Adding Confidentiality late is one of the more expensive SOC 2 scope mistakes a SaaS team can make. It usually shows up after a large prospect asks for it in procurement, legal points to confidentiality clauses already sitting in customer contracts, or the auditor asks why sensitive customer data is in scope operationally but missing from the report. At that point, the issue is no longer theoretical. It affects sales cycles, audit fees, and the work your team has to squeeze into an already tight timeline.
The Confidentiality Trust Services Criterion is optional under SOC 2, but the budget impact is real because optional does not mean low-risk from a buyer’s perspective. If your product handles customer financial records, source code, pricing data, product plans, or other restricted business information, adding Confidentiality often changes audit scope, evidence requirements, and control design. Teams that start with only Security can save money upfront, then spend more later expanding controls, updating policies, and collecting another round of evidence. That is why it helps to review the broader SOC 2 Trust Services Criteria framework before you lock scope.
For a CTO or GRC lead, having the SOC 2 confidentiality criteria explained in plain terms comes down to one practical question. Have you clearly identified what counts as confidential data, and can you show that access, retention, sharing, and disposal match the promises you made to customers?
If the answer is unclear, the audit gets more expensive fast. Auditors will ask for tighter scoping, cleaner data classification, stronger evidence of restricted access, and proof that confidential data is retained and deleted on purpose rather than by habit. Teams that prepare for that early usually avoid the worst version of the problem, which is discovering halfway through readiness that customer expectations are broader than the control set. For companies already working on broader security programs, resources on mastering data security compliance can help connect SOC 2 planning to the operational controls buyers expect to see.
Understanding the SOC 2 Confidentiality Criterion
Adding Confidentiality to a SOC 2 report is often the point where a straightforward audit becomes a scoping, evidence, and budget decision.
The criterion covers information your company or your customers designate as confidential based on contractual commitments and internal handling requirements. In practice, that usually includes customer files, source code, financial information, product plans, pricing terms, security documentation, and other restricted business data. Security remains the baseline for every SOC 2 report. Confidentiality adds a narrower question that auditors will test directly: are you handling specific classes of restricted information the way you said you would?
That distinction matters to buyers and to your audit plan. A team can have solid security controls and still fail to show that confidential data is limited by purpose, access, retention, sharing, and disposal. Once Confidentiality is in scope, auditors do not stop at “is the system protected?” They ask whether the protected data is clearly defined, whether the handling rules are documented, and whether the evidence matches those rules across systems, vendors, and personnel.
For a CTO, the business impact is usually immediate. Scope gets tighter, but the control narrative gets more specific. Legal has to line up contracts with policy language. Engineering has to show where confidential data lives and who can reach it. GRC has to collect evidence that proves restricted access, approved sharing, and timely deletion. If that groundwork is weak, audit hours go up and timelines stretch.
Confidentiality is also separate from Privacy. Privacy focuses on personal information and the obligations attached to it. Confidentiality applies to any information designated as confidential, whether or not it includes personal data. If your platform stores customer source code, internal forecasts, pricing models, or acquisition materials, Confidentiality may matter even when Privacy is not the main issue.
A practical rule works well here: if sales, procurement, or legal signs agreements that limit use or disclosure of customer information, evaluate Confidentiality before you finalize audit scope. Waiting until readiness testing usually costs more than making the decision early.
Teams that want a clearer baseline for how this criterion fits into the broader SOC 2 trust services criteria framework should review that structure before choosing report scope. If your control environment still feels disconnected across policy, operations, and customer commitments, guidance on mastering data security compliance can help tie those pieces together in a way auditors and buyers will both understand.
How to Define and Scope Confidential Data
Scope mistakes here are expensive. If the company cannot say what counts as confidential data, the audit scope expands, control owners multiply, and readiness work starts pulling in systems that never needed testing.

Start with business commitments
Begin with the commitments that create handling obligations. Review customer MSAs, security addenda, order forms, statements of work, procurement questionnaires, and internal handling standards. Pull the clauses that limit access, use, disclosure, retention, return, and deletion.
This step does more than improve policy language. It sets the audit boundary. If a contract says customer exports must be restricted to approved personnel and deleted after termination, that is no longer a general security discussion. It becomes a scoped confidentiality requirement with evidence behind it.
The categories that usually surface are predictable. Customer-uploaded files, source code, product roadmaps, incident records, pricing models, financial packages, model training data, and vendor assessments show up often. What matters is not the label itself. What matters is whether legal, sales, product, and engineering would classify the same information the same way under time pressure.
