A surprising fact about soc 2 processing integrity criteria explained is that Processing Integrity is optional in SOC 2, yet over 40% of SaaS firms pursuing SOC 2 Type 2 include it to meet enterprise demands and show reliable data handling, according to Compyl’s overview of the Processing Integrity criterion. That creates a practical decision for leadership teams. You don’t add it because it sounds thorough. You add it when customers, regulators, or your own product risk profile require proof that your system processes data correctly, not just securely.
For many organizations, the primary question isn’t “What is Processing Integrity?” It’s “Should we scope it now, later, or not at all?” That’s a business decision first, and a controls decision second. If your product moves money, calculates balances, routes orders, syncs operational records, or generates data customers rely on for decisions, this criterion often matters far more than founders expect.
What is SOC 2 Processing Integrity
Processing Integrity is one of the five Trust Services Criteria in SOC 2, defined by the AICPA as ensuring that “system processing is complete, valid, accurate, timely, and authorized to meet the entity’s objectives.” Unlike Security, which is mandatory, Processing Integrity is optional. But for financial systems, payment processors, and data-driven SaaS platforms, it directly addresses whether your application does the job customers think they’re buying.
That distinction matters for SOC 2 because buyers increasingly separate two questions. First, is the vendor secure? Second, does the system reliably process data without omission, corruption, delay, or unauthorized changes? Security answers the first. Processing Integrity helps answer the second.
Why some companies should scope it now
If your product’s value depends on trustworthy outputs, Processing Integrity can become a deal issue quickly. That’s especially true when customers rely on your platform for calculations, transaction handling, record updates, reconciliations, or reporting that feeds other systems. In those environments, a clean Security-only report can still leave a buyer asking whether the application logic is controlled.
A good go or no-go test is simple:
- Go now: Your platform processes payments, financial entries, claims, patient-related workflows, usage-based billing, or operational records where bad outputs create customer harm.
- Maybe later: Your product is early, your buyers only ask for baseline SOC 2, and your core risk is access security rather than processing correctness.
- No for now: Your system stores or transmits data but doesn’t materially transform it in ways customers depend on.
Practical rule: If a customer can ask, “How do you know the numbers in your platform are right and complete?”, you should at least assess Processing Integrity scope before starting your audit.
What the criterion really asks you to prove
This criterion isn’t abstract. It pushes teams to define processing objectives, validate inputs, control changes to processing logic, verify outputs, and preserve records. In practice, that means engineering, product, data, and GRC have to agree on what counts as correct processing and how they’ll prove it.
Why this matters for SOC 2 is straightforward. Auditors don’t just want a policy that says your system is accurate. They want evidence that your controls make bad data, bad logic, and bad outputs easier to prevent, detect, and correct.
