If you’re comparing soc 2 vs cmmc, you’re dealing with a practical business question, not a theoretical one. You may already be preparing for a SOC 2 report because enterprise buyers expect it, and now a defense customer, prime contractor, or government-facing prospect is asking whether that work also moves you toward CMMC. The short answer is yes, but only up to a point. SOC 2 is an attestation engagement performed by a licensed CPA firm under AICPA standards to report on controls relevant to the Security, Availability, Processing Integrity, Confidentiality, or Privacy of a system. CMMC is the U.S. Department of Defense model for verifying that contractors implement required cybersecurity practices to protect Federal Contract Information and Controlled Unclassified Information. For a company pursuing SOC 2, that distinction matters because SOC 2 can build the operating discipline, evidence habits, and control base you need, while CMMC determines whether you can compete for certain defense work.
Defining the Frameworks SOC 2 and CMMC
A common starting point looks like this. A SaaS company is midway through SOC 2 prep because enterprise deals require it. Then a defense prospect asks whether the same work gets the company closer to CMMC. In many cases, it does. The catch is that the two frameworks answer different business questions, so teams need to understand where the overlap ends.
SOC 2 is the first formal assurance framework commercial software companies adopt. It helps buyers evaluate whether a company has designed and operated controls around a defined system. If your team needs a primer before planning scope, this guide to SOC 2 Certification explains the audit model and the preparation work behind it.
What SOC 2 is built to assess
SOC 2 is based on the Trust Services Criteria. Security is always in scope. Availability, Processing Integrity, Confidentiality, and Privacy are added based on what the company commits to customers and what the system does.
In practice, SOC 2 tests whether your control environment is organized, documented, and operating consistently over time. That includes evidence in areas such as:
- Access control: onboarding, offboarding, privileged access, MFA, and periodic access reviews
- Change management: approvals, testing, release controls, and rollback procedures
- Risk assessment: how management identifies, evaluates, and responds to risk
- Third-party oversight: vendor due diligence and ongoing monitoring
- Incident response: escalation, investigation, containment, and post-incident follow-up
The business advantage is scope control. A company can define the in-scope system carefully, prove that controls work for that system, and build credibility with commercial buyers without dragging every process and environment into the first audit.
What CMMC is built to assess
CMMC serves a different purpose. It is meant to confirm that contractors and subcontractors in the defense industrial base can protect Federal Contract Information and, where applicable, Controlled Unclassified Information at the level required for the work they perform.
That changes the operating model. CMMC is tied to contract requirements, prescribed practices, and assessment expectations set by the Department of Defense ecosystem. The framework is structured into three levels, with higher levels requiring broader implementation depth and more formal validation. For companies handling CUI, the center of gravity is Level 2 and its alignment to NIST SP 800-171 practices.
From a consulting standpoint, this is the distinction that affects budget and sequencing. SOC 2 lets you choose scope around a customer-facing system. CMMC scope is driven by where FCI or CUI lives, how it moves, who can access it, and whether the surrounding environment meets the required controls.
Why the distinction matters
Teams often ask whether SOC 2 and CMMC are redundant. They are not.
SOC 2 can speed up CMMC preparation if it is implemented with discipline. Documented policies, access reviews, change control evidence, risk registers, incident records, and ownership structures all carry value into a CMMC gap assessment. I have seen companies save meaningful time during CMMC readiness work because they had control operators, evidence habits, and management review in place from SOC 2.
But SOC 2 does not settle CMMC-specific questions. It does not decide CUI boundaries, inherited controls, enclave design, asset categorization, or how you meet every NIST SP 800-171 requirement. That is why a SOC 2-first path works best as a strategic accelerator. It reduces rework later, provided the company maps controls early and identifies the gaps before a defense opportunity forces a rushed remediation cycle.
Comparing the Governance and Audit Processes
A common failure pattern looks like this. A SaaS company finishes its SOC 2 audit, then a defense subcontract appears and leadership assumes the same auditor, the same evidence set, and the same scope will carry them into CMMC. That assumption costs a quarter or two.