Build a classification model teams will actually use
Keep the model short enough to survive daily operations. Three levels are usually enough:
- Public. Information approved for external release, such as published documentation or marketing copy.
- Internal. Information intended for employees and approved contractors, such as internal procedures or project notes.
- Confidential. Information restricted by contract, sensitivity, or business impact, such as customer data exports, source code, security diagrams, banking details, and unreleased pricing.
If the model gets too granular, teams stop using it consistently and auditors start finding exceptions. I usually advise CTOs to avoid six-tier schemes unless they already have mature data governance and dedicated owners for classification decisions. For many B2B SaaS companies, simple and enforced beats detailed and ignored.
A usable policy also needs examples by function. Support should know whether ticket attachments are confidential. Engineering should know whether staging data copied from production is confidential. Finance should know whether board materials and forecast files fall under the same handling rules. Logical Commander’s internal control advice is useful on this point because control design fails when staff cannot apply it the same way in real workflows.
A weak classification model creates audit sprawl. A usable one reduces testing hours because the auditor can see which data requires special handling and which systems do not.
Scope systems, workflows, and exceptions
After the categories are set, map them to systems and workflows. Identify where confidential data is created, stored, processed, shared, backed up, and exported. Include cloud storage, support platforms, ticketing tools, messaging platforms, developer environments, data warehouses, laptops, file transfer tools, and any AI workflow where staff paste customer content.
Use a short worksheet for each system:
- What confidential data enters the system
- Who can access it
- Why that access is needed
- How data leaves the system
- What retention and disposal rules apply
Scope usually changes in various ways. Customer success may export reports to spreadsheets. Engineers may use production-like data in testing. Analysts may copy sensitive records into a warehouse that was never mentioned in the original SOC 2 narrative. Those decisions affect budget and timeline because each newly scoped system can trigger extra access reviews, logging checks, retention evidence, and policy exceptions.
Set handling rules that change behavior
The definition is only useful if it drives controls. For confidential data, that usually means restricted access, approval for sharing, encrypted storage and transmission, retention limits, approved transfer methods, and secure disposal.
Auditors do not need a long philosophy statement. They need to see that the label changes how the company operates. If confidential data can still be emailed to personal accounts, copied into unmanaged tools, or kept forever because nobody owns deletion, the scope exercise is incomplete.
Done well, this section saves real money. It cuts rework, limits surprise systems in scope, and gives sales a cleaner answer when buyers ask what data is covered by the report.
Mapping Core Controls to Confidentiality Requirements
The cleanest way to understand soc 2 confidentiality criteria explained is to map the criterion to the two points of focus auditors care about. The Confidentiality TSC centers on an entity’s commitment to protect confidential information and on controls that prevent unauthorized disclosure. It is distinct from Privacy, which is aimed at personal data, and breach notification policies are especially relevant because they appear in over 95% of enterprise agreements, as described by the Cloud Security Alliance’s explanation of the Trust Services Criteria.
That difference matters in implementation. Privacy controls often start with data subject rights and notice obligations. Confidentiality controls start with restricted access, controlled use, transmission safeguards, retention, disposal, and contract alignment.
What auditors actually expect to see
A common mistake is assuming that strong perimeter security automatically proves confidentiality. It doesn’t. Auditors usually look for evidence that confidential data has been deliberately identified and handled differently from other data.
The table below is the practical blueprint.
| AICPA Point of Focus | Example Control | Implementation Example | Required Evidence |
|---|---|---|---|
| Commitment to protect confidential information | Data classification and handling policy | Policy defines confidential data, approved storage locations, sharing restrictions, retention expectations, and disposal rules | Approved policy, revision history, employee acknowledgement, training artifact |
| Commitment to protect confidential information | Contractual confidentiality obligations | Customer agreements and vendor contracts include confidentiality clauses, permitted use language, and breach notification obligations | Sample customer agreement, vendor security addendum, contract review checklist |
| Commitment to protect confidential information | Retention and secure disposal | Retention schedule exists for confidential data repositories; disposal workflows are documented and approved | Retention schedule, deletion tickets, disposal procedure, system setting screenshots |
| Prevent unauthorized disclosure | Encryption at rest and in transit | Cloud storage encryption enabled; application and API traffic use encrypted transport | Configuration screenshots, cloud settings, architecture diagram, encryption standard reference |
| Prevent unauthorized disclosure | Role-based access control | Access to confidential repositories is limited by role, team, and business need | IAM role matrix, access request tickets, approval records, user access export |
| Prevent unauthorized disclosure | Data masking or restricted views | Support staff see limited fields; finance and engineering have segmented access based on job function | Screen captures of masked fields, role design document, test user evidence |
| Prevent unauthorized disclosure | Monitoring and incident handling | Alerts, logging, and escalation procedures exist for suspicious access or unauthorized sharing | Log samples, incident response procedure, alert configurations, investigation tickets |
| Prevent unauthorized disclosure | Breach notification procedure | Response playbook includes customer communication triggers for confidentiality incidents | Incident response plan, notification template, tabletop record, legal review artifact |
Controls that work and controls that don’t
Controls work when they are tied to the data flows. For example, RBAC in Okta, Entra ID, AWS IAM, GitHub, Jira, and your cloud data platform can be strong evidence if role design reflects business need. Encryption settings in AWS, Azure, Google Cloud, Snowflake, or your storage layer are useful only when they cover the repositories that contain confidential data.
