A System and Organization Controls 2 (SOC 2) report is an attestation from a licensed Certified Public Accountant (CPA) firm, providing an opinion on the effectiveness of a service organization’s internal controls relative to one or more of the five Trust Services Criteria (TSC): Security, Availability, Processing Integrity, Confidentiality, and Privacy. The Payment Card Industry Data Security Standard (PCI DSS) is a prescriptive set of security requirements mandated by the major payment card brands, designed exclusively to protect cardholder data wherever it is stored, processed, or transmitted. For a Software-as-a-Service (SaaS) company, understanding this distinction is fundamental to developing an efficient and effective compliance strategy.
Defining SOC 2 and PCI DSS for SaaS Companies

SOC 2 is an attestation framework from the American Institute of Certified Public Accountants (AICPA). It’s designed to let service organizations, like a SaaS company, report on their internal controls. The report is built around five Trust Services Criteria (TSCs): Security, Availability, Confidentiality, Processing Integrity, and Privacy. The Security TSC, also known as the Common Criteria, is mandatory for every SOC 2 report.
PCI DSS, or the Payment Card Industry Data Security Standard, is a prescriptive set of rules created by the PCI Security Standards Council (PCI SSC), which includes major payment card brands (Visa, Mastercard, etc.). Its sole purpose is to protect cardholder data wherever it is stored, processed, or transmitted, by enforcing a strict set of over 300 technical and operational requirements.
Why does this matter for someone pursuing SOC 2?
For a SaaS company pursuing SOC 2 compliance, this distinction is critical for scoping and resource allocation. While both frameworks address data security, SOC 2’s flexible, principles-based structure allows you to build controls that align with your specific business operations and customer commitments. PCI DSS is a rigid, mandatory standard that only applies if you handle cardholder data directly. Even if you use a third-party processor and your PCI DSS scope is minimal, enterprise clients will still demand a SOC 2 report to gain assurance over your platform’s overall security, availability, and confidentiality—areas PCI DSS does not cover. Your SOC 2 audit is the primary mechanism for providing this comprehensive assurance. You can get a full rundown in our complete guide on what SOC 2 compliance is.
Core Focus and Applicability
A principles-based framework like SOC 2 allows you to design security controls that fit your company’s unique technology stack and operational environment. For example, to meet the requirements of TSC CC6.1 (Logical Access Security), you can implement controls that are appropriate for your cloud-native architecture rather than being forced to adhere to prescriptive rules designed for on-premise data centers. This flexibility is why SOC 2 is the foundational compliance report for most B2B SaaS companies seeking to demonstrate broad operational security to enterprise customers.
PCI DSS, with its 12 core requirements and over 300 specific sub-requirements, only applies if your systems store, process, or transmit a primary account number (PAN). If you offload that responsibility to a third-party payment processor like Stripe or Braintree, your PCI DSS scope shrinks dramatically. However, you still need to prove your own platform’s security for all other customer data, a gap that a SOC 2 report fills perfectly.
The table below breaks down the key differences at a high level.
| Attribute | SOC 2 (System and Organization Controls 2) | PCI DSS (Payment Card Industry Data Security Standard) |
|---|---|---|
| Primary Goal | To report on controls relevant to security, availability, confidentiality, processing integrity, and privacy. | To protect cardholder data and prevent credit card fraud. |
| Governing Body | American Institute of Certified Public Accountants (AICPA) | PCI Security Standards Council (PCI SSC) |
| Core Structure | Principles-based, flexible framework based on the five Trust Services Criteria. | Prescriptive, with 12 specific and detailed requirements. |
| Primary Audience | Customers, partners, and stakeholders who need assurance about a service’s security posture. | Banks, payment brands, and any entity involved in payment processing. |
| Typical Outcome | A SOC 2 Type 1 or Type 2 attestation report issued by a CPA firm. | A Report on Compliance (RoC) or Self-Assessment Questionnaire (SAQ). |
Analyzing Core Objectives and Scope
To understand the practical implications of SOC 2 vs. PCI DSS, you must analyze their core objectives, as this directly dictates the audit scope. SOC 2’s objective is to provide assurance to stakeholders that a service organization has effective internal controls in place to meet its commitments, benchmarked against the chosen Trust Services Criteria. PCI DSS has a singular mission: preventing credit card fraud by protecting cardholder data.
