SOC 2 continuous monitoring is the ongoing, systematic process of collecting, analyzing, and reviewing evidence to verify that an organization’s internal controls are operating effectively over time, as required by the American Institute of Certified Public Accountants (AICPA) for a SOC 2 Type 2 report. The annual cost for these activities typically ranges from $5,000 to over $40,000, representing a recurring operational expense separate from the one-time audit fee. This process automates the verification of controls related to the Trust Services Criteria (TSC), shifting compliance from point-in-time assessments to a state of real-time, provable oversight. This is fundamental for a SOC 2 Type 2 report, which evaluates the operational effectiveness of controls over a defined period, usually 6 to 12 months.

Why this matters for SOC 2: Continuous monitoring transforms compliance from a reactive, pre-audit fire drill into a proactive, constant state of audit readiness. It is the operational engine that ensures your controls function daily, providing the necessary evidence for a successful Type 2 audit and preventing last-minute control failures.
Continuous monitoring directly supports an auditor’s need for evidence that controls for criteria like Security (e.g., CC6.6 on monitoring system components, CC6.7 on responding to security incidents), Availability (A1.2 on monitoring system performance), and Confidentiality (C1.2 on protecting confidential information) are consistently effective. For a deeper understanding of the specific controls involved, refer to detailed guides on SOC 2 logging and monitoring controls.
Without it, an organization is essentially operating without visibility into its control environment. This significantly increases the risk of control failures, which can lead to emergency remediation, increased audit costs, and a qualified audit opinion that undermines customer trust and jeopardizes enterprise sales. Ultimately, continuous monitoring provides objective proof that your security program is not just a paper-based policy but a living, breathing system that actively protects customer data every day.
Why Continuous Monitoring Is a Core SOC 2 Requirement
For a SOC 2 Type 2 audit, point-in-time evidence is insufficient. The audit’s objective is to assess the operational effectiveness of controls over an extended observation period, typically six to twelve months. Continuous monitoring is the mechanism that provides this longitudinal evidence, proving that security controls are not just designed correctly but are also functioning consistently day-to-day.
Why does this matter for SOC 2? The AICPA Trust Services Criteria (TSC) implicitly and explicitly require ongoing monitoring activities. A SOC 2 Type 2 report is an opinion on the effectiveness of controls over time, not just at a single moment. Auditors cannot form this opinion based on static checklists or manual spot-checks. They require a continuous stream of evidence demonstrating consistent control operation, which is precisely what a robust continuous monitoring program delivers.
Connecting Monitoring to the Trust Services Criteria
Continuous monitoring is the engine that generates the evidence needed to satisfy specific TSC requirements. For an auditor, a well-implemented monitoring program signifies a mature compliance operation, reducing the need for manual sampling and increasing confidence in the control environment.
Here are specific examples of how monitoring directly addresses SOC 2 criteria:
- Logical Access (CC6.1, CC6.3): Per CC6.1, the entity implements controls to prevent or detect and act upon the origination of unauthorized logical access. Continuous monitoring tools automatically track user access privileges, flag dormant accounts, and verify that access changes follow approved workflows. For CC6.3, which requires monitoring of access to sensitive data, automated systems provide a clean, time-stamped log proving that only authorized individuals accessed critical systems, thereby satisfying the auditor’s evidence requirements.
- Vulnerability Management (CC7.1): CC7.1 states that the entity uses detection and monitoring procedures to identify potential vulnerabilities. Instead of scrambling to conduct scans before an audit, automated vulnerability scanners continuously assess the environment for missing patches and newly disclosed threats. This provides a verifiable record of a consistent, proactive process for mitigating security risks, which is exactly what auditors look for.
- Anomaly and Threat Detection (CC7.2): This criterion requires monitoring to detect changes that could impact system objectives. A Security Information and Event Management (SIEM) system is a primary tool for this, aggregating logs to identify anomalous activities like brute-force login attempts or unusual data exfiltration patterns. These system-generated alerts serve as concrete evidence of active monitoring controls.
A common mistake is treating monitoring as a simple checkbox. For SOC 2, it is the central nervous system of your compliance program. Its function is to provide an early warning system that identifies control deviations before an auditor does, preventing them from becoming audit exceptions.
This shift to perpetual vigilance has fundamentally changed how companies must budget for SOC 2. The cost is no longer a one-time audit fee but an ongoing operational expense, with annual spending on monitoring tools and services often landing between $10,000 and $30,000. These costs are in addition to audit fees and are driven by the non-negotiable requirement for 6-12 months of evidence. To explore SOC 2 certification cost trends in more detail, external analyses offer valuable insights.
