A System and Organization Controls (SOC) 2 report is an attestation performed by a licensed Certified Public Accountant (CPA) firm, designed to evaluate and report on the effectiveness of a service organization’s controls over information and systems. For a Managed Service Provider (MSP), a SOC 2 report provides independent validation that its internal controls effectively secure and manage client data, based on the Trust Services Criteria established by the American Institute of Certified Public Accountants (AICPA).
Why SOC 2 Matters in the MSP World

For a Managed Service Provider, obtaining a SOC 2 report demonstrates that its internal processes meet specific standards across one or more of the five Trust Services Criteria (TSC): Security, Availability, Confidentiality, Processing Integrity, and Privacy. This matters for someone pursuing SOC 2 because it shifts the conversation with clients from subjective promises to objective, audited proof. The SOC 2 framework requires an MSP to design, implement, and operate controls relevant to its services, which are then tested by an independent auditor. This process substantiates claims of operational maturity and security, which is critical for winning and retaining clients concerned about supply chain risk.
Moving Beyond a Checkbox Mentality
The managed services market has matured, and clients now demand verifiable proof of security. Your SOC 2 report provides this proof by attesting to the effectiveness of your control environment. This matters for someone pursuing SOC 2 because it directly addresses the primary concerns of sophisticated clients, especially in regulated industries. A SOC 2 report is not merely a checklist; it is an auditor’s opinion on your ability to meet specific AICPA criteria.
Achieving this attestation validates your ability to:
- Protect client environments from unauthorized access, as required by the Security TSC (also known as the Common Criteria).
- Securely manage infrastructure and client data, aligning with controls for system monitoring and data protection.
- Demonstrate your own operational integrity, thereby reducing the perceived supply chain risk for your clients.
For an MSP pursuing SOC 2, the report transforms security from a marketing claim into a verified fact. It provides a formal attestation that you don’t just promise security; you have implemented and operate controls to achieve it. This is a powerful differentiator that answers client due diligence questions proactively.
A Framework for Trust and Growth
Pursuing SOC 2 compliance unlocks opportunities with larger, more mature clients—especially in regulated sectors like finance, healthcare, and technology, where it is often a non-negotiable vendor requirement. This matters for someone pursuing SOC 2 because the process itself forces the MSP to build a more resilient and mature organization. You will document processes, formalize controls, and embed a culture of security and accountability. This not only prepares you for the initial audit but establishes a system of continuous monitoring that makes future audits more efficient. To understand the ongoing commitment, you can review examples like Tackle’s SOC 2 Type II certification.
Scoping Your Audit: An MSP-Specific Approach

The scope of a SOC 2 audit defines the system, services, and criteria to be examined by the auditor. This matters for someone pursuing SOC 2 because proper scoping is the most critical factor in achieving a useful and cost-effective report. An over-scoped audit wastes resources on irrelevant controls, while an under-scoped audit results in a report that fails to provide the assurances your clients require, rendering the exercise pointless.
Mapping Your Services to System Boundaries
For an MSP, the “system” is the entire collection of infrastructure, software, people, processes, and data used to deliver the in-scope services. This means accurately identifying every component that supports your client commitments.
Your scope must include the specific components used to deliver the services you want covered in the report:
- Remote Monitoring and Management (RMM) platform
- Professional Services Automation (PSA) tool
- Backup and Disaster Recovery (BDR) solutions
- Managed Security services (e.g., EDR, SIEM, vulnerability scanners)
- Cloud infrastructure (e.g., AWS, Azure) hosting client data or internal tools
- The people (e.g., engineers, administrators) who operate these systems
Defining your scope is an exercise in precision. You are telling your auditor, “This is the promise we make to our clients, and these are the exact components and controls we use to fulfill that promise.” A well-defined scope ensures your final report directly addresses your customers’ biggest security and availability concerns.
Before finalizing your scope, a compliance risk assessment is essential. This process identifies risks to client data and system availability, providing a logical foundation for selecting your controls and Trust Services Criteria.
Selecting the Right Trust Services Criteria
After setting system boundaries, you must select the appropriate Trust Services Criteria (TSCs). Security is mandatory. The others are chosen based on the services you provide and the commitments you make to clients. This matters for someone pursuing SOC 2 because the selected TSCs determine which controls will be audited and what assurances the final report provides.