Why does this matter for someone pursuing SOC 2?
This difference in objective directly impacts your SOC 2 readiness strategy. The flexible scope of a SOC 2 audit is a strategic advantage. You, in collaboration with your CPA firm, define the system boundaries to create a report that directly addresses your customer contracts and business needs. For instance, you can scope the audit to a specific SaaS product line and the underlying production environment, while explicitly excluding development networks or other non-relevant services. This allows you to focus your resources on implementing and testing controls that are most critical to your customers, such as those related to CC7.1 (Monitoring) to detect changes and anomalies in your environment.
The scope of PCI DSS is, by contrast, rigid and non-negotiable. It automatically covers every system component, person, and process that stores, processes, or transmits cardholder data—the Cardholder Data Environment (CDE)—as well as any system connected to it. The primary strategy for PCI DSS is therefore scope reduction through network segmentation, a stark contrast to the business-aligned scoping of SOC 2.
SOC 2 vs PCI DSS Scope and Objective Comparison
This table puts the fundamental differences in purpose and scoping methodology into sharp focus.
| Attribute | SOC 2 | PCI DSS |
|---|---|---|
| Objective | Assure stakeholders about the effectiveness of controls related to the selected Trust Services Criteria. | Prevent credit card fraud by protecting cardholder data. |
| Scoping Method | Flexible and defined by the organization based on its services and customer commitments. | Prescriptive and defined by data flow; encompasses the entire Cardholder Data Environment (CDE). |
| Control Focus | Principles-based, focusing on the design and effectiveness of controls that meet the criteria. | Rules-based, with over 300 specific requirements that must be met for a “pass” verdict. |
| Primary Driver | Customer demand, sales enablement, and demonstrating operational maturity. | Mandatory requirement for any entity that handles payment card data. |
Understanding this difference is central to preparing for a SOC 2 audit. It confirms that even if you use a PCI-compliant payment processor, your customers still need the broader assurance for your platform’s security, availability, and confidentiality that only a SOC 2 report can provide. Your SOC 2 readiness journey begins by identifying the controls and criteria that matter most to your customers and scoping your audit to prove you protect what you promise.
Mapping Control Overlaps for Efficiency
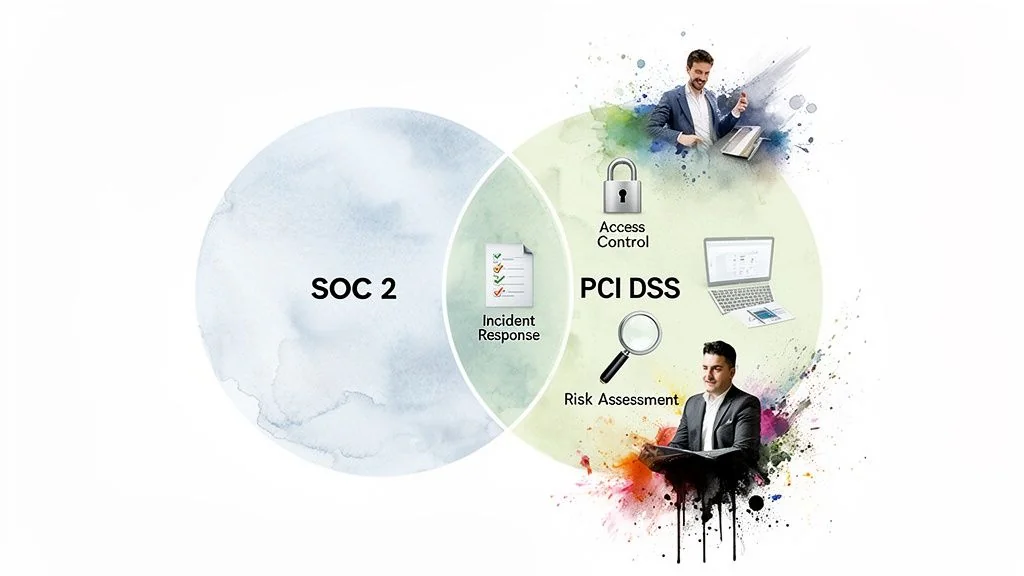
While SOC 2 and PCI DSS serve different purposes, a significant portion of the controls required by both frameworks overlap. This means the work you invest in preparing for a SOC 2 audit is not a sunk cost; it is a strategic investment that builds the foundation for PCI DSS compliance, creating significant efficiencies.
