A SOC 2 report is an independent attestation, issued by a licensed CPA firm under AICPA standards, on whether a service organization’s controls are suitably designed and, for Type 2, operating effectively against the Trust Services Criteria. For healthcare companies, that matters because the industry’s attack surface is large, interconnected, and unforgiving. Between 2009 and 2020, U.S. healthcare providers reported 3,705 data breaches involving 500 or more records, exposing over 260 million healthcare records (Censinet). If you’re selling into hospitals, clinics, payers, or digital health platforms, soc 2 for healthcare companies isn’t a nice-to-have security badge. It’s evidence that your controls can stand up to scrutiny from procurement, legal, security, and privacy reviewers.
Healthcare buyers already expect HIPAA alignment. What they still need is proof that your controls run the way your policies say they do. That’s the gap SOC 2 fills. If you need a concise baseline before diving into audit planning, this SOC 2 compliance overview is a useful refresher on the framework and audit model.
Why SOC 2 Matters in Healthcare Beyond HIPAA

HIPAA is a legal requirement for protecting PHI. SOC 2 is an assurance report that shows a healthcare company or vendor has implemented and maintained controls in a way an independent auditor can test. Those are different jobs.
That distinction matters during enterprise sales. A security team reviewing your vendor package doesn’t want to hear that you encrypt data or restrict access. They want to see that access reviews happen on schedule, logging is retained, changes are approved, incidents are handled through a repeatable process, and backup or recovery controls are more than policy text.
HIPAA tells you the obligation
HIPAA sets the floor for protecting PHI. It gives covered entities and business associates a legal framework for security and privacy.
But HIPAA leaves room for interpretation. Two companies can both say they are HIPAA compliant while operating at very different levels of control maturity. One may have solid evidence, tested procedures, and strong vendor oversight. The other may have scattered documentation and controls that depend on one overworked engineer remembering to do the right thing.
SOC 2 shows whether the controls hold up
SOC 2 matters for someone pursuing an audit because it forces discipline in the parts of the business that usually break first under customer due diligence:
- Access governance: Who can reach PHI, production systems, support tools, and backups.
- Operational consistency: Whether the team performs reviews, patching, incident response, and change approvals as designed.
- Third-party oversight: Whether subprocessors, hosting providers, EHR integration partners, and support vendors are managed formally.
- Evidence quality: Whether you can prove the control happened, not just assert it.
Practical rule: In healthcare, buyers don’t separate security maturity from business maturity. If you can’t produce clean evidence, they assume your operational risk is higher.
For HealthTech vendors, this affects procurement friction. Security questionnaires get shorter when your report answers common diligence questions in a standardized format. Legal review gets easier when your controls line up cleanly with the promises you make in BAAs. Internal leadership also gets a clearer picture of what still needs work before an external auditor starts testing.
SOC 2 also matters beyond data protection. Healthcare platforms support scheduling, chart access, care coordination, remote monitoring, and clinical workflows. Downtime, bad change control, or weak vendor governance can spill into patient operations fast. That’s why mature healthcare buyers don’t treat SOC 2 as redundant with HIPAA. They treat it as proof.