- Security (The Common Criteria): This is non-negotiable. It covers foundational controls like access management (CC6.0), network security, and change management (CC3.0). For an MSP, this directly addresses how you secure your RMM and PSA to prevent unauthorized access.
- Availability: Select this if you provide service level agreements (SLAs) for uptime. To meet AICPA criterion A1.2, which addresses recovery from disruptions, you must demonstrate controls like system redundancy and a tested disaster recovery plan.
- Confidentiality: This is mandatory if you handle sensitive client data (e.g., intellectual property, M&A plans). Controls must align with criterion C1.2, requiring the protection of confidential information through measures like data encryption and strict access policies.
- Processing Integrity: Add this if your services involve transaction processing where completeness, validity, accuracy, and timeliness are critical (e.g., financial data processing).
- Privacy: Include this if you handle Personally Identifiable Information (PII), which is subject to specific regulations. It requires controls over the collection, use, retention, disclosure, and disposal of personal information.
The market trend is toward more comprehensive reports. The 2024 SOC benchmark study shows that the inclusion of Confidentiality has climbed to 64.4% and Availability now sits at 75.3%. This data demonstrates that clients are specifically looking for assurances beyond the baseline Security criterion. A formal SOC 2 readiness assessment is the most effective way to finalize scope before engaging an auditor.
Implementing Controls and Gathering Evidence
This phase transitions your policies from documentation into operational practice. This matters for someone pursuing SOC 2 because auditors test the operating effectiveness of controls, not just their design. For an MSP, success depends on integrating SOC 2 requirements into the tools used daily—your RMM, PSA, and security platforms—to generate auditable evidence as a byproduct of normal operations.
Mapping Controls to Your Daily MSP Operations
Translate abstract AICPA criteria into concrete actions your team performs. This reframes compliance from an external burden into a structured methodology for delivering secure, high-quality services.
Here are specific examples of this mapping:
-
Security (CC6.1 - Logical Access): This criterion requires restricting access to authorized users. For an MSP, this translates to implementing role-based access control (RBAC) in your RMM and PSA. Your evidence would be screenshots of user permission groups (e.g., “Tier 1 Technician” vs. “Senior Engineer”) and logs from your identity provider demonstrating quarterly user access reviews.
-
Availability (A1.2 - System Redundancy and Recovery): This aligns with your BDR service. A disaster recovery plan is insufficient evidence on its own. Your auditor will require reports from your BDR solution showing successful backup jobs and, critically, documentation from your annual DR test, including test objectives, outcomes, and remediation actions.
-
Confidentiality (C1.2 - Data Destruction): This applies to your client offboarding process. The control is a documented offboarding checklist. The evidence is the closed PSA ticket detailing the steps taken to securely delete client data from all systems, including backups, with sign-off from the responsible personnel.
Automating Evidence Collection: The MSP Advantage
Manual evidence collection is inefficient and prone to gaps, which can lead to audit exceptions. Your RMM, PSA, and security tools are your primary sources of evidence, but they must be configured for audit readiness.
Audit Mindset: If it is not logged, it did not happen. Configure your systems to capture and retain the data needed to prove your controls are operating effectively over the entire audit period.
Leverage your existing toolset to create a repeatable, auditable trail:
-
Change Management (CC3.1): Use your PSA as the single source of truth. A dedicated “Change Request” ticket type can enforce an approval workflow. An export of these tickets from the audit period, showing timestamps, approvals, and post-implementation review, serves as powerful evidence.
-
User Access Reviews (CC6.3): Use an identity provider like Azure AD or Okta to automate the generation of quarterly reports showing all accounts with administrative access to in-scope systems. Archiving these reports provides time-stamped evidence of regular reviews.
A Practical Table for Mapping MSP Controls
This table connects common MSP services and controls directly to specific AICPA requirements and explains their relevance to a SOC 2 audit.
