SOC 2 encryption requirements refer to the implementation of cryptographic controls to protect data as mandated by the Trust Services Criteria (TSC), primarily under the Security and Confidentiality categories. SOC 2 does not prescribe specific algorithms or key lengths, but instead requires an organization to define, implement, and operate a risk-based encryption strategy that protects data both in transit across networks and at rest in storage systems. Compliance is demonstrated through documented policies, verifiable technical configurations, and evidence that these controls are operating effectively to meet criteria such as CC6.1, CC6.8, and C1.2.
SOC 2 demands that organizations have strong, documented encryption policies aligned with current industry standards and can prove they are being followed. This covers every piece of customer data handled, whether it is stored in a database or transmitted across a network. For anyone pursuing a SOC 2 attestation, failing to implement and evidence a comprehensive encryption strategy is a direct path to an audit finding, as it signifies a failure to protect information from unauthorized access and disclosure—a core principle of the framework.
Understanding SOC 2 Encryption Principles
Unlike prescriptive frameworks like PCI DSS, SOC 2 is principle-based, meaning it focuses on control objectives rather than specific technologies. This flexibility allows an organization to tailor controls to its environment but places the burden of proof squarely on the entity to justify its encryption strategy. For someone pursuing SOC 2, this matters because you must demonstrate to an auditor that your encryption controls are a reasonable and effective response to the specific risks your organization faces regarding data protection.
You must be able to articulate a clear narrative to your auditor: here is the data we have identified as sensitive, here are the risks to that data (e.g., unauthorized access, interception), and here is how our encryption strategy directly mitigates those risks. This justification is as important as the technical implementation itself.
The Two States of Data Protection
For a SOC 2 audit, an organization must implement and evidence distinct, robust controls for data in its two fundamental states. An auditor will request specific evidence for each, and a failure in one area can lead to a qualified opinion or finding.
- Data-in-Transit: This refers to any data actively moving from one point to another, such as API calls between microservices, user traffic to a web application, or data transfers between a user and a cloud service. For SOC 2, this is critical because unencrypted data in transit can be intercepted, exposing sensitive information.
- Data-at-Rest: This includes all data stored on any digital media, such as data in production databases, files in object storage like S3, server backups, and virtual machine disks. This matters for SOC 2 because it represents the primary defense against data theft if an attacker gains access to physical or virtual storage.
A significant part of this involves implementing strong API security best practices, which is a common point of failure where data in transit is left exposed.
Evolving Industry Standards
While SOC 2 does not mandate specific algorithms, auditors operate based on current, recognized industry standards. For someone pursuing SOC 2, this means your chosen controls must be defensible as “best practice.” Using outdated standards is a clear indicator of a weak control environment.
For example, while AES-128 was once acceptable, AES-256 is the current, de facto standard for symmetric encryption. Similarly, for data in transit, TLS 1.2 is the absolute baseline. An organization not using at least TLS 1.2 will face significant scrutiny. Forward-looking organizations are standardizing on TLS 1.3 for its enhanced security and performance.
An auditor will often find that while external-facing websites are secured with TLS, internal traffic between microservices, database connections, and backup transmissions are left unencrypted. This is a common and significant control gap that directly violates SOC 2 principles and will result in an audit finding.
Properly addressing these foundational principles is essential for audit readiness. The goal is to prove to an auditor that you have a thoughtful, risk-based encryption strategy that is documented, implemented, and consistently enforced across all systems and data states.
How Encryption Maps to the SOC 2 Trust Services Criteria
SOC 2 does not have a dedicated “encryption” control family. Instead, encryption requirements are integrated within the Trust Services Criteria (TSCs), which are the control objectives that form the foundation of a SOC 2 audit. This is a critical distinction for anyone pursuing SOC 2: your encryption controls are not just technical implementations; they are direct evidence used to satisfy specific criteria within the Security and Confidentiality TSCs.
Failing to implement and document encryption properly means you cannot satisfy some of the most fundamental requirements of SOC 2. It is a non-negotiable control that demonstrates how you protect customer data from clearly defined risks, and its absence represents a material weakness in the control environment.
