A Service Organization Control (SOC) 2 report is a voluntary, market-driven assurance report issued by a licensed CPA firm that attests to the controls a service organization has in place relevant to the security, availability, processing integrity, confidentiality, and/or privacy of its systems. The General Data Protection Regulation (GDPR) is a mandatory legal framework enacted by the European Union that regulates the collection, processing, and storage of personal data belonging to individuals within the EU. While SOC 2 demonstrates operational control effectiveness to business partners, GDPR enforces legal obligations to protect individual privacy rights.
Defining SOC 2 and GDPR Frameworks
A SOC 2 report is an attestation performed under the standards set by the American Institute of Certified Public Accountants (AICPA). Its purpose is to provide assurance to customers and stakeholders that a service organization has designed and implemented effective controls over one or more of the five Trust Services Criteria (TSCs): Security, Availability, Processing Integrity, Confidentiality, and Privacy. For organizations pursuing SOC 2, this matters because the report serves as direct, third-party validation of their control environment, which is often a contractual requirement from enterprise customers.
The General Data Protection Regulation (GDPR) is a comprehensive data privacy law that became enforceable on May 25, 2018. It applies to any organization, regardless of location, that processes the personal data of EU residents. Its core mandate is to grant individuals control over their personal data and to unify data protection regulations across the EU. This is critical for any organization seeking SOC 2 compliance that also serves or may serve the European market, as GDPR’s legal requirements for data handling must be integrated into the control environment being audited.

Core Distinctions and Drivers
The enforcement mechanisms for each framework highlight their fundamental differences. Non-compliance with GDPR can result in significant financial penalties, with fines of up to €20 million or 4% of a company’s annual global turnover, whichever is higher. Enforcement is carried out by data protection authorities within the EU.
SOC 2, in contrast, has no direct legal or governmental enforcement. The “penalty” for not having a SOC 2 report is commercial; it manifests as lost business opportunities, stalled sales cycles, and the inability to meet contractual security requirements from customers. With an estimated 92% of SaaS buyers requiring a SOC 2 report, its driver is purely market-based demand. This matters for a company pursuing SOC 2 because the primary motivation is to build trust with customers and unblock revenue, not to avoid regulatory fines. A typical company privacy policy is a direct artifact of GDPR requirements, whereas a SOC 2 report is an artifact of business-to-business assurance needs.
Here’s a clear, side-by-side look at how they stack up.
| Feature | SOC 2 | GDPR |
|---|---|---|
| Type | Assurance Framework | Legal Regulation |
| Origin | AICPA (U.S. Accounting Body) | European Union Law |
| Focus | Security of service organization systems | Protection of individual personal data |
| Applicability | Market-driven (customer demand) | Legally mandatory for EU data |
| Enforcement | Loss of business, contractual risk | Fines, legal action |
| Scope | Based on chosen Trust Services Criteria | Broadly defined personal data of EU residents |
A key aspect of SOC 2 is its inherent flexibility. An organization scopes its audit by selecting the applicable SOC 2 Trust Services Criteria relevant to the services and commitments it provides to customers. GDPR offers no such flexibility; its articles apply universally to all organizations within its jurisdiction. For those preparing for a SOC 2 audit, understanding this distinction is crucial for defining the audit’s scope while ensuring that mandatory legal obligations like GDPR are concurrently addressed within the control framework.
Analyzing Scope, Purpose, and Legal Standing
SOC 2’s scope is organization-centric, focusing on the controls a service organization implements to protect its systems and the customer data it processes. The scope is defined by the service commitments made to customers. GDPR’s scope is data-centric; it applies to any organization worldwide that processes the personal data of an EU resident, regardless of where the organization is located. This matters for a company pursuing SOC 2 because it dictates how data must be classified and handled. The data within a SOC 2 audit’s scope may contain personal data subject to GDPR, meaning the controls must satisfy both the TSCs and GDPR’s legal requirements.
This difference in scope defines their purpose. SOC 2 is an attestation designed to build B2B trust and validate security claims. GDPR is a legal mandate created to protect the fundamental privacy rights of individuals.
In preparation for a SOC 2 audit, the objective is to gather evidence demonstrating that controls were operating effectively over a defined period (typically 3-12 months for a Type 2 report). For GDPR, the objective is to maintain continuous, demonstrable compliance with its legal articles, including the ability to respond to data subject requests within a 30-day window.
Legal Standing and Core Mandates
The most significant distinction is legal standing. SOC 2 is a voluntary industry standard developed by the AICPA, not a law. Its adoption is driven by market and contractual demands. GDPR is a legally binding regulation enforced by supervisory authorities.