Mapping MSP Services to SOC 2 Trust Services Criteria
This table provides practical examples of how common MSP services and operational controls align with the AICPA’s Trust Services Criteria, helping MSPs connect their daily activities to specific SOC 2 requirements.
| Trust Service Criterion | Example MSP Control or Service | Applicable AICPA Requirement (Example) | Why It Matters for an MSP |
|---|---|---|---|
| Security | Implementing mandatory MFA on all administrative accounts for the RMM, PSA, and cloud consoles. | CC6.1 - Restricts logical access to authorized individuals. | This is a foundational control that auditors scrutinize. It directly mitigates the risk of unauthorized access to your most powerful tools and client environments. |
| Availability | Performing and documenting annual failover testing of managed backup and disaster recovery (BDR) services. | A1.2 - Addresses the recovery from disruption to meet objectives. | This proves your BDR service isn’t just “shelfware.” It shows clients you can meet recovery time objectives (RTOs) when an incident occurs. |
| Confidentiality | Using a formal data classification policy to apply encryption to all client data stored in your cloud tenant. | C1.2 - Addresses the protection of confidential information. | This demonstrates you can identify and protect a client’s sensitive information, a key requirement for winning business in finance or healthcare. |
| Security | Running automated, monthly vulnerability scans on all in-scope servers and tracking remediation in the PSA. | CC7.1 - Detects and responds to vulnerabilities. | This provides a clear, auditable trail of your patch and vulnerability management process, showing you proactively reduce the attack surface. |
By building evidence collection into standard operating procedures, you achieve a state of continuous compliance, dramatically reducing audit friction and ensuring you have consistent, accessible records when auditors request proof.
Navigating Common Pitfalls in an MSP’s SOC 2 Journey
Pursuing SOC 2 compliance presents several common pitfalls that can delay audits, increase costs, and result in a qualified report with exceptions. This matters for someone pursuing SOC 2 because these mistakes directly undermine the goal of building client trust. The most damaging error is the policy versus reality gap.
MSPs often create well-defined policies for processes like patch management or user access reviews, but fail to execute them consistently. When an auditor requests evidence, logs from the RMM or identity provider reveal a discrepancy between the policy and actual practice. For example, a policy may state critical patches are deployed within 30 days. If an auditor finds servers with overdue patches at 60 or 90 days, this is a direct contradiction of a stated control. This leads to an audit exception, particularly for a crucial control under the Security criterion like CC7.1 (vulnerability management).
The Peril of Incomplete Evidence
Another significant pitfall is the failure to produce tangible evidence to support a control’s operation. This matters for someone pursuing SOC 2 because without verifiable proof, from an auditor’s perspective, the control was not performed.
Consider this audit failure scenario:
- The Control: The MSP’s policy mandated annual security awareness training for all technical staff, a control related to CC2.1 (communication and training).
- The Breakdown: The training was conducted, but no attendance records were kept, and no attestations of completion were collected.
