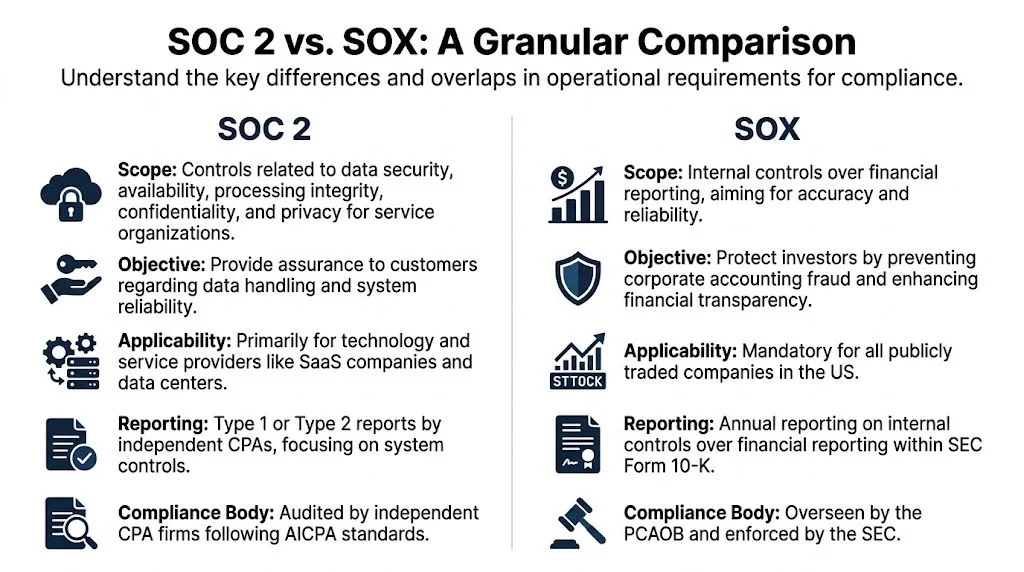
If you’re a CTO at a SaaS company, you’ve probably seen this happen. A large prospect sends a security questionnaire, asks for your SOC 2 report, then adds questions about SOX controls because their procurement, internal audit, or finance team wants to understand your impact on their financial reporting environment. Those requests aren’t interchangeable. SOC 2 is an attestation report on a service organization’s controls against the AICPA Trust Services Criteria. SOX, specifically SOX 404, is a public-company requirement focused on internal controls over financial reporting. If you’re pursuing SOC 2, that distinction matters because it determines what belongs in scope, what evidence you need, and whether you’re building a lean trust program or an unnecessarily expensive one.
Defining SOC 2 and SOX Compliance
A startup usually hits this fork earlier than expected. Sales wants a SOC 2 report to close enterprise deals. Finance or a large customer starts asking SOX-flavored questions because your product touches billing, revenue, payroll, or another process tied to financial reporting. Those requests sound related, but they lead to different scopes, evidence sets, and audit costs.
SOC 2 is an attestation framework for service organizations. It is built to show customers and partners that your controls are designed and operating effectively against the AICPA Trust Services Criteria. Security is always in scope. Availability, processing integrity, confidentiality, and privacy are added based on what your product does, what data you handle, and what your buyers review. If your team needs a baseline explainer, this guide to what SOC 2 compliance means in practice is a useful starting point.
The report type matters. A Type 1 report tests controls at a point in time. A Type 2 report tests whether those controls operated over a review period, which is why buyers usually value it more. If you need a refresher on the differences between SOC 2 Type 1 and Type 2 reports, make that decision before you pick an auditor or promise a date to sales.
SOX is different because the audience and risk are different. SOX 404 focuses on internal control over financial reporting. For public companies, and private companies preparing to go public, the question is whether management can support the accuracy of the financial statements and whether auditors can test that support. On the IT side, that usually means IT general controls over systems that affect financial reporting, including access, change management, and operational controls.
The practical mistake I see is over-scoping too early. A SaaS company pursuing SOC 2 does not need to build a full SOX program just because a prospect uses the term loosely in a questionnaire. It does need to identify where the same evidence can serve both purposes later. Access reviews, ticket-based change approvals, logging, and vendor due diligence often overlap. The testing standard, population, and audience do not.