Mitigating Audit Risk and Reducing Remediation Stress
The primary objective for any CISO or GRC manager undergoing a SOC 2 audit is to avoid a qualified opinion. A “pass with exceptions” can delay or kill enterprise deals and requires uncomfortable explanations to every new prospect.
Why does this matter for SOC 2? Continuous monitoring is your primary defense against a qualified opinion. By providing a real-time dashboard of your compliance posture, it enables your team to identify and remediate control gaps as they occur. This proactive remediation prevents the high-stress, last-minute fire drills that happen when a control failure is discovered mid-audit, which can lead to scope exceptions or a qualified report. By embedding these practices into daily operations, compliance shifts from a disruptive, annual event to a predictable and manageable business function, laying a resilient security foundation that strengthens audit readiness.
Breaking Down Your SOC 2 Monitoring Costs
Budgeting for SOC 2 continuous monitoring requires a detailed breakdown of expenses rather than a single, aggregate number. The total cost is a composite of software licenses, internal personnel time, and specialized third-party services. Miscalculating this can lead to budget overruns, strained engineering teams, and potential audit delays.
Why does this matter for SOC 2? A granular budget allows you to make strategic investment decisions that directly support your compliance objectives. For example, investing in a tool that automates evidence collection for controls like CC6.1 (Logical Access) or CC7.1 (Vulnerability Management) can yield a direct ROI by freeing up engineering resources. Understanding how monitoring cloud services to optimize performance and cost also plays a crucial role, as inefficient monitoring can inflate infrastructure spending.
Tooling Costs
Your technology stack is the backbone of an effective continuous monitoring program. These tools automate the collection and analysis of evidence required by auditors.
Your primary tooling expenses will fall into these categories:
-
Compliance Automation Platforms: These platforms serve as a central command center, integrating with your tech stack (e.g., AWS, Azure, GCP) to automatically collect evidence and map it directly to SOC 2 criteria. Annual costs range from $7,500 to over $30,000, depending on company size and system complexity.
-
Security Information and Event Management (SIEM) Systems: A SIEM is essential for meeting monitoring-related criteria like CC7.2. It aggregates and analyzes log data from across your environment to detect security incidents. Costs vary widely, from $5,000 per year for a basic cloud-native solution to $50,000+ per year for advanced enterprise platforms.
-
Vulnerability Scanners: To provide evidence for control CC7.1, you need tools that continuously scan your systems for vulnerabilities. Budget between $2,000 and $15,000 annually for reputable scanning solutions.
-
Endpoint Detection and Response (EDR): EDR solutions monitor employee workstations and servers, providing crucial evidence for controls related to malware protection and device security (CC7.2, CC7.3). Pricing is typically on a per-endpoint basis, often starting at $8 to $15 per endpoint per month.
Personnel and Internal Resource Costs
The most frequently underestimated expense is the time your internal team spends on compliance tasks. Without automation, the manual burden of collecting evidence, performing control checks, and remediating issues falls directly on your engineering and security staff.
This internal effort represents a significant financial drain. For a mid-sized company, manual compliance activities can consume between 700 and 1,000 staff hours per year. This is time your engineers could be spending on product development rather than taking screenshots for an audit.
Why does this matter for SOC 2? Quantifying this internal cost is critical for justifying an investment in automation. If an engineer earning $150,000 per year spends 20% of their time on manual evidence gathering, that’s a $30,000 annual cost. A tool that reduces that effort by 80% provides a clear and immediate ROI while improving the quality and consistency of evidence for your audit.
External Services Costs
Even with a strong internal team and modern tools, you will likely require external services to meet specific SOC 2 requirements and fill expertise gaps.
Plan on budgeting for these common third-party services:
-
Annual Penetration Test: A requirement for satisfying CC7.1, a penetration test simulates a real-world attack to test your defenses. Costs typically range from $10,000 to $30,000, depending on the scope.
-
Managed Detection and Response (MDR): If you lack a 24/7 internal security operations center (SOC), an MDR provider can monitor your SIEM and respond to threats, helping you meet continuous monitoring requirements for a cost of $10,000 to $40,000+ per year.
-
Compliance Consultants or vCISOs: If your organization lacks in-house GRC expertise, a consultant can help design your control framework and prepare for the audit. Engagements can range from $5,000 for short-term project work to over $100,000 annually for a fractional CISO.
This detailed breakdown serves as a strategic roadmap for building a sustainable compliance program. By understanding where every dollar is going, you can construct an efficient, audit-ready system that withstands scrutiny and prevents the last-minute financial chaos that can jeopardize your SOC 2 report.
