A SOC 2 compliance framework comparison chart is a document that maps the control requirements of the SOC 2 Trust Services Criteria against other information security and privacy frameworks, such as ISO 27001, HIPAA, and PCI DSS. Its purpose is to identify overlapping controls, highlight unique requirements (gaps), and provide a strategic basis for planning integrated audits, thereby reducing redundant effort and cost for organizations pursuing multiple attestations or certifications. This analysis is foundational for creating an efficient, unified compliance program that meets diverse market and regulatory demands.
Defining The SOC 2 Attestation Framework for Audit Readiness
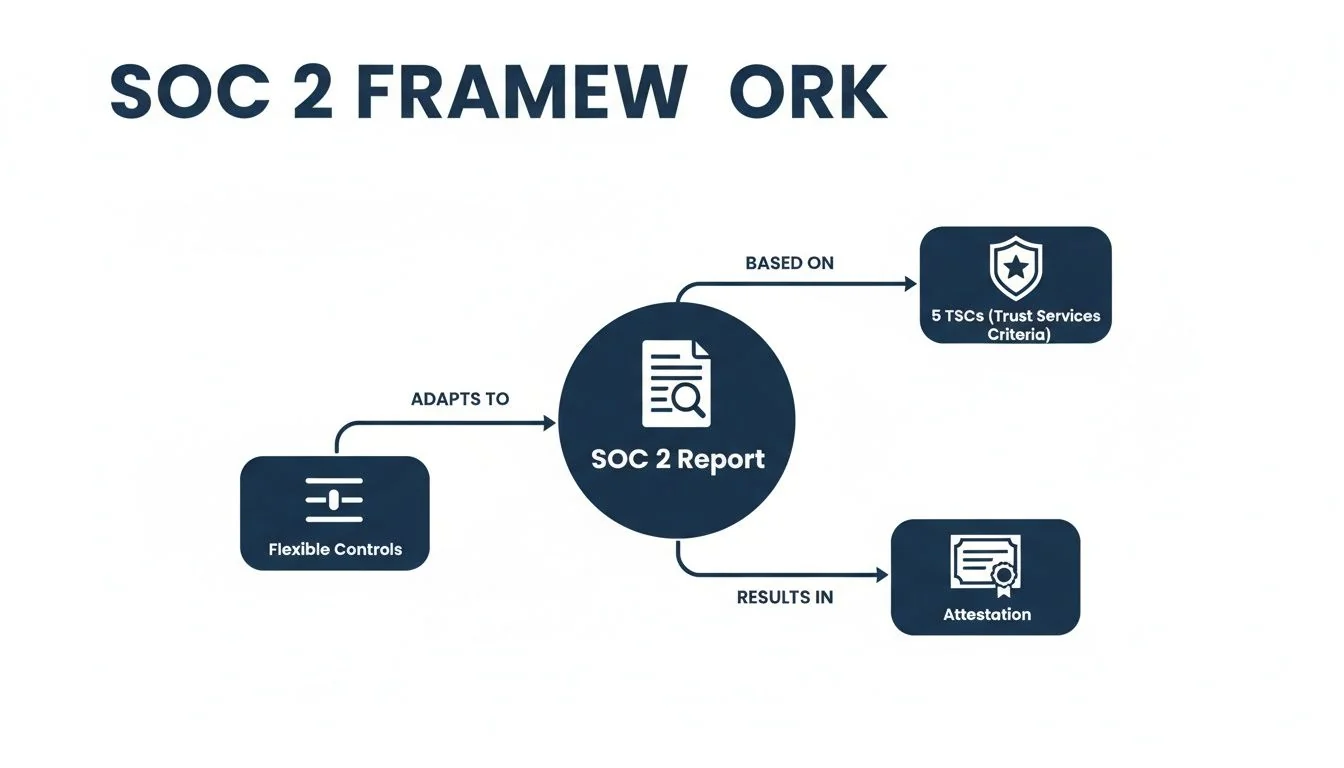
SOC 2 is not a certification; it is an attestation framework developed by the American Institute of Certified Public Accountants (AICPA) for service organizations. The outcome of a SOC 2 engagement is not a certificate but a formal report issued by an independent CPA firm. This report contains the auditor’s opinion on the design (Type 1) or the design and operating effectiveness (Type 2) of an organization’s internal controls relative to the selected Trust Services Criteria. This matters for someone pursuing SOC 2 because it fundamentally shifts the audit conversation from a prescriptive checklist to a principles-based discussion, requiring you to design, implement, and defend controls that are uniquely suited to your business, technology stack, and contractual commitments to customers.