Controls don’t work when they exist as generic policy language with no system trace. “We restrict access on a need-to-know basis” is not evidence. An auditor will ask who has access, who approved it, how often it is reviewed, and whether terminated users lose access promptly.
Many teams also overlook internal controls outside the security stack. Offboarding, procurement review, contract review, legal language, and exception management all affect Confidentiality. If you’re tightening the operating model behind those processes, Logical Commander’s internal control advice is a practical complement to the technical work.
Strong confidentiality scope is usually less about buying a new tool and more about proving that policies, contracts, identity controls, and retention rules say the same thing.
Gathering the Right Evidence for Your Auditor
A confidentiality control that isn’t evidenced might as well not exist. This often causes many SOC 2 projects to slow down. Engineering says encryption is enabled. HR says NDAs are standard. Legal says vendor clauses are in place. The auditor still needs artifacts.

Build an evidence list by control owner
Don’t collect evidence by framework language alone. Collect it by owner and system. That means HR provides signed confidentiality acknowledgements and onboarding records. Legal provides standard contract clauses and executed examples. Engineering provides encryption settings, repository access evidence, and environment segmentation records. IT provides IAM screenshots, access review outputs, and offboarding tickets.
A pre-audit evidence pack for Confidentiality usually includes:
- Classification artifacts. Approved data classification policy, handling standard, and examples showing labels or documented categories in use.
- Access artifacts. Current user-role export, access approval tickets, quarterly review records, and screenshots from identity systems.
- Encryption artifacts. Cloud configuration screenshots, storage settings, transport security configurations, and architecture diagrams that show where confidential data resides.
- Retention and disposal artifacts. Retention schedules, deletion workflows, secure disposal procedures, and completed tickets or logs.
- Contractual artifacts. Employee NDA language, contractor confidentiality terms, customer clauses, and third-party contract provisions.
- Monitoring artifacts. Logs, alerts, DLP events if used, incident tickets, and response playbooks.
- Training artifacts. Confidentiality or security awareness training records tied to employees who access confidential systems.
AI evidence is now part of the conversation
Recent AICPA updates for 2025-2026 are adding points of focus around AI-processed confidential data, including audit trails for synthetic data generation and testing for prompt injection defenses, according to ISMS.online’s write-up on SOC 2 Confidentiality. For teams using LLM features, this changes evidence expectations. Auditors may ask how customer prompts are classified, whether model training inputs are restricted, what vendor AI clauses exist, and whether tokenization or other protective techniques are used.
That means your evidence list should now include AI-specific artifacts where relevant:
- Prompt handling controls. Internal standards for what staff or systems may send to AI services.
- Vendor review records. Security and confidentiality review for AI providers.
- Audit trails. Logs showing synthetic data generation or controlled AI processing activity.
- Testing records. Prompt injection or misuse testing tied to confidential workflows.
If confidential data touches an AI feature, don’t wait for the auditor to define the test population. Define the workflow yourself and gather evidence before fieldwork starts.
For teams that want a more structured pack-out process, this SOC 2 evidence collection guide is useful when assigning artifacts across engineering, legal, HR, and security owners.
Common Confidentiality Gaps and Remediation Strategies
Confidentiality is usually where a clean SOC 2 project gets more expensive.
Security controls can be in place and still fail this criterion if the company cannot show which data is confidential, where it lives, who can access it, and how that access is reviewed. That gap shows up late. By then, remediation work is competing with audit deadlines, contract reviews, and sales commitments.
The cost problem is usually scoping, not tooling. Add Confidentiality late, and teams often discover they need tighter legal terms, cleaner access review evidence, stricter production-data handling, and training that reflects real workflows. That work touches engineering, IT, legal, support, and procurement at the same time. For a CTO, that means budget pressure and lost time from people who were not planned into the audit.
