SOC 2 security controls are the specific policies, procedures, and technical configurations that an entity implements to protect customer data and meet the requirements of the SOC 2 framework. These controls are the auditable evidence that demonstrates an organization’s system and data management practices align with the Trust Services Criteria established by the American Institute of Certified Public Accountants (AICPA). The primary purpose of these controls is to mitigate security risks and provide assurance to customers that their data is handled securely.
What Are SOC 2 Security Controls
SOC 2 security controls are the core components of a SOC 2 compliance program, representing the tangible actions, rules, and technical settings implemented to satisfy one or more of the five Trust Services Criteria (TSCs). These criteria are defined by the American Institute of Certified Public Accountants (AICPA) and form the basis of every SOC 2 audit. While the framework includes five criteria, only one is mandatory for every report: Security. For a company pursuing SOC 2, these controls are not just best practices; they are the specific evidence an auditor will test to verify that the organization’s promises regarding data protection are being met in practice.
For the purpose of a SOC 2 audit, your security controls are the evidence an auditor tests to prove you meet the requirements of the selected Trust Services Criteria. The Security criterion, also known as the Common Criteria, is the non-negotiable foundation for every audit, as its controls are prerequisite to satisfying the other four criteria.
The Five Trust Services Criteria
Understanding these five categories is the first step in building a SOC 2 program, as every control must map to at least one criterion. The choice of which optional criteria to include depends on the services provided and the commitments made to customers.
- Security (Required): Often called the “Common Criteria,” this is the mandatory starting point. Its controls, such as those outlined in criteria CC6 (Logical and Physical Access Controls) and CC7 (System Operations), are designed to protect information and systems from unauthorized access, unauthorized disclosure, and system damage.
- Availability: This criterion answers: “Is your system operational and accessible as committed or agreed?” For a company pursuing SOC 2, this matters because it requires demonstrable controls for performance monitoring (A1.1), disaster recovery plans (A1.2), and incident response to meet service level agreements (SLAs).
- Processing Integrity: This focuses on ensuring system processing is complete, valid, accurate, and timely. This is crucial for SOC 2 readiness if your service involves transaction processing or data manipulation, as you must implement controls for quality assurance and data processing validation (PI1.1) to prove system reliability.
- Confidentiality: This criterion is about protecting information designated as confidential. For a SOC 2 audit, this means implementing specific controls like data encryption (C1.1) and strict access rules to enforce data protection policies, which is essential for organizations handling sensitive, non-personal information.
- Privacy: This gets more specific than Confidentiality, addressing how an organization collects, uses, retains, and disposes of personally identifiable information (PII). A company pursuing SOC 2 must include this criterion if it handles PII, as auditors will test controls against the entity’s privacy notice and the criteria outlined in the AICPA’s Generally Accepted Privacy Principles (GAPP).
For anyone preparing for a SOC 2 audit, this structure is paramount. The security controls designed are the substance the auditor will spend months testing. They are the concrete, auditable evidence proving that policies are not just documented but are actively operating to protect customer data.
How Controls Map to the Trust Services Criteria
To successfully complete a SOC 2 audit, an organization’s security controls must directly address the requirements specified in the AICPA’s Trust Services Criteria (TSCs). This mapping is the logical foundation of the audit; it provides a clear, traceable line from a specific control—like a multi-factor authentication (MFA) policy—to the TSC it is designed to satisfy. For those pursuing SOC 2, this process is non-negotiable. Without this clear mapping, an auditor cannot validate that the control environment is suitably designed and operating effectively to meet the SOC 2 standard.
This diagram shows how a SOC 2 report is structured around the five Trust Services Criteria. It highlights the central, mandatory role of the Security criterion.
