatically collect evidence for CC6.1 (Logical Access) by monitoring user access reviews and flagging when employee offboarding processes fail, providing the auditor with a complete evidence trail.
Comparing SOC Service Provider Models for SOC 2 Audits
| Provider Model | Typical SOC 2 Type 2 Cost (2026) | Ideal Audit Timeline | Best Suited For | Impact on Your SOC 2 Audit |
|---|---|---|---|---|
| Big Four Firm | $60,000 - $400,000+ | 12-20 months | Public companies, pre-IPO firms, or those contractually required to use one. | Provides maximum brand credibility for risk-averse stakeholders. Processes are often rigid and less adaptable to agile, cloud-native environments. |
| Boutique Auditor | $20,000 - $50,000 | 6-10 months | Most SaaS startups and mid-market tech companies needing a balance of expertise and value. | Offers specialized expertise in modern tech stacks and more collaborative, efficient audit processes. The report is equally valid under AICPA standards. |
| Readiness Consultant | $15,000 - $30,000 (Prep Only) | 1-4 months (Prep) | Companies new to SOC 2 or those with limited internal compliance staff. | De-risks the formal audit by ensuring controls are properly designed and documented. An added cost that increases the probability of a clean opinion. |
| SOC-as-a-Service | $15,000 - $40,000 (Software) | Continuous | Tech-forward companies looking to automate monitoring and evidence collection. | Operationalizes compliance and reduces manual audit effort by automating evidence collection for up to 70% of controls. Requires proper management to avoid over-reliance on tool-based evidence. |
The model you choose directly influences your audit’s scope and outcome. A Big Four firm provides brand assurance, a boutique auditor offers specialized expertise, a readiness consultant ensures preparedness, and a SOC-as-a-Service platform drives efficiency through automation.
Budgeting Your Financial Investment in a SOC 2 Audit
A SOC 2 audit is a formal attestation engagement performed by an independent CPA firm, resulting in a report on a service organization’s internal controls relevant to the Trust Services Criteria (TSCs): Security, Availability, Processing Integrity, Confidentiality, and Privacy.
Why does this matter for someone pursuing SOC 2? Accurately budgeting for a SOC 2 audit is a critical project management task. Budgeting only for the auditor’s fees is a common failure point. A comprehensive budget must account for direct audit fees, internal resource allocation, and necessary technology subscriptions to ensure the project is viable and can be completed without compromising on control implementation.

Breaking Down the Primary Cost Drivers
There is no standard price for a SOC 2 audit. The final cost is determined by the level of effort required by the SOC service provider, which is driven by several key factors. The scope of the audit is the most significant variable. The Security criterion (also known as the Common Criteria) is mandatory. Adding other TSCs—Availability, Processing Integrity, Confidentiality, or Privacy—increases the number of controls to be tested and, therefore, the cost.
Other factors influencing the price include:
- Company Size and Complexity: Larger organizations with more employees, complex systems, and multiple data sources require more extensive testing procedures.
- Audit Type: A SOC 2 Type 1 report (a point-in-time assessment of control design) is less expensive than a Type 2 report, which tests the operating effectiveness of controls over a 3-12 month period and is the standard expected by most customers.
- Maturity of Controls: Organizations with immature or undocumented controls will incur higher costs, either through a higher audit fee to account for increased risk and effort or through the necessary engagement of a readiness consultant.
Why This Matters for Your SOC 2 Audit: Each added TSC introduces specific control requirements that the auditor must test. For example, while the Security criterion covers baseline logical access (CC6.1), adding the Availability criterion requires the auditor to test specific controls related to disaster recovery and business continuity plans (A1.2), adding significant time and cost to the engagement.
A Type 2 SOC 2 audit can cost anywhere from $10,000-$20,000 for a small, simple organization using a boutique firm to over $100,000 for a large enterprise using a Big Four firm. A median price is often around $30,000, but this can climb substantially, especially if the scope includes the Privacy TSC.
Accounting for Indirect and Hidden Costs
The auditor’s fee is only one component of the total cost. A successful SOC 2 program requires an ecosystem of tools and significant internal effort.
These additional costs include:
- Compliance Automation Software: Platforms like Vanta or Drata are becoming standard for efficient SOC 2 management. They automate evidence collection and continuous monitoring, with annual subscription fees typically ranging from $7,000 to $25,000+.
- Internal Engineering Time: Engineering resources will be consumed remediating control gaps, implementing new security measures, and providing evidence to auditors. This opportunity cost is a significant part of the total investment.