The Security Criterion (Common Criteria)
The Security criterion, also known as the Common Criteria (CC), is mandatory for all SOC 2 reports. Several of its specific objectives are directly or indirectly fulfilled by encryption controls.
- CC6.1 - Logical Access Controls: This criterion requires the entity to implement logical access security measures to protect against unauthorized use of its information assets. Encryption of data at rest is a primary control here. It ensures that even if an attacker bypasses other access controls and gains access to a physical server or virtual disk, the data remains unreadable without the cryptographic keys.
- CC6.8 - Transmission Encryption: This criterion explicitly states that the entity protects information during transmission. To satisfy this, you must enforce strong encryption protocols like TLS for all data transmitted over untrusted networks, including public internet traffic and internal network communications where appropriate.
- CC7.1 - Risk Mitigation: This criterion requires the entity to identify, select, and develop risk mitigation activities for risks arising from potential business disruptions. Since unauthorized data exposure is a significant business risk, encryption is a key mitigating control that auditors expect to see as a direct response to an organization’s risk assessment.
The Confidentiality Criterion
If your organization handles information designated as “confidential” under an agreement or policy, the Confidentiality criterion will be in the scope of your audit. It is virtually impossible to meet this TSC without a comprehensive encryption strategy.
C1.2 - Protection of Confidential Information: This criterion requires that the entity implements controls to protect confidential information from unauthorized disclosure throughout its lifecycle, from creation to disposal. Both encryption at rest and in transit are essential controls to demonstrate to an auditor that you are meeting this requirement effectively.
This mapping from a technical control (encryption) to a TSC objective is what auditors are looking for. For a deeper understanding of how auditors evaluate these objectives, see our guide to the SOC 2 Trust Services Criteria.
To make this explicit, the following table illustrates how specific encryption controls map to the TSCs and the type of evidence an auditor will demand.
Mapping Encryption Controls to SOC 2 Trust Services Criteria
This table shows how specific encryption controls directly support key SOC 2 Trust Services Criteria (TSCs) and provides examples of the evidence auditors expect.
| Trust Service Criterion (TSC) | Control Expectation | Required Encryption Control Example | Audit Evidence Example |
|---|---|---|---|
| CC6.1 (Security) | Protect systems against unauthorized logical access. | Database encryption (TDE) is enabled for all production databases containing sensitive data. | A screenshot from your cloud provider’s console (e.g., AWS RDS) showing encryption is turned on for the database instance. |
| CC6.8 (Security) | Protect data from interception during network transmission. | Enforce a minimum of TLS 1.2 for all external web traffic and API endpoints. | A report from a vulnerability scanner or SSL testing tool confirming that weak protocols (like SSLv3, TLS 1.0/1.1) are disabled. |
| C1.2 (Confidentiality) | Safeguard confidential information from unauthorized disclosure. | All backups containing customer data are encrypted at rest using AES-256. | A configuration file or policy document from your backup solution that specifies the encryption algorithm and settings used. |
Understanding this mapping is critical for a successful audit. It allows you to build a defensible narrative for your auditor, stating, “Our TLS policy directly addresses CC6.8, our database encryption satisfies CC6.1, and our full data protection strategy fulfills C1.2.” This approach transforms technical controls from a simple checklist into powerful evidence of a well-designed, compliant security program.
Protecting Data in Transit with TLS
Securing data as it travels across networks—whether from a user’s browser to your server or between internal microservices—is a fundamental requirement for SOC 2. This is known as protecting data in transit, and its goal is to ensure that intercepted data is rendered unreadable through cryptography. For anyone undergoing a SOC 2 audit, the primary control for this is Transport Layer Security (TLS). An auditor will specifically look for evidence that all data transmission channels are encrypted using modern, robust protocols.
This is not a matter of preference but a direct response to the threat landscape. A weak data-in-transit posture presents a significant risk of data interception, which directly contravenes the control objectives in SOC 2. Failing to secure these channels is a clear path to an audit finding.