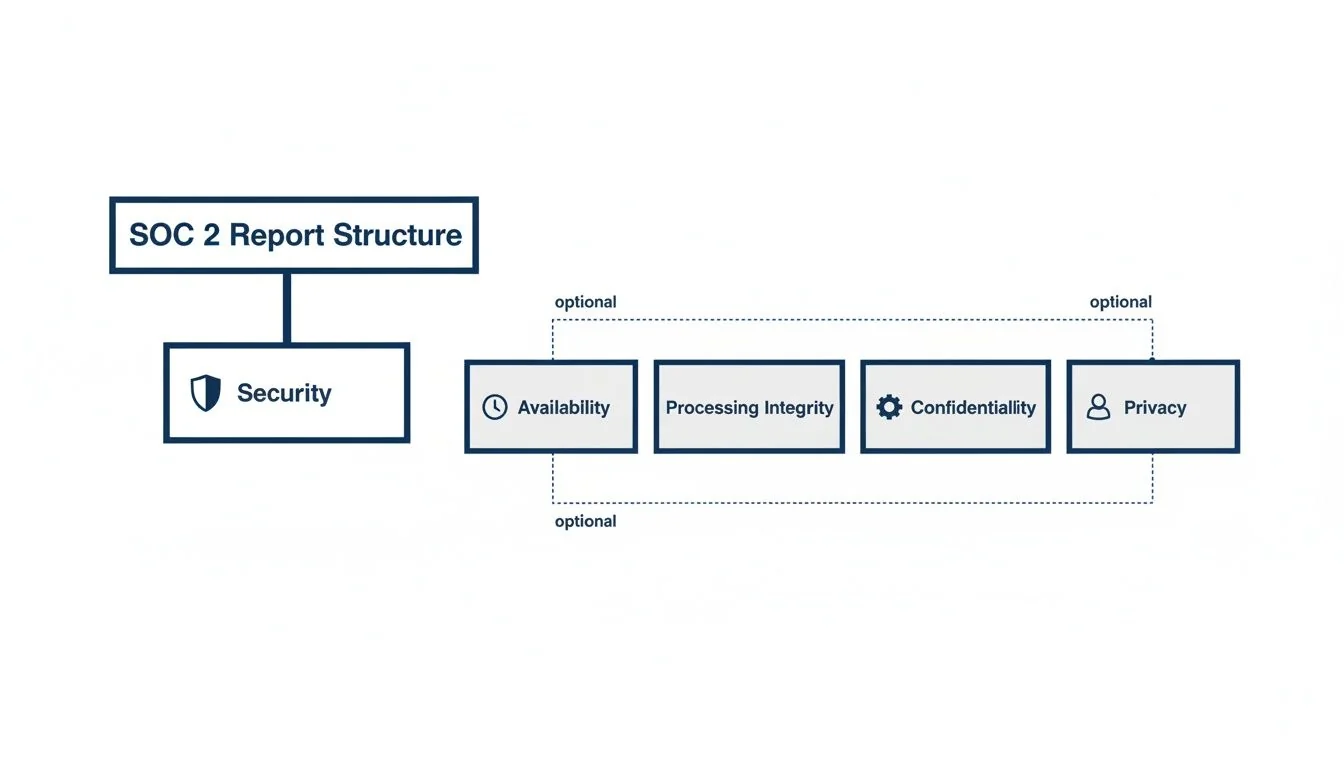
This matters for SOC 2 readiness because while Availability, Processing Integrity, Confidentiality, and Privacy can be added based on service commitments, every SOC 2 audit is built on the foundation of the Security controls defined in the Common Criteria.
The Security Criterion as Your Blueprint
The Security criterion, also known as the Common Criteria (CC), serves as the blueprint for all SOC 2 security controls. It is organized into nine distinct series of requirements (CC1 through CC9), each addressing a different domain of information security. This structure is critical for anyone pursuing SOC 2, as it provides a clear framework for building a compliant program. For instance, the CC6 series focuses on logical and physical access controls, while the CC7 series covers system operations like monitoring and incident response. This allows organizations to design and document controls in a way that directly maps to what auditors will test, rather than guessing at requirements. Our in-depth guide offers a closer look at the SOC 2 Trust Services Criteria and their specific requirements.