The Five Trust Services Criteria
The entire SOC 2 audit is built on the five Trust Services Criteria (TSCs). The Security criterion is mandatory for every SOC 2 report and its controls are often called the “Common Criteria” because they form the baseline for information and systems security. Understanding these criteria is critical for SOC 2 readiness because it allows you to scope your audit accurately, focusing only on the TSCs relevant to the services you provide and the promises you have made to customers.
- Security: This is the non-negotiable foundation. It requires controls to protect information and systems from unauthorized access, disclosure, and damage that could compromise the availability, integrity, confidentiality, and privacy of data. For SOC 2 readiness, this means implementing controls for logical and physical access, system operations, and change management, such as those outlined in Common Criterion 3.2 (CC3.2), which mandates the organization “designs and implements controls to mitigate security risks.”
- Availability: This criterion addresses whether systems are available for operation and use as committed or agreed. This matters for SOC 2 if your service level agreements (SLAs) promise specific uptime percentages. Your controls must demonstrate system monitoring, disaster recovery, and business continuity readiness, directly addressing criterion A1.2, which requires the organization to have recovery plans to meet its objectives.
- Processing Integrity: This criterion is for services performing transactions or critical computations. It ensures system processing is complete, valid, accurate, timely, and authorized. If your platform processes financial transactions, for example, your SOC 2 audit will require you to prove the controls that ensure data inputs are accurate and outputs are correct, as per criterion PI1.1.
- Confidentiality: This criterion concerns the protection of information designated as confidential by agreement or policy. It is essential for SOC 2 readiness if you handle sensitive customer data. Controls must be in place to identify and protect confidential information throughout its lifecycle, from creation to destruction, aligning with criterion C1.2, which requires controls over data disposal.
- Privacy: Distinct from Confidentiality, this addresses how you collect, use, retain, disclose, and dispose of personal information (PI). It is critical for B2C companies or any organization handling PII, as it requires controls that align with the organization’s privacy notice and the AICPA’s Generally Accepted Privacy Principles (GAPP), such as P1.1, which mandates providing notice of privacy practices.
For anyone going through SOC 2, the difference between criteria and controls is everything. You are not buying a checklist. You are designing a security program that logically and defensibly meets the AICPA’s criteria.
SOC 2 Report Types Explained
The final output of your audit is the report, which comes in two distinct types. Choosing the correct report type is a crucial step in SOC 2 readiness, as it determines the level of assurance you provide to customers and the internal resources required for the audit. A Type 2 report is the market standard and demonstrates a mature, operational security program.
| Report Type | Description | Key Characteristic | Why It Matters for SOC 2 |
|---|---|---|---|
| Type 1 | An audit of the design of your controls at a single point in time. | Assesses if your controls are suitably designed. | Fulfills an urgent customer request or demonstrates initial compliance progress, but offers limited assurance. |
| Type 2 | An audit of the design and operating effectiveness of your controls over a period, typically 3-12 months. | Proves your controls work consistently over time. | The gold standard for enterprise customers. It provides a high level of assurance and is necessary for building long-term trust. |
This distinction isn’t a small detail; it’s fundamental. A Type 2 report provides a much higher level of assurance and is what the market, especially B2B SaaS buyers, expects to see. Your framework comparison is only valuable once you understand that SOC 2’s flexibility and the Type 2 requirement demand a sustained, evidence-based approach to security that goes far beyond a point-in-time check.
The SOC 2 Compliance Framework Comparison Chart
Approaching compliance frameworks like SOC 2, ISO 27001, and HIPAA in isolation is a common but costly mistake. A SOC 2 compliance framework comparison chart is a strategic tool that maps control requirements across these standards to identify overlaps. For a company pursuing SOC 2, this matters because it provides a clear path to efficiency. By leveraging existing controls and evidence from other compliance efforts (e.g., HIPAA), you can significantly reduce the preparation time, internal workload, and overall cost of your SOC 2 audit. This transforms compliance from a series of disconnected tasks into an integrated, strategic program.
SOC 2 is not a one-size-fits-all certification. It’s a custom report built around five Trust Services Criteria, a core concept you have to grasp before comparing it to anything else.
Core Differentiators Across Frameworks
When comparing SOC 2 with frameworks like ISO 27001, HIPAA, and PCI DSS, you are evaluating different philosophies for demonstrating security. For an organization pursuing SOC 2, understanding these differences is crucial for communicating with auditors and stakeholders and for leveraging prior compliance work effectively.
-
Control Style: SOC 2 is criteria-based, offering the flexibility to design controls that fit your specific business environment. This is important for SOC 2 candidates because it allows for innovation and efficiency. In contrast, PCI DSS is highly prescriptive, mandating specific controls, such as detailed firewall configuration rules.