This distinction directly impacts the preparation process. Preparing for a SOC 2 audit involves performing a gap analysis against the AICPA’s Trust Services Criteria, implementing controls, and collecting evidence for an auditor. This includes specific technical and operational controls, such as implementing logical access controls based on the principle of least privilege (as required by CC6.1) or maintaining a formal change management process (as required by CC8.1). In contrast, GDPR readiness involves legal and procedural activities, such as conducting a Data Protection Impact Assessment (DPIA) for high-risk processing activities and establishing a lawful basis for processing personal data.
For those needing a deeper dive into GDPR’s technical and legal requirements, this practical AI GDPR compliance guide is a useful resource.
SOC 2 vs GDPR A Comparative Breakdown
This table clearly shows why SOC 2 and GDPR are not interchangeable. Understanding these distinctions is the key to planning your compliance roadmap and allocating resources effectively.
| Attribute | SOC 2 | GDPR |
|---|---|---|
| Primary Focus | Systems and operational controls of a service organization | The rights of individuals and their personal data |
| Geographic Scope | Defined by your service commitments and customer locations | Any organization processing personal data of EU residents |
| Legal Status | Voluntary industry standard (AICPA) | Legally binding regulation (EU Law) |
| Key Output | An audit report (Type 1 or Type 2) from a CPA firm | No formal certification; ongoing documented compliance |
| Enforcement | Market-driven; loss of contracts and business opportunities | Regulatory fines (up to 4% of global turnover) and legal action |
For an organization pursuing SOC 2, this comparison highlights a critical strategic point: while SOC 2 is the immediate commercial goal, the controls built to achieve it provide a powerful technical foundation for meeting GDPR’s legal requirements. For example, the evidence gathered to demonstrate effective system monitoring for SOC 2 (e.g., audit logs, alerts) is the same evidence needed to demonstrate the ability to detect and respond to a data breach under GDPR. Properly leveraging this overlap is key to achieving efficient SOC 2 audit readiness.
How SOC 2 Controls Overlap with GDPR Articles
The most direct and significant overlap between SOC 2 and GDPR exists between the SOC 2 Trust Services Criteria (TSCs) and GDPR’s Article 32, “Security of Processing.” This article requires organizations to implement “appropriate technical and organizational measures” to ensure data security. This language mirrors the entire purpose of a SOC 2 audit, which is to provide assurance over those very measures.
This overlap matters for a company pursuing SOC 2 because it allows for a “test once, satisfy many” approach. The evidence collected for the SOC 2 audit can be directly repurposed to demonstrate GDPR compliance, creating significant operational efficiency. For example, a SOC 2 auditor will test controls related to data encryption both at rest and in transit. This evidence directly satisfies a key technical measure expected under Article 32.
Mapping Common Criteria to GDPR Requirements
The SOC 2 Common Criteria (CC) series, which forms the mandatory foundation of every SOC 2 audit, provides a robust security baseline that aligns with GDPR’s requirements. This is why for a company focused on SOC 2, a well-executed audit inherently strengthens its GDPR posture.
Consider these specific mappings:
- Risk Management (CC3.0): This series requires a formal risk assessment process where the organization identifies, analyzes, and responds to risks. This process directly supports GDPR’s requirement to conduct a Data Protection Impact Assessment (DPIA) before engaging in high-risk data processing activities.
- Logical and Physical Access Controls (CC6.0): Controls implemented to meet CC6.1 (restricting logical access) and CC6.3 (reviewing user access) provide direct evidence that an organization is taking appropriate technical measures to prevent unauthorized access to personal data, a core GDPR requirement.
- Change Management (CC8.0): The documented processes for authorizing, testing, and deploying system changes, required by CC8.1, demonstrate a commitment to maintaining system integrity. This is a fundamental security principle under GDPR that ensures personal data is not improperly altered.
Your SOC 2 evidence for access reviews and data encryption directly serves as proof of the technical and organizational measures required under GDPR.
Go Deeper by Adding the Privacy Criterion
To maximize the overlap, an organization can include the optional SOC 2 Privacy criterion in its audit scope. This criterion is specifically designed to align with international privacy frameworks like GDPR and maps directly to many of its core principles. By doing so, a SOC 2 report becomes a much more powerful tool for demonstrating comprehensive data governance.
The overlap is massive. SOC 2’s privacy criterion mirrors GDPR’s principles of data minimization, purpose limitation, and individual rights, enabling 60–80% control reuse, according to mappings in GRC platforms like Sprinto and Vanta. For the tech and startup companies using SOC2Auditors.org, this means choosing an auditor with Type 1/2 expertise can put you on the fast track to GDPR alignment. The business impact is huge: a Forrester study of 500 B2B SaaS firms found that companies holding both credentials report 2.5x faster sales cycles and 30% higher win rates.