Mapping Controls to Common Criteria
In practice, mapping involves connecting specific SOC 2 security controls to their corresponding Common Criteria categories. This demonstrates how a control (e.g., an MFA requirement) satisfies what the TSC requires (e.g., protection against unauthorized access). For a company undergoing a SOC 2 audit, this documented mapping is essential for proving the control environment is comprehensive and logically sound.
This table provides concrete examples of this mapping.
Mapping Security Controls to Common Criteria Categories
| Common Criteria Category | Objective | Example Security Controls |
|---|---|---|
| CC6 Logical and Physical Access | The entity implements logical access security measures to protect against unauthorized access. | • Implementing Role-Based Access Control (RBAC) to enforce the principle of least privilege. • Requiring Multi-Factor Authentication (MFA) for all users accessing production systems. • Conducting and documenting quarterly user access reviews. |
| CC7 System Operations | The entity monitors the system, evaluates, and responds to incidents. | • Deploying a Security Information and Event Management (SIEM) tool to centralize logs. • Establishing an on-call rotation and response plan for security alerts. • Performing annual disaster recovery and incident response tests. |
| CC8 Change Management | The entity authorizes, designs, develops, tests, approves, and implements changes to infrastructure, data, software, and procedures. | • Enforcing a formal change management process via a ticketing system. • Requiring peer reviews for all code changes before deployment. • Maintaining an audit trail of all changes to production environments. |
As shown, the mapping is the core logic that proves a security posture is sound and meets AICPA standards. For a deeper dive, you can find more details in this guide to SOC 2 Type 2 requirements and compliance. The 2026 SOC Benchmark Report found that the percentage of SOC 2 reports with over 150 security controls jumped from 16% to 23%, indicating a trend toward more granular controls to meet rising auditor expectations.
During an audit, this traceability is non-negotiable. An auditor must be able to select any implemented control and see which TSC requirement it addresses. For those pursuing SOC 2, a well-organized control mapping demonstrates a mature security program and is essential for a smooth audit process.
Essential Security Controls You Need to Implement
For SOC 2, compliance is demonstrated through tangible, day-to-day activities that protect customer data. These are your SOC 2 security controls—the specific policies, technical settings, and procedures that form the backbone of your security program. These are not a generic checklist but the concrete evidence you will provide to an auditor to prove you are meeting the AICPA’s Trust Services Criteria. For a company seeking SOC 2 certification, this is the phase where compliance objectives become operational realities.

Here are the non-negotiable controls every auditor expects to see, mapped directly to the criteria they test against.
Logical Access Controls
This is a fundamental control area. Logical access controls are technical and procedural measures designed to ensure only authorized individuals can access systems and data. This directly addresses the CC6 series of the Common Criteria, which focuses on restricting logical and physical access. The core principle is least privilege: users should only have the minimum level of access necessary to perform their job functions. For someone pursuing SOC 2, ineffective access management is a primary cause of audit failures, as it demonstrates a failure to prevent unauthorized access to sensitive customer data.
Key logical access controls include:
- Role-Based Access Control (RBAC): Define roles (e.g., “Developer,” “Support Agent”) with specific, pre-determined permissions. Assign users to these roles rather than granting permissions on an ad-hoc basis. This creates a clean, auditable system that is easier to manage and review.
- Multi-Factor Authentication (MFA): This is a mandatory control. You must require MFA for all access to production environments, code repositories, and critical administrative tools. Auditors view the absence of MFA on critical systems as a significant control deficiency.
- Quarterly Access Reviews: At least quarterly, system owners must formally review user access lists to verify that permissions are still appropriate. This process must be documented to provide evidence that access for terminated employees is promptly revoked and that current users’ access levels remain appropriate.
Change Management
A formal change management process provides auditable proof that all modifications to the production environment—from code deployments to infrastructure updates—are tracked, tested, and approved. This control directly maps to the CC8 series. For a SOC 2 audit, the absence of a disciplined process indicates a risk of unauthorized or unstable changes, which can lead to security vulnerabilities or service disruptions. Auditors will scrutinize ticketing systems, pull requests, and deployment logs to verify this process is followed consistently.