SOC 2 and CMMC are both control-driven programs, but the governance model and the assessment process are different in ways that affect budget, staffing, and partner selection.
| Topic | SOC 2 | CMMC |
|---|---|---|
| Primary purpose | Demonstrate controls relevant to customer trust and vendor assurance | Meet DoD cybersecurity requirements for defense contracting |
| Governing basis | AICPA attestation standards and Trust Services Criteria | CMMC program requirements tied to DoD expectations |
| Who performs the assessment | Licensed CPA firms | Accredited C3PAOs for required third-party assessments |
| Assessment format | Type 1 or Type 2 | Assessment tied to required CMMC level |
| Scope flexibility | Flexible system scope and optional criteria beyond Security | Less flexible, requirement-driven scope |
| Why it matters to SOC 2 buyers | Faster path to commercial trust | Needed when federal or defense opportunities require it |
Auditor authority is not interchangeable
SOC 2 reports come from CPA firms operating under AICPA attestation standards. CMMC third-party assessments, where required, are performed by authorized C3PAOs under the CMMC ecosystem.
That distinction changes procurement and readiness planning early. A firm can be excellent at SOC 2 and still be the wrong choice to prepare your team for a CMMC assessment if it cannot help you define the right boundary, organize evidence for NIST 800-171 practices, or coordinate with the assessment ecosystem. I have seen companies discover this after signing the first engagement letter, which means they pay twice for scoping and document cleanup.
Ask two separate questions during vendor selection:
- Can this firm perform the SOC 2 examination?
- Can this partner support CMMC readiness with credible experience, control mapping discipline, and working knowledge of the C3PAO process?
Companies selling into both commercial and government markets benefit from treating those as related workstreams, not one vendor decision. A SOC 2 approach for government contractors works best when the audit plan already anticipates later federal requirements.
Type 1 and Type 2 are reporting choices, not CMMC maturity tiers
Internal teams compare SOC 2 Type 1 and Type 2 to CMMC Levels 1, 2, and 3. That comparison creates confusion.
SOC 2 Type 1 asks whether controls are designed appropriately at a point in time. SOC 2 Type 2 asks whether those controls operated consistently over a review period. CMMC levels serve a different purpose. They reflect the cybersecurity requirements tied to the kind of federal information your organization handles and the contract conditions attached to it.
A clean SOC 2 Type 2 report can still leave major CMMC gaps. It shows operating discipline. It does not prove that your environment meets every required CMMC practice, that your boundary is defined correctly, or that your handling of controlled information would survive a defense-focused assessment.
For a team pursuing SOC 2 first, this affects evidence design. Collect evidence in a way that supports both attestation and future readiness work. That means preserving control narratives, asset context, ownership, screenshots, tickets, approvals, and boundary explanations instead of gathering only the minimum an auditor samples.
Governance rhythm changes once CMMC is on the roadmap
SOC 2 governance follows an annual cycle. Policies are reviewed, access is recertified, exceptions are tracked, and evidence is assembled around the reporting window.
CMMC readiness puts more pressure on repeatability and technical specificity. Assessors will care how access is approved, how configurations are controlled, where protected data resides, who administers systems, and whether your documented process matches what administrators and engineers operate. The control may look familiar on paper. The required proof often looks different.
That is why a SOC 2-first strategy works only if the program is built with reuse in mind. Teams that maintain clear operating procedures for onboarding, offboarding, change control, access reviews, and incident response have a much easier path into CMMC readiness work. Teams that rely on scattered screenshots, Slack approvals, and undocumented exceptions end up rebuilding the record from scratch. This guide to documenting IT processes is a practical reference if your procedures still live in tribal knowledge and ticket comments.
What translates well, and what creates rework
What works:
- One accountable owner per control area. Security, IT, engineering, HR, and leadership should each own specific evidence and review duties.
- Evidence organized by control objective. Store approvals, logs, reviews, tickets, and screenshots where both auditors and readiness teams can find them.
- A defined system narrative. Explain what is in scope, who uses it, where data moves, and which controls are inherited.
What creates rework:
- Choosing an audit firm before deciding whether CMMC is a credible near-term possibility
- Treating a policy set as proof of operational maturity
- Assuming a successful SOC 2 audit answers boundary and protected-data questions
- Waiting until a contract opportunity arrives to clarify who handles federal information
The business consequence is straightforward. Control gaps can be fixed on a schedule. Governance mistakes force rescoping, duplicate testing, and another round of documentation work. That is why SOC 2 should be set up as an accelerator for CMMC, not as an isolated trust exercise.
Detailed Control Mapping and Gap Analysis
Control mapping is where the SOC 2 versus CMMC decision stops being theoretical and starts affecting budget, staffing, and timing. Teams that have a functioning SOC 2 program have more usable material than they think. They also have a few blind spots that become expensive if nobody names them early.