Setting the Baseline: TLS 1.2 and Beyond
For any organization pursuing SOC 2, TLS 1.2 is the absolute, non-negotiable minimum standard for encrypting data in transit. The use of older, compromised protocols like SSLv3, TLS 1.0, or TLS 1.1 is an automatic red flag and will be documented as a control deficiency by an auditor. These legacy protocols contain known vulnerabilities that attackers can exploit to decrypt sensitive data.
However, meeting the minimum is not the goal for a strong security posture. Auditors expect to see organizations using TLS 1.3. Standardizing on TLS 1.3 demonstrates a proactive approach to security and offers tangible benefits:
- Faster Handshakes: Establishes secure connections more quickly, improving application performance.
- Stronger Ciphers: Removes obsolete, insecure cryptographic algorithms, enforcing the use of modern, secure cipher suites.
- Perfect Forward Secrecy (PFS): Ensures that the compromise of a long-term key does not allow an attacker to decrypt previously recorded traffic.
From a SOC 2 perspective, implementing TLS 1.3 provides stronger evidence of a mature control environment. Implementing robust TLS hardening techniques is essential to meet audit expectations.
Configuring Strong Cipher Suites
Enabling TLS is insufficient; you must also configure your servers to use strong cipher suites—the specific combination of algorithms used to secure the connection. A weak cipher suite can undermine the security of an otherwise modern TLS protocol. An auditor will examine your server configurations to ensure you have explicitly disabled weak and outdated ciphers, such as:
- RC4
- DES/3DES
- Any ciphers using MD5 for hashing
- Anonymous Diffie-Hellman (ADH) suites
Your server configurations (e.g., in Nginx, Apache, or a cloud load balancer) must prioritize modern, high-strength ciphers. For TLS 1.3, this would be TLS_AES_256_GCM_SHA384. For TLS 1.2, a strong choice is ECDHE-RSA-AES256-GCM-SHA384.
Auditor’s Tip: Auditors frequently use automated tools like SSL Labs to scan public-facing endpoints. These tools will instantly identify weak protocols or ciphers, generating an easy finding that can lead to an audit exception. Proactively running these scans yourself is a critical pre-audit step.
Managing the Certificate Lifecycle
A surprisingly common failure point in SOC 2 audits is the management of TLS/SSL certificates. An expired certificate is not just a service availability issue; it is a security control failure that an auditor will note. This is why a mature, documented process for certificate lifecycle management is essential for anyone pursuing SOC 2. You must demonstrate control over:
- Procurement: Acquiring certificates from a reputable Certificate Authority (CA).
- Deployment: Securely installing certificates and private keys.
- Monitoring: Actively tracking expiration dates.
- Renewal: Automating renewal processes well in advance of expiration.
- Revocation: Having a defined procedure for revoking a certificate if its private key is compromised.
For your SOC 2 audit, you will need to provide evidence of this process in action. This includes policy documents, screenshots from monitoring tools, and logs showing successful automated renewals. A failure to demonstrate control over your certificate lifecycle undermines your entire data-in-transit encryption strategy and puts a clean audit report at risk.
Securing Data at Rest Across Your Systems
Encryption for data at rest refers to the cryptographic protection of inactive data stored on any digital media, including databases, file storage systems like Amazon S3, virtual machine disks, and backups. For SOC 2, this is a mandatory control under CC6.1 and C1.2, as it serves as a critical defense against unauthorized data access if an attacker breaches storage infrastructure or gains physical access to hardware. An auditor will expect to see a multi-layered strategy for protecting this data wherever it resides.
Choosing the Right Encryption Strategy
There is no single “correct” method for encrypting data at rest; the optimal approach depends on your architecture and risk profile. For a SOC 2 audit, you must be prepared to justify your choices as being appropriate for the sensitivity of the data you are protecting.
- Full-Disk Encryption (FDE): Operates at the hardware or volume level (e.g., AWS EBS encryption, Azure Disk Encryption). It is a foundational control that protects against the physical theft of a drive. However, once the operating system is running, the volume is decrypted and accessible, offering no protection against attacks at the OS or application level.
- Transparent Database Encryption (TDE): A feature offered by most major database systems (e.g., SQL Server, Oracle, PostgreSQL) that automatically encrypts the database files on disk. This is a crucial control for SOC 2, as it protects database files from being read if an attacker gains access to the underlying server storage.