Comparing Monitoring Approaches And Pricing Models
Selecting a continuous monitoring strategy is a critical decision that directly impacts your budget, team workload, and the long-term viability of your SOC 2 program. You have three primary options: a do-it-yourself (DIY) approach using disparate tools, adopting a compliance automation platform, or outsourcing to a managed service provider.
Why does this matter for SOC 2? Your choice determines the nature and quality of evidence you can provide to an auditor. A poorly chosen approach can lead to incomplete evidence, excessive manual labor, and a higher risk of audit exceptions. Each option presents a different mix of software costs, internal labor expenses, and reliance on external GRC expertise.
This infographic outlines the core cost drivers that define each approach.
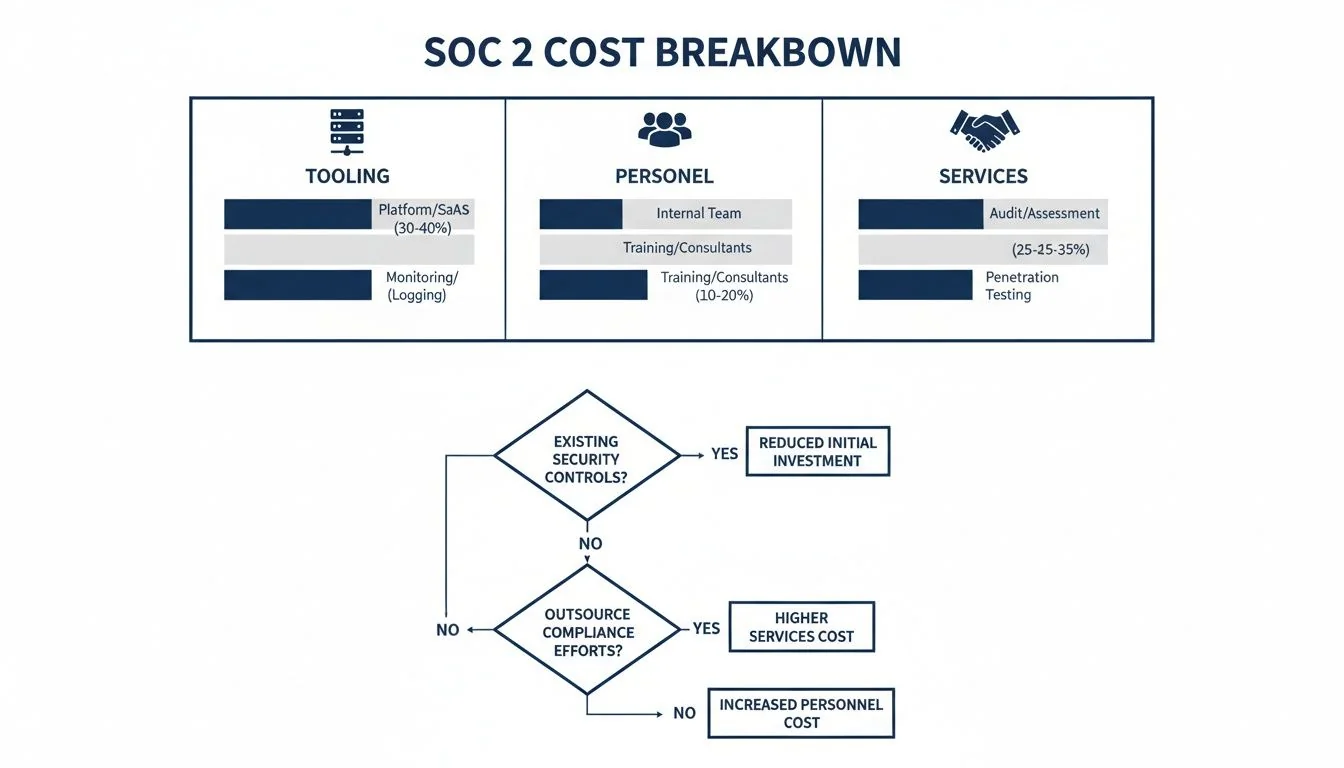
The DIY approach appears inexpensive initially but incurs significant hidden personnel costs. Conversely, managed services shift the entire cost burden to the service fee.
The DIY Approach With Separate Tooling
The DIY model involves manually integrating separate tools—such as a SIEM, vulnerability scanner, and EDR solution—and managing evidence collection yourself. This can seem cost-effective if you already own some of these tools.
However, the real cost lies in the immense internal effort required. Engineers must build and maintain custom integrations, write scripts to extract evidence, and manually correlate data from disparate systems into spreadsheets for the audit.
This hidden labor cost is substantial. For a mid-sized company, manual evidence collection can easily consume 1,000 staff hours annually, diverting valuable engineering resources from product innovation.