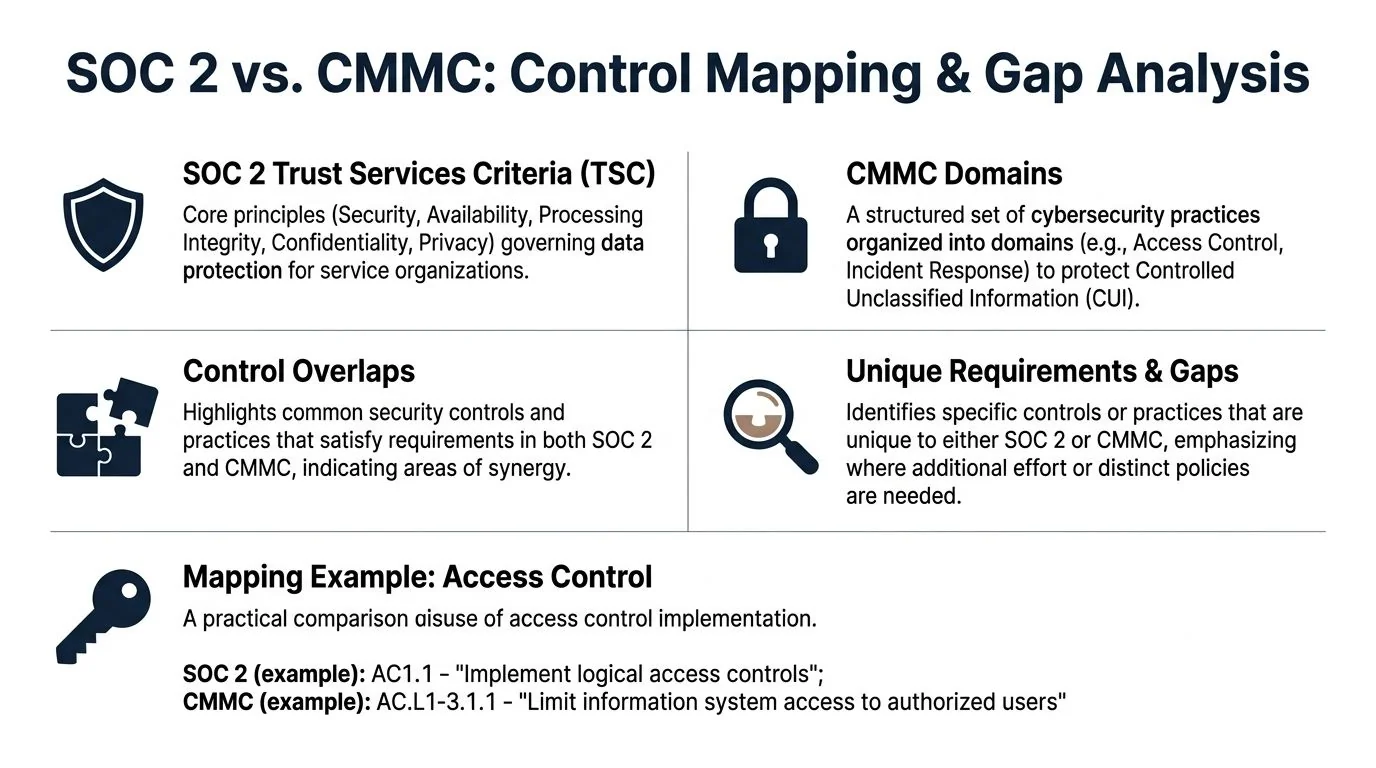
SOC 2 and CMMC are built differently, but they meet in many of the same operational areas. Access control, logging, incident response, change management, risk review, and physical safeguards carry over well enough to shorten a CMMC readiness effort. That does not mean a SOC 2 report substitutes for CMMC. It means a well-run SOC 2 program can reduce the amount of net-new design and documentation work.
Where SOC 2 gives you a head start
The best SOC 2 to CMMC transitions start with controls that operate on a schedule and produce evidence without manual scrambling. If user access reviews happen quarterly, privileged access is restricted, incidents are tracked, and changes are approved in tickets, the company already has a workable baseline.