- Application-Level Encryption: The most granular and secure method, where the application encrypts specific sensitive data fields (e.g., PII, financial information) before writing them to the database. This protects the data even from privileged database administrators but requires more development effort and rigorous key management.
For SOC 2 purposes, a defensible strategy often involves a combination of these layers: FDE as a baseline, TDE for all databases containing sensitive data, and application-level encryption for the most critical data elements.
Selecting Algorithms and Implementing Cloud Controls
The choice of algorithm for symmetric encryption is straightforward: AES-256 is the undisputed industry standard. An auditor will expect to see AES-256 used for any modern system. While older standards might not automatically cause a finding, using AES-256 demonstrates a commitment to current best practices.
Cloud providers offer robust, auditable services that make implementing this straightforward. For anyone pursuing SOC 2, using these native services is highly recommended.
Leveraging a managed service like AWS Key Management Service (KMS) or Azure Key Vault is a significant advantage for a SOC 2 audit. These services centralize key management, provide a detailed audit trail of all key usage (perfect evidence for an auditor), and simplify the process of enabling encryption across services like S3, RDS, and EBS. Attempting to build a custom key management solution is complex, risky, and difficult to audit.
The table below outlines common cloud-native encryption options that are highly defensible during a SOC 2 audit.
| Cloud Service | Encryption Type | Common Use Case | SOC 2 Evidence |
|---|---|---|---|
| AWS S3 | Server-Side Encryption (SSE-S3, SSE-KMS) | Encrypting files and objects in storage buckets. | A screenshot of the bucket policy that enforces encryption on all new object uploads. |
| AWS RDS | Transparent Database Encryption (TDE) | Securing production and staging database instances. | A screenshot from the RDS console clearly showing the “Encryption enabled” status. |
| Azure Blob Storage | Storage Service Encryption (SSE) | Encrypting unstructured data stored in containers. | A configuration view from the Azure Portal confirming SSE is active for the storage account. |
A well-documented strategy for securing data at rest is a cornerstone of audit readiness. An auditor will not just ask if you encrypt but will probe the how and why of your implementation. You must be prepared to show that you have thoughtfully chosen the right methods for each data store, used industry-standard algorithms like AES-256, and are using secure, auditable tools for key management.
Implementing a Robust Key Management Program
Encryption controls are only as strong as the management of the cryptographic keys that protect them. A perfectly encrypted database is rendered useless if the encryption key is stored in plaintext in a configuration file or checked into a source code repository. For this reason, SOC 2 auditors scrutinize key management practices as a critical component of the overall security posture, directly impacting criteria like CC6.1. Weak key management is a significant control failure.
A robust key management program consists of documented, repeatable procedures for handling cryptographic keys throughout their entire lifecycle. This matters for someone pursuing SOC 2 because it demonstrates that your encryption strategy is not just a technical feature but an operational discipline designed to prevent unauthorized key access and, by extension, data compromise.
The Key Management Lifecycle Explained
SOC 2 compliance requires demonstrating control over every stage of a key’s life. An auditor will look for evidence of a continuous, cyclical process.
- Generation: Keys must be created using a cryptographically secure random number generator (CSPRNG). Using predictable or weak sources for randomness is a major vulnerability.
- Storage: Keys must be stored in a secure, hardened system, such as a Key Management Service (KMS) or a Hardware Security Module (HSM). Storing keys in plaintext is a critical finding.
- Distribution: There must be a secure and auditable process for distributing keys to authorized applications and services, enforcing strict, role-based access control.
- Rotation: Keys must be rotated on a regular, defined schedule to limit the impact of a potential key compromise. Your policy should define the rotation period (e.g., annually), and you must have logs to prove it happens.
- Destruction: When a key is no longer needed (e.g., after data has been destroyed), it must be permanently and securely destroyed to prevent the decryption of old data.
This lifecycle underpins the entire process of applying encryption to critical data stores, as illustrated below.