Why does this matter for someone pursuing SOC 2?
Understanding this control overlap is crucial for an efficient SOC 2 readiness process. By designing your SOC 2 controls with an eye toward future compliance needs, you can “test once, comply many.” For example, the evidence gathered for your SOC 2 audit’s logical access controls (CC6.1) can be directly repurposed to satisfy PCI DSS Requirement 7. This synergy saves time, reduces audit fatigue for your engineering team, and lowers overall compliance costs. Analyses show a control overlap of up to 60% between the frameworks, and companies that plan for this can slash their combined compliance costs by 20-30%. You can find more detail on how this overlap drives efficiency at Strikegraph.com.
Principles vs. Prescriptions in Practice
The key difference lies in implementation and testing. SOC 2 is principles-based, allowing you to design controls that fit your specific technology and business processes. PCI DSS is prescriptive, demanding specific configurations and actions with little flexibility.
Consider access control:
- SOC 2 (CC6.1): The entity implements logical access security measures to protect against threats from sources both internal and external. This is a broad principle. You meet it by demonstrating you have a robust system for managing access, such as role-based access control (RBAC) and regular access reviews, regardless of the specific tools used.
- PCI DSS (Requirement 7): Restrict access to cardholder data by business need to know. It gets granular, specifying that access control systems must be configured to “deny all” by default and that roles must be formally defined and assigned.
A strong SOC 2 program designed around the Trust Services Criteria will naturally build the processes, documentation, and security posture needed to satisfy many of the rigid PCI DSS requirements.
Key Areas of Control Synergy
To make this practical, let’s examine where the controls directly map. By focusing on these areas during your SOC 2 readiness, you proactively prepare for future compliance needs without significant extra effort.
| Control Domain | SOC 2 Trust Services Criteria (TSC) | Corresponding PCI DSS Requirement | Actionable Insight for SaaS |
|---|---|---|---|
| Risk Management | CC3.1: The entity identifies risks…and analyzes them to determine how the risks should be managed. | Req 12.2: Implement a formal risk assessment process that identifies threats, vulnerabilities, and results in a formal, documented analysis of risk. | Your annual SOC 2 risk assessment can be extended to specifically address risks to cardholder data, satisfying both frameworks with a single, unified process. |
| Access Control | CC6.2 & CC6.3: Controls for authorizing, modifying, and removing user access in a timely manner. | Req 7.1 & 7.2: Restrict access based on need-to-know and establish an access control system with assigned privileges. | Your SOC 2 Joiner, Mover, Leaver (JML) process, including documented approvals and timely de-provisioning, directly supports PCI’s stringent access control demands. |
| Incident Response | CC7.3: The entity has a plan to respond to security incidents. | Req 12.10: Implement an incident response plan. Test it at least annually. | The incident response plan developed for SOC 2 can be adapted with specific procedures for handling cardholder data breaches to meet PCI’s prescriptive reporting requirements. |
| System Monitoring | CC7.2: The entity monitors control components…and takes corrective action to remediate deficiencies. | Req 10: Track and monitor all access to network resources and cardholder data. | Log collection, correlation, and review processes established for your SOC 2 audit (e.g., using a SIEM) are foundational for the detailed, continuous logging required by PCI DSS. |
This mapping creates a clear path to efficiency. By thoughtfully designing your controls to meet the SOC 2 Trust Services Criteria, you’re not just preparing for one audit; you’re building a mature, flexible security program that simplifies future compliance efforts.