That distinction shapes who you hire. For an early-stage company chasing enterprise deals, a SOC 2 auditor that works with venture-backed SaaS companies is usually the right first move. For a late-stage company with IPO plans or audited financials under tighter scrutiny, bring in advisors who understand ICFR scoping and can map your existing security controls to future SOX testing without turning a lean trust program into a finance-heavy compliance project.
The Core Purpose of Each Framework
SOC 2 and SOX can share controls, but they exist for different reasons. If you miss that, you usually overspend.
SOC 2 is about commercial trust
Most companies pursue SOC 2 because customers ask for proof. Enterprise buyers want a report they can hand to security, legal, procurement, and sometimes internal audit. They don’t want a policy binder. They want independent validation that your controls work.
SOC 2 Type 2 is especially useful because it tests operating effectiveness over time, which gives buyers more confidence than a point-in-time snapshot. The business implication is direct. Strong evidence and a credible report can remove friction from vendor reviews and help sales teams move deals forward faster.
The framework supports that commercial purpose through the AICPA Trust Services Criteria:
- Security: Mandatory for every SOC 2. It covers protection against unauthorized access.
- Availability: Relevant if uptime commitments matter to your contracts or enterprise buyers.
- Processing integrity: Important when customers rely on complete, valid, accurate, and timely processing.
- Confidentiality: Often selected when you handle sensitive business data under contract.
- Privacy: Relevant when you process personal information and need controls around notice, consent, retention, and disclosure.

What works for SOC 2 is a scoped, buyer-aware program. If you sell B2B SaaS into regulated or enterprise accounts, start with the criteria your customers care about. What doesn’t work is selecting every optional criterion because it sounds thorough. That creates more control design, more evidence requests, and more room for exceptions.
SOX is about regulatory accountability
SOX is not a market signal. It’s a legal requirement for public companies focused on investor protection and accurate financial reporting. That purpose drives a more rigid posture.
The controls under SOX aren’t chosen because a customer asked for them. They’re chosen because a failure could affect the reliability of financial statements. That makes the scoping logic narrower in one sense and tougher in another. Narrower because only systems and processes tied to financial reporting are in scope. Tougher because scrutiny is tied to financial risk and formal attestation.
Buyers read a SOC 2 report to decide whether they can trust your service. Auditors test SOX controls to decide whether financial reporting can be trusted.
For a CTO pursuing SOC 2, this difference matters because it should change your design standard. You need disciplined control operation and evidence retention, but you don’t need to force every engineering and security process into a SOX-style documentation burden unless the company is preparing for public-company obligations.
Why this matters in practice
Teams get into trouble when they borrow the wrong mindset:
- SOC 2 overbuilt like SOX: Too many approvals, too much paperwork, too little operational fit.
- SOX treated like SOC 2: Controls look reasonable on paper but aren’t sufficiently tied to financial reporting risk.
- Shared controls with no ownership model: Security, IT, finance, and engineering all assume someone else owns the evidence.
If you’re deciding where to invest first, SOC 2 usually delivers earlier business value for a private SaaS company because it directly supports customer trust and enterprise sales. SOX matters when your company is public, close to public, or your product is tightly embedded in financially significant workflows.
A Detailed Comparison of SOC 2 and SOX Requirements
A CTO usually feels the difference between SOC 2 and SOX the first time an auditor asks, “What exactly is in scope?” That question drives cost, timeline, evidence burden, and which internal teams get pulled into the work.
SOC 2 and SOX can share control themes, but they are not interchangeable audits. One is usually a sales and trust motion for service organizations. The other is a financial reporting obligation tied to public-company requirements and investor scrutiny.
SOC 2 vs. SOX At a Glance
| Criterion | SOC 2 | SOX (Sarbanes-Oxley) |
|---|---|---|
| Primary objective | Demonstrate trust in operational controls for service delivery | Demonstrate effective internal controls over financial reporting |
| Main audience | Customers, prospects, partners | Management, external financial auditors, regulators, investors |
| Applicability | Common for service organizations, especially SaaS | Mandatory for public companies |
| Governing framework | AICPA Trust Services Criteria | SOX 404 and related ICFR expectations |
| Core control focus | Security, availability, processing integrity, confidentiality, privacy | ITGCs and business controls affecting financial reporting |
| Required scope logic | Systems, processes, people, and vendors supporting the in-scope service | Systems and processes that can affect financial statements |
| Audit output | Type 1 or Type 2 report | Annual ICFR assessment and related attestation requirements |
| Flexibility | Tailored to the service and selected criteria | More rigid because controls must align to financial reporting risk |
Scope is where teams overspend
The practical difference starts with what each framework asks you to prove.