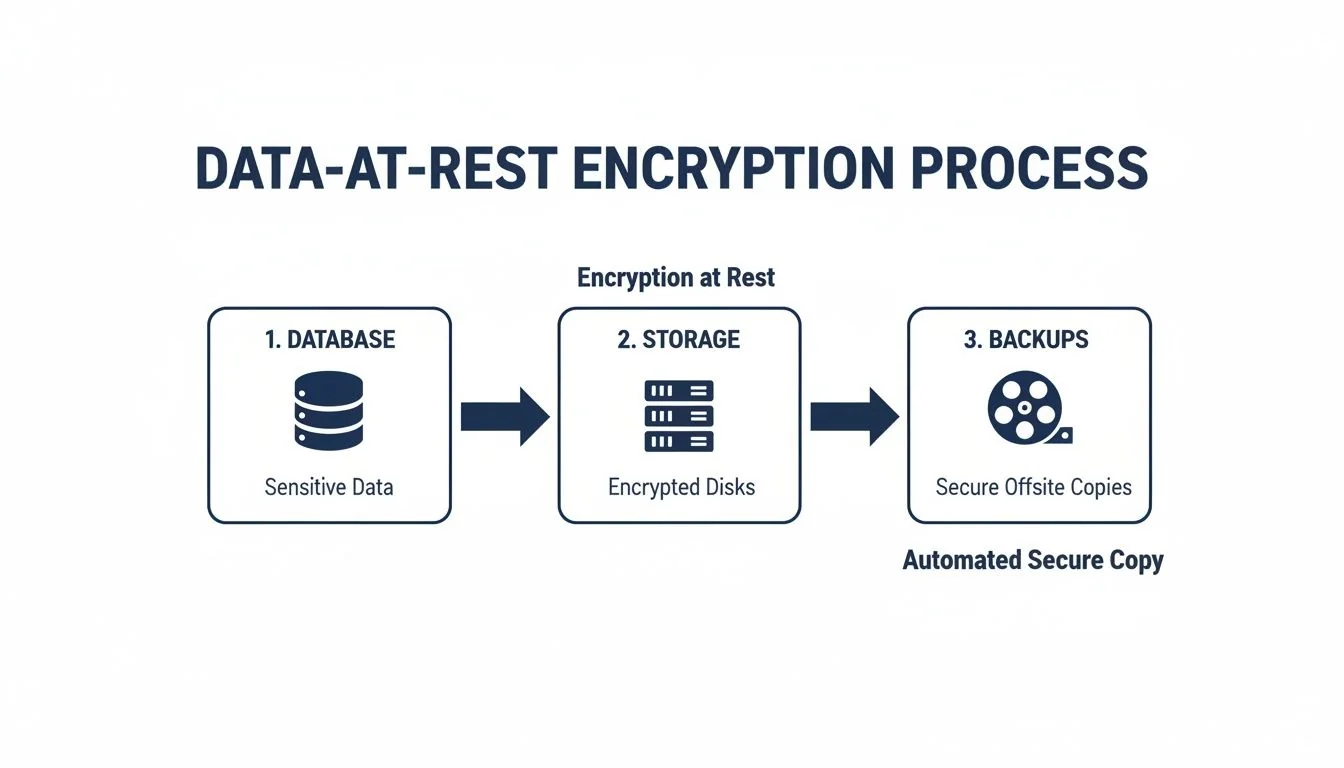
The entire process shown in the diagram is rendered ineffective without a solid key management program to protect the keys at each step.
Centralizing Control with KMS and HSMs
For a SOC 2 audit, manual key management using spreadsheets or text files is indefensible. Centralized key management solutions are purpose-built to handle the key lifecycle securely and provide the necessary audit trail.
- Key Management Service (KMS): Cloud-native services like AWS KMS or Azure Key Vault are the standard for most technology companies. They offer APIs for key operations and generate detailed audit logs of every action, which serves as excellent evidence for a SOC 2 audit.
- Hardware Security Module (HSM): A physical, tamper-resistant device designed for securely managing cryptographic keys. HSMs offer the highest level of security and are often used to protect root keys or in highly regulated environments.