Understanding Attestation vs. Certification
The most significant philosophical difference between SOC 2 and PCI DSS is the nature of the final deliverable. A SOC 2 audit results in an attestation report, while a PCI DSS assessment leads to a certification.
A SOC 2 attestation is a formal opinion from a licensed CPA firm. The report includes a detailed management-prepared description of the service organization’s system and the design (Type 1) or design and operating effectiveness (Type 2) of its controls.
A PCI DSS certification is a binary pass/fail validation from a Qualified Security Assessor (QSA) confirming that an organization has met every applicable prescriptive requirement at a point in time.
Why does this matter for someone pursuing SOC 2?
This distinction is crucial because it positions your SOC 2 report as a strategic sales and trust-building asset, not just a compliance checkbox. The collaborative nature of a SOC 2 audit means you work with the CPA firm to craft a detailed “system description” that explains your services, infrastructure, software, people, and processes. This narrative provides rich context that enterprise clients need to evaluate your security posture. A simple pass/fail certificate from a PCI DSS assessment offers no such insight. The goal of your SOC 2 audit is to produce a comprehensive attestation report that demonstrates security maturity, helps your sales team overcome objections, and builds customer trust. For a deeper look, see our guide on the SOC 2 certification report.
The pass/fail rigidity of PCI DSS certification is its defining feature. An organization must meet every one of the 300+ prescriptive controls exactly as written to pass. There is no room for compensating controls or contextual explanations in the same way a SOC 2 report allows. This structure is effective for its narrow purpose—validating payment security—but it fails to provide the broader assurance that enterprise customers demand regarding a SaaS platform’s overall security, availability, and confidentiality.
Here’s a quick breakdown of the key distinctions between the final reports.
| Characteristic | SOC 2 Attestation Report | PCI DSS Report on Compliance (RoC) |
|---|---|---|
| Issuer | Licensed CPA Firm | Qualified Security Assessor (QSA) |
| Outcome | Auditor’s opinion (unqualified, qualified, etc.) with detailed findings. | Pass/fail certification. |
| Content | System description, control details, test procedures, and results. | Validation of adherence to specific PCI DSS requirements. |
| Flexibility | Scope and controls are tailored to the service organization. | Scope and requirements are rigidly defined by the standard. |
Understanding this difference is vital for your SOC 2 readiness. The objective is not merely to get a “pass,” but to produce a high-quality attestation report that clearly communicates the strength of your control environment, based on the established principles of the AICPA’s Trust Services Criteria.
A Decision Framework for Your SaaS Business
Choosing between SOC 2 and PCI DSS is not a subjective preference; it is a determination based on your business model and data flows. The decision hinges on one primary question: Does your system store, process, or transmit raw cardholder data?
Why does this matter for someone pursuing SOC 2?
Answering this question accurately is the first and most critical step in defining your compliance roadmap and preparing for a SOC 2 audit. If you incorrectly assume you need a full PCI DSS certification, you could waste six months and over $100,000 on an unnecessary and grueling project. Conversely, understanding that your path is SOC 2 clarifies your priorities. It confirms that even when you offload payment processing, your enterprise customers still require the broad assurance that only a SOC 2 report can provide for the security of their data within your application. This clarity allows you to focus your resources on the SOC 2 audit that will actually help you close deals.
Scenario-Based Decision Paths
Let’s walk through common SaaS scenarios to determine the correct compliance path.
Scenario 1: General B2B SaaS
- Your Model: You use a PCI-compliant payment processor like Stripe and their hosted payment pages or tokenization solutions (e.g., Stripe Elements). Raw cardholder data never touches your servers.
