Cybersecurity audit companies are third-party, licensed Certified Public Accountant (CPA) firms that systematically evaluate an organization’s information systems against the AICPA’s established Trust Services Criteria (TSC) to produce a SOC 2 attestation report. Their primary function is to provide an objective, independent assessment of the design and operating effectiveness of security controls, identify gaps, and deliver a formal opinion that provides assurance to customers and stakeholders.
The Role of Cybersecurity Audit Companies in SOC 2

For an organization pursuing SOC 2, a cybersecurity audit company acts as the independent examiner, not a consultant. Their role is strictly defined by AICPA attestation standards: to test the controls you have designed and implemented, and then issue a formal opinion on whether they meet the specified Trust Services Criteria. This independence is mandatory for the final SOC 2 report to be valid and credible.
The auditor’s primary function is to provide an attestation—a formal, expert opinion on whether your organization’s controls meet the specific requirements of the chosen TSC. This process is covered in detail in this practical guide to computer security audits. For the final SOC 2 report to be credible, this independence must be absolute.
Core Evaluation Benchmarks: The TSC
The entire foundation of any SOC 2 audit is the AICPA’s Trust Services Criteria. Auditors use these five criteria as their benchmark to evaluate your controls. While you can choose which to include, Security is the one mandatory criterion for every single SOC 2 engagement.
- Security (Common Criteria): This is the baseline. It covers all the controls designed to protect information and systems from unauthorized access, disclosure, and system damage. A good example is CC6.1, which requires you to have procedures to manage risks from vendors and business partners. For SOC 2, this means an auditor will demand evidence of your vendor risk management program, including contracts with security requirements and periodic reviews.
- Availability: Focuses on whether your systems are available for operation and use as you’ve promised your customers. For SOC 2, an auditor will test controls related to performance monitoring, disaster recovery, and incident handling to validate these commitments.
- Processing Integrity: Addresses if your system’s processing is complete, valid, accurate, timely, and authorized. To satisfy an auditor, you must demonstrate controls over data input, processing, and output to ensure integrity.
- Confidentiality: Pertains to the controls you have in place to protect any information you’ve designated as “confidential.” An auditor will verify that you have robust access controls and encryption policies for this specific data set.
- Privacy: Concerns how you handle personal information—its collection, use, retention, disclosure, and disposal, as outlined in your privacy notice. Auditors will test your controls against the commitments made in that notice.
The table below shows the difference in focus between the mandatory Security criterion and one of the optional criteria, Availability, to give you a feel for how auditors apply these benchmarks.
| Trust Service Criterion | Primary Focus for Auditors | Sample AICPA Requirement (CC) |
|---|---|---|
| Security (Mandatory) | Protecting information and systems from unauthorized access and damage. | CC4.1 – The entity selects, develops, and deploys logical access security software, infrastructure, and architectures. |
| Availability (Optional) | Ensuring systems are operational and accessible as promised. | A1.2 – The entity authorizes, designs, develops, and implements recovery plans to meet its objectives. |
Why this matters for SOC 2: The auditor’s interpretation of these TSCs is what determines your audit’s outcome. Their testing procedures for a criterion like CC7.1 (Risk Assessment) will directly dictate the evidence you need to provide, such as documented risk analyses and mitigation plans. Choosing a firm with deep expertise in the TSCs relevant to your business is critical for ensuring your controls are evaluated correctly and for achieving a clean attestation report.
The New Reality of Cybersecurity Audits
Cybersecurity audits are no longer an isolated IT function; they are a board-level concern integral to business operations, driven by regulatory pressure and customer demands. For organizations pursuing SOC 2, understanding this shift is crucial, as it dictates the urgency, scope, and strategic importance of the audit itself.
This isn’t just a trend; it’s a massive market shift. The global cybersecurity audit market is expected to surge from $4.8 billion in 2024 to a staggering $12.3 billion by 2033. Why the explosion? Relentless cyberattacks, like the ransomware that hit over 66% of organizations in 2023, and tough new regulations like the SEC’s four-day breach disclosure rule are forcing everyone’s hand. You can dig into the market trend data to see just how fast this is moving.