A mature change management process, evidenced by a complete audit trail for every change, signals operational discipline to auditors. This trail must connect the initial request, review, approval, and final deployment.
Actionable change management controls include:
- Formal Change Request Process: All changes must originate from a ticket in a system like Jira. The ticket must detail the change, its purpose, a risk assessment, and a rollback plan.
- Mandatory Peer Reviews: Code changes must not be merged into the main branch without a documented review and approval from at least one other qualified engineer within the pull request.
- Separation of Duties: The individual who develops the code should not be the same person who deploys it to production. This control prevents a single individual from introducing unauthorized changes.
System Monitoring and Risk Management
These two control areas are interconnected. System monitoring enables the detection of and response to security incidents, a core requirement of the CC7 series. Risk management demonstrates a proactive approach to identifying and mitigating threats, which aligns with CC3. For a company pursuing SOC 2, implementing these controls proves it has real-time visibility into its systems and a structured methodology for managing threats before they escalate into major incidents.
Key controls in this area include:
- Security Information and Event Management (SIEM): Implement a SIEM tool to aggregate logs from all critical systems. Configure automated alerts for suspicious activities, such as multiple failed login attempts or unusual data access patterns, to enable timely incident response.
- Risk Register Maintenance: Maintain a formal risk register that documents potential threats, their likelihood, their potential impact, and the mitigation strategy. This document must be reviewed and updated at least annually to demonstrate ongoing risk management.
- Vendor Due Diligence: You must perform security due diligence on all critical vendors and sub-processors before onboarding them. This includes reviewing their security certifications (like their own SOC 2 report) to ensure they meet your organization’s security requirements.
Building these essential SOC 2 security controls is the practical work of preparing for an audit. They provide the tangible evidence needed to demonstrate that your security program is operationally effective.
How Auditors Test Your Security Controls
During a SOC 2 audit, auditors do not simply accept that controls exist; they must verify their effectiveness. They use three core testing methods: inquiry, observation, and inspection of evidence. For an organization pursuing SOC 2, understanding these methods is critical because it dictates how evidence must be collected and how staff should be prepared for the audit. The goal is to provide irrefutable proof that controls are operating as described.

Auditors combine these methods to build a complete picture of how a control operates in the live environment.
The Three Methods of Auditor Testing
To illustrate how this works, consider a critical SOC 2 security control: the change management process. An auditor will use all three methods to verify its operational effectiveness.
Here’s how it plays out:
- Inquiry: The auditor will interview a lead developer and ask, “Can you walk me through your standard process for deploying code to production?” This establishes the formally documented process.
- Observation: The auditor will then request a live demonstration: “Please share your screen and show me a developer merging an approved pull request.” This allows the auditor to observe the actual workflow, including peer review checks and automated pipeline tests.
- Inspection: Finally, the auditor will request a sample of evidence to verify consistency. For example, they will ask for a population of recent deployments and select a sample, requesting the associated Jira tickets and deployment logs to confirm that approvals and tests were performed for each one.
This three-pronged approach is designed to expose discrepancies between policy, practice, and proof. This level of scrutiny is standard across compliance frameworks; for example, a guide to Sarbanes-Oxley cybersecurity compliance shows a similar depth of control testing.
Type 1 vs Type 2 Evidence
The type of audit—Type 1 or Type 2—determines the scope of evidence required. While the testing methods remain the same, the timeframe and nature of the evidence differ significantly. This distinction is crucial for SOC 2 readiness, as it directly impacts the evidence collection effort.
A SOC 2 Type 1 report tests if your controls are suitably designed at a single point in time. A Type 2 report tests if those controls have operated effectively over a period of time, usually 3-12 months.