- Decision: Your primary focus is SOC 2. Your PCI DSS obligation is minimal, typically limited to completing a Self-Assessment Questionnaire (SAQ) A. Your SOC 2 report, with an opinion on the Security (Common Criteria) TSC, is the key deliverable for demonstrating security to enterprise clients.
Scenario 2: FinTech with a Third-Party Processor
- Your Model: You operate a FinTech platform but use a fully compliant third-party processor for all card transactions. You handle other sensitive financial data but not raw card numbers.
- Decision: SOC 2 is your foundational report, and you should strongly consider including the Confidentiality and Availability TSCs to meet heightened customer expectations. Your PCI DSS scope remains minimal (likely SAQ A), but your SOC 2 report is essential for proving the robustness of your overall control environment.
Scenario 3: SaaS Handling Raw Cardholder Data
- Your Model: Your application directly stores, processes, or transmits raw cardholder data. This is rare for a modern SaaS company but may apply if you are a payment gateway or use a custom payment solution.
- Decision: You require both PCI DSS and SOC 2. You must achieve a full PCI DSS certification via a Report on Compliance (RoC) from a Qualified Security Assessor (QSA). Concurrently, enterprise customers will still demand a SOC 2 report to gain assurance over your broader service and operational controls.
Here’s how those paths break down in a simple table.
| SaaS Model | Handles Raw Cardholder Data? | Primary Compliance Focus | PCI DSS Obligation |
|---|---|---|---|
| General B2B SaaS | No (uses third party) | SOC 2 | Minimal (e.g., SAQ A) |
| FinTech Platform | No (uses third party) | SOC 2 (with additional TSCs) | Minimal (e.g., SAQ A) |
| Payment Gateway | Yes (directly on servers) | PCI DSS & SOC 2 | Full Certification (RoC) |
This framework makes it clear: for the overwhelming majority of modern SaaS businesses, the journey starts with SOC 2. Getting this right allows you to scope your SOC 2 audit to deliver maximum value by proving you have the controls that matter to your customers. Foundational practices like adhering to IT asset management best practices for compliance are critical for maintaining readiness for any security audit, supporting both SOC 2 and PCI DSS by ensuring a complete and accurate inventory of systems in scope.
Tying It All Back to Your SOC 2 Audit Readiness
Understanding the nuances of the SOC 2 vs. PCI DSS debate is instrumental for effective SOC 2 audit readiness. By recognizing PCI DSS as a narrow, prescriptive standard for a specific data type, you can confidently focus your resources on a well-scoped SOC 2 attestation that addresses the broader security concerns of your enterprise customers. When your SaaS company uses a PCI-compliant payment processor like Stripe or Braintree, you strategically outsource the highest-risk component of payment processing. This frees you to concentrate on the SOC 2 report needed to prove the security, availability, and confidentiality of your core platform—the very things that enable sales and build trust.
The principles-based nature of SOC 2 allows you to build a security program based on the AICPA’s Trust Services Criteria (TSCs) that is both robust and adaptable. This is not just about passing a single audit; it’s about creating a scalable compliance foundation. The controls you implement for SOC 2—from risk management (CC3 series) to logical access controls (CC6 series) and change management (CC8 series)—are not single-use. They form a mature security program whose evidence and processes can be mapped directly to the prescriptive requirements of other frameworks like PCI DSS, ISO 27001, or HIPAA, significantly reducing the effort and cost of future audits. For example, strong IT asset management best practices for compliance developed for SOC 2 directly support PCI Requirement 2 by ensuring all system components are inventoried and managed.
This visual decision tree makes it simple to see which compliance path your SaaS business should prioritize based on how you handle customer data.