A practical mapping often looks like this:
| SOC 2 area | Typical SOC 2 focus | Likely CMMC overlap | Why it matters for SOC 2 teams |
|---|---|---|---|
| CC6 Logical and physical access | Provisioning, deprovisioning, MFA, privileged access, office/server room controls | Access Control and Physical Protection practices | Access governance evidence is reusable if reviews are consistent and ownership is clear |
| CC7 System operations | Monitoring, vulnerability handling, incident detection, change tracking | Incident handling and operational security practices | Operating evidence from SOC 2 shortens later assessment prep |
| CC3 Risk management | Risk identification, risk response, management review | Risk-informed security management | Leadership review habits tend to carry over well |
| Change management related criteria | Approvals, testing, segregation, deployment tracking | Configuration and system integrity expectations | Engineering discipline becomes evidence instead of last-minute reconstruction |
This is the business case for a SOC 2-first path. The same control set that helps close commercial deals can become the starting point for CMMC gap analysis, provided the controls are operating and documented well.
AICPA criteria that carry the most weight
In practice, the SOC 2 programs that convert cleanly into CMMC readiness tend to be strong in the Common Criteria, especially:
- CC2 and CC3: governance, accountability, risk assessment, and management oversight
- CC6: logical and physical access controls
- CC7: system operations, monitoring, and incident response
- CC8: change management
- CC9: risk mitigation activities
I pay close attention to those areas during readiness reviews because they tell me whether the company has an operating security program or just a policy package. This classification matters because many teams overestimate readiness based on policy existence rather than operational proof.
A SOC 2 report is useful. A SOC 2 control system is what saves time later.
Where the overlap ends
The gaps appear once the conversation shifts from general security hygiene to federal handling requirements.
SOC 2 does not require you to define a Controlled Unclassified Information boundary with the precision CMMC expects. It also does not produce the implementation detail, system scoping decisions, and readiness artifacts that assessors will ask for in a defense context.
The net-new work shows up in a few predictable places:
- CUI boundary definition: where covered data is stored, processed, transmitted, and backed up
- System Security Plan and POA&M discipline: expected parts of CMMC preparation, but not standard outputs of a SOC 2 audit
- Federal reporting and contractual obligations: commercial incident processes often need updates for defense-related requirements
- Higher-assurance technical measures: some CMMC requirements go beyond what many SaaS companies build for an initial SOC 2
For teams sorting through that crossover, this guide on SOC 2 readiness for government contractors is a useful reference for understanding where commercial assurance work aligns with federal expectations and where it falls short.
How to run the gap analysis without wasting time
Start with what already exists. Use your SOC 2 control inventory, policy set, evidence repository, ticket workflows, vendor records, and system narrative as source material. Then test each item against likely CMMC expectations.
A practical process looks like this:
- Map each SOC 2 control to relevant CMMC domains or practices. Start with access control, logging, incident response, asset management, and change management.
- Rate the evidence, not just the control statement. A written policy has limited value if nobody can show reviews, approvals, logs, or remediation records.
- Separate implemented from assessor-ready. Many companies have the control behavior but not the artifact quality or traceability.
- Identify gaps that depend on CUI scope. Some issues do not appear until the company decides which systems, users, and vendors sit inside the boundary.
- Write remediation as specific projects. Name the owner, systems affected, required artifact, and completion criteria.
That approach keeps SOC 2 from becoming sunk cost. It turns prior audit work into a faster, cheaper starting point for CMMC readiness.
Strategic Scenarios When to Prioritize Each Framework
The right answer depends less on ideology and more on who is asking for proof, what information you handle, and how soon revenue depends on it.

Commercial SaaS startup
You sell workflow software, analytics, or infrastructure tooling to enterprise buyers. Security questionnaires are slowing deals. No current customer requires defense eligibility.
Prioritize SOC 2.
In this scenario, a Type 1 may help early, but most growth-stage teams should design for Type 2 from the beginning because the operating evidence discipline is what creates long-term value. Build your controls cleanly so the work can later support a federal gap analysis if that opportunity appears.
Growth-stage tech firm entering the defense supply chain
You have a SOC 2 report or are close to one. A prime contractor now wants to know whether your environment is suitable for government-related work.
This is the point where many teams ask whether the SOC 2 report can substitute for CMMC. The answer is nuanced. Workstreet notes that overlap exists, and it also cites a real-world case where Premier LogiTech replaced an annual SOC 2 with a CMMC Level 3 pre-assessment because customers accepted the stricter standard in lieu of SOC 2, while also noting that no official policy exists for SOC 2 to satisfy CMMC broadly (Workstreet).