Here’s a practical comparison of the evidence required for an access control:
| Report Type | Focus of Testing | Example Evidence for an Access Control |
|---|---|---|
| SOC 2 Type 1 | Design Effectiveness | A single screenshot of your RBAC configuration showing defined roles. |
| SOC 2 Type 2 | Operating Effectiveness | A population of all new hires over 6 months, with proof that each was assigned the correct role upon onboarding. |
For a Type 2 report, the auditor requires evidence that the control has operated consistently throughout the observation period. This is why establishing a robust SOC 2 evidence collection process from the beginning is critical.
Achieving a SOC 2 Type 2 certification is a significant undertaking, typically taking 5.5 to 17.5 months. This timeline includes preparation (1.5-3.5 months), the mandatory 3-12 month observation period, and the final reporting phase. While startups may aim for a shorter 3-6 month observation period to accelerate market entry, larger enterprises often choose a 12-month period to demonstrate long-term, sustained compliance. You can learn more about how long it takes to get SOC 2 compliance.
Knowing how auditors will test your controls is fundamental to audit readiness. It shifts the focus from merely having controls to actively proving they are effective. Preparing for inquiry, observation, and inspection enables you to train your team for interviews, ensure your systems produce a clear audit trail, and organize documentation for a more efficient audit.
Fixing Common Control Gaps Before Your Audit
An organization’s SOC 2 security controls must be operational realities, not just documented ideals. Many companies, particularly those new to formal audits, have significant control gaps stemming from informal processes that do not withstand audit scrutiny. Identifying and remediating these gaps before the audit begins is the most effective strategy for ensuring a smooth audit and avoiding formal findings. This proactive approach demonstrates security maturity to an auditor and prevents a last-minute scramble to address deficiencies.

Let’s break down the most frequent gaps auditors find and the specific, actionable steps to close them.
Informal “Tap-on-the-Shoulder” Processes
The most common gap is reliance on informal, undocumented approvals, such as a verbal “looks good” in Slack for deploying code to production. This is a critical failure from a SOC 2 perspective.
The auditor’s principle is: if it isn’t documented, it didn’t happen.
- The Problem: Changes are deployed without a formal ticket, a recorded peer review, or a clear, auditable approval trail.
- How to Fix It: Implement a mandatory ticketing system like Jira for all change requests. Every code change must have an associated ticket, a documented peer review in a tool like GitHub, and verifiable evidence of approval before deployment.
- Why It’s Critical for SOC 2: This directly satisfies Common Criterion 8 (CC8), which requires that all system changes are authorized, tested, and approved. A complete audit trail is non-negotiable for proving this control.
Inconsistent or Missing Risk Assessments
Many organizations either perform a risk assessment once and fail to update it or skip the process entirely. A static risk assessment is a useless one. This control is not a one-time task but the foundation of a proactive security program.
A risk assessment is a living document that guides your entire security strategy. For SOC 2, its ongoing maintenance is proof that you are adapting your controls to evolving threats.
Here’s how to turn this common weakness into a strength for your audit:
- Build a Risk Register: Document potential threats, their likelihood, their business impact, and your current mitigation controls in a spreadsheet or GRC tool.
- Assign Ownership: Every identified risk must have a designated owner responsible for monitoring and managing it.
- Schedule Annual Reviews: Schedule a recurring annual meeting to formally review and update the risk register. This provides evidence for auditors that you are actively managing risk as your business and the threat landscape evolve, satisfying the requirements of CC3.
Poor Vendor and Sub-Processor Oversight
Using a third-party vendor to store or process customer data means their security posture is part of your risk profile. A common failure is onboarding vendors without performing adequate security due diligence.
- The Problem: Onboarding a critical vendor without reviewing their security reports or certifications.
- How to Fix It: Establish a formal vendor management policy. Before signing a contract with any new sub-processor, your team must review their security documentation, such as their SOC 2 report or ISO 27001 certification.
- Why It’s Critical for SOC 2: This directly addresses CC9.2, which requires you to assess and manage risks associated with vendors and business partners. This process must be documented to prove to auditors that you are not outsourcing your compliance responsibilities.