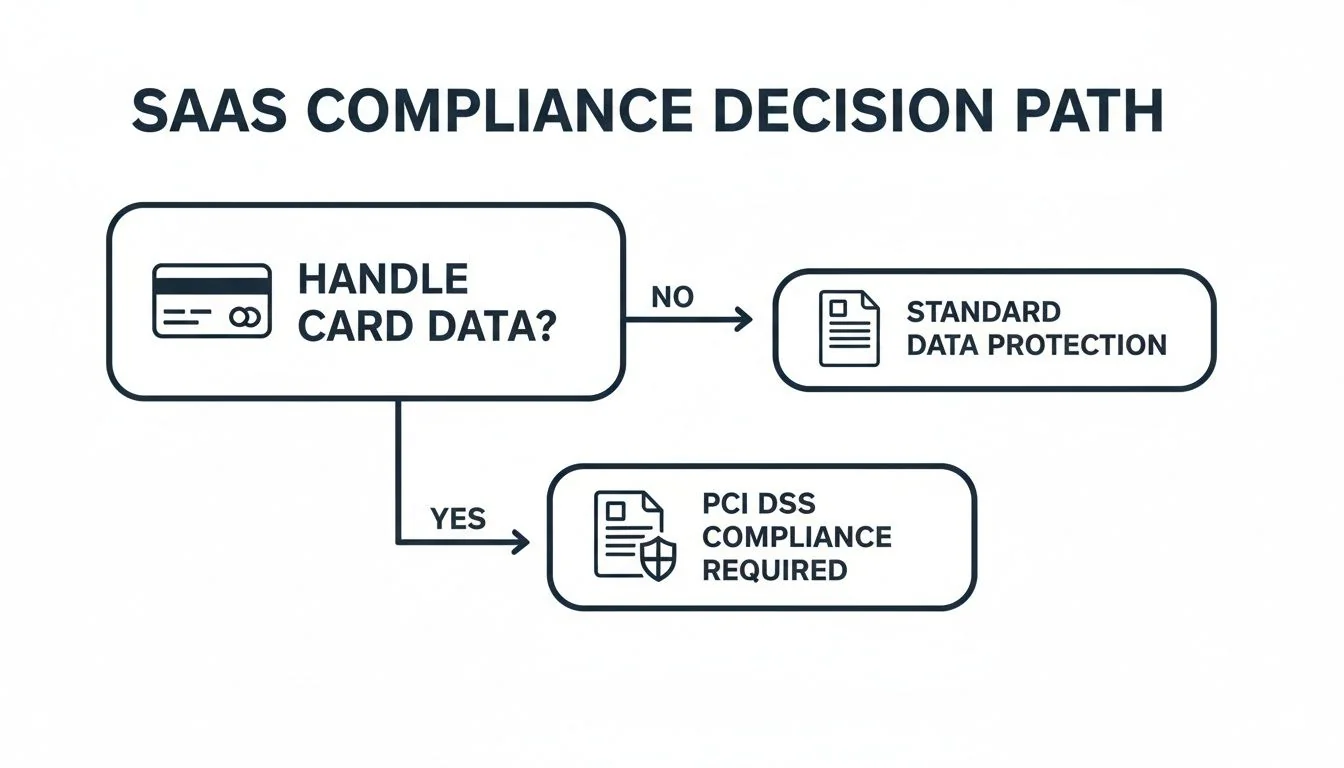
As the flowchart illustrates, for the majority of SaaS companies that wisely avoid direct contact with raw cardholder data, the primary compliance mission is SOC 2. It is the key to unlocking enterprise contracts and demonstrating operational maturity. Your SOC 2 audit readiness begins with a clear understanding of your system, your customer commitments, and the strategic value of a comprehensive attestation report. By connecting this knowledge to your business model, you transform the SOC 2 audit from a mandatory hurdle into a powerful asset for growth.
Navigating auditor selection can feel as tough as the audit itself. At SOC2Auditors, we’ve done the hard work for you. Our platform gives you verified data on pricing, timelines, and real client satisfaction for over 90 firms, helping you find the perfect auditor for your SOC 2 journey without the sales calls. Get three tailored matches in 24 hours and make a data-driven decision with confidence at https://soc2auditors.org.