-
Audit Outcome: A SOC 2 audit results in an attestation report from a CPA firm, which includes the auditor’s detailed opinion. An ISO 27001 audit yields a certification, which is a pass/fail outcome. This matters for SOC 2 because the detailed nature of the report provides more transparency to customers than a simple certificate.
-
Geographic Focus: SOC 2 is the predominant standard for service organizations in the United States, driven by the AICPA. ISO 27001 is the leading information security standard globally, recognized extensively in the EU and APAC. This is a critical consideration for SOC 2 planning, as companies with international ambitions may need to prepare for an integrated audit approach.
The most important takeaway from a comparison chart is understanding the control philosophy. With SOC 2, you tell the auditor, “Here is how we meet the criteria.” With prescriptive frameworks, the auditor tells you, “Here is the checklist you must follow.”
This distinction has a massive impact on your audit readiness. If you already have a mature Information Security Management System (ISMS) for ISO 27001, a significant portion of your existing processes and documentation can be directly mapped to the SOC 2 Common Criteria, saving hundreds of hours of preparation.
SOC 2 vs Other Frameworks A Detailed Comparison
This table is not just an informational list; it is a decision-making tool. For a company preparing for a SOC 2 audit, this comparison helps justify the investment, scope the project correctly, and plan for future compliance needs by showing how different frameworks serve distinct business objectives.
| Attribute | SOC 2 | ISO 27001 | HIPAA | PCI DSS |
|---|---|---|---|---|
| Primary Goal | Attest to controls over customer data based on Trust Services Criteria. | Certify an organization’s Information Security Management System (ISMS). | Mandate protection of Protected Health Information (PHI) for covered entities. | Secure cardholder data environments and prevent credit card fraud. |
| Control Style | Criteria-based; flexible design. | Framework-based; prescriptive Annex A controls are a starting point. | Rule-based; requires specific administrative, physical, and technical safeguards. | Highly prescriptive; detailed and mandatory technical requirements. |
| Output | Restricted-use attestation report (Type 1 or 2). | Publicly verifiable certification. | No official certification; compliance is demonstrated via risk analysis and audits. | Attestation of Compliance (AOC) and Report on Compliance (ROC). |
| Governing Body | AICPA (American Institute of CPAs). | ISO (International Organization for Standardization). | U.S. Department of Health & Human Services (HHS). | PCI Security Standards Council (PCI SSC). |
| Best For | B2B SaaS, cloud providers, and service organizations serving the US market. | Global enterprises or companies expanding into international markets (especially EU/APAC). | Healthcare organizations and their business associates handling PHI in the US. | Any entity that stores, processes, or transmits cardholder data. |
For an organization pursuing SOC 2, identifying these overlaps is the key to efficiency. For example, the technical safeguards required by the HIPAA Security Rule, such as access controls (§164.312(a)) and audit controls (§164.312(b)), directly map to the SOC 2 Security criterion (Common Criteria). Presenting this existing evidence to your SOC 2 auditor demonstrates control maturity from day one and streamlines the audit process, turning a compliance requirement into a strategic advantage.
SOC 2 vs. ISO 27001: It’s a Strategic Market Decision
A SOC 2 report is an attestation from a CPA firm, governed by the AICPA, and is the standard for service organizations in the U.S. to demonstrate robust internal controls. In contrast, ISO 27001 is the global benchmark for implementing and certifying a comprehensive Information Security Management System (ISMS). For an organization preparing for SOC 2, deciding if and when to pursue ISO 27001 is a critical strategic decision that directly impacts sales opportunities and market access. While SOC 2 is often the price of entry for U.S. enterprise deals, ISO 27001 is frequently the requirement for expansion into Europe and Asia.
The market momentum is shifting. While SOC 2 remains dominant in the U.S., global demand for ISO 27001 is growing rapidly. A 2025 survey revealed that organizations now rank ISO 27001 as more important to their business than SOC 2, reflecting a broader push for a globally recognized security posture. This matters for your SOC 2 audit readiness because it forces you to consider a longer-term compliance roadmap. A SOC 2-only strategy may limit your future growth.
Mapping Controls for Real-World Efficiency
This is where a comparison chart becomes an actionable tool for a company pursuing SOC 2. While the frameworks have different approaches, many of the underlying security controls are functionally identical. This mapping exercise is a critical step in preparing for an efficient SOC 2 audit.
Let’s take a concrete example: logical access control.