SOC 2 reaches across the systems and processes that support the service your customers rely on. That often includes production infrastructure, identity, change management, logging, incident response, support workflows, and third-party vendors. If a control failure could weaken security or service commitments, it can land in scope.
SOX is narrower, but it is not lighter. It focuses on internal control over financial reporting. The question is whether a system, process, or access path could affect the financial statements. That usually pulls in the ERP, billing stack, finance applications, and the IT controls around systems feeding revenue, journal entries, or reporting outputs.
For a SaaS company, that creates a real budget difference. A broad SOC 2 scope can touch more systems. A SOX program often touches fewer systems but demands tighter linkage to financial reporting risk, stronger segregation of duties, and more formal review evidence.
The same control can mean different things
Access reviews are a good example.
In SOC 2, an auditor wants to know whether privileged access is approved, limited, and reviewed because that supports customer trust and system security. In SOX, the same access review matters only if the user can alter financially relevant data or change logic that affects reporting.
Change management works the same way. A production deployment record may satisfy part of a SOC 2 test because it shows changes are approved and tested before release. Under SOX, that same evidence has to show the change affected a financially relevant system, the right reviewer approved it, and the reviewer had the authority and independence to do so.
That difference matters when building controls early. Startups often write one policy and assume it covers both frameworks. It rarely does unless the evidence is structured with both use cases in mind.
Report format affects how you prepare
SOC 2 produces a report that prospects, customers, and procurement teams read. If you are deciding between a Type 1 and a Type 2, the business question is simple: will buyers accept design-only assurance, or do they want operating evidence over time? The answer often shows up in enterprise deal cycles. If your sales team keeps hearing “send the Type 2,” the priority is already set. This difference between a SOC 1 and SOC 2 report also helps clarify why these reports get used differently by buyers and auditors.
If you need a deeper operational checklist for evidence and control execution, this SOC 2 Type 2 Requirements and Compliance guide is useful because it frames what auditors typically look for in a live environment.
SOX does not produce a customer-facing trust report in the same way. It supports management assessment and, for many public companies, external auditor attestation over internal controls tied to financial reporting. That changes the writing standard, the review standard, and the tolerance for vague ownership.
A quick explainer is worth watching if your team needs a visual overview before scoping control work:
Auditor choice matters more than teams expect
This is one of the biggest planning mistakes I see.
For SOC 2, an early-stage company usually needs a CPA firm that understands cloud infrastructure, startup velocity, and how to scope to the actual service instead of auditing the entire company by habit. A firm that mainly handles mature public-company work can create unnecessary documentation overhead and slow engineering teams without improving the report buyers care about.
For SOX, industry experience and coordination with the financial statement auditor matter much more. The auditor has to understand ICFR testing, management review controls, and how ITGC failures cascade into financial reporting conclusions. A great SOC 2 auditor is not automatically the right SOX advisor.
Mid-market companies preparing for an IPO or serving public-company customers should choose with reuse in mind. The best outcome is not one auditor for everything. It is a pair of advisors who can align control language, testing expectations, and evidence retention so today’s SOC 2 work does not have to be rebuilt later.
What this means for priority setting
If the company is private and selling into enterprise accounts, SOC 2 usually comes first because it affects pipeline movement, security reviews, and time to close. If the company is public, close to filing, or already dealing with ICFR scrutiny, SOX takes priority because the regulatory and financial stakes are higher.
For companies in between, the smarter decision is usually staged. Build controls that satisfy current SOC 2 demand, but document ownership, approvals, and evidence in a way that can support SOX later. That keeps compliance work tied to business timing instead of forcing public-company process weight onto a team that is still trying to ship product.
Evidence Mapping and Control Overlap
The smart way to handle soc 2 vs sox isn’t to run two separate compliance universes. It’s to identify where one control activity can satisfy both, then store evidence so auditors can test it without asking your team for the same artifact twice.

Where overlap usually exists
The strongest overlap sits in IT General Controls. In practice, that usually means:
- Access management: Provisioning, deprovisioning, role changes, privileged access reviews, MFA.
- Change management: Request tickets, approvals, testing evidence, deployment records, separation of duties.