The Five Core Criteria of Processing Integrity
Processing Integrity scope gets expensive fast. The five criteria. completeness, accuracy, timeliness, authorization, and validation. tell you whether that expense is justified for your product and customer base. If a failed control in one of these areas can create billing errors, payment mistakes, broken reports, or customer record issues, PI is usually worth serious consideration. If not, you may be adding audit work that does little for deals.
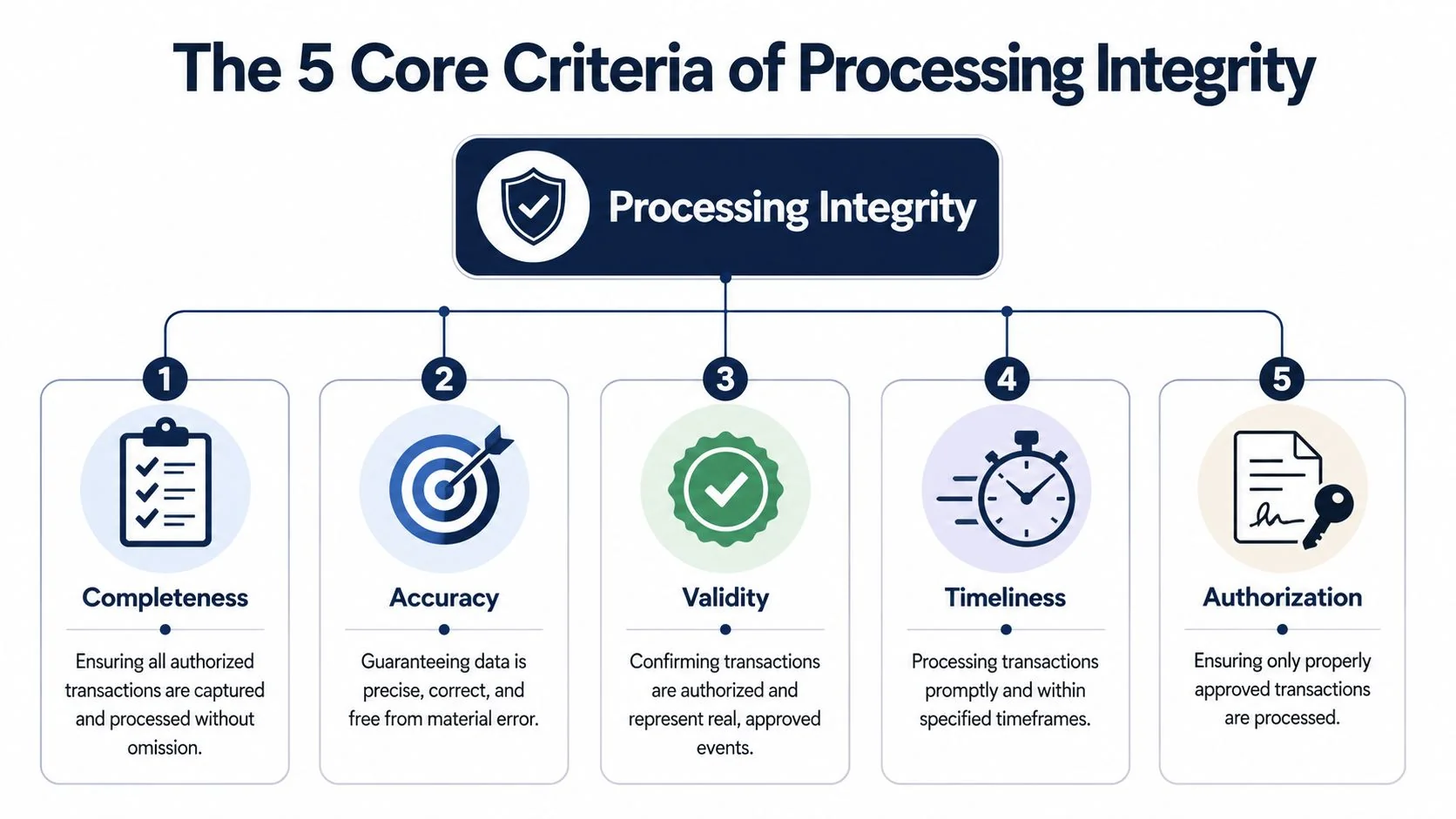
Completeness and accuracy
Completeness asks a simple question. Did every authorized record that should have been processed make it through the system? In SaaS, that often means webhook events, invoice line items, imported files, usage logs, or API transactions. The practical risk is silent loss. Missing records often create bigger customer disputes than obviously broken ones because no one notices them until reconciliation fails.
Accuracy asks whether the system produced the right result after processing. That includes calculations, mappings, transformations, currency conversions, rating logic, and downstream updates. For a workflow app, the impact may be limited to reporting. For fintech, payroll, claims, or usage-based billing, accuracy problems can turn into refunds, manual remediation, and contract risk.
For SOC 2, these two points connect directly to engineering work:
- Completeness controls usually mean sequence checks, batch totals, reconciliation jobs, queue monitoring, and exception handling with documented follow-up.
- Accuracy controls usually mean input constraints, deterministic calculation logic, peer-reviewed code changes, automated tests, and output comparisons against known expected results.
This pair is often the first go or no-go filter. Teams evaluating the broader Trust Services framework can use this guide to SOC 2 Trust Services Criteria to decide whether Processing Integrity belongs in scope.
Timeliness and authorization
Timeliness is about meeting the window your business has already promised. That window may come from SLAs, contracts, product requirements, settlement deadlines, or internal operating rules. A batch job that completes eventually can still fail the control objective if late processing changes customer balances, delays notifications, or breaks downstream dependencies.
Authorization focuses on who can trigger, approve, modify, or override processing. In practice, that includes production changes to calculation logic, rerunning jobs, correcting records, changing configuration, and using privileged access to alter outcomes. At this stage, PI authorization starts to involve significant financial outlay, because strong authorization controls usually require tighter change management, cleaner role design, and better logs than a Security-only scope would demand.
For buyers, authorization can be a strong reason to include PI. It shows that output reliability is tied to controlled software delivery, not just to good intentions.
Validation
Validation asks whether inputs and outputs are sensible before bad data spreads. That includes required-field checks, range checks, duplicate detection, format checks, balance checks, and reconciliations between systems.