Addressing these common gaps is a critical step toward audit readiness. Finding and remediating these issues proactively saves time, money, and stress, transforming the audit from a source of anxiety into a straightforward validation of your robust SOC 2 security controls.
From Controls to a Clean Report: The Final Steps
You have designed and implemented your controls. The final phase of the process involves translating those policies, procedures, and technical settings into a clean SOC 2 report that can be used to build customer trust and accelerate sales cycles. This requires proving the controls operate consistently and preparing your team to articulate their function to an external auditor. Nailing these last steps is essential for walking into an audit with confidence.
Conduct a Thorough Readiness Assessment
Before engaging an audit firm, you must conduct a readiness assessment. This is a self-audit designed to identify and fix control gaps before the formal audit begins. It is the single most effective way to prevent official findings in your final report.
A readiness assessment should include:
- Gap Analysis: Compare your current controls against the specific Trust Services Criteria in scope for your audit to identify any deficiencies.
- Evidence Review: Verify that the evidence you have gathered is sufficient and properly formatted to demonstrate control effectiveness.
- Remediation Planning: Create a detailed project plan to address every identified gap, with clear owners and deadlines.
Why is this non-negotiable for SOC 2 readiness? It provides a final opportunity to fix issues internally. A gap found during a readiness assessment is a project task; the same gap found by an auditor becomes a formal exception noted in your report for customers to see.
Selecting the Right Auditor for Your Business
The choice of auditor is a critical strategic decision. The right firm can act as a collaborative partner, while the wrong one can lead to misunderstandings and delays. Do not select based on price alone.
When evaluating potential auditors, focus on these factors:
- Industry and Tech Stack Expertise: Does the firm understand your business model and technology? A SaaS company on AWS needs an auditor familiar with cloud environments, not one who primarily audits on-premise data centers.
- Company Size and Culture: A large, bureaucratic firm may be inefficient for a small startup, while a boutique shop may lack the resources for a complex enterprise. Find a firm that aligns with your scale and communication style.
- Responsiveness and Support: The audit is an interactive process. The firm’s responsiveness during the sales cycle is a strong indicator of the support you will receive during the actual engagement.
For a successful SOC 2 audit, view your auditor as a partner in validation, not an adversary. Selecting a firm with relevant expertise and a collaborative approach is key to a positive outcome.
This choice is increasingly important as demand for SOC 2 reports grows. The SOC Reporting Services market, currently valued at USD 5,392 million, is projected to reach USD 10,470 million by 2030, growing at 12.3% annually. This demonstrates that a SOC 2 Type 2 report is now a standard requirement for enterprise sales. You can dive deeper into this market growth and what it means for you at marksparksolutions.com.
Preparing Your Team for Auditor Interviews
The final element is your team. Auditors talk to the employees who operate the controls daily. Your engineers, IT staff, and HR team must be able to explain what they do and why it is important for security.
Prepare them with this plan:
- Identify Control Owners: For each key control, clearly identify the individual responsible for its execution.
- Conduct Mock Interviews: Practice with control owners by asking the questions an auditor would, such as, “Walk me through your process for de-provisioning a user’s access when they leave the company.”
- Focus on “Why”: Ensure your team understands not just what they do, but why it is important for security and SOC 2 compliance. This demonstrates a culture of security that impresses auditors.
A well-prepared team can turn an interview from a point of stress into a demonstration of competence.
Ultimately, your soc2 security controls are the foundation of customer trust. The process of implementing these controls and achieving a clean SOC 2 report is a direct measure of your organization’s commitment to data protection. Proving the operational effectiveness of these controls is essential for audit readiness, as a successful audit provides the tangible proof needed to unblock enterprise sales and grow your business.
Navigating the complex world of audit firms can be overwhelming. SOC2Auditors simplifies the entire process by providing transparent, data-driven comparisons of over 90 verified audit firms. Get matched with the right auditor for your budget, timeline, and tech stack—without the sales calls. Visit https://soc2auditors.org to find your perfect SOC 2 auditor with confidence.