- Operations: Logging, incident response, backups, and monitoring.
These controls matter in SOC 2 because they support system security and reliability. They matter in SOX when they protect systems tied to financial reporting.
The common mistake is storing the same evidence in different folders for different frameworks. That creates duplicate work and inconsistent versions.
A concrete example with Jira and identity systems
Take a production change ticket in Jira.
A good ticket package usually includes the requested change, reviewer approval, testing notes, a link to the pull request, and deployment evidence. In a mature environment, it may also point to CI/CD checks and rollback steps.
That same package can support:
- SOC 2: Evidence that changes are authorized, tested, and controlled.
- SOX: Evidence that changes to a financially relevant application were approved and implemented under a defined control process.
The same principle applies to access reviews in Okta, Google Workspace, or Microsoft Entra ID. One monthly or periodic review can support both frameworks if the review population, approver, and follow-up actions are clear.
One artifact should answer three questions: what changed, who approved it, and what happened after implementation.
How to structure evidence so it can be reused
A workable method is simple. Tag evidence by framework, system, control owner, and review period.
For example:
| Evidence item | Primary owner | Useful for SOC 2 | Useful for SOX |
|---|---|---|---|
| Jira change ticket with approvals and test results | Engineering manager | Yes | Yes, if the app affects financial reporting |
| Okta access review export | IT or Security | Yes | Yes, if finance-linked apps are included |
| Incident response record | Security | Yes | Sometimes, if the incident affects financial systems |
| Backup restore test record | Infrastructure | Yes | Yes, when the system is financially relevant |
This is also where teams often confuse reporting types. If your internal stakeholders are mixing up service-organization reporting with controls over financial reporting, this explainer on the difference between a SOC 1 and SOC 2 report helps reset the conversation.
A practical workflow that works
The teams that keep evidence reuse manageable usually follow a basic pattern:
-
Define shared control families first
Start with access, change, and operations controls. Those are the most reusable. -
Map systems, not just frameworks
Label which applications are in SOC 2 scope, which are financially relevant, and which are both. -
Assign one evidence owner per artifact
If Jira tickets come from engineering, don’t ask GRC to recreate them in a spreadsheet. -
Store evidence in one system of record
That can be a GRC platform, a structured document repository, or a well-managed audit workspace. -
Write control narratives that explain reuse
Auditors move faster when the intent and applicability are documented up front.
What doesn’t work is retrofitting overlap at the end of the audit period. By then, screenshots are missing, approvals are inconsistent, and the team is trying to reconstruct what happened from Slack threads and memory.
For startups with IPO ambitions, evidence mapping is one of the few compliance habits that keeps paying off. It makes your SOC 2 program easier to run now and gives you a cleaner launch point if SOX becomes a real requirement later.
If you’re already past readiness and need the firm-side view — which auditors can credibly cover both attestation work and SOX 404 ITGC scope under one engagement — see the SOC 2 Type 2 + SOX 404 ITGC bridge. It walks through the TSC-to-ITGC mapping and the “SOC 2+” scope concept that lets a single firm cover both without the duplicate testing tax.
Timelines and Costs A Realistic Breakdown
A CTO usually feels the cost difference between SOC 2 and SOX long before finance labels it. One shows up as a project with a defined audit window. The other becomes a standing operating requirement that keeps pulling time from engineering, IT, finance, and executives every quarter.
That distinction matters because bad assumptions here create two expensive outcomes. Teams underbudget SOC 2 by treating it as an audit invoice instead of a program. Or they overbuild it with public-company rigor they do not need yet.
What SOC 2 usually costs in practice
For startups and mid-market companies, SOC 2 spend is driven less by the report itself and more by how much cleanup is needed before the auditor starts fieldwork. A company with clear ownership, working access controls, consistent change records, and a clean asset inventory can move fast. A company doing evidence collection from Slack, screenshots, and last-minute policy edits usually pays for that disorder in audit fees and internal labor.
The cost typically breaks into four buckets:
- Readiness work: Gap assessment, control design, policy updates, and assigning owners.
- Tooling: GRC software, identity systems, endpoint management, ticketing discipline, and evidence collection workflows.
- Audit fees: Type 1 is narrower. Type 2 adds the observation period and more testing effort.
- Internal time: Security, engineering, IT, HR, legal, and leadership all contribute, even if no one calls it budget.