This is usually the dividing line between low-stakes SaaS and high-consequence platforms. A project management tool may tolerate some bad records with limited fallout. A platform handling payouts, claims, tax data, or customer billing usually cannot.
Buyers rarely ask for validation by name. They ask whether your system catches bad data before it affects invoices, reports, payments, or account records. If your workflows cross multiple enterprise tools, documenting those checkpoints is often half the battle. This guide to SAP ServiceNow Salesforce documentation is useful for capturing the handoffs auditors and customers will ask about.
The business decision is straightforward. If these five criteria map to customer harm, revenue leakage, or material remediation effort, adding Processing Integrity can strengthen deals and answer harder buyer questions. If they do not, keep scope tighter and invest in PI later, once customer expectations justify the added control burden.
Mapping Criteria to Controls and Evidence
A lot of teams make the same mistake. They document Processing Integrity as a policy topic, then discover late in readiness that auditors expect application-level evidence. The fastest way to avoid that is to map each criterion to an operational control and then map that control to evidence you can produce.
If your workflows span tools like SAP, ServiceNow, and Salesforce, documenting the handoffs is often harder than building the control itself. A practical reference for that problem is this guide to SAP ServiceNow Salesforce documentation, which shows how to capture complex enterprise process steps in a way auditors can follow.
Processing Integrity controls and evidence map
| Criterion | Control Objective | Example Technical Control | Example Audit Evidence |
|---|---|---|---|
| Completeness | Ensure all authorized records are captured and processed | Batch totals, event queue monitoring, import job counts, reconciliation of source to destination | Reconciliation reports, exception logs, evidence of investigated discrepancies |
| Accuracy | Ensure data is processed correctly | Input format checks, range validation, calculation testing, peer-reviewed code changes | Code review records for validation logic, test results for processing changes, data quality dashboards |
| Timeliness | Ensure processing meets required deadlines | Queue alerts, job runtime monitoring, SLA thresholds, retry controls | Monitoring screenshots, incident tickets for delayed jobs, records showing investigation and resolution |
| Authorization | Prevent unauthorized processing or changes | RBAC, approval-based deployments, logging, change management workflows, restricted production access | Access reviews, change tickets linked to releases, logs showing approved actions and traceable changes |
| Validation | Confirm outputs match expected results | Balance testing, file verification, reconciliation scripts, output exception checks | Output verification records, reconciliation evidence, documented follow-up for mismatches |
What auditors usually ask for
The strongest evidence tends to come from systems your team already uses every day. For Processing Integrity, that often includes GitHub or GitLab pull requests, Jira change tickets, Datadog alerts, queue dashboards, SQL reconciliation outputs, and application logs that show what happened when a transaction failed.
A readiness checklist should include:
- Documented objectives: Define what complete, accurate, timely, and authorized processing means for each critical workflow.
- Linked evidence: Connect tickets, commits, deployments, alerts, and reconciliations to the same process, not separate folders with no storyline.
- Exception handling: Show that failures are reviewed, corrected, and retained, not retried unnoticed until everyone forgets them.
- Retention planning: Keep evidence in a way that supports your audit window, especially for Type 2.
For teams building an evidence locker, this SOC 2 evidence collection guide is useful because it helps translate broad control language into specific artifacts. That matters for SOC 2 because Processing Integrity reports fail more often on evidence quality than on control intent.
A control you can explain but can’t evidence is not audit-ready.
What works and what usually doesn’t
What works is narrow scoping. Pick the workflows customers depend on most, then build controls around those. Billing runs, payout calculations, claims processing, import pipelines, and customer-facing reports are common candidates.
What doesn’t work is trying to make every application path part of Processing Integrity. That creates heavy evidence collection, inconsistent ownership, and audit fatigue. Start with the transactions that would materially damage trust if they were wrong.
Implementing and Monitoring Processing Integrity
The implementation gap between Type 1 and Type 2 is where organizations often underestimate effort. Processing Integrity was formalized in the AICPA’s 2014 Trust Services Criteria framework, and for a Type 2 audit auditors examine a population of transactions over a 6 to 12 month period, according to Linford & Co.’s Processing Integrity write-up. That means you’re not proving control design once. You’re proving consistent operation over time.

Type 1 versus Type 2 in real terms
A Type 1 review asks whether the controls are designed appropriately at a point in time. That’s manageable if you have documented validation checks, approvals, and logging in place.