For a more detailed breakdown of these intersections, check out this excellent guide on the key differences and overlaps between GDPR and SOC 2.
Specifically, the Privacy criterion addresses concepts like notice, choice and consent, collection, use, and data disposal—all central tenets of GDPR. For example, a control designed to satisfy P3.1 (providing notice of privacy practices to data subjects) also helps fulfill GDPR’s transparency requirements under Articles 13 and 14. For a company preparing for SOC 2, recognizing this strategic alignment is critical. It transforms the audit from a simple compliance exercise into a foundational step towards building a scalable, legally robust data governance program.
Industry Implications for SaaS, FinTech, and HealthTech
For companies in technology-driven sectors like SaaS, FinTech, and HealthTech, the relationship between SOC 2 and GDPR is not abstract; it directly influences product development, market expansion, and risk management. The industry context determines which framework takes precedence and how controls must be implemented to satisfy both commercial and regulatory demands. For any organization in these sectors pursuing SOC 2, understanding these industry-specific drivers is essential for correctly scoping the audit and ensuring its relevance.
A SaaS company targeting enterprise clients will find that a SOC 2 report is a non-negotiable prerequisite for sales conversations. However, if that company plans to expand into the European market, GDPR compliance becomes a legal necessity. This matters for their SOC 2 journey because the controls they build must be robust enough to not only pass the audit but also to support GDPR’s stringent requirements for data subject rights and cross-border data transfers.
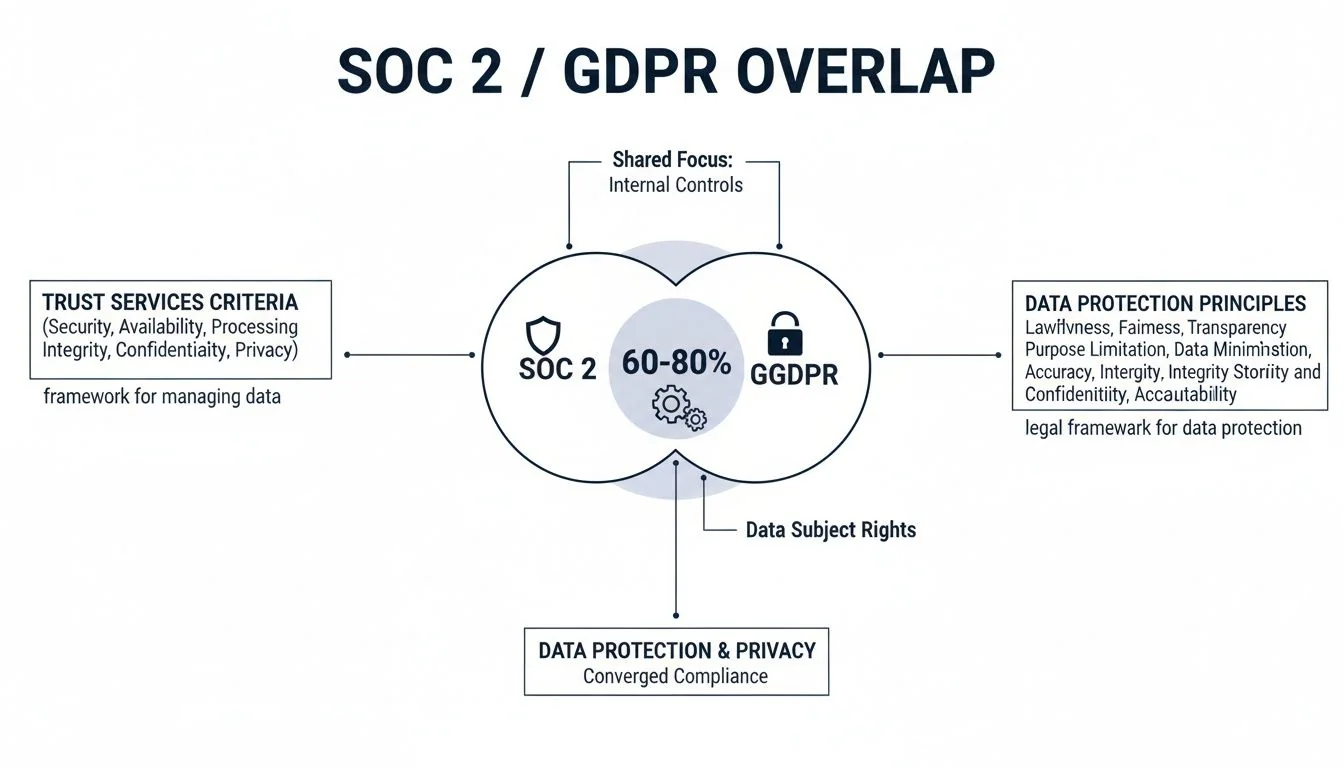
As the diagram shows, a significant 60-80% overlap in required controls means that a strategic approach can address the majority of requirements for both frameworks simultaneously, optimizing resource allocation.