What’s Driving the Change?
Several key pressures are reshaping what companies demand from cybersecurity audit firms. Understanding these forces is essential for successfully navigating a SOC 2 audit.
- Tougher Regulations: New laws like the EU’s Digital Operational Resilience Act (DORA) and the NIS 2 Directive are making audits a non-negotiable legal requirement. For SOC 2, this means your control environment must be robust enough to meet both customer expectations and emerging legal standards.
- The Enterprise “No SOC 2, No Deal” Rule: For B2B and SaaS companies, a clean SOC 2 report is now a prerequisite for closing enterprise deals. The lack of a valid attestation is a major sales blocker, making the audit a direct driver of revenue.
- Smarter Threats, Demanding Stakeholders: Attackers are more sophisticated than ever. Your board, investors, and customers want independent proof that your controls, such as those required by CC5.1 (Incident Management), are effective against modern threats, not just compliant on paper.
Why this matters for SOC 2: These forces transform a SOC 2 audit from a discretionary project into a time-sensitive, high-stakes business initiative. The pressure from enterprise sales often dictates your audit timeline, making your choice of an efficient and experienced audit firm a critical decision that impacts your ability to compete and grow.
Audits Aren’t a Yearly Scramble Anymore
The audit industry is adapting to meet the demand for continuous assurance. The traditional, point-in-time audit is being replaced by a more integrated, technology-driven approach where auditors use platforms to monitor controls throughout the observation period.
Why this matters for SOC 2: This shift is highly beneficial for teams preparing for an audit. Instead of a frantic, multi-month evidence-gathering sprint, continuous monitoring allows you to validate controls year-round. For example, a compliance automation platform can continuously check that your cloud configurations adhere to policies relevant to CC6.1 (Control Monitoring), flagging deviations in real time. This streamlines evidence collection, reduces the audit-prep workload, and turns compliance into a sustainable operational process—the new expectation for SOC 2 readiness.
Comparing Big Four vs Boutique Specialist Audit Firms
When selecting a cybersecurity audit company for a SOC 2 engagement, the choice generally falls between two models: large, multi-service ‘Big Four’ firms and focused, specialist boutiques. This decision is critical, as it directly impacts the audit’s cost, timeline, and the level of expertise applied to your specific technology and business model.
For a company pursuing SOC 2, the operational differences between these two models are huge. Their approach to project management, communication, and technical depth can vary wildly. Understanding this distinction is the key to avoiding a painful, drawn-out audit.

Big Four Firms: The Power of Scale and Brand
The Big Four—Deloitte, PwC, KPMG, and EY—are massive professional services networks. Their primary advantage is unparalleled brand recognition, which can be valuable for large, publicly-traded companies or those preparing for an IPO. They offer a “one-stop shop” for global enterprises needing audits across multiple frameworks (e.g., SOX, GDPR, ISO 27001).
Their market dominance is staggering. Deloitte alone commands 16.6% of the $77 billion global security services market, raking in over $12.7 billion a year thanks to its army of 40,000+ security professionals. This scale allows them to tackle massive, complex audits across different frameworks. You can read more about it in the official 2026 cybersecurity market report.
However, their scale can be a disadvantage for smaller companies. The audit may be conducted by junior staff with oversight from senior managers, leading to a less personal and more bureaucratic experience.
Why this matters for SOC 2: If your primary objective is to satisfy the procurement requirements of a Fortune 500 company that values brand prestige, the logo of a Big Four firm on your SOC 2 report carries significant weight. However, their auditors may lack specific expertise in modern, cloud-native environments, potentially leading to misinterpretations of controls related to criteria like CC6.6 (Cloud and Virtualization Controls).
Boutique Specialist Firms: The Advantage of Focus and Agility
Boutique firms specialize exclusively in information security and compliance frameworks like SOC 2, ISO 27001, and HITRUST. Their strength lies in deep, focused expertise. The auditors you engage have often conducted hundreds of SOC 2 audits for companies with similar business models and tech stacks. You can see more examples in our guide on SOC service providers.