Why does this matter for SOC 2? This approach is brittle and highly susceptible to human error. It is difficult to prove the “continuous” aspect of monitoring to an auditor when evidence is collected in manual, periodic batches. This path is only viable for mature organizations with a large, dedicated security team and a pre-existing, well-integrated security infrastructure.
Compliance Automation Platforms
Compliance automation platforms have become the standard for most technology companies pursuing SOC 2. These are integrated solutions that connect directly to your cloud environments (AWS, GCP, Azure), HR systems, and code repositories to automate the entire evidence collection lifecycle.
These platforms perform checks 24/7, continuously monitoring configurations, user access, and other key controls. When a configuration drifts from policy, a real-time alert is generated and automatically mapped to a specific SOC 2 control, such as CC6.1 (Logical Access) or CC7.1 (Vulnerability Management). Pricing is typically a subscription based on factors like employee count or the number of connected systems. For a detailed overview, it’s useful to understand the full scope of SOC 2 automation.
Why does this matter for SOC 2? This approach provides the best balance of cost and effectiveness. It drastically reduces the manual evidence-gathering burden on engineers—often by over 80%—and provides a centralized dashboard for managing all audit evidence. This ensures evidence is complete, consistent, and readily available for auditors.
Managed Services and vCISO Engagements
For companies with no internal security or compliance expertise, a managed service or virtual CISO (vCISO) offers a turnkey solution. In this model, a third-party firm assumes full responsibility for your continuous monitoring program.
They manage tool selection, configuration, alert monitoring, and direct interaction with the auditor. This is the most expensive option, with retainers often ranging from $5,000 to over $15,000 per month.
Why does this matter for SOC 2? This model provides instant expertise, which is invaluable for early-stage startups needing to achieve compliance quickly to secure a critical enterprise contract. The primary benefit is access to on-demand GRC professionals. The tradeoff is a lack of internal skill development, creating long-term dependency on the provider.
Comparison of SOC 2 Continuous Monitoring Models
This table compares the three main approaches based on cost, effort, required expertise, and scalability to help organizations select the best fit for their SOC 2 journey.
| Criteria | DIY with Tooling | Compliance Automation Platform | Managed Service / vCISO |
|---|---|---|---|
| Annual Cost | $10,000 - $40,000+ (mostly personnel) | $15,000 - $50,000 (platform + some personnel) | $60,000 - $180,000+ (all-inclusive fee) |
| Implementation | 3-6 months | 1-3 months | 1-2 months |
| Internal Effort | Very High (dedicated engineering time) | Low (focused on remediation) | Very Low (provider handles everything) |
| Required Expertise | High (in-house GRC & security engineering) | Medium (understanding of controls & remediation) | Low (provider brings the expertise) |
| Scalability | Poor (brittle and requires constant maintenance) | High (designed to scale with your tech stack) | High (provider scales with your needs) |
For most technology companies, the DIY path creates an unsustainable operational drag, while a fully managed service can be cost-prohibitive. Compliance automation platforms typically represent the most effective balance of cost, efficiency, and long-term sustainability, enabling organizations to build a robust, evidence-backed security program that satisfies auditor requirements.
Calculating the ROI of Your Monitoring Investment
Viewing continuous monitoring as a mere compliance cost is a strategic error. It is not a cost center but a business enabler that accelerates revenue and mitigates risk. A proper ROI calculation extends beyond the software price tag to quantify efficiency gains, risk reduction, and faster sales cycles.
Why does this matter for SOC 2? This ROI-focused perspective is crucial for securing budget approval from leadership. You are not just purchasing a tool to pass an audit; you are investing in a system that makes the engineering team more productive, shortens the sales cycle for enterprise deals, and builds a defensible security posture that increases company valuation.
Quantifying Cost Savings
The most direct return on a monitoring investment comes from quantifiable cost reductions.
- Reduced Manual Labor: Automated monitoring can reduce the time engineers spend on manual evidence collection by over 80%. This translates to hundreds of hours of high-value engineering time redirected from compliance tasks back to product development.
- Faster Audit Cycles: With evidence automatically collected and organized, auditors spend less time on fieldwork. This directly reduces the billable hours from your audit firm and minimizes the internal disruption caused by the audit.
- Avoided Remediation Costs: Continuous monitoring acts as an early warning system, identifying control failures in real-time rather than six months later during an audit. This proactive approach prevents the high costs associated with emergency remediation, re-testing fees, and project delays.
Why this matters for SOC 2: Investing in continuous monitoring is about building an efficient, predictable compliance engine. It pays for itself by eliminating wasted engineering hours and preventing the costly surprises that can lead to a qualified audit opinion.