The Definitive Mapping of SOC 2 to HIPAA
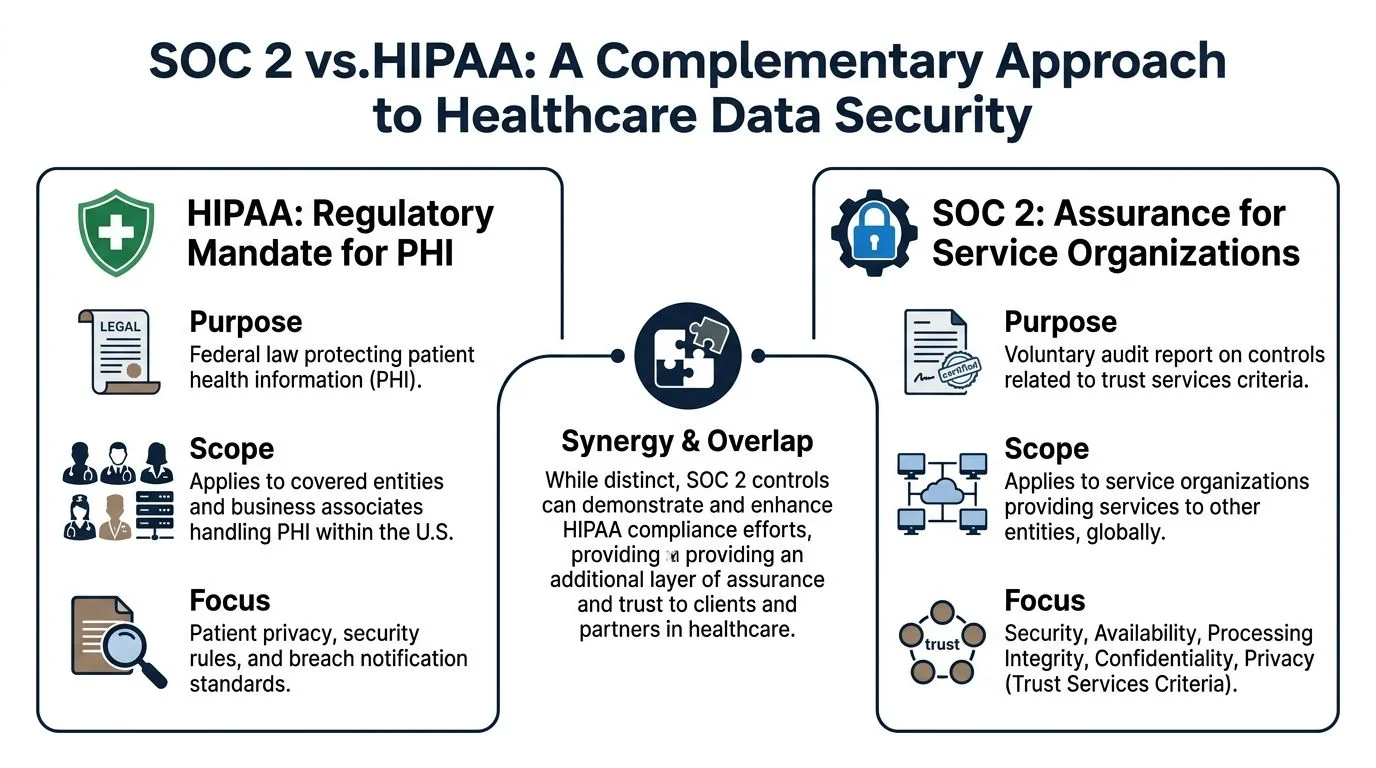
If you’re already HIPAA compliant, you still may need SOC 2 because HIPAA is a regulation and SOC 2 is an attestation framework. One defines obligations. The other gives customers independent assurance that your controls were examined and, in a Type 2 engagement, tested over time. Many healthcare companies lose time at this stage. They assume HIPAA documentation can be dropped into a SOC 2 audit with minor edits. Sometimes it can. Often it can’t, because the auditor is evaluating control design, evidence quality, system boundaries, and operating effectiveness in a more structured way.
A useful comparison chart for framing this with internal stakeholders is this healthcare-focused SOC 2 compliance framework comparison chart.
HIPAA and SOC 2 are complementary
HIPAA focuses on PHI and covered regulatory duties in the U.S. SOC 2 can be applied broadly across the systems and services your company operates, including environments that support healthcare workflows but go beyond the narrow legal scope of HIPAA.
For a HealthTech company, that difference shows up in places like:
- Customer-facing infrastructure that supports uptime and resilience
- Engineering workflows for code deployment and change approvals
- Vendor management for cloud platforms, support providers, and subcontractors
- Data segregation when you serve multiple customers in a shared SaaS environment
SOC 2 doesn’t replace HIPAA. It makes your security program easier to verify.