The timeline follows the same pattern. A first-time Type 1 can move relatively quickly if scope is tight and the environment is stable. A Type 2 takes longer because the controls have to operate consistently over time, not just exist on paper.
For early-stage SaaS, the practical mistake is buying an oversized audit before the company has repeatable control execution. For a growth-stage company selling into larger enterprises, the bigger risk is choosing the cheapest path, then missing buyer deadlines because the audit drags or the report raises questions procurement cannot clear.
SOX is an operating function, not a one-time project
SOX behaves differently because the company is not just proving security and operational discipline. It is supporting financial reporting that management and external auditors will test on a recurring cycle.
That changes both staffing and cadence.
SOC 2 can often be run as a focused cross-functional program with a defined owner and a bounded scope. SOX usually requires sustained participation from finance, accounting, IT, internal audit or SOX program leads, control owners, and external auditors. Walkthroughs, testing, issue tracking, remediation, retesting, and sign-off become part of the annual calendar.
The business implication is simple. SOC 2 usually helps revenue by reducing security review friction. SOX is about reducing financial reporting risk and meeting public-company obligations. If a private company starts building SOX-level process too early, it can slow product and infrastructure teams without improving close rates.
Auditor selection changes the economics
Auditor choice has more impact on cost and timing than many teams expect. The wrong firm creates rework, slow review cycles, vague evidence requests, and report delays. The right firm keeps scope disciplined and tests the controls that matter.
For a startup or smaller mid-market SaaS company, a boutique SOC 2 firm is often the better fit if the goal is getting a credible first report out quickly. These firms usually move faster, give clearer guidance on evidence expectations, and understand how to scope a first audit without turning it into a six-month consulting exercise.
For later-stage companies, especially those with IPO plans, financially significant systems, or regulated workflows, the better choice may be a firm with stronger experience in IT general controls and audit coordination across both security and finance stakeholders. That does not mean paying for a brand name by default. It means choosing an auditor whose testing approach matches your stage.
Use three filters:
- Stage fit: First-time SOC 2 teams need a firm that can work with immature but fixable processes.
- Scope fit: Complex environments, multiple products, or regulated customer data require tighter testing and clearer scoping.
- Future fit: If you expect SOX later, pick an auditor who recognizes reusable ITGC structure and will not force a rebuild next year.
Cheap audits often become expensive in predictable ways. The report lands late. Exceptions are written poorly. Buyer security teams ask follow-up questions your auditor should have anticipated. Engineering spends another month pulling evidence to defend a report that was supposed to reduce diligence work.
The best cost control is not squeezing the audit fee. It is setting a realistic scope, cleaning up evidence collection early, and choosing an auditor whose model fits the company you are now, while leaving room to reuse controls if SOX becomes relevant later.
Making the Right Compliance Choice for Your Company
Most companies don’t need a philosophical answer to soc 2 vs sox. They need to know what to do next based on stage, buyer pressure, and future plans.
Scenario one early-stage B2B SaaS
If you’re an early-stage SaaS company trying to unblock enterprise deals, prioritize SOC 2.
Not “SOC 2 plus a little SOX.” Not a giant control universe because one prospect asked an overbroad questionnaire. Build a practical SOC 2 program around your in-scope service, core infrastructure, identity, change management, HR onboarding and offboarding, incident response, and vendor oversight.
A few signs this is your situation:
- Your biggest pain is security review friction.
- Prospects ask for a report before they sign.
- Your finance stack is still relatively simple.
- No one is seriously planning for public-company obligations yet.
What works here is disciplined scoping and an auditor who understands first-time reports. What doesn’t work is overdesigning controls for hypothetical future IPO needs.
Scenario two growth-stage FinTech or HealthTech
If you’re moving upmarket and your product sits closer to regulated or financially sensitive workflows, pursue a rigorous SOC 2 Type 2 while intentionally designing reusable ITGCs.
That means your control set should still be driven by SOC 2 buyer needs, but your execution should be cleaner:
- Access reviews should be formal and attributable.
- Change records should be complete enough for later reuse.
- Logging and incident handling should support traceability.
- Vendor governance should be tight around critical subprocessors.
This common misunderstanding leads many teams to make a costly mistake. They hear “overlap” and assume SOC 2 is basically SOX-lite. It isn’t.