FinTech Data Protection Nuances
In the FinTech sector, a SOC 2 report is the baseline evidence required by banking partners and institutional clients to verify operational integrity and system security. The audit’s focus on the Security and Processing Integrity TSCs is particularly relevant.
However, GDPR classifies financial data as sensitive personal information, imposing a higher standard of care. This is critical for a FinTech company preparing for a SOC 2 audit. The audit scope must include controls that not only secure the processing environment but also explicitly address GDPR requirements like lawful basis for processing, data portability, and the right to erasure for individual customers’ financial data.
For FinTechs, the SOC 2 report proves system reliability to partners, while the underlying controls must also be designed to meet GDPR’s heightened standards for protecting sensitive personal financial data.
HealthTech and the HIPAA Overlap
HealthTech companies operate in a complex regulatory environment, often juggling SOC 2, GDPR, and the Health Insurance Portability and Accountability Act (HIPAA). Protected Health Information (PHI) under HIPAA is also considered a ‘special category of personal data’ under GDPR, requiring the highest level of protection.
This matters for a HealthTech company pursuing SOC 2 because the audit provides an opportunity to unify controls across all three frameworks. The technical and administrative safeguards implemented for HIPAA can be directly mapped to SOC 2’s Confidentiality criterion and GDPR’s Article 32.
Actionable guidance includes:
- Data Segregation: SOC 2 controls for data segregation and de-identification should be implemented to satisfy both HIPAA’s Privacy Rule and GDPR’s principle of data minimization.
- Encryption Standards: Evidence of PHI encryption at rest and in transit, required by the HIPAA Security Rule, can be repurposed to meet SOC 2’s CC7.1 (information protection) and GDPR’s Article 32.
- Breach Notification: An incident response plan must be designed to meet GDPR’s strict 72-hour notification deadline, which is far more stringent than HIPAA’s 60-day window. This robust plan will strengthen the SOC 2 control environment and ensure compliance on all fronts.
For any organization pursuing SOC 2, understanding these industry-specific drivers is crucial. It ensures the audit scope is relevant, satisfies key stakeholder demands, and builds a powerful foundation for meeting complex legal obligations like GDPR, leading to a more efficient path to audit readiness.
Audits Timelines and Operational Demands
A SOC 2 audit is a project-based attestation with a defined lifecycle, whereas GDPR compliance is a continuous, legally mandated state of being. This fundamental difference in timelines and operational demands is critical for any organization planning its SOC 2 journey, as it dictates resource allocation and long-term strategy. The SOC 2 process provides a structured framework for building and validating controls, while GDPR requires those controls to operate perpetually and respond to real-time events.
The Structured Cycle of a SOC 2 Audit
The SOC 2 audit process is cyclical and predictable. It typically begins with a readiness assessment to identify control gaps. This is often followed by a Type 1 audit, which assesses the design of controls at a single point in time and can be completed in 2–4 weeks once the controls are in place.
The primary engagement is the Type 2 audit, which tests the operating effectiveness of controls over a specified period, usually 3 to 12 months. After this observation period, the CPA firm conducts its fieldwork and issues a formal report. This cycle repeats annually. This predictable rhythm matters for a company pursuing SOC 2 because it allows for clear project planning, budgeting, and resource management.
The core operational demand of SOC 2 is evidence collection for a defined audit period. Your team’s primary focus is gathering logs, screenshots, and documentation to prove to an auditor that controls were operating effectively from, for example, January 1st to June 30th.
GDPR’s Perpetual and Event-Driven Demands
GDPR’s timeline is continuous and reactive. Its operational demands are triggered by events and are subject to strict, legally mandated deadlines. This is why for a company preparing for SOC 2, it is crucial to design controls that can support these ongoing legal obligations, not just pass a point-in-time audit.
To get a feel for the project-based nature of SOC 2, you can learn more about how long a SOC 2 audit takes in our detailed guide.