A Type 2 review asks whether people and systems followed those controls during the review period. That’s where missing logs, undocumented exceptions, and ad hoc fixes become problems. If an engineer patched production logic to resolve a customer issue but the approval trail is weak, the auditor may treat that as an integrity control gap, not just a process issue.
Monitoring that auditors can test
Continuous monitoring is where Processing Integrity becomes operational instead of theoretical. Useful implementations usually include a mix of automated alerts and human review:
- Queue and batch monitoring: Alert when processing jobs stall, fail, or exceed the defined SLA.
- Reconciliation review: Compare source and destination records on a recurring basis and document variance handling.
- Change traceability: Tie code changes that affect logic to approved tickets and deployment records.
- Data quality dashboards: Track completeness, timeliness, and accuracy signals for critical workflows.
If your team is using AI to help generate test cases, runbooks, or exception triage instructions, the discipline is similar to mastering prompt engineering techniques. Clear instructions produce more consistent outputs. In compliance operations, vague control descriptions create vague evidence.
Here’s a useful overview of the kind of audit mindset teams should prepare for:
A practical operating model
The best implementations assign owners by workflow, not by policy document. Engineering owns application validations and deployment controls. Data or operations teams own reconciliations and exception review. GRC owns evidence cadence, retention, and auditor coordination.
If nobody owns the transaction from input to output, Processing Integrity will break at the handoff.
Why this matters for SOC 2 is direct. Type 2 fieldwork often follows a transaction from entry through processing to final output. If ownership changes three times and no one can reconstruct the path, the control may exist in practice but fail in audit.
Common Pitfalls in Processing Integrity Audits
The most common mistake is assuming strong Security controls automatically satisfy Processing Integrity. They don’t. An access-controlled system can still produce incomplete, delayed, or incorrect outputs if validation, reconciliation, and change discipline are weak.
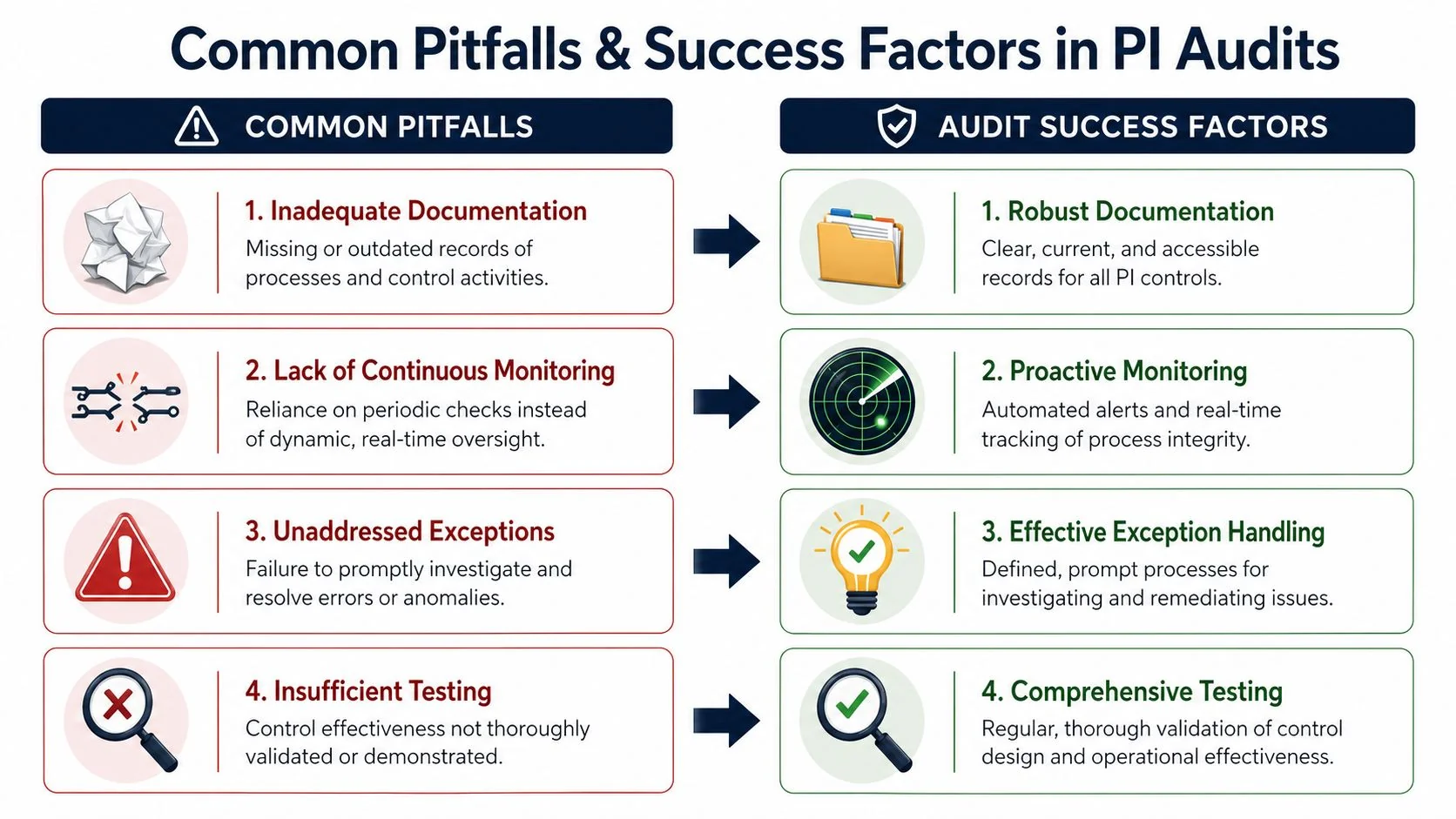
Four failure patterns auditors keep finding
-
Manual reconciliation with no procedure: Teams compare totals in a spreadsheet but never define who reviews it, when it happens, or what triggers escalation.