- The Audit Result: The MSP could only provide the training slides. Without proof of who attended and acknowledged the material, the auditor issued an exception.
The rule of any audit is: if you cannot prove it, you did not do it. Evidence must be concrete, consistent, and irrefutable. Your RMM, PSA, and identity provider (IDP) are not just operational tools; they are the backbone of your SOC 2 evidence repository.
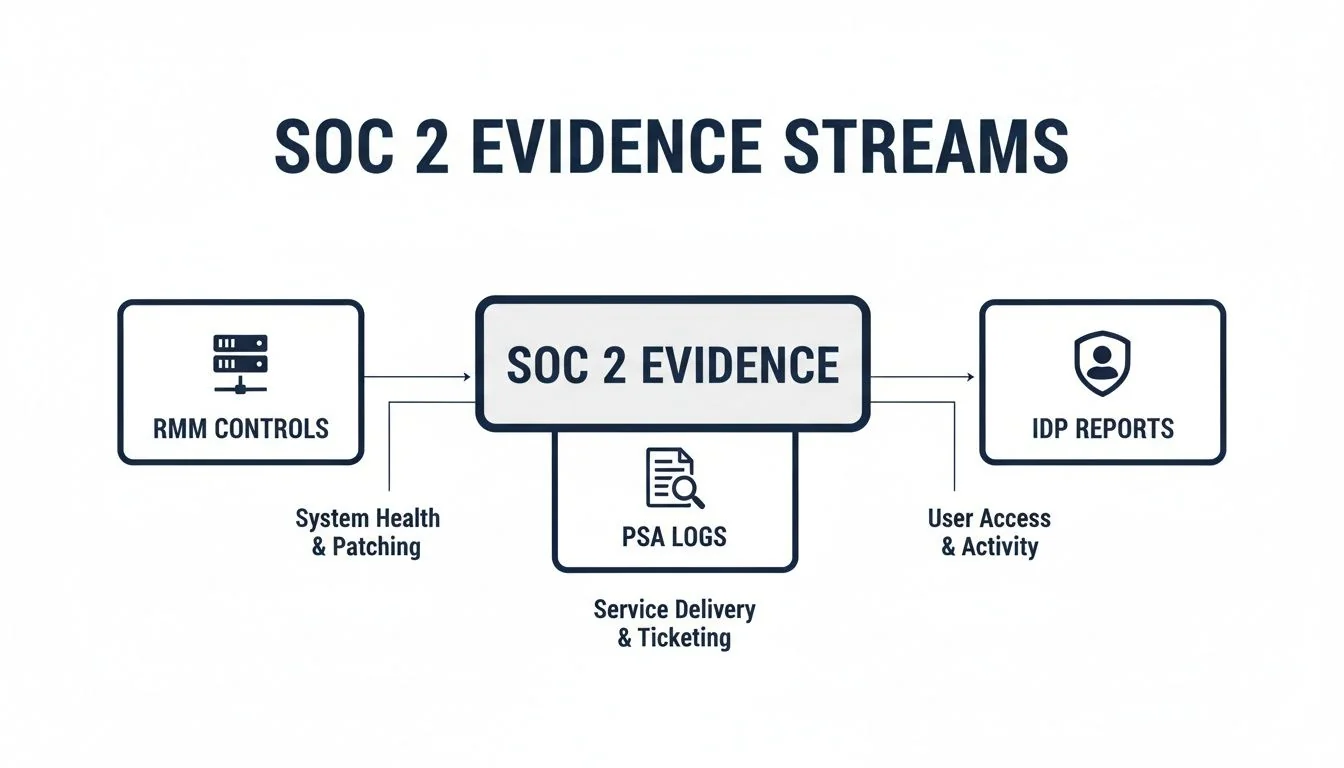
This diagram illustrates how operational data from your core platforms—RMM logs, PSA tickets, and IDP reports—serve as primary audit artifacts.
Mis-Scoping the Audit Boundaries
Incorrectly defining the audit’s system boundaries is a frequent and costly error. Omitting a critical component, such as a third-party data center or a cloud storage provider used for client backups, will lead to an audit exception. The system description in your report must perfectly mirror all components involved in delivering the in-scope services. This matters for someone pursuing SOC 2 because a report with an inaccurate system description fails to provide the assurance clients are seeking. Avoiding these common mistakes—closing the policy-reality gap, collecting robust evidence, and meticulously defining your scope—is fundamental to a successful audit and a clean report.
Choosing Your Auditor and Understanding the Costs
Selecting a SOC 2 auditor is a critical decision that directly impacts the cost, timeline, and value of your final report. This matters for someone pursuing SOC 2 because you are hiring a licensed CPA firm to formally attest to your security controls against AICPA standards. The right firm understands your business model and produces a report that helps win new clients; the wrong one can lead to an inefficient, overpriced audit and a confusing report.
Large National Firm vs. Boutique Specialist
The choice between a large national firm and a specialized boutique depends on your target market.
-
Large National Firms: These firms offer significant brand recognition, which can be valuable when targeting Fortune 500 clients. However, they are typically more expensive, less flexible, and may assign junior auditors unfamiliar with MSP-specific tools like RMM or PSA platforms.
-
Boutique Specialist Firms: These smaller firms often have deep expertise in technology and cloud services. They tend to be more cost-effective, agile, and are staffed by senior auditors who understand the MSP operational model. Their reports are often clearer and more practical, though their brand may carry less weight in highly traditional industries.
The optimal choice depends on your client base. If you serve large, traditional enterprises, the brand recognition of a “Big Four” auditor may justify the premium. For technology and mid-market clients, a boutique firm’s expertise and efficiency are often the better investment.
A Data-Driven Approach to Selecting an Auditor
Make your selection based on data, not sales pitches. Platforms like SOC2Auditors.org aggregate metrics on over 90 audit firms, allowing you to compare capabilities, accreditations, and even qualitative factors like report clarity. By filtering based on your industry, budget, and timeline, you can obtain a shortlist of matched firms. Data from such platforms shows timelines ranging from 3–20 months and costs from $15K–$400K+, enabling you to benchmark your project and avoid unforeseen costs and delays.