- Legal and Policy Review: New and updated policies required for the audit, such as an Information Security Policy or an Incident Response Plan, will require review and approval from internal or external legal counsel.
For a more detailed analysis of these expenses, refer to our guide on how much a SOC 2 audit costs. A realistic budget is a prerequisite for a successful audit, ensuring you can select an appropriate SOC service provider and fund the internal and external resources needed to meet AICPA standards.
Matching a Provider to Your Industry and Company Stage
Selecting a SOC service provider requires matching their specific expertise to your industry’s regulatory landscape and your company’s stage of maturity. A generic audit that ignores industry context will fail to provide meaningful assurance to your customers and may focus on irrelevant controls.
Why does this matter for someone pursuing SOC 2? An auditor with deep industry experience can conduct a more relevant and efficient audit. They understand the specific risks and customer expectations of your sector, enabling them to provide practical guidance on control implementation and produce a report that directly addresses the concerns of your target market.
FinTech and the Demand for Uptime
For FinTech companies, system availability and data integrity are paramount. Service interruptions can cause direct financial loss and erode customer trust, while processing errors can have severe regulatory consequences.
A SOC service provider for a FinTech must have demonstrable expertise in financial services. Their audit approach must focus on the Availability and Processing Integrity Trust Services Criteria (TSCs), in addition to Security.
- Availability (A1.1, A1.2): The auditor must rigorously test the organization’s business continuity and disaster recovery plans, including system monitoring, backup procedures, and failover capabilities, to ensure they can meet stated service level agreements (SLAs).
- Processing Integrity (PI1.1, PI1.2): This criterion requires proving that system processing is complete, valid, accurate, and timely. For a FinTech, this means the auditor will test transaction processing controls to ensure they prevent errors, duplicate transactions, and unauthorized modifications.
Why This Matters for Your SOC 2 Audit: An auditor without FinTech experience may not adequately test the controls that banking partners and enterprise clients rely on for assurance. This can result in a SOC 2 report that is insufficient for closing high-value deals in the financial sector.
HealthTech and the Intersection of SOC 2 and HIPAA
HealthTech organizations operate at the complex intersection of SOC 2 and the Health Insurance Portability and Accountability Act (HIPAA). While SOC 2 is a voluntary framework, the handling of Protected Health Information (ePHI) makes HIPAA compliance a legal mandate. An experienced provider can perform an integrated audit that maps SOC 2 controls to HIPAA Security and Privacy Rule requirements.
Your provider must be an expert in the Confidentiality and Privacy TSCs.
- Confidentiality (C1.1, C1.2): This TSC focuses on protecting information designated as confidential. An auditor experienced in HealthTech will know how to test access controls, encryption of data in transit and at rest, and data handling procedures specifically for ePHI.
- Privacy (P1.1 and beyond): This extensive TSC addresses how personal information is collected, used, retained, disclosed, and destroyed. A provider with HealthTech expertise can map these SOC 2 controls directly to HIPAA requirements, creating efficiencies and avoiding the need for a separate, redundant HIPAA audit.
Company Stage SaaS Scenarios
A company’s maturity directly influences the optimal choice of provider.
Scenario 1: The Growth-Stage SaaS Needing Speed A Series B SaaS company needs a SOC 2 report to unblock an enterprise contract. The primary need is speed and credibility. A specialized boutique audit firm that understands agile, cloud-native environments is the ideal choice. They can deliver a valid, respected report efficiently without the high costs and bureaucratic delays of a larger firm.
Scenario 2: The Mature Organization Needing Credibility An established private company preparing for an IPO or acquisition needs a SOC 2 report that will stand up to the intense scrutiny of underwriters and investors. In this context, the brand recognition of a Big Four or a top-tier national firm provides a level of assurance that can de-risk the transaction, justifying the higher cost and longer timeline.
Why does this matter for someone pursuing SOC 2? Aligning the provider with your specific context ensures the audit is a business enabler, not a compliance burden. The right auditor provides relevant guidance, runs an efficient process, and delivers a report that builds customer trust and accelerates sales.
Your Data-Driven Checklist for Vetting SOC Service Providers
Selecting a SOC service provider is a critical control in your compliance program. A structured, data-driven vetting process is essential to move beyond marketing claims and assess a firm’s true qualifications.
Why does this matter for someone pursuing SOC 2? The provider you select determines the quality and credibility of your audit. A poor choice can result in a qualified opinion, excessive evidence requests that burden your team, or a final report that fails to provide the assurance your enterprise customers require. This structured vetting process mitigates that risk.

Verify Foundational Credentials
Before discussing scope or price, verify the firm’s fundamental qualifications. These are non-negotiable requirements for any firm performing a SOC 2 attestation.