Fix: Write a short procedure, assign an owner, require signoff, and retain the output. -
Logging that captures failures but not decisions: The system shows an error happened, but nobody can show whether it was investigated or resolved correctly.
Fix: Link error logs to tickets or case records with documented disposition. -
Change tickets that don’t map to processing logic: Release notes say “bug fix” but don’t identify whether billing logic, transformation rules, or validation checks changed.
Fix: Require change descriptions to state the workflow affected and the validation performed before release. -
Undefined timeliness targets: Teams say jobs run “quickly” or “daily,” but the control never defines what counts as on time.
Fix: Tie timeliness to a documented operational target or contractual requirement.
The trade-off teams often resist
Automation is better for consistency, but not every reconciliation or review should be automated immediately. Early-stage companies often get further by formalizing a manual control first, then automating the highest-risk step later. Auditors will usually accept a well-run manual control if it’s documented, repeatable, and evidenced.
What doesn’t work is pretending a manual control is automated because the data exists somewhere in the system. If a human still has to inspect the output, make that review explicit and retain the record.
A hidden manual step is one of the fastest ways to create an audit exception.
Why this matters for SOC 2 is practical. Processing Integrity exceptions often come from ordinary operational shortcuts. The company isn’t reckless. It’s just relying on tribal knowledge that can’t survive audit testing.
Connecting Processing Integrity to Audit Success
Processing Integrity should enter scope only when the revenue case is clear. If your product mainly stores or routes customer data, Security may cover what buyers and auditors need today. If your product produces outputs customers rely on for billing, reporting, payouts, calculations, or compliance actions, leaving Processing Integrity out can slow deals and trigger longer security reviews.
That is the ultimate go or no-go test. Add PI when incorrect, incomplete, delayed, or unauthorized processing would create customer harm that a buyer can easily describe in a questionnaire or redline. Skip it for now if the control burden will outweigh deal value and your customers are not asking for proof that system outputs are accurate and complete.
Auditor fit matters more once PI is in scope. A firm that handles Security-only startup audits may not be the right choice if they also need to test application logic, reconciliations, exception handling, and the path from code change to customer-facing output. During auditor interviews, ask how they would sample transactions, trace failed jobs, inspect validation rules, and confirm that fixes were tested before release. If the answers stay at the policy level, expect friction during fieldwork.
Public examples can help calibrate expectations. DocsBot’s SOC 2 Type II audit shows how audit scope can become part of a company’s trust story once controls are running in production and evidence is routine. If you are comparing audit firms, platforms like SOC2Auditors exist to match companies with auditors based on criteria such as timeline, budget, and Type 1 or Type 2 capability.
The business upside is specific. Processing Integrity can support procurement conversations where buyers care less about whether data is encrypted and more about whether outputs are correct, complete, timely, and traceable. The cost is specific too. Engineering usually needs to formalize validation logic, define service-level targets for processing, retain reconciliation evidence, and make hidden manual reviews visible. For a SaaS company with low-risk workflows, that may be more effort than the pipeline justifies. For FinTech, payroll, billing, tax, or workflow automation products, it is often worth the added audit effort because it answers the question customers ask: can we rely on what your system does with our data?