- SOC 2’s CC6.1: This Common Criterion requires an organization to “implement logical access security software, infrastructure, and architectures” to prevent unauthorized access. For your SOC 2 audit, you must provide evidence that only authorized individuals can access systems and data.
- ISO 27001’s Annex A.5.15: This control requires that “rules to control physical and logical access…shall be established and implemented based on business and information security requirements.”
The core principle is identical: restrict access to authorized users based on their job roles. If you’ve already built robust role-based access controls (RBAC) to satisfy ISO 27001’s Annex A, you’ve simultaneously done the hard work for SOC 2’s CC6.1. Your auditor won’t ask you to reinvent the wheel.
This control mapping is more than a technical task; it’s a strategic advantage for your SOC 2 engagement. By documenting these overlaps, you provide your auditor with a unified set of evidence, which enables a combined or “bridged” audit. This can dramatically reduce the cost, time, and internal resources needed to achieve both a SOC 2 report and an ISO 27001 certification. For any business with global ambitions, understanding the nuances of ISO 27001 certification is a vital first step in this strategic planning.
Automating Your Multi-Framework Compliance Game
A SOC 2 compliance framework comparison chart provides the blueprint, but compliance automation platforms provide the engine for execution. For a company pursuing SOC 2, the challenge is not just identifying control overlaps with frameworks like ISO 27001 but managing the evidence collection for them without duplicating effort. This is why automation tools like Drata, Vanta, and Secureframe are essential for an efficient audit. They integrate with your tech stack—cloud providers, code repositories, HR systems—to continuously monitor controls and collect evidence automatically. This matters because a single piece of automated evidence can be used to satisfy requirements across multiple frameworks simultaneously.

The Power of Continuous Monitoring
The most significant benefit of these platforms for SOC 2 readiness is continuous control monitoring. This eliminates the traditional pre-audit scramble for screenshots and log files by automating evidence gathering 24/7.
A perfect real-world example is employee offboarding, a critical control in any security program.
- For SOC 2, this directly maps to CC6.1, which focuses on timely removal of access for terminated users.
- For ISO 27001, the same action satisfies control A.7.1.2, which covers termination and changes of employment responsibilities.
An automation platform connects to your HR system (e.g., Gusto) and identity provider (e.g., Okta). When an employee is terminated, the platform automatically collects evidence that their access to all key systems was revoked within the policy-defined timeframe. This single, automated workflow generates the evidence needed for both your SOC 2 and ISO 27001 auditors.
This approach flips compliance from a stressful, cyclical fire drill into a state of continuous readiness. You’re not just preparing for an audit; you’re operating a verifiably secure business every single day.
Making Multi-Framework Compliance Achievable
The projected growth of the compliance automation market from $1.5 billion in 2023 to $3.8 billion by 2028 shows that this technology is now a mainstream operational necessity. For a company preparing for SOC 2, investing in automation makes it feasible to pursue both a SOC 2 report and an ISO 27001 certification without hiring a large governance, risk, and compliance (GRC) team. It allows a small security team to manage a sophisticated, multi-framework compliance program. Using tools like AI legal software can also help manage policy updates and legal reviews across different frameworks more efficiently. This has direct implications for your auditor selection. Asking potential audit firms about their experience with these platforms is a crucial due diligence step. An auditor proficient with your chosen tool can work more efficiently, leading to a smoother, faster, and more cost-effective audit. Understanding the role of SOC 2 automation tools makes you a more informed buyer of audit services.
Navigating The Expanding Scope Of SOC 2 Audits
The scope and complexity of SOC 2 audits are increasing, driven by heightened customer expectations, emerging regulations, and evolving cyber threats. For a company pursuing SOC 2, this means a “basic” Security-only report is often no longer sufficient. You must plan for a more comprehensive audit from the outset, as this is what the market now demands. Understanding this trend is critical for accurately budgeting, scoping, and scheduling your SOC 2 engagement to avoid unexpected costs and delays.
The Shift Beyond A Security-Only Report
A decade ago, a SOC 2 report covering only the Security TSC might have been sufficient. Today, it is merely the starting point. Enterprise customers now expect assurance beyond foundational security, demanding proof of service availability and data confidentiality. The data shows that the average number of controls in a SOC 2 report is rising, with the Availability TSC now included in 75.3% of all reports issued in 2024.
This expanding scope requires a holistic view of the data lifecycle. For SOC 2 readiness, this means your controls must address not just firewalls and access management, but also data handling from creation to final disposition. This includes having defensible processes for data destruction, such as using services for secure hard drive shredding for compliance to ensure sensitive business and customer data is irretrievably destroyed, a key component of the Confidentiality and Privacy criteria.