That means your SOC 2 report may help in conversations. It should not be treated as guaranteed substitution.
Field note: If a defense customer informally accepts SOC 2 evidence while you build toward CMMC, document that acceptance in writing. Verbal comfort disappears when procurement or legal gets involved.
Established defense contractor
If defense contracts already define your business, CMMC is not optional. SOC 2 may still be useful for commercial expansion, partner diligence, or customer assurance outside the defense channel, but it won’t outrank the contractual requirement.
In this case, SOC 2 can still matter for operational reasons. Teams with a well-run SOC 2 style evidence program perform better during readiness because they know how to assign owners, preserve audit trails, and maintain recurring control activities.
Dual-use company selling into both markets
This is the most interesting case. Think of a company with software, managed services, or connected products serving both enterprise customers and defense-adjacent buyers.
The smart path is integrated, not sequential in the old sense. You still anchor the operating model in SOC 2-style governance, because that structure supports broad commercial trust. But you design the program with future federal needs in mind, especially around access control rigor, incident documentation, environment scoping, and system boundary clarity.
What this means for someone pursuing SOC 2
Use these scenarios as a decision filter:
- If commercial deals are blocked now: get SOC 2 moving.
- If defense opportunity is credible but not immediate: build SOC 2 controls so they can be mapped later.
- If contract language already points to defense requirements: start CMMC readiness planning alongside your SOC 2 work.
- If you’re handling mixed customer environments: avoid rebuilding later by documenting boundaries and exceptions now.
The business implication is straightforward. A SOC 2-first path is often the fastest route to disciplined controls, but it is not a permanent workaround for defense compliance.
Cost Timeline and Maturity An Honest Comparison
A common pattern looks like this. The sales team commits to an enterprise prospect, the defense opportunity looks promising, and leadership assumes SOC 2 and CMMC are just two audits on the same control set. A few weeks later, the budget is off, the timeline slips, and the team learns the expensive part was never the audit fee. It was the operating change underneath it.

Cost planning works better when framed around reuse. The pertinent question is which work strengthens your control program now and which work you will still have to build later for federal requirements.
Where budgets usually break
For SOC 2, the visible line items are the CPA firm and, in many cases, an automation platform. The under-budgeted work sits inside the business: assigning control owners, cleaning up joiner and leaver processes, tuning logging, documenting exceptions, reviewing vendors, and collecting evidence in a way that can survive scrutiny over time.
For CMMC, the surprise costs come from narrower system boundaries, stricter handling requirements, technical hardening, and the documentation package needed to explain how the environment operates. Teams also underestimate the time required to get an assessor-ready System Security Plan and a defensible POA&M in place.
A budget model should account for five categories:
- Readiness work: gap assessment, policy revision, control design, and scoping decisions
- Technology changes: identity controls, endpoint management, logging, segmentation, and evidence collection
- Internal labor: security, IT, engineering, HR, legal, and management review time
- External validation: CPA audit costs for SOC 2 or the CMMC assessment path
- Remediation reserve: scope changes and control fixes that show up once testing starts
Timeline is driven by maturity, not urgency
SOC 2 starts faster because the scoping model is more flexible and the evidence expectations are more familiar to commercial SaaS teams. CMMC tends to slow teams down for a different reason. It forces sharper answers about system boundaries, data handling, technical implementation, and formal documentation.
That distinction matters.
A company can launch a SOC 2 project quickly and still discover later that its environment is not ready for CMMC without meaningful redesign. Access control may need tighter enforcement. Logging may need better retention and review. Asset inventory, incident records, and boundary definitions need more discipline than a typical first-time SOC 2 effort requires.
Here is the practical comparison:
| Factor | SOC 2 Type 2 | CMMC 2.0 Level 2 |
|---|---|---|
| Primary driver | Commercial buyer assurance | Defense contract eligibility |
| Assessment body | CPA firm | C3PAO-based assessment path |
| Control structure | Trust Services Criteria with flexible scope | Required practice set tied to NIST SP 800-171 |
| Evidence style | Design and operating effectiveness of scoped controls | More prescriptive implementation evidence and readiness artifacts, explaining how the environment operates. |
| Typical maturity challenge | Building repeatable governance and audit evidence | Closing technical and documentation gaps around federal requirements |
| Business implication | Strong base for reusable control operations | Higher follow-on effort if federal work becomes material |
SOC 2 first usually saves money, but only if it is built well
I have seen SOC 2 programs reduce later CMMC effort by months. I have also seen weak SOC 2 programs create false confidence and force a rebuild.