Where the overlap is strongest
The strongest overlap sits in the Security criterion. That includes access control, logical security, logging, system monitoring, and technical safeguards that map to HIPAA Security Rule expectations.
The overlap is helpful, but it isn’t automatic. A healthcare company needs to translate its HIPAA program into auditor-ready controls with named owners, evidence sources, review cadence, and exception handling.
Here’s a practical mapping:
| HIPAA Security Rule Safeguard | Relevant SOC 2 Trust Services Criteria | Example Control |
|---|---|---|
| Access Control | Security, Confidentiality | Role-based access, MFA, periodic user access reviews, documented deprovisioning |
| Audit Controls | Security, Processing Integrity | Centralized logging, alert review, investigation workflow, retained audit trails |
| Integrity | Processing Integrity, Security | Change management approvals, validation checks, defect management |
| Person or Entity Authentication | Security | SSO, MFA enforcement, privileged account restrictions |
| Transmission Security | Security, Confidentiality | Encryption in transit, secure API connections, key management procedures |
| Contingency Planning and Availability-related safeguards | Availability, Security | Backups, disaster recovery testing, redundancy, restoration procedures |
The operational difference buyers care about
A HIPAA program can exist mostly in policy form. A SOC 2 report forces an auditor to ask, “Show me.”
That means healthcare companies need evidence such as:
- Access matrices tied to job roles
- Network diagrams that show in-scope systems and data flows
- Patch management logs
- Incident response records
- Change tickets with approvals
- Vendor assessments and contract tracking
- Training completion records
Buyers don’t reject vendors because a policy is missing one sentence. They reject vendors because the operating model behind the policy looks unreliable.
That’s why soc 2 for healthcare companies is usually less about writing more documents and more about tightening execution. When a security reviewer asks how your team protects EHR integrations, controls support the answer. When legal asks how subprocessors are governed under a BAA chain, your vendor risk records support the answer. When an auditor samples evidence, your team doesn’t scramble.
Prioritizing Trust Services Criteria for Healthcare
Healthcare companies don’t need to approach the five Trust Services Criteria as a checkbox menu. They should prioritize them based on the systems they run, the data they hold, and the promises they make to customers. For most HealthTech vendors, Security is mandatory, and Availability plus Confidentiality are the criteria that make the report commercially useful.

The Security criterion is mandatory. It overlaps with HIPAA’s Security Rule, including §164.312, and effective implementation verified in a SOC 2 audit can reduce breach probabilities in PHI-handling systems by 40-60% through controls such as access reviews, patch management logs, and intrusion detection audits (Censinet). That’s why healthcare teams pursuing SOC 2 should start by getting Security controls clean, testable, and consistently evidenced.
Security is the audit backbone
Security includes the control environment auditors expect to see in any serious healthcare environment.
Typical evidence includes:
- Access reviews: for admins, support personnel, and contractors
- Baseline configurations: documented standards for endpoints, servers, and cloud resources
- Monitoring records: alerts, investigations, and escalation paths
- Patch and vulnerability records: proof that known weaknesses are identified and addressed
The reason this matters for SOC 2 is simple. If Security controls are weak, the audit becomes painful everywhere else. Exceptions pile up. Sampling becomes messy. Customer confidence drops.
Availability matters because healthcare systems can’t just be secure
A secure platform that isn’t reliably available still creates risk in healthcare. If your product supports chart access, messaging, intake, scheduling, RPM data, or care coordination, buyers will want to understand backups, restoration procedures, incident handling, and infrastructure resilience.
Availability becomes important when your system touches:
- EHR-connected workflows
- clinician-facing applications
- patient scheduling or intake
- interfaces that route time-sensitive data
An auditor will look for whether your availability commitments are backed by existing controls, not just uptime language in a contract.
Confidentiality is where PHI handling gets real
Healthcare companies often assume Security fully covers PHI protection. It doesn’t. Confidentiality pushes you to define what information is considered confidential, how it is classified, how access is restricted, and how disclosure is prevented across storage, transmission, support operations, and vendor relationships. Practical issues show up fast in this area:
- a support engineer exporting production data without proper approval
- a third-party lab integration receiving broader data than necessary
- shared internal channels exposing customer identifiers
- weak segregation between customer environments
Teams working through broader data privacy concerns often find that confidentiality controls fail not because encryption is missing, but because internal handling practices are loose.
Processing Integrity and Privacy are situational, not automatic
Some healthcare vendors need them. Others add them too early and create audit scope they can’t support yet.
Use Processing Integrity when your customer is buying accuracy, completeness, timeliness, or authorized processing. Think claims workflows, clinical routing logic, eligibility checks, lab result handling, or automation that materially affects downstream use.
Use Privacy when your service collects, uses, retains, discloses, or disposes of personal information under formal privacy commitments that customers will scrutinize in detail.
A practical explainer can help teams align on the criteria before scoping controls:
Selection heuristic: If a criterion doesn’t map to customer diligence questions, contractual commitments, or existing system risk, don’t add it merely for the sake of completeness.
For soc 2 for healthcare companies, the strongest starting position is Security, Availability, and Confidentiality. That combination reflects how healthcare buyers evaluate risk in real deals.
Common SOC 2 Control Gaps in HealthTech Companies
Most HealthTech companies don’t fail readiness because they lack policies. They fail because controls around PHI, integrations, and third parties aren’t operating in a way an auditor can test consistently.
EHR integration controls are often under-scoped
Teams scope the app and forget the integration layer. That’s a mistake.
If your platform pulls, pushes, transforms, or displays data from an EHR, the auditor will care about API authentication, logging, error handling, access to integration secrets, and how changes to interface mappings are approved. Weak evidence here creates doubt about both Security and Processing Integrity, even if the rest of the environment looks clean.
Vendor risk management breaks under real scrutiny
Healthcare companies rely on cloud hosting, support tools, communication platforms, observability products, outsourced development, and niche healthcare data vendors. Yet vendor inventories are often incomplete, security reviews aren’t updated, and BAA obligations aren’t tracked in one place.
This becomes a major issue because healthcare organizations have been impacted by third-party incidents, and customer reviewers know it. If your team can’t explain who your critical vendors are, what data they touch, and what due diligence you performed, procurement slows down.
Logging exists, but monitoring doesn’t
A lot of teams can produce logs. Fewer can show that someone reviews them, investigates anomalies, and retains evidence of follow-up.
Common examples include:
- API audit trails without ownership: data access is logged, but nobody reviews unusual patterns.
- Admin actions without escalation criteria: privileged activity is captured, but there’s no process for investigating risky events.
- Alert fatigue in cloud tooling: monitoring tools trigger events, but triage is informal and undocumented.
Disaster recovery plans look good on paper and weak in practice
Healthcare buyers care about disruption because service interruption can affect operations beyond IT. Yet many HealthTech companies haven’t validated restore procedures, assigned recovery roles clearly, or documented lessons from tabletop exercises.
An auditor will notice quickly if your recovery plan is just a policy file with no tested evidence behind it.
Medical device and edge security are ignored
Companies working with connected devices, remote monitoring hardware, or clinic-based equipment often build strong cloud controls and weak edge controls. Device provisioning, update management, physical handling, and service account restrictions get overlooked.
If your product touches a device, kiosk, tablet, or edge component in a clinical setting, auditors and customers will expect those boundaries to be governed, not assumed.
The pattern across these gaps is consistent. The control usually exists in intention, but not in evidence. That’s exactly what SOC 2 exposes.
A Step-by-Step SOC 2 Readiness Roadmap
Healthcare companies should treat readiness as an operating project, not a documentation sprint. The path is straightforward when the scope is right and the control owners know what evidence they need to produce.
The endpoint most healthcare buyers want is SOC 2 Type 2, because it evaluates control effectiveness over a 6 to 12 month period and is widely treated as the gold standard for healthcare technology vendors. Without a Type 2 report, vendors can face 2-3x higher rejection rates in procurement due diligence because health systems want proof of operational resilience, not just a point-in-time design review (AmplifyMD).
Step 1 should define the system boundary
Start by deciding what service is being audited.
For healthcare companies, that usually means identifying:
- the product or platform in scope
- the environments that support it
- the people who administer it
- the vendors that materially affect it
- the data flows involving PHI and confidential information
Bad scoping creates two expensive outcomes. You either over-scope and spend months documenting systems that don’t matter, or under-scope and discover late in the process that critical workflows were excluded incorrectly.
Step 2 needs a real gap assessment
A useful gap assessment doesn’t just compare your policies to a template. It checks whether controls exist, whether owners are assigned, and whether evidence is generated in a form an auditor can sample. Teams often waste effort at this stage. They write detailed policies while leaving control execution weak.
Focus on areas that commonly fail in healthcare:
| Readiness area | What to verify before the audit |
|---|---|
| Access management | Role design, joiner-mover-leaver process, admin review cadence |
| Change management | Ticketing, approvals, emergency changes, production deployment records |
| Incident response | Severity definitions, investigation records, response ownership |
| Vendor oversight | Vendor inventory, security reviews, contract tracking, BAA handling |
| Backup and recovery | Backup success evidence, restore testing, recovery responsibilities |
Step 3 is remediation, not paperwork theater
Teams often waste effort at this stage. They write detailed policies while leaving control execution weak.
What works:
- assign a named owner to each control
- automate evidence where possible
- standardize recurring reviews on a fixed cadence
- narrow admin access aggressively
- centralize system logs and vendor records
What doesn’t work:
- storing evidence in random folders
- relying on manual screenshots for every test
- leaving production access exceptions undocumented
- using a generic security policy that doesn’t match your environment
Strong SOC 2 readiness comes from repeatable operations. The report is the output, not the system.
Step 4 is building the evidence trail
By the time the audit starts, your team should know exactly where each evidence item lives and who owns it. Auditors don’t want a heroic scramble. They want clean, timely samples.
Good evidence management usually includes:
- Control narratives that describe what happens and who performs it
- System diagrams that match the scoped environment
- Linked evidence repositories for approvals, logs, tickets, and reviews
- Exception handling records showing how deviations were addressed
Step 5 is surviving the observation period
Type 1 asks whether controls are designed at a point in time. Type 2 asks whether they operated over the review period. In healthcare, Type 2 is usually the report that closes deals because it answers the buyer’s real question: can this team run a disciplined security program consistently?
The healthcare-specific challenge is that operations change fast. New integrations launch. Vendors get added. support models evolve. That means your control cadence has to survive growth, not just exist long enough to pass one test sample.
Budgeting Your SOC 2 Timeline and Costs
SOC 2 projects for healthcare are expensive when leadership treats them as a side task, and manageable when they budget for scope, evidence, and internal ownership up front.
The hard benchmark is this: SOC 2 compliance projects typically take 3-12 months for preparation and cost between $15K and $400K+, depending on scope and company size. In healthcare, that investment also matters because 55% of organizations have been impacted by third-party supply chain incidents, which raises the importance of vendor oversight and BAA review discipline (Azalea Health).
What drives the cost
The biggest cost drivers are not mysterious. They usually come from scope and operating complexity.
| Cost driver | Why it raises budget |
|---|---|
| Broad system scope | More systems, teams, controls, and evidence to test |
| Multiple customer commitments | More scrutiny around uptime, privacy, confidentiality, and subprocessors |
| Weak starting controls | More remediation work before the audit period can begin |
| Healthcare integrations | More diagrams, change controls, and access controls around data exchange |
| Vendor sprawl | More due diligence and dependency tracking |
Internal labor is often the hidden line item. Security, engineering, IT, legal, HR, and product operations all contribute evidence. If nobody owns the project centrally, timelines slip and external audit costs rise because the process drags.
Type 1 is cheaper. Type 2 is more useful.
That trade-off should be discussed plainly with leadership.
Type 1 can help a first-time team validate control design and find obvious holes. It may be enough for very early conversations. But healthcare buyers usually want stronger proof. If your revenue plan depends on enterprise provider deals, Type 2 is usually the spend that matters.
A realistic budget conversation should include:
- Audit fees: what the CPA firm will charge based on scope
- Readiness support: internal staff time or outside advisory help
- Tooling: evidence collection, ticketing, access management, and monitoring support
- Remediation work: engineering or IT effort to close gaps before testing starts
Which compliance platform should a healthcare company actually pick? We ranked the platforms that handle HIPAA and SOC 2 together — with BAA availability, PHI-specific controls, and infrastructure-layer options for digital health — in Best SOC 2 Software for Healthcare.
How to keep the project from overrunning
The teams that stay close to budget do a few things well:
- They scope tightly: only include systems and services that support the product being sold.
- They reduce manual evidence: recurring controls should produce evidence through normal operations.
- They fix ownership early: every control has a person accountable for execution and evidence.
- They control vendor sprawl: fewer high-risk dependencies means cleaner diligence and cleaner audits.
If leadership wants a cheap SOC 2 and a fast SOC 2 at the same time, someone needs to explain the trade-off. In healthcare, weak readiness almost always costs more later.
How to Select a Specialized Healthcare SOC 2 Auditor
A generic CPA firm can issue a SOC 2 report. That doesn’t mean they understand the pressure points in healthcare. If your company handles PHI, signs BAAs, supports EHR-connected workflows, or operates infrastructure that a provider depends on, the auditor needs to understand how those realities affect scope, testing, and report quality.
That matters for SOC 2 readiness because the wrong auditor creates friction in two ways. First, they may miss important healthcare-specific risks during scoping, which leads to confusion later. Second, they may test controls in a way that doesn’t line up with how healthcare buyers review your report.
What to ask before you sign
Don’t ask whether they “do healthcare.” Ask questions that force specifics.
Use prompts like these:
- Describe your experience with EHR integrations. What evidence do you usually request around interface security, access, and change management?
- How do you evaluate PHI-related confidentiality controls? What distinguishes a mature healthcare SaaS environment from a generic SaaS environment?
- How do you review vendor risk management where BAAs are involved? What records do you expect to see?
- What do you typically test for availability in healthcare-facing systems? How do you evaluate backup and recovery evidence?
- How do you handle first-time Type 2 clients? What usually causes delays?
- Who runs the fieldwork? Senior auditors or junior staff following a checklist?
The quality of the answers matters more than the sales deck. Good healthcare auditors speak clearly about system boundaries, evidence expectations, common exceptions, and how they coordinate with internal security or GRC teams.
What strong auditor fit looks like
A suitable healthcare auditor usually has:
- a clear method for mapping controls to healthcare use cases
- comfort reviewing cloud infrastructure and vendor dependencies
- a practical view of PHI handling and confidentiality boundaries
- a disciplined request process so your team isn’t flooded with vague asks
- experience with first-time and repeat Type 2 engagements
If you’re comparing firms, tools such as SOC2Auditors healthcare auditor matching can help teams review healthcare-focused options by criteria such as industry fit, pricing range, and timeline expectations. That kind of comparison is useful when procurement, security, and finance all need to align on the selection.
For the auditor-side mechanics — how firms actually scope a combined SOC 2 + HIPAA engagement, and where HITRUST acts as an overlay proxy that filters the field from 74 down to 17 firms — see SOC 2 + HIPAA overlay auditor engagements.
The right auditor doesn’t make the standards easier. They make the process clearer, the scope sharper, and the final report more credible to the buyers who will read it.
A strong auditor is a force multiplier for readiness. They won’t build your controls for you, but they will test the right things in the right way. For healthcare companies, that’s the final reason soc 2 for healthcare companies should always be approached as an audit-readiness program, not just a compliance project. If your controls are scoped correctly, mapped sensibly to HIPAA realities, evidenced consistently, and reviewed by an auditor who understands healthcare operations, you’re in a much stronger position to pass the audit and win enterprise deals.