These firms are more agile and typically offer a higher-touch service model. For a startup or mid-market company undergoing its first SOC 2, direct access to senior auditors is invaluable. They can provide practical context on applying the Trust Services Criteria to specific technologies, such as a serverless architecture or a containerized environment.
- Deeper Niche Expertise: Many boutiques focus on specific industries like FinTech or HealthTech, so they already understand your unique risks and regulatory landscape.
- Consistent Engagement Team: You’ll likely work with the same senior auditors from start to finish—no getting passed off to a new junior associate every few months.
- Cost-Effective Structure: With far less overhead than the Big Four, their pricing for a standard SOC 2 audit is almost always more competitive.
Why this matters for SOC 2: A boutique firm’s specialized knowledge is a significant advantage. They understand how to efficiently test controls in cloud environments (AWS, GCP, Azure), which is crucial for satisfying criteria like CC6.8 (Change Management) in a CI/CD pipeline. Their responsiveness and practical guidance are critical for navigating the evidence collection process without delays.
Comparing Big Four and Boutique Specialist Firms for SOC 2 Audits
| Evaluation Criterion | Big Four Firms (e.g., Deloitte, KPMG) | Boutique Specialist Firms (e.g., Coalfire, A-LIGN) |
|---|---|---|
| Best For | Publicly-traded, global enterprises; IPO-bound companies; complex, multi-framework audits. | Startups (Seed-Series C), SaaS companies, and mid-market firms needing their first SOC 2. |
| Price | Very high ($60k - $400k+). Typically 2-4x more expensive than specialists. | Competitive ($20k - $75k). Often offer fixed-fee pricing to avoid surprise costs. |
| Timelines | Slow. 12-20 months is common due to bureaucracy and longer review cycles. | Fast. Can often complete a Type 2 audit in 6-10 months due to agile processes. |
| Service Model | Formal and process-heavy. Day-to-day contact is often with junior staff. | High-touch and collaborative. Direct access to senior partners and experienced auditors. |
| Expertise | Broad business expertise but may lack deep, modern tech-stack knowledge. | Deep specialization in SOC 2 and cloud-native environments (AWS, GCP, Azure). |
Why this matters for SOC 2: For most tech companies, a boutique firm provides the right blend of expertise, agility, and cost-effectiveness needed for a successful SOC 2 audit. A Big Four firm is often overkill unless required by specific enterprise clients or complex corporate structures. Choosing the right type of firm is the first step to ensuring your audit is efficient and its outcome is credible.
How to Evaluate Your SOC 2 Auditor
Selecting the right SOC 2 auditor is a critical project management decision that directly determines the cost, timeline, and success of your attestation. A thorough evaluation process is not just about comparing prices; it’s about finding a partner with the technical expertise and procedural rigor to validate your controls against the AICPA Trust Services Criteria effectively.
You’re not just buying a report. You’re selecting a partner for a complex technical and procedural assessment. A thorough evaluation process prevents scope creep, budget overruns, and painful audit failures. This is your framework for finding an auditor who actually understands your business and tech stack.
Key Evaluation Criteria for Auditor Selection
When engaging with potential audit firms, focus on factors that directly correlate with a successful SOC 2 outcome. Your goal is to assess their competence, methodology, and ability to support your team through the complexities of the audit.
-
Deep Industry Expertise: Does the firm have proven experience auditing companies exactly like yours (e.g., B2B SaaS, FinTech, HealthTech)? An auditor familiar with your business model will understand how to apply the TSCs to your specific context, preventing misinterpretations. For instance, testing CC8.1 (Change Management) for a SaaS company with a CI/CD pipeline requires different expertise than for a company with traditional software release cycles.
-
Relevant Firm and Individual Certifications: The firm must be a licensed CPA firm and a member of the AICPA. Beyond that, look for individual auditor certifications like Certified Information Systems Auditor (CISA) and Certified Information Systems Security Professional (CISSP), which demonstrate a high level of technical proficiency required to test complex IT controls.
-
Clear Audit Methodology: A quality firm will provide a transparent, step-by-step audit plan. Ask them to demonstrate their audit platform. A modern portal that streamlines evidence collection and communication is far superior to managing hundreds of emails and spreadsheets, reducing the administrative burden on your team.