Key ongoing GDPR obligations include:
- 72-Hour Breach Notifications: A personal data breach triggers a strict 72-hour window to notify the relevant supervisory authority. This requires a well-documented and tested incident response plan, a key component of the SOC 2 Security criterion.
- 30-Day Data Subject Access Requests (DSARs): An individual’s request for their personal data must be fulfilled within one month. This necessitates robust data mapping and retrieval processes, which are supported by the controls for data management and system operations tested in a SOC 2 audit.
- Maintaining Records of Processing Activities (ROPAs): Article 30 requires continuous documentation of all data processing activities. This is an ongoing administrative task, not a one-time project.
- Appointing a Data Protection Officer (DPO): Many organizations are required to appoint a DPO to oversee their data protection strategy, representing an ongoing operational role.
For an organization focused on SOC 2, the processes built to satisfy the TSCs—such as incident response, change management, and access controls—are the same processes that enable a company to meet GDPR’s perpetual, event-driven demands. Integrating these legal requirements into the SOC 2 control environment from the outset is the key to achieving efficient and sustainable SOC 2 audit readiness.
Building a Unified Compliance Roadmap
A unified compliance roadmap is a strategic plan that integrates multiple frameworks, such as SOC 2 and GDPR, into a single, efficient initiative. It focuses on identifying and leveraging overlapping control requirements to avoid redundant work. For a company pursuing SOC 2, this means designing security and operational controls from the outset to simultaneously address the legal and privacy requirements of GDPR. This approach transforms compliance from a series of disconnected projects into a cohesive governance program, reducing audit fatigue and accelerating time-to-market.

Step 1: Perform a Consolidated Gap Analysis
The first step is a consolidated gap analysis that assesses the current control environment against both the AICPA’s Trust Services Criteria and relevant GDPR articles. This is critical for a company pursuing SOC 2 because it immediately identifies where planned SOC 2 controls can also satisfy GDPR requirements. For example, when evaluating access control policies to meet SOC 2’s Common Criteria 6.0, the analysis should simultaneously map these controls to GDPR’s Article 32. This prevents the need for a separate, duplicative assessment later.
The output of this analysis should be a unified control matrix that lists each control, the SOC 2 TSC it addresses, and the corresponding GDPR article it supports. This matrix becomes the central blueprint for the compliance effort, ensuring that every control is implemented with maximum efficiency.
Step 2: Implement Controls for Dual-Purpose Evidence
With the roadmap from the gap analysis, the next step is to implement controls with dual-purpose evidence collection in mind. This is an operational discipline that streamlines the audit process. For instance, a logging and monitoring system required for a SOC 2 audit to demonstrate compliance with CC7.2 (monitoring of controls) and CC7.3 (monitoring for security incidents) should be configured to also capture events relevant to GDPR, such as access to personal data stores.
When you configure your Security Information and Event Management (SIEM) tool, create alerts and reports that can be used for both your SOC 2 auditor and a potential GDPR data breach investigation. This single system now generates evidence for two distinct purposes.
This matters for the SOC 2 journey because it simplifies evidence gathering during the audit observation period. Instead of ad-hoc data pulls, the required evidence is systematically collected in a format that serves both the SOC 2 auditor and the Data Protection Officer (DPO).
Step 3: Prioritize the SOC 2 Audit as a GDPR Accelerator
A successful SOC 2 audit is a powerful accelerator for demonstrating GDPR readiness. The formal, independent validation from a CPA firm provides tangible proof of the “technical and organizational measures” required by GDPR’s Article 32. This is especially true if the audit scope includes the Privacy or Confidentiality criteria. The SOC 2 report becomes a strategic asset that can be used to provide assurance to customers and partners concerned about GDPR compliance.
This approach transforms the SOC 2 audit from a market-driven requirement into a cornerstone of a comprehensive data governance program. The structured, cyclical nature of SOC 2—readiness, Type 1, Type 2, and annual renewal—enforces a discipline of continuous improvement that directly supports ongoing GDPR obligations. For any organization navigating the landscape of SOC 2 vs GDPR compliance, this strategic alignment is the key to building a resilient, scalable, and efficient compliance posture. This strategic integration ensures that every step taken toward the SOC 2 audit also strengthens the organization’s overall data protection capabilities, making SOC 2 audit readiness a foundational element of long-term legal and commercial success.
Navigating the complexities of auditor selection can be daunting. At SOC2Auditors, we simplify the process by providing transparent, data-driven comparisons of over 90 verified audit firms. Find the right partner for your SOC 2 journey and ensure your compliance roadmap leads to success. Get your tailored auditor matches at https://soc2auditors.org.