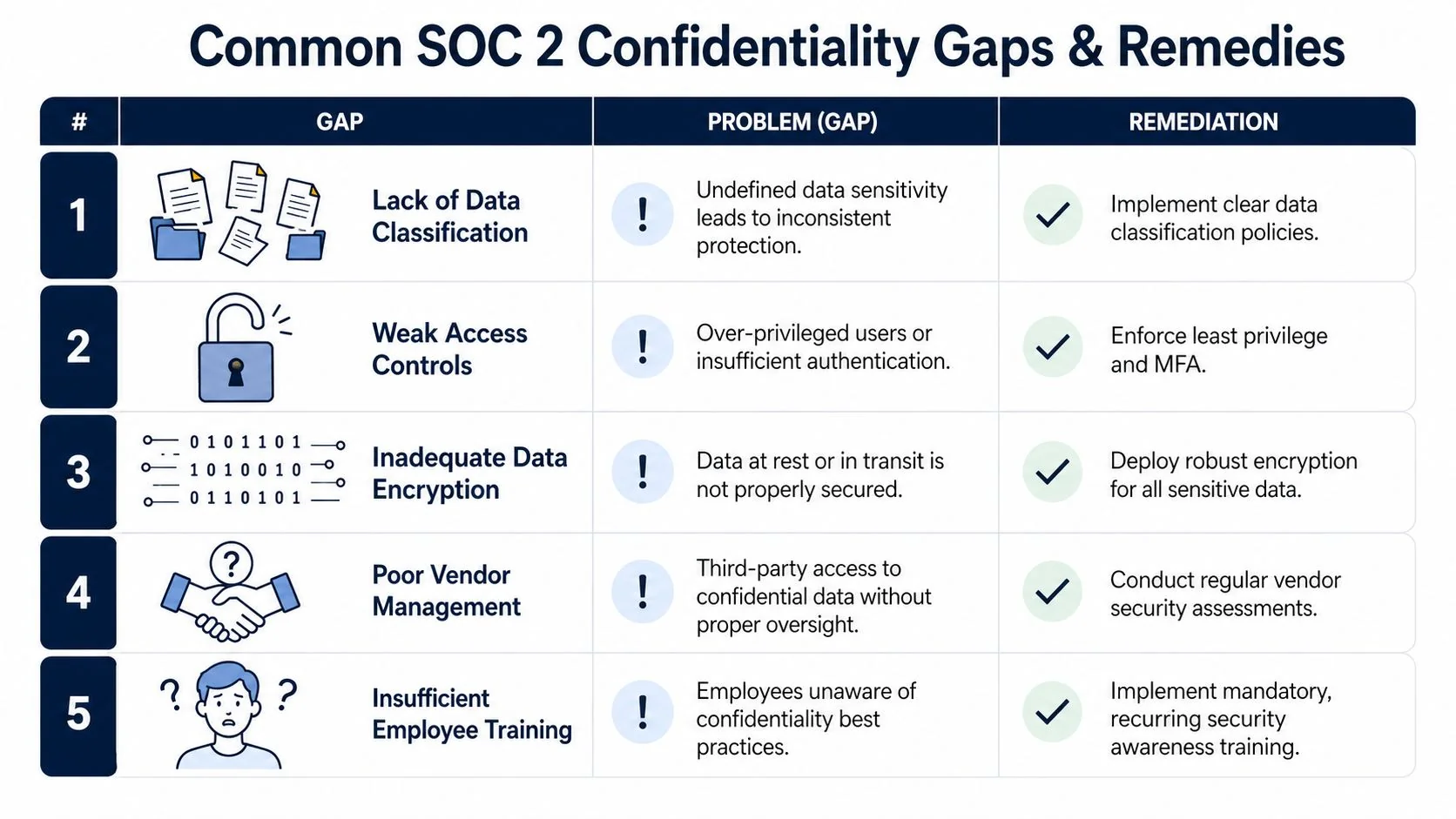
Five gaps that show up repeatedly
-
No usable data classification policy. Teams label everything as sensitive, which sounds cautious but creates audit trouble. If every system is marked critical, nothing is prioritized, and auditors cannot tell what handling rules apply. Fix: Write a short classification standard with clear labels, required handling, and named system owners. Then map those labels to your inventory so engineering and GRC are working from the same list.
-
Privilege creep. Employees keep access long after their role changes, especially across support tools, cloud infrastructure, BI platforms, and code repositories. This is one of the fastest ways to expand the audit sample because exceptions tend to spread across multiple systems.