The difference is maturity. If the SOC 2 project produces clear ownership, recurring reviews, stable evidence, and documented exceptions, it becomes a strong base for CMMC readiness. If it produces screenshots gathered at the end of the period and policies nobody follows, the money is mostly gone.
The reusable pieces are easy to recognize:
- Access reviews happen on a schedule and leave evidence.
- Terminations follow a documented workflow.
- Change management includes approvals and traceable tickets.
- Incidents are recorded the same way every time.
- Risk decisions are reviewed by management and retained.
Those habits are more valuable than any template library.
Teams save money when they build controls once, document them clearly, and use the same operating rhythm across frameworks.
If you’re budgeting your first SOC 2, use market ranges to set expectations, then pressure-test the assumptions with your scope, headcount, architecture, and evidence burden. This guide on how much a SOC 2 audit can cost is a useful starting point before you talk to firms.
The Trade-off
The cheapest-looking path is often the one that creates the most rework. A narrow SOC 2 scoped without future federal needs can still make sense, but leadership should make that choice consciously. If defense work is even a credible next-step market, build the SOC 2 program with cleaner boundaries, stronger access control, and better documentation from day one.
That is the honest comparison. SOC 2 is often the faster commercial move. CMMC is the stricter maturity test. For companies that may need both, a disciplined SOC 2-first program is not redundant cost. It is the lower-cost way to prepare for the work CMMC will eventually require.
Your Next Steps From SOC 2 to CMMC Readiness
If you already have a SOC 2 report, or you’re preparing for one now, the next move is not to rebuild your program. It’s to use what you’ve built as the baseline and pressure-test it against defense requirements.
Start with a formal mapping exercise
Take your current SOC 2 controls, evidence inventory, system description, and policies. Map them to the CMMC-relevant practice areas you expect to face.
Don’t score this exercise loosely. Mark each area as one of the following:
- Covered and evidenced
- Partially covered
- Present but undocumented
- Not addressed
That classification matters because many teams overestimate readiness based on policy existence rather than operational proof.
Build the documents SOC 2 doesn’t force you to own
SOC 2 can tolerate a lot of narrative flexibility. CMMC readiness is less forgiving about foundational documentation.
At minimum, prepare to develop and maintain:
- A System Security Plan that explains how controls are implemented in your environment
- A POA&M that tracks open gaps, owners, and remediation status
- A boundary definition for the systems, users, processes, and data flows that matter for the target requirement set
These aren’t just paperwork. They force clarity. And clarity is what turns “we probably do this” into “we can prove this.”
Tighten the controls that create the most crossover value
If you’re still early in your SOC 2 journey, put extra discipline into the controls most likely to pay forward:
- Access control: approval trails, review cadence, privileged access handling
- System operations: logging, alert handling, issue response, vulnerability management
- Change management: testing evidence, approvals, emergency change handling
- Risk management: management review and action tracking
- Incident response: consistent tickets, timelines, roles, and lessons learned
By doing this, SOC 2-first teams gain the highest advantage. Not by claiming equivalence, but by making the operating model strong enough that the next framework starts with structure instead of chaos.
Choose specialists carefully
If CMMC may be on your roadmap, ask every advisor the same practical questions:
- Have you supported both SOC 2 and CMMC readiness work?
- How do you translate SOC 2 evidence into a CMMC gap assessment?
- What artifacts do you expect to be reusable?
- Where do clients underestimate the gap?
- Can you separate CPA attestation work from CMMC-specific readiness support cleanly?
Those questions protect you from firms that are good at commercial compliance language but weak in defense-oriented implementation detail.
Treat SOC 2 as the platform, not the finish line
The companies that make this transition efficiently don’t start over. They reuse governance, tighten technical implementation, and upgrade the quality of their evidence and documentation. That’s the practical value in a SOC 2-first strategy.
If your goal is to serve both enterprise buyers and defense-adjacent customers, SOC 2 audit readiness is still the best starting point. It forces the habits that every later framework depends on: scoped systems, named control owners, recurring reviews, evidence collection, and management accountability. CMMC may become the next requirement, but the fastest route there is a SOC 2 program built for operational rigor instead of checklist theater. If you’re comparing audit partners or trying to find a firm that understands that progression, SOC2Auditors can help you evaluate options with a clearer view of timelines, capabilities, and fit.