Decoding the Costs and Timelines
The wide cost range for a SOC 2 audit is driven by several predictable factors. Understanding them is key to accurate budgeting.
| Cost Driver | Why It Impacts Price | Example Cost Influence |
|---|---|---|
| Audit Scope | More Trust Services Criteria (like adding Availability and Confidentiality) and more in-scope systems mean more work. | A Security-only report might start at $15,000, while a report covering all five TSCs could easily top $75,000. |
| Report Type | A Type 2 report covers a 3-12 month period, which requires way more evidence review than a point-in-time Type 1. | A Type 2 audit usually costs 30-50% more than a Type 1 from the same firm because of the extended testing. |
| Company Size & Complexity | More employees, locations, and complex infrastructure (like multi-cloud setups) add to the audit effort. | A 20-person MSP with one office will pay a lot less than a 200-person MSP with multiple data centers. |
| Auditor Reputation | Big-name, national firms charge a premium for their brand recognition and perceived authority. | Going with a “Big Four” firm can easily double the cost compared to a highly reputable boutique for the exact same scope. |
This investment requires careful planning. An auditor who understands the MSP model can help you scope appropriately and focus on controls relevant to your client commitments, making the audit more efficient and the final report more effective. For additional guidance, see this resource on how to choose a SOC 2 auditor.
Your SOC 2 Report Is Done. Now What?
Obtaining your SOC 2 report is a milestone, not a destination. The report is valid for only 12 months, and the clock for your next audit’s observation period begins immediately. This matters for someone pursuing SOC 2 because maintaining compliance requires a shift from a one-time project to a continuous program.
Moving From a Project to a Program
The most common post-audit failure is treating SOC 2 as a project that is now complete. Compliance must become an integral part of your MSP’s operations. This requires assigning clear ownership for every control to ensure that tasks are performed, evidence is collected, and deficiencies are remediated on an ongoing basis.
- Quarterly Access Reviews: A designated service manager is responsible for running and documenting user access reviews for the RMM, PSA, and cloud consoles every 90 days to satisfy CC6.3.
- Monthly Vulnerability Scans: A senior engineer is accountable for executing scans, creating remediation tickets in the PSA, and tracking them to closure.
- Annual DR Testing: The service delivery manager is responsible for planning, executing, and documenting the annual disaster recovery test to meet the requirements of A1.2.
Bake Compliance Into Your Daily Workflow
Manual evidence collection is unsustainable for a busy MSP. The only scalable solution is to integrate evidence gathering directly into your existing tools and workflows. This is where compliance automation platforms provide significant value. These tools integrate with your tech stack to continuously monitor controls, assign tasks to owners, and automatically collect evidence, such as logs showing successful backups or MFA enforcement.
This automated approach is becoming standard. For instance, Vanta’s partners now offer managed SOC 2 services alongside other frameworks. This trend is part of a broader security focus, with increasing adoption of frameworks like ISO 27001. You can find more data on this evolving landscape on Eventus Security.
The objective is to make compliance an automated byproduct of your daily operations. When a technician documents a change in the PSA or HR onboards a new employee according to procedure, the evidence for your next SOC 2 audit should be generated automatically.
Turn That Report Into a Sales Weapon
Your SOC 2 report is a powerful sales and marketing asset. It provides objective, third-party validation of your security posture.
Use it proactively to:
- Streamline Due Diligence: Provide your sales team with a summary of your report to address security questions early in the sales cycle and reduce the friction of security questionnaires.
- Build a Security Trust Center: Create a public-facing webpage on your site that details your compliance posture, explains the scope of your SOC 2 report, and reinforces your commitment to security.
- Access Larger Markets: A SOC 2 Type 2 report is a prerequisite for entering regulated markets like finance, healthcare, and enterprise SaaS. Without it, you cannot compete for these valuable contracts.
By embedding controls into operations and leveraging your report as a strategic asset, you can effectively demonstrate your security commitment and operational maturity. This transforms the annual audit from a disruptive event into a simple validation of your established processes, which is the true essence of being audit-ready.
Finding the right SOC 2 auditor is a critical first step in your compliance journey. At SOC2Auditors, we replace sales pitches with verified data, matching you with the ideal CPA firm for your budget, timeline, and industry. Get your tailored auditor shortlist at https://soc2auditors.org.