The Opportunity Cost of Inadequate Monitoring
The most significant component of your ROI is often the costs you avoid. Inadequate monitoring exposes the business to substantial risks, including security breaches, regulatory fines, and reputational damage, with potential costs that dwarf any investment in monitoring tools. Ongoing SOC 2 maintenance typically costs about 40% of the initial certification expense. A significant portion of that spend is dedicated to continuous monitoring, which can range from $5,000 to $15,000 annually for a mid-sized company. Trying to cut corners here merely defers the cost to a larger, more catastrophic failure later on. You can find more detail in the breakdown of SOC 2 compliance costs on sprinto.com.
Connecting Monitoring to Revenue Acceleration
Ultimately, an investment in continuous monitoring is directly linked to revenue. A robust monitoring program provides the verifiable proof of security that enterprise customers demand before signing a contract. It transforms a SOC 2 report from a compliance burden into a powerful sales enablement tool.
Why does this matter for SOC 2? A clean SOC 2 Type 2 report, supported by months of auditable data from your monitoring system, removes security as a procurement obstacle. It signals to prospective customers that you are a mature, trustworthy partner, enabling your sales team to close larger contracts more quickly. This is the most compelling argument for any budget discussion. A strong monitoring program proves your commitment to security is not just a marketing claim but an operational reality, transforming the SOC 2 continuous monitoring cost from an expense into a strategic driver of business growth.
Optimizing Your Investment for Audit Readiness
A well-implemented continuous monitoring program is the single most valuable asset for a successful SOC 2 audit. It functions as the definitive source of truth for control effectiveness, significantly reducing the time, cost, and friction associated with evidence collection. It is the key to transforming an audit from a chaotic, manual scramble into an orderly review of pre-collected data.

Why does this matter for SOC 2? This proactive approach is essential for meeting the stringent evidence requirements of a Type 2 report, which assesses control performance over a 6-12 month period. Without an automated system for continuous evidence collection, you risk evidence gaps, control failures, and a qualified opinion that can derail your business objectives.
Integrating Monitoring With Your Audit Workflow
The most efficient monitoring programs integrate directly with the audit process itself. Modern compliance automation platforms often include auditor-specific portals that provide read-only access to the necessary evidence.
Why does this matter for SOC 2? This direct-access model eliminates the need for endless email threads and screen-sharing sessions to transfer evidence. It presents a professional, organized front that builds immediate trust and credibility with your audit firm. The goal is to make the auditor’s job as straightforward as possible. Presenting a complete, well-organized body of evidence on day one sets the stage for a faster, smoother, and more efficient audit.
Mapping Automated Evidence to SOC 2 Controls
A critical feature of effective monitoring platforms is their ability to map automated evidence directly to specific SOC 2 criteria. This provides an unambiguous link between your technical controls and the AICPA TSC framework.
For example, you can configure your platform to:
- Tie failed login alerts directly to CC6.1 (Logical Access Control): This gives auditors a clear, automated log demonstrating how you monitor and respond to potential unauthorized access.
- Link vulnerability scan results to CC7.1 (Vulnerability Management): This creates a continuous record proving you have a systematic process for identifying and remediating security weaknesses.
- Connect cloud infrastructure change logs to CC8.1 (Change Management): This shows auditors that all modifications to production systems adhere to a documented approval process.
Why does this matter for SOC 2? This mapping removes ambiguity. It translates technical data from your tools into the precise language of the AICPA Trust Services Criteria, leaving no room for misinterpretation and streamlining the auditor’s review process.
Generating Pre-Audited Reports to Streamline Fieldwork
Before an auditor begins fieldwork, a robust monitoring platform can generate comprehensive reports that function as a “pre-audit.” These reports summarize the operational status of every control throughout the entire observation period, highlighting any deviations and the corresponding remediation actions taken.
Why does this matter for SOC 2? This capability fundamentally changes the audit dynamic. Instead of starting from a blank slate, your auditor begins with a detailed summary of your compliance posture, complete with supporting evidence. This allows them to focus their limited time on testing key controls rather than on basic document requests, which significantly accelerates the audit timeline. The reduction in billable audit hours can directly lower the overall SOC 2 continuous monitoring cost.
By providing continuous, automated evidence, you build a foundation of trust and transparency with your auditor. This not only ensures a successful SOC 2 Type 2 report but also fosters a genuinely stronger security posture. This tangible commitment to security becomes a cornerstone for business growth, reassuring enterprise customers and stakeholders that their data is protected by a system of verifiable, always-on controls, making the investment in monitoring an essential pillar of not just compliance, but of trust.