SOC 2 is broader in operational scope and customer trust. SOX is narrower and more financially specific. The overlap is useful, but the objectives are still different. If you’re in FinTech, billing, revenue workflow, payment processing, and integrations with accounting systems may increase the value of designing controls that won’t need to be rebuilt later.
Scenario three pre-IPO or newly public tech company
If you’re pre-IPO or newly public, run parallel SOC 2 and SOX thinking, but keep ownership clear.
Security and engineering shouldn’t try to absorb finance control design on their own. Finance shouldn’t assume the existing SOC 2 evidence model automatically satisfies SOX. Shared ITGCs should be mapped centrally, and the teams should agree on control owners, testing cadence, and remediation flow.
In this phase, the question isn’t “Which one do we choose?” It’s “How do we prevent duplicate effort while preserving the intent of each framework?”
A clean operating model often looks like this:
| Company stage | Priority | Recommended posture |
|---|---|---|
| Early-stage SaaS | Win enterprise trust | SOC 2 first, minimal SOX consideration |
| Growth-stage regulated SaaS | Scale into larger accounts | SOC 2 Type 2 with SOX-aware ITGC design |
| Pre-IPO or public | Support trust and reporting integrity | Parallel programs with mapped shared evidence |
The misconception to avoid
The worst framing is “SOC 2 is the easy version of SOX.”
That leads CTOs to underprepare for buyer scrutiny and overestimate how much of a future SOX program is already done. A better framing is this: SOC 2 is the right trust report for a service organization, and parts of a well-run SOC 2 program can become the operational backbone for future SOX-relevant controls.
That’s a much better reason to invest in quality. You’re not doing duplicate work. You’re building the right first layer.
Next Steps to Achieve SOC 2 Audit Readiness
A CTO usually feels the pressure here when a large prospect says, “Send your SOC 2 report,” and the sales team realizes there is no report to send. At that point, the question is not SOC 2 versus SOX in theory. It is how fast the company can produce a report that clears security review without building a program it has to redo in 12 months.
For most private SaaS companies, the right move is to get SOC 2 ready first and build it so the underlying evidence can support future ITGC work where overlap exists. That approach protects sales velocity now and reduces rework later.
Start with scope before you buy software
Define the product, environment, and people in scope first. Then pick the Trust Services Criteria that match actual customer expectations and contractual obligations. Security is always included. Availability, Processing Integrity, Confidentiality, and Privacy should be added only if they reflect how the service operates and what customers will ask your team to prove.
This decision drives cost, audit effort, and control burden. A scope that is too broad creates extra testing, more exceptions, and higher audit fees. A scope that is too narrow creates buyer friction because the report does not answer the questions enterprise security teams care about.
Run readiness like an operator, not a checkbox exercise
Before setting an audit period, test whether the control environment works in day-to-day operations. Review joiner-mover-leaver evidence, change approvals, ticket-to-deployment traceability, vendor reviews, incident handling, logging, endpoint controls, and security awareness records. If evidence only exists because the team is scrambling for the audit, the program is not ready.
A useful readiness review should answer a small set of practical questions:
- Is every control assigned to a specific owner?
- Can the team pull evidence quickly, without chasing screenshots across Slack and email?
- Do written policies match what engineering, IT, and HR do?**
- Will a buyer’s security team see a clean report or a list of exceptions and vague remediation notes?
This is also the point where startups can save future SOX effort. If access reviews, change management, and system administration controls are documented clearly now, that evidence structure can often be reused later for finance-relevant ITGCs. Not all of it will carry over, but the operating discipline will.
Choose the auditor for your stage, not just for the quote
Auditor selection has more impact than many teams expect. A startup selling into mid-market buyers usually needs a firm that can move quickly, explain evidence expectations clearly, and avoid turning a straightforward audit into a consulting project. A later-stage company with board pressure, complex infrastructure, or IPO timing may need a firm with deeper bench strength, tighter project management, and experience coordinating with legal, finance, and external stakeholders.
Price matters, but buyer acceptance matters too. A cheap audit that produces a weak report can slow deals more than it helps.
Use a shortlist based on budget, timeline, Type 1 versus Type 2 capability, industry fit, and company stage. If you want to compare firms without cold outreach, SOC2Auditors.org is a practical place to start.
SOC 2 readiness should produce more than a passing report. It should give sales a report buyers accept, give leadership a cleaner view of operational risk, and give the company an evidence model that is easier to reuse if SOX becomes relevant later.