Why this matters for SOC 2: Choosing an auditor without specific experience in your industry is a common and costly mistake. An auditor unfamiliar with cloud-native technologies might struggle to test controls for CC6.6 (Logical Access) within an AWS environment, leading to requests for irrelevant evidence and potential findings that could have been avoided with a more knowledgeable partner.
Assessing Scope, Timelines, and Cost
An accurate quote and realistic timeline are only possible after a clear definition of the audit scope. Use a comprehensive SOC 2 compliance checklist to prepare for scoping discussions with potential auditors.
Be prepared to specify which Trust Services Criteria are in scope and provide a clear overview of your systems and business processes. This information is essential for firms to create a precise proposal. The 2026 landscape of top cybersecurity audit companies, from giants like Deloitte to tech-focused specialists, shows a massive variance in how projects are run. Timelines can stretch from 3 to 20 months and costs can range from $15,000 to over $400,000.
In fact, an estimated 70% of startups overpay for their audits simply because they fail to compare the right types of firms. For a deeper dive, you can explore the latest analysis of top audit firms.
Use the table below as a benchmark to gauge the proposals you receive.
| Audit Scope | Typical Timeline (Type 2) | Estimated Cost Range | Best For |
|---|---|---|---|
| Security Only | 6-9 Months | $20,000 - $45,000 | Early-stage startups needing a baseline report for initial customer requests. |
| Security + 1-2 TSCs | 8-12 Months | $30,000 - $75,000 | Growth-stage companies handling sensitive data (e.g., Confidentiality). |
| All 5 TSCs | 10-14 Months | $50,000 - $120,000+ | Mature organizations with complex systems and enterprise-level requirements. |
Evaluating Support and Responsiveness
The quality of an auditor’s support during the evidence collection phase is critical. Your team will inevitably have questions interpreting AICPA criteria, such as the requirements for documenting system components under CC3.2.
A responsive auditor provides clear, timely answers, preventing your team from being blocked. During initial calls, ask specific questions: “Who is my primary point of contact?” and “What is your firm’s SLA for responding to questions during fieldwork?”
Why this matters for SOC 2: This evaluation directly impacts your audit readiness. An auditor with proven industry experience ensures your controls are correctly interpreted and tested against the TSCs. Transparent pricing and realistic timelines allow for proper budgeting and project planning. Responsive support prevents delays and keeps your audit on track. A thorough vetting process de-risks the entire engagement and is a foundational step toward a successful attestation.
Creating A Decision Matrix To Finalize Your Choice
After narrowing your list to two or three cybersecurity audit firms, use a decision matrix to make an objective, data-driven selection. This tool formalizes the evaluation process by forcing you to quantify your priorities and score each firm against them.
Why this matters for SOC 2: A decision matrix is more than just a project management tool; it’s a piece of evidence demonstrating due diligence. For your SOC 2 audit, this document can be included in your evidence package to show that you followed a structured process for vendor selection, satisfying requirements like CC9.2 (Vendor Management). It provides a defensible rationale to leadership and stakeholders for your choice.
The process involves identifying your key criteria, assigning a weight to each based on its importance, and then scoring each finalist. For example, a company with urgent customer deadlines might weight ‘Timeline to Report’ twice as heavily as ‘Total Cost’.
Building Your Weighted Scoring Matrix
First, define your evaluation criteria with specific, measurable metrics. “Good support” is vague; “24-hour response time SLA during fieldwork” is a concrete metric you can score.
Your criteria should reflect the practical factors that will determine the audit’s success.
- SOC 2 Experience with Relevant TSCs: How many SOC 2 audits have they performed for B2B SaaS companies using the Availability and Confidentiality criteria? Don’t just ask if they’ve done SOC 2; ask if they’ve done an audit for a company like yours.
- Audit Methodology and Platform: Do they use a modern portal for evidence collection, or will your team be managing a complex spreadsheet? An efficient platform significantly reduces the administrative burden and potential for error.
- Timeline and Speed to Report: Obtain a firm delivery date for the final report. This is critical if your sales team is facing deadlines from prospects.
- Post-Audit Support: Clarify their process for supporting you after the report is issued. Will they help you address customer questions about the report, or does their engagement end upon delivery?
Next, assign a weight to each criterion (e.g., from 1 to 5, with 5 being mission-critical). A startup might weight ‘Total Cost’ as a 3 but ‘SaaS Industry Experience’ as a 5. Then, score each firm (e.g., from 1 to 10) on how well they meet each criterion.
Why this matters for SOC 2: The matrix forces internal alignment on what truly matters. It crystallizes whether speed is more important than cost, or if deep technical expertise outweighs a well-known brand. This alignment is crucial before committing to a significant contract, ensuring the chosen partner meets your strategic SOC 2 objectives.
Finally, multiply the score by the weight for each criterion to get a weighted score. The firm with the highest total score is the quantitative winner. To see how these factors play out across different kinds of firms, check out our comparison of different types of IT audit companies.
This flowchart shows the kind of high-level filtering that happens before you even get to the matrix.
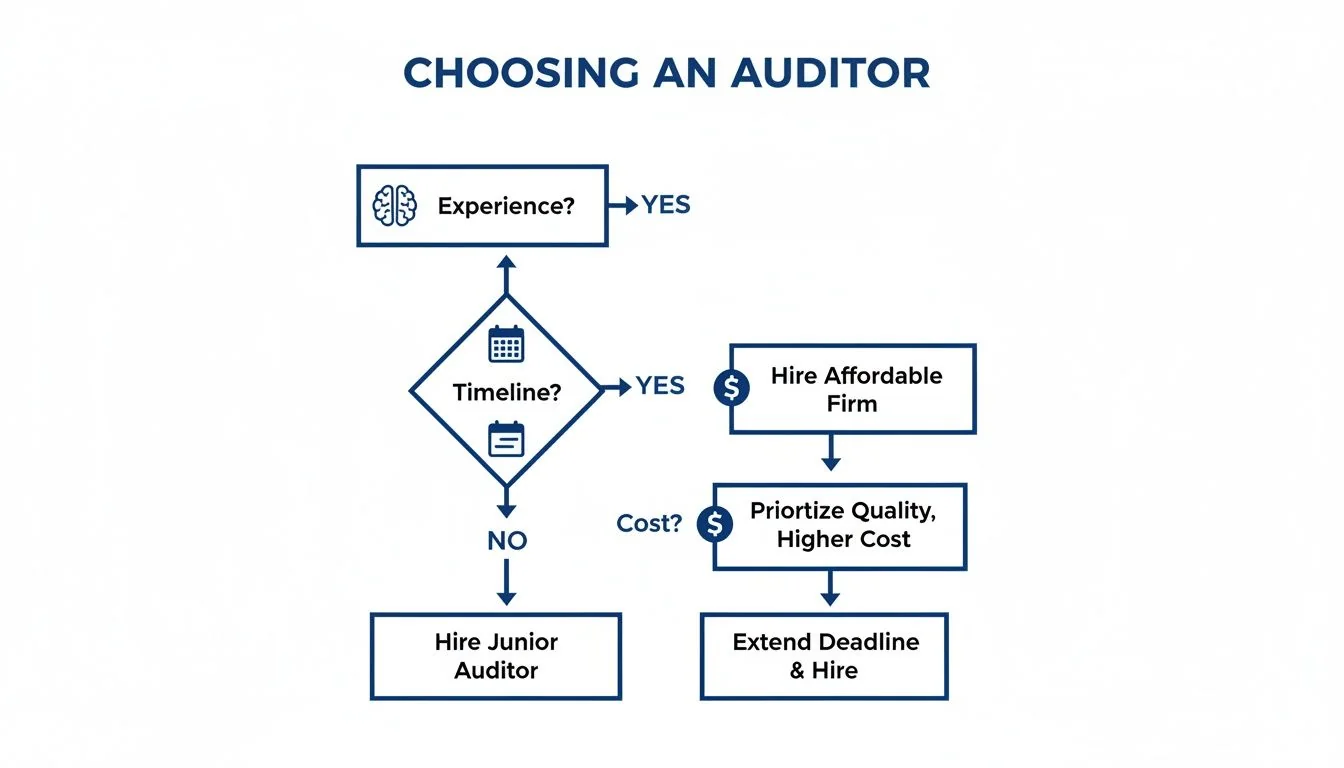
These initial filters—experience, timeline, and cost—are exactly what you’ll break down and score in your matrix for a much more granular comparison.
Sample Auditor Selection Decision Matrix for SOC 2
Here’s a sample matrix for a SaaS company choosing a SOC 2 auditor. Notice how the weights reflect their priorities: experience and speed are everything.
| Criterion | Weight (1-5) | Firm A Score (1-10) | Firm A Weighted Score | Firm B Score (1-10) | Firm B Weighted Score |
|---|---|---|---|---|---|
| SOC 2 & SaaS Industry Experience | 5 | 9 | 45 | 7 | 35 |
| Speed to Report Delivery | 5 | 8 | 40 | 6 | 30 |
| Quality of Audit Platform | 4 | 9 | 36 | 8 | 32 |
| Auditor Responsiveness & Support | 4 | 7 | 28 | 9 | 36 |
| Total Cost | 3 | 6 | 18 | 9 | 27 |
| Total Score | 167 | 160 |
Why this matters for SOC 2: The matrix provides a clear, defensible conclusion. While Firm B is cheaper and more responsive, Firm A is the superior choice because it excels in the two most critical areas for this company: SaaS experience and speed to report. This methodical approach ensures you select a partner strategically aligned with your SOC 2 goals, not just the one with the lowest bid.
Why Your Auditor Choice Is Critical for SOC 2 Success
Choosing a cybersecurity audit company is the most impactful decision in a SOC 2 engagement. This choice dictates how the AICPA’s Trust Services Criteria are interpreted and tested against your specific technology and business processes. The right firm acts as a knowledgeable partner, while the wrong one can lead to scope creep, budget overruns, and a failed attestation that jeopardizes key business relationships.
The Direct Link Between Auditor and Audit Outcome
A qualified audit firm provides crucial context. For a SaaS company, this means an auditor who understands cloud-native architecture can provide practical guidance on how to satisfy criteria like CC4.1 (Logical and Physical Access Controls) within an AWS or Azure environment, rather than applying outdated on-premise standards. Their experience helps you design controls that are not only compliant but also efficiently testable.
An inexperienced auditor, conversely, may misinterpret a valid control, resulting in an unnecessary finding or a qualified opinion on your report—a major red flag for prospective customers.
Why this matters for SOC 2: The difference between a smooth audit and a painful one often comes down to the auditor’s ability to provide clear, actionable feedback during testing. While they cannot consult, their expert guidance on how to meet a control objective is invaluable. This is especially true for complex criteria like CC7.2 (Risk Identification and Analysis), where an experienced auditor can help you understand the level of detail required in your risk assessment documentation.
De-Risking Your Path to a Clean Report
A structured, data-driven selection process is the most effective way to de-risk your SOC 2 audit from the outset. It forces you to define and prioritize your objectives—is speed the top priority to meet sales demands? Is cost the primary constraint? Or is the brand recognition of a global firm a must-have?
Using a formal evaluation, such as the decision matrix previously discussed, ensures your chosen partner is aligned with your strategic goals. For more details on the importance of formal certification, you can review this guide on the role of compliance in cybersecurity.
A well-chosen partner from the hundreds of cybersecurity audit companies available is fundamental to SOC 2 audit readiness. An experienced auditor who understands your business will ensure a smooth process, resulting in a high-quality SOC 2 report that acts as a sales accelerator. This decision directly prepares your team for a successful audit by aligning the testing process with your operational reality, ultimately making your journey to SOC 2 compliance more efficient and effective.
Ready to find the right SOC 2 auditor without the guesswork? SOC2Auditors.org provides verified data on 100+ audit firms, letting you compare real pricing, timelines, and satisfaction scores. Get three tailored matches in 24 hours and make a data-driven choice with confidence by visiting https://soc2auditors.org.