The importance of this has grown as client expectations have increased. One study found that the inclusion of the Confidentiality criteria in SOC 2 reports jumped from 34% to 64.4% in just one year, as detailed in this recent SOC benchmark report. This trend directly increases the scrutiny on encryption and key management, as protecting confidentiality is impossible without them.
For anyone pursuing SOC 2, a strong key management program is not optional. Auditors will request your key management policy, review access logs from your KMS, and verify your key rotation schedule. Demonstrating a mature, centralized, and automated approach provides powerful evidence that your encryption controls are designed correctly and are operating effectively.
How to Prepare Encryption Evidence for Your SOC 2 Audit
Implementing strong encryption controls is only half the battle. To pass a SOC 2 audit, you must provide clear, verifiable evidence that your controls are designed appropriately and have been operating effectively over the audit period. Preparing this evidence is a critical process of connecting your security policies to your real-world technical configurations and operational activities.
For someone pursuing SOC 2, this is where the audit is won or lost. The goal is to build an undeniable evidence trail that leaves no ambiguity for the auditor. A well-prepared evidence package demonstrates maturity and control, making the audit process smoother and more efficient.
Assembling Your Policy and Procedure Documentation
Auditors always begin with documentation to understand your stated controls. These policies are the foundation upon which all your technical evidence is built. For SOC 2, your documentation must be clear, specific, and approved.
- Data Classification Policy: This policy must define your data sensitivity levels (e.g., Public, Internal, Confidential) and explicitly state the minimum encryption requirements for each level.
- Encryption Policy: This dedicated policy must specify approved algorithms (AES-256), protocols (TLS 1.2 minimum, TLS 1.3 preferred), and required key lengths. Ambiguity here is a red flag for auditors.
- Key Management Procedures: This document must detail the entire key lifecycle: how keys are generated, stored, distributed, rotated, and destroyed, and who is responsible for these processes.
Gathering Technical Configuration Evidence
After reviewing your policies, the auditor’s next request will be to see the implementation. Screenshots and configuration files serve as direct proof that your policies are being enforced. Your technical evidence package must be organized and ready.
- Cloud Provider Screenshots: Clear screenshots from your AWS, Azure, or GCP console showing encryption enabled for databases (e.g., RDS “Encryption enabled”), storage (e.g., S3 bucket properties enforcing encryption), and virtual machine disks (e.g., EBS volume encryption status).
- Web Server and Load Balancer Configurations: Configuration file snippets (e.g., from Nginx or an AWS Application Load Balancer) that explicitly disable weak protocols like SSLv3 and TLS 1.0/1.1 and define the prioritized list of strong cipher suites.
- Vulnerability Scan Reports: An external validation report from a tool like Qualys SSL Labs provides objective, third-party proof that your public-facing endpoints are configured securely according to industry best practices.
An auditor will ask for specific evidence, such as “Provide a screenshot of the production S3 bucket policy that enforces server-side encryption with KMS on all object uploads.” Having these artifacts pre-gathered and organized demonstrates preparedness. Our guide on SOC 2 documentation requirements provides a more exhaustive list.
Demonstrating Operational Effectiveness with Logs
For a SOC 2 Type 2 audit, you must prove that your controls were operating effectively over the entire 6- to 12-month audit period. Logs are the primary evidence for this.
- KMS Audit Logs: Exported logs from your Key Management Service (e.g., AWS CloudTrail logs filtered for KMS activity) showing that keys were rotated according to the schedule defined in your policy.
- Certificate Management Logs: Records from your monitoring or automation tools showing alerts for expiring TLS certificates and corresponding logs confirming their successful renewal.
A comprehensive encryption strategy, backed by clear documentation, verifiable technical configurations, and operational logs, is not just a best practice—it is a prerequisite for a successful SOC 2 audit. Demonstrating this level of rigor shows an auditor that you have a mature security program and are well-prepared to meet the standards required for a clean SOC 2 report.
Finding the right SOC 2 auditor is as critical as preparing your evidence. SOC2Auditors is a comparison platform that helps you select the right firm with confidence, providing verified data on pricing, timelines, and satisfaction scores from over 90 firms. Avoid overpaying and delays by getting three tailored auditor matches in 24 hours. https://soc2auditors.org