Fix: Run scheduled access reviews for privileged and confidential-data roles, keep approval evidence, and remove stale access quickly. Role-based groups are easier to test than one-off grants. -
Production data copied into unsafe places. Confidential records end up in tickets, spreadsheets, lower environments, screenshots, and chat threads because teams are trying to solve customer issues quickly. The operational trade-off is real. Faster troubleshooting often creates weaker data handling.
Fix: Limit export paths, mask or tokenize fields outside production, and publish approved support workflows. Teams that sell services built around customer records, including providers of secure time tracking for agencies, need this documented before the first enterprise prospect asks how production data is used in support.
A short walkthrough helps teams visualize these failure points before the audit:
-
Weak vendor confidentiality terms. Security reviews may be thorough while contracts stay vague about permitted use, retention, subprocessors, and notification duties. Auditors will notice the mismatch if a vendor can access confidential data but the agreement does not clearly limit that access.
Fix: Standardize contract language for confidentiality obligations, data use restrictions, retention periods, subprocessors, and incident notification. Legal and procurement should treat those terms as part of control design, not just deal paper. -
Training that never covers confidentiality decisions. Generic awareness training does not help a support lead decide whether a CSV export can be shared internally or help a developer decide what belongs in a test dataset.
Fix: Add role-based examples for engineering, support, finance, and go-to-market teams. Good training reduces preventable exceptions and gives auditors something concrete to test besides policy acknowledgments.
Remediation that survives audit testing
Remediation has to be specific enough to test and cheap enough to maintain. Broad statements such as “improve access controls” or “protect sensitive data” create extra audit questions because nobody can prove what was supposed to happen. A control like “review privileged Okta and AWS access quarterly, retain manager approval in tickets, and track removals to completion” is much easier to test and much cheaper to defend during fieldwork.
Execution usually breaks at handoffs.
HR processes the termination. IT removes accounts. Engineering owns production access. Legal writes vendor terms. Procurement pushes vendors through review. GRC has to pull those pieces into one evidence trail. If ownership is implied instead of assigned, Confidentiality turns into exception cleanup, and that cleanup hits the audit timeline first.
Connecting Confidentiality to Audit Readiness and Selection
Confidentiality affects more than report language. It affects whether your audit scope matches what buyers ask for, whether your internal teams can produce evidence without chaos, and whether your auditor can test your environment efficiently.
A well-scoped Confidentiality program changes auditor conversations. Instead of debating what “sensitive” means halfway through fieldwork, you can present a defined data inventory, a classification standard, mapped controls, named system owners, and an evidence list that already aligns to those controls. That reduces rework. It also makes it easier to choose an auditor who understands your data model, whether you’re a SaaS platform with customer uploads, a FinTech handling banking workflows, or a HealthTech company managing sensitive operational records.
What buyers and auditors both care about
Enterprise customers usually don’t want a theory of confidentiality. They want confirmation that your commitments are matched by controls. Auditors want the same thing, but they test it through policy, configuration, operation, and evidence.
That overlap is why Confidentiality can be a deal-enabling decision rather than a compliance add-on. If your sales process routinely involves security reviews, confidentiality language in MSAs, or customer questions about restricted access to sensitive business data, including this criterion can remove friction earlier.
A practical signal comes from vendors that already talk openly about trust posture as part of customer evaluation. For example, TimeTackle’s note on secure time tracking for agencies reflects the broader market reality that buyers increasingly treat SOC 2 scope as part of vendor selection, not just a badge after procurement starts.
Readiness before auditor selection
Before you compare firms, have these items settled:
- Scope statement. Which products, environments, and data flows are in the report.
- Confidential data definition. What counts as confidential and why.
- Control ownership. Who owns IAM, contracts, retention, AI usage, offboarding, and incident communication.
- Evidence readiness. Whether artifacts already exist and are organized by control.
If those items are weak, any auditor will struggle. If they’re solid, you can compare firms based on fit instead of guessing who will interpret your scope correctly.
SOC 2 audit readiness isn’t just having controls in place. It’s being able to defend your confidentiality scope, show that the controls operate as designed, and produce evidence without improvising. When you can do that, Confidentiality stops being an optional add-on and becomes a clear part of a report that supports both assurance and sales.
If you’re preparing for a first Type 1 or planning a Type 2 with Confidentiality in scope, use SOC2Auditors.org to compare auditor fit, pricing, and timelines before you commit. It helps teams shortlist firms based on scope, industry, and readiness so the audit process starts with the right partner, not just the first proposal.