- Licensed CPA Firm: Per AICPA standards, only a licensed CPA firm can issue a SOC 2 report. Verify the firm’s license on their state’s board of accountancy website. If they are not a licensed CPA firm, they cannot be your auditor.
- Key Personnel Certifications: The engagement partner and manager should hold relevant professional certifications. Look for Certified Information Systems Auditor (CISA), Certified Information Systems Security Professional (CISSP), and Certified Public Accountant (CPA) designations.
- Industry Specialization: Review the firm’s client list or case studies to confirm they have experience with companies of your size, in your industry (e.g., FinTech, HealthTech), and with your technology stack (e.g., AWS, Azure).
Assess Audit Quality and Methodology
After verifying credentials, evaluate the firm’s audit methodology. A superficial, checklist-based audit will produce a weak report that lacks credibility.
The primary differentiator between SOC service providers is their testing approach. Top-tier auditors conduct substantive testing to validate the operating effectiveness of controls, not just their existence. This rigor is what creates a trustworthy report.
Request a redacted sample SOC 2 report from a company similar to yours and assess the following:
- Clarity and Specificity: Are the control descriptions precise and tailored, or are they generic and boilerplate?
- Thoroughness of Testing: Does the description of the auditor’s tests demonstrate a deep examination of the control, or does it appear superficial?
- Readability: Is the report clear and understandable to a non-auditor, such as a potential customer’s security team?
Ask Targeted Discovery Call Questions
Use discovery calls to probe for practical expertise beyond the sales presentation. Ask specific questions that test their knowledge of the AICPA Trust Services Criteria.
- Testing Approach: “Can you describe your testing procedures for CC8.1 (Change Management) in a CI/CD environment?” This question tests their understanding of a core criterion in a modern development context.
- Handling Exceptions: “What is your process when a control test fails or an exception is noted during the observation period?” Their answer will reveal their collaborative approach and how they handle adverse findings.
- Communication and Support: “What is your firm’s standard communication protocol during an engagement, and who will be our primary point of contact?” This establishes clear expectations for project management and support.
Why does this matter for someone pursuing SOC 2? A rigorous vetting process is your first and most important control for ensuring a successful audit outcome. By asking targeted questions and verifying credentials, you can make an evidence-based decision that sets the stage for a smooth attestation and a report that builds customer trust.
Turning Provider Selection into Long-Term Audit Readiness
Choosing a SOC service provider is not a single transaction but the beginning of a long-term strategic partnership. A successful SOC 2 program depends on this relationship to maintain continuous compliance and navigate future audit cycles efficiently.
Why does this matter for someone pursuing SOC 2? A SOC 2 report is not a one-time achievement; it must be renewed annually. A Type 2 report requires demonstrating control effectiveness over a period of time. A stable, long-term relationship with your audit firm creates continuity, making each subsequent audit more efficient and less disruptive to your operations.
The Value of Audit Continuity
A consistent relationship with your auditor establishes audit continuity. The firm develops deep institutional knowledge of your business, technology, and control environment. This familiarity drastically reduces the time your team spends on re-education and redundant evidence requests each year, lowering the internal cost of the audit. For readiness principles, refer to this guide on how to prepare for your first financial audit, as many concepts apply.
Adapting to Evolving Requirements
The AICPA Trust Services Criteria are updated periodically to address emerging threats and technologies. A strong provider partnership provides you with an expert who can proactively guide you in adapting your control environment to meet these new requirements, ensuring you remain compliant year after year.
This strategic alignment transforms the audit from a transactional necessity into a collaborative effort to maintain a strong security posture. Compliance becomes a competitive advantage rather than a cost center.
Recent data from 193 SOC reports in 2024 showed that 23% now include over 150 controls, a significant increase that demands deep provider expertise. A completed SOC 2 report can increase enterprise sales win rates by as much as 5% in security-conscious industries.
Choosing the right SOC service provider is a critical step for your SOC 2 audit readiness. This decision directly supports your ability to provide assurance, build customer trust, and maintain a robust security posture aligned with the AICPA Trust Services Criteria. A well-chosen provider partnership transforms the annual SOC 2 audit from a compliance burden into a valuable asset that demonstrates your commitment to security and facilitates business growth.
Stop wasting time on endless discovery calls and opaque pricing. SOC2Auditors provides a data-driven platform to compare 100+ verified audit firms. Get three tailored matches in 24 hours and make a confident, objective choice for your SOC 2 audit. Find your perfect auditor at https://soc2auditors.org.