The Rise of SOC 2+ Integrated Audits
Another major trend impacting SOC 2 planning is the growth of SOC 2+ reports. In these integrated audits, a CPA firm evaluates your controls against the SOC 2 framework and another standard—like HIPAA or ISO 27001—within a single engagement.
- SOC 2 + HIPAA: Essential for HealthTech companies, this report maps SOC 2 controls to the specific safeguards required by the HIPAA Security and Breach Notification Rules.
- SOC 2 + ISO 27001: For companies with global customers, this combines the U.S.-focused SOC 2 with the international standard for information security management.
- SOC 2 + CSA STAR: Crucial for cloud service providers, this maps SOC 2 controls to the Cloud Security Alliance’s Cloud Controls Matrix (CCM).
The rise of integrated audits is a direct response to market fatigue. Businesses are tired of running separate, redundant, and expensive audits for every framework they need. A SOC 2+ report uses the massive control overlap shown in a SOC 2 compliance framework comparison chart to get way more bang for your audit buck.
For someone pursuing SOC 2, this shift is paramount. It means your initial readiness activities should anticipate future needs. By planning for a SOC 2+ audit from the beginning and selecting an audit firm with proven experience in integrated engagements, you turn your SOC 2 effort into a foundational asset for future compliance, not a one-off project that will be obsolete next year.
How To Select The Right Auditor For Your Needs
Selecting an audit firm is a strategic decision that directly influences the cost, timeline, and ultimate value of your SOC 2 report. The right auditor acts as a long-term partner who understands your business, technology, and strategic goals. For a company preparing for SOC 2, making an informed choice is critical to ensuring the audit process is efficient and the final report meets the expectations of key customers and stakeholders. The SOC 2 compliance framework comparison chart is the foundational tool for this process, enabling you to ask targeted questions that go beyond price and reveal an auditor’s true expertise and efficiency.

Step 1: Identify Your Framework Roadmap
Before contacting any auditors, use the comparison chart to define your compliance roadmap. Identify the framework you need now (likely SOC 2 for U.S.-based SaaS companies). Then, anticipate future requirements. If you plan to expand into the EU, ISO 27001 should be on your two-year plan. If you handle healthcare data, a SOC 2 + HIPAA integrated audit is inevitable. This initial step provides a clear, long-term view of your compliance needs, which is essential for selecting a partner who can grow with you.
Step 2: Filter Auditors by Relevant Expertise
With your roadmap in hand, filter potential audit firms based on demonstrated expertise across all your required frameworks. Do not simply search for a “SOC 2 auditor.” Look for a firm with verifiable experience in SOC 2 and ISO 27001, or SOC 2 + HIPAA. This is critical for SOC 2 readiness because choosing a firm that can only handle your immediate needs is a shortsighted mistake that will force you to repeat the selection process and potentially duplicate audit efforts for your next framework.
Your goal is to find a partner, not a one-time vendor. Selecting a firm that can only handle your immediate SOC 2 needs is a shortsighted mistake that will force you to repeat this entire search process in a year or two for your next framework.
Step 3: Ask Intelligent, Specific Questions
This is where your understanding of control overlaps becomes a powerful tool. During interviews, move beyond generic inquiries about price and timeline. Ask questions that probe their expertise and operational efficiency:
- “How do you approach evidence collection for overlapping controls between SOC 2’s Common Criteria and ISO 27001’s Annex A to maximize efficiency?”
- “Can you describe your methodology for a SOC 2 + HIPAA integrated audit? Specifically, how do you map controls to the HIPAA Security Rule safeguards?”
- “What is your experience with compliance automation platforms like Drata or Vanta? How does your audit process leverage the capabilities of these tools?”
The quality of their answers will reveal their ability to conduct efficient, multi-framework audits. This structured approach, guided by your framework comparison, is a critical component of successful SOC 2 audit readiness. It ensures you select a partner who can leverage control overlaps to minimize redundant work and deliver a high-value report.
Finding the right auditor can feel overwhelming, but it doesn’t have to be. SOC2Auditors provides verified data on over 90 audit firms, with real price ranges and performance metrics to help you make a confident decision. Get three tailored, objective auditor matches without the sales calls by visiting SOC2Auditors.org.
A well-executed SOC 2 compliance framework comparison chart is more than just a document; it’s the cornerstone of a strategic and efficient compliance program. By understanding control overlaps, planning for future requirements, and selecting the right partners and tools, you transform your SOC 2 audit from a mandatory hurdle into a powerful demonstration of trust and security. This strategic approach ensures you are not just compliant, but truly ready for the audit, laying a scalable foundation that supports business